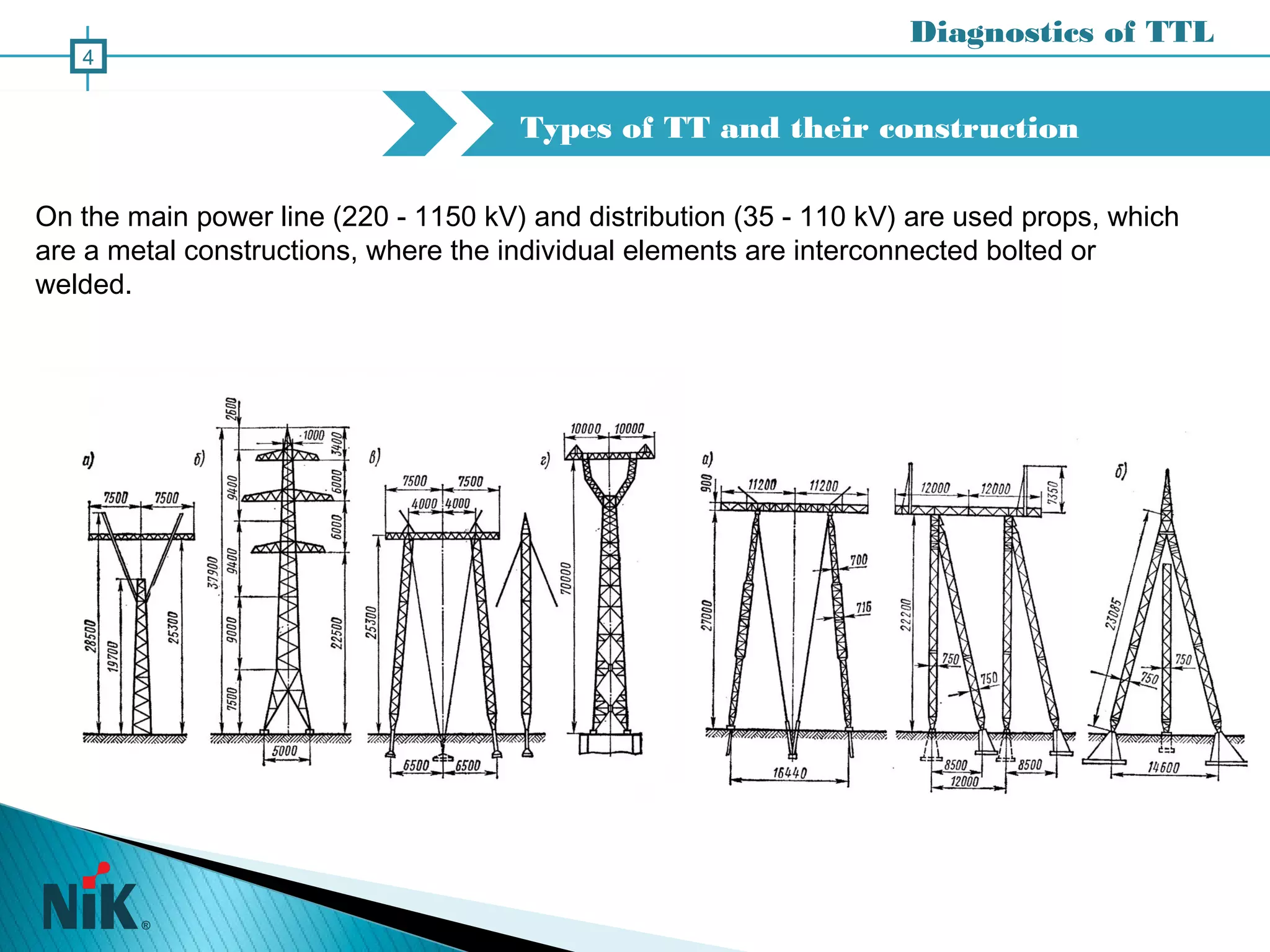
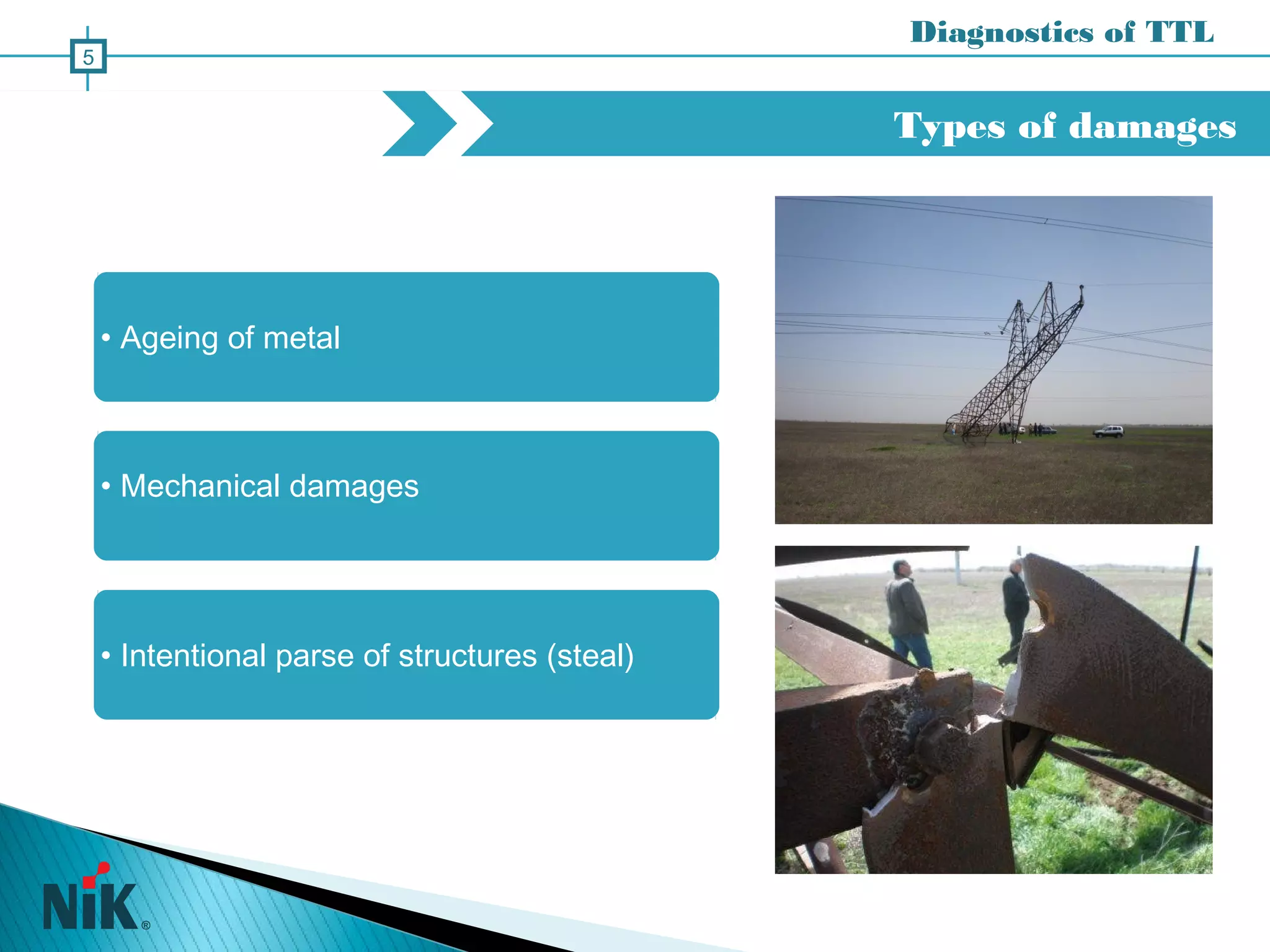
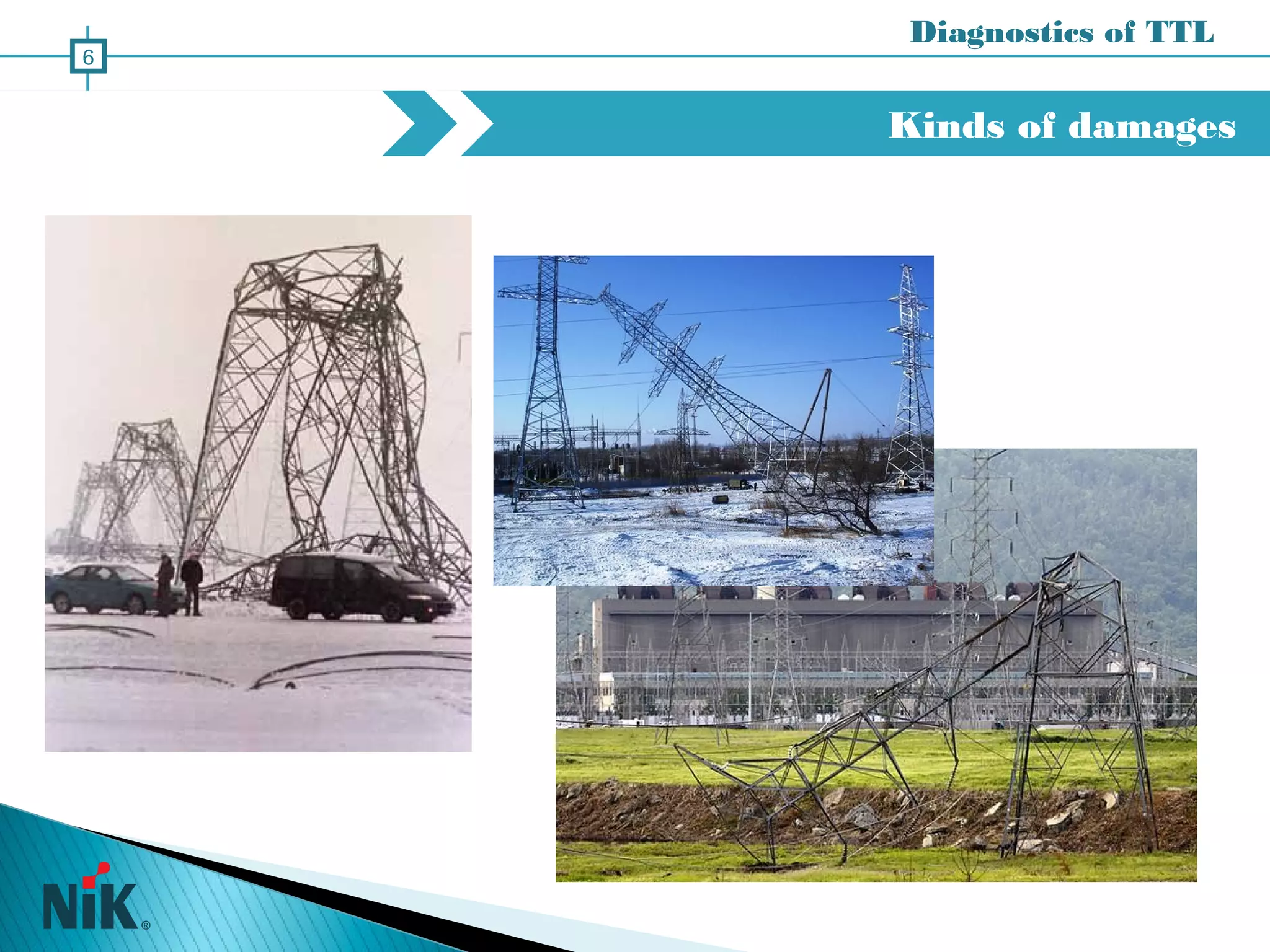
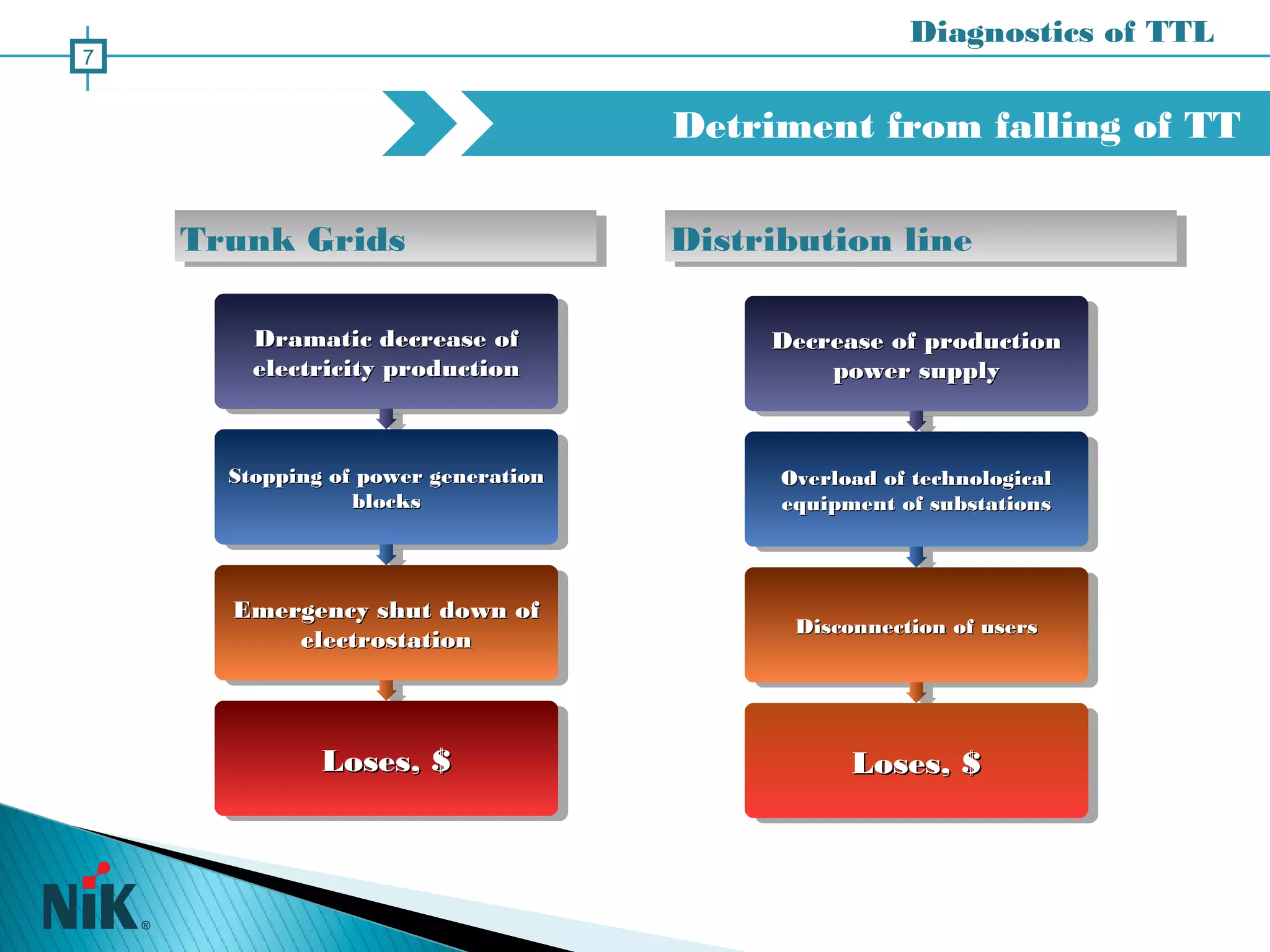
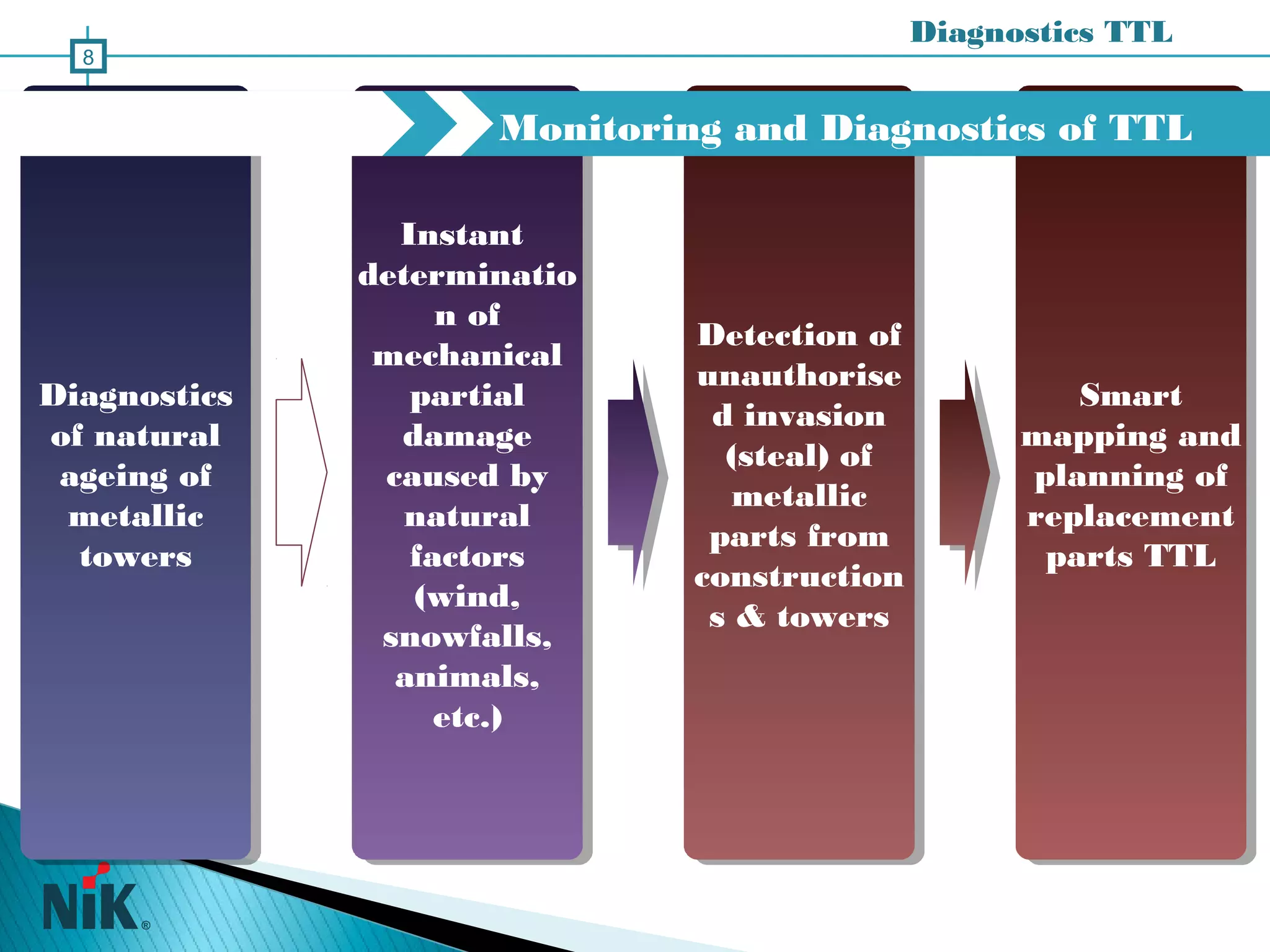
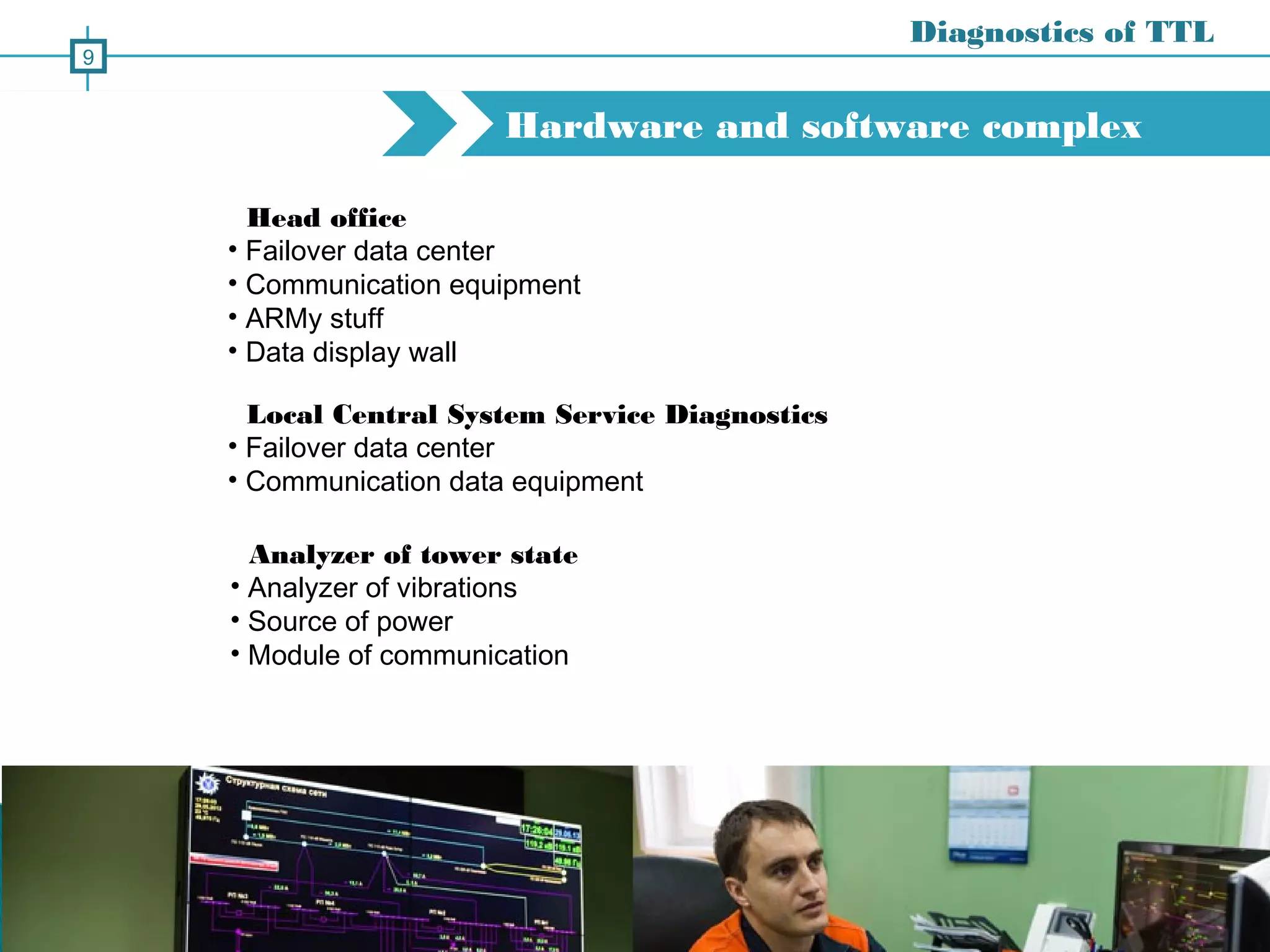
This document discusses an automated diagnostic system for monitoring the structural integrity of metal transmission towers used in power lines. It describes the types of towers and common damages, such as aging of metals and mechanical damage. The system uses sensors to monitor towers for natural degradation, partial damage from weather or animals, and theft. It analyzes vibration data to detect issues and provides smart mapping of problems to plan repairs. The system aims to prevent power outages from tower failures through remote monitoring of large numbers of structures.