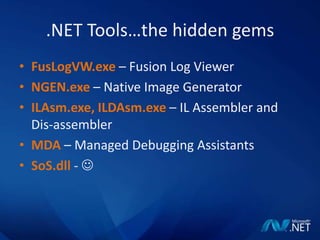
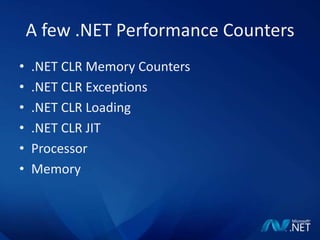
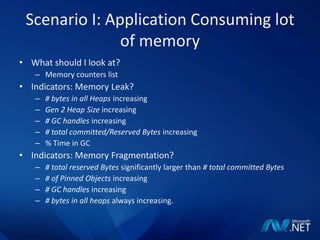
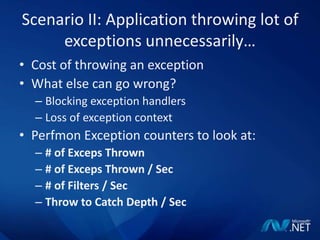
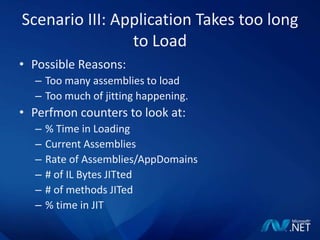
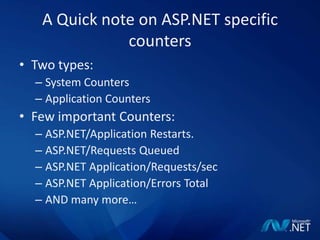
This document discusses .NET performance tips and techniques. It provides an overview of common .NET performance issues such as memory leaks, exceptions, and slow loading applications. It also introduces tools in the .NET framework that can help debug these issues, such as Fusion Log Viewer, Native Image Generator, and Performance Monitor counters. Specific scenarios are presented around resolving FileNotFoundExceptions, improving load time, identifying memory leaks, and troubleshooting PInvoke issues. The document emphasizes that performance is relative and introduces approaches like adding trace messages and using debugging tools to analyze problems.