Military Cyber Security Market 2019-2029
•
0 likes•37 views
To view full report please click on: https://www.visiongain.com/report/military-cyber-security-market-2019-2029/
Report
Share
Report
Share
Download to read offline
Recommended
Global Cybersecurity Market Industry Trends, Analysis Report 2021

By 2021 the global cybersecurity market is expected to be worth $1bn, up from $765m in 2017. The cybersecurity industry’s revenues over the next two years are network security appliances, cloud security, and artificial intelligence (AI).
https://www.aarkstore.com/financial-services/957606/cybersecurity-in-insurance-thematic-research
Time for a Cloud Security Strategy

As cloud adoption grows globally with the market projected to be worth $180 billion by 2020, organizations are increasingly turning to hybrid cloud infrastructures which incorporate both public and private clouds. However, this expansion creates new security challenges as threats like identity theft, data breaches, insecure APIs, system vulnerabilities, account hijacking, and denial of service attacks threaten customer data and systems. As such, experts recommend companies develop a comprehensive cloud security strategy to safely harness the benefits of hybrid cloud computing.
Security Threats in IT Infographic

NTT's breadth and scope allowed it to analyse three billion IT Security attacks in 2013, the results was combined to produce the Global Threat Intelligence Report. This infographic is an extract from the Global Threat Intelligence Report.
Latin america cyber security market,symantec market share internet security,m...

This document provides a summary of the Brazil cyber security market report by Ken Research. It details that the Brazil cyber security market has grown from USD ~million in 2011 to USD ~million in 2016 at a CAGR of ~%. The market is expected to continue growing due to rising internet and smartphone usage, increasing online transactions, and growing cyber threats. The report segments the market by type of security, solutions, industries, and regions and provides competitive analysis of companies in the Brazil cyber security market.
Global Cyber Security Overview | TechSci Research 

Simple Cyber Security Overview that provide you a simple way to understand the cyber security and their benefits. https://www.techsciresearch.com/
Deception Technology Market – Overview of advancements in innovation 2025

Computing systems and servers are largely affected by numerous security issues such as viruses, malware, cyber-attacks, worm infections, trojan attacks, and others.
Data Security Trends - Q4 2018 M&A Report

Get Ready for Data Security M&A Trends:
There is a high demand for robust and effective data security solutions for governments, banks, hospitals, and companies. The need to securely access remote servers, collaborate with international co-workers, and interact with customers around the globes is indispensable for most businesses today. We want to be a resource for executives and investors in Data Security companies who are considering their strategic growth and exit options in today's environment.
eSIM Market in Numbers

Up until today, there is a minimum of 158 mobile operators (including some MVNOs) providing eSIM services. The technology is spread across more than 60 countries in almost all regions. Here are some fun facts about eSIM market as of 2020!
Recommended
Global Cybersecurity Market Industry Trends, Analysis Report 2021

By 2021 the global cybersecurity market is expected to be worth $1bn, up from $765m in 2017. The cybersecurity industry’s revenues over the next two years are network security appliances, cloud security, and artificial intelligence (AI).
https://www.aarkstore.com/financial-services/957606/cybersecurity-in-insurance-thematic-research
Time for a Cloud Security Strategy

As cloud adoption grows globally with the market projected to be worth $180 billion by 2020, organizations are increasingly turning to hybrid cloud infrastructures which incorporate both public and private clouds. However, this expansion creates new security challenges as threats like identity theft, data breaches, insecure APIs, system vulnerabilities, account hijacking, and denial of service attacks threaten customer data and systems. As such, experts recommend companies develop a comprehensive cloud security strategy to safely harness the benefits of hybrid cloud computing.
Security Threats in IT Infographic

NTT's breadth and scope allowed it to analyse three billion IT Security attacks in 2013, the results was combined to produce the Global Threat Intelligence Report. This infographic is an extract from the Global Threat Intelligence Report.
Latin america cyber security market,symantec market share internet security,m...

This document provides a summary of the Brazil cyber security market report by Ken Research. It details that the Brazil cyber security market has grown from USD ~million in 2011 to USD ~million in 2016 at a CAGR of ~%. The market is expected to continue growing due to rising internet and smartphone usage, increasing online transactions, and growing cyber threats. The report segments the market by type of security, solutions, industries, and regions and provides competitive analysis of companies in the Brazil cyber security market.
Global Cyber Security Overview | TechSci Research 

Simple Cyber Security Overview that provide you a simple way to understand the cyber security and their benefits. https://www.techsciresearch.com/
Deception Technology Market – Overview of advancements in innovation 2025

Computing systems and servers are largely affected by numerous security issues such as viruses, malware, cyber-attacks, worm infections, trojan attacks, and others.
Data Security Trends - Q4 2018 M&A Report

Get Ready for Data Security M&A Trends:
There is a high demand for robust and effective data security solutions for governments, banks, hospitals, and companies. The need to securely access remote servers, collaborate with international co-workers, and interact with customers around the globes is indispensable for most businesses today. We want to be a resource for executives and investors in Data Security companies who are considering their strategic growth and exit options in today's environment.
eSIM Market in Numbers

Up until today, there is a minimum of 158 mobile operators (including some MVNOs) providing eSIM services. The technology is spread across more than 60 countries in almost all regions. Here are some fun facts about eSIM market as of 2020!
iot-bringing-trust-to-iot[1]![iot-bringing-trust-to-iot[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![iot-bringing-trust-to-iot[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The document discusses the potential of the Internet of Things (IoT) to generate $19 trillion in value over the next decade. However, it also notes that security concerns could hamper widespread adoption of IoT technologies if not addressed properly. The document advocates for a three-pronged approach to building trust in the IoT ecosystem through reliable connectivity, reliable security, and agile monetization solutions.
Cyfirma is launching its proprietary cyber intelligence analytics platform ca...

CYFIRMA is launching the cloud-based Cyber Intelligence Analytics Platform (CAP) v2.0 powered by Artificial Intelligence and Machine Learning engines, at media round table in Tokyo, Japan, on 25th July 2019.
Investing in Cybersecurity, 2020 outlook for Mexico

The document discusses investing in cybersecurity for 2020. It notes that Mexico is the 8th most targeted country by ransomware hackers. Global spending on cybersecurity services exceeds $124 billion annually from 4300 companies. Private capital investment in cybersecurity startups has grown 19% annually in recent years, with some startups raising over $100 million. However, M&A exit activity has not reflected this growth. The document suggests areas Mexico could improve in, such as supporting home-grown cybersecurity and public-private partnerships. It notes that 9 cybersecurity startups currently call Mexico home.
Networkers cyber security market intelligence report

In this report we share our insight on the recruitment of cyber security professionals including information regarding the key drivers in the cyber security market, permanent and contract recruitment trends, transferable skills, the top job titles, salaries and qualifications analysis, a heat map of skills demands/talent pools across the UK, concluding with recommendations on attracting and retaining cyber security talent.
Data Con LA 2018 Keynote - The secret to your big data success by Tim Eusterman

The document discusses how organizations can succeed with big data by integrating, automating, and orchestrating their digital business automation processes. It provides an example of how Malwarebytes leverages big data, artificial intelligence, and the cloud to protect millions of users by processing over 1.7 trillion data records per day to detect malware threats and remediate issues for their customers. The document advertises learning more at the BMC Software booth about their Control-M product and a chance to win a drone.
Cloud Computing could change mobile business

Cloud computing could change the mobile phone business in three main ways:
1) By providing scalable infrastructure resources that mobile companies can access on demand, reducing costs compared to building their own data centers.
2) Allowing mobile companies to more easily expand into new markets around the world without establishing their own local infrastructure first.
3) Potentially opening up new revenue opportunities for mobile companies by leveraging cloud-based services like artificial intelligence and analytics.
INFOGRAPHIC - 6 Reasons Why Cyber Security is Top Priority in 2019 for INDIA

India's cybersecurity is not different from that of the rest of the world. There are a host of reasons to pay utmost consideration to India's cybersecurity in 2019. This post speaks it all - the top 6 reasons why Cyber Security should be Digital India's foremost priority. Have a look:
Dutch Cyber Security Investment Landscape 2020

The number of cyber security companies in the Netherlands has risen sharply over the last decade, growing from 23 companies in 2000 to over 172 companies in 2020. However, the number of new companies founded each year has slowed in recent years. Amsterdam and Zuid-Holland are the largest hubs for cyber security companies. Seed-stage funding has dominated investment activity, though the average size of seed rounds has fluctuated between €0.3 million and €1 million from 2015 to 2020. Threat intelligence companies have raised the most capital on average per round despite identity and access management and public safety companies receiving more total rounds of funding. The largest exits include acquisitions valued over €100 million.
Growth Codes 

http://www.ericsson.com/unplug/growth/
How operators turn data growth into
profitable revenue growth.
Over the past year, we’ve talked to customers all over the world about our UNPLUG! Logics – smart ways of creating mobile broadband value that are inspired by models from other industries. We started UNPLUG! by discussing business before moving onto technology – and we’ve had a great response. Now it’s time for the third phase of the campaign – it’s time to focus on growth.
European Smart Home Investment Landscape

European smart home investments peaked in 2018 but have since declined, impacted by COVID-19. While the number of deals fell after 2018, average deal sizes increased. The UK secured the most deals, followed by Germany. Most funding went to security/safety, energy management and voice recognition companies. Major investors included corporate giants and VC funds, though crowdfunding also played a role. Notable acquirers were from the US, seeking to expand their smart home presence in Europe. The global market is projected to grow substantially, led by smart speakers, though COVID-19 has slowed 2020 growth.
[Webinar] The impact of innovation and technology for businesses in 2018![[Webinar] The impact of innovation and technology for businesses in 2018](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar] The impact of innovation and technology for businesses in 2018](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This document outlines key themes from Somo's 2018 webinar on digital transformation. It discusses 6 major trends: 1) Interface Humanization, 2) Owning Data, 3) Contextual Relevance, 4) Monopoly Integration, 5) Immersive Engagement, and 6) Culture Reset. For each trend, it identifies accelerators, enabling technologies, and examples of companies demonstrating these concepts. The overall message is that businesses must prepare for continuous mobile evolution and innovation in order to stay relevant in 2018 and beyond.
TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy

TeleSign’s Findings on the Future of Digital Identity
Guillaume Bourcy, Data Growth and Strategy at TeleSign
COVID-19, A sign of What’s to Come: Accelerated Digital Transformation brings vulnerabilities, even with basic mitigation practice.
How Fraud is Endemic: Shifting from offline to online increases the need to establish trusted digital identities in real-time.
Today weaknesses, myth and reality of current solutions: Evolving government regulations have a serious impact on global industries.
Mitigating friction, while adhering to regulation and enhanced security processes, can be challenging.
Rising need for Ubiquity: A single, reliable partner to enable engagement and provide security insights.
Industrial Control Cybersecurity for Critical National Infrastructure 

Accelerating the implementation and increasing the cybersecurity posture among energy companies
throughout Europe and North America.
SonMax Launches its portfolio of Cyber Security, Risk Advisory and Big Data S...

SonMax, a leading cybersecurity company, has launched a new website at www.sonmax.com along with enhanced services. The new website features a modern design and easy-to-understand content to help clients better understand cybersecurity risks and solutions. SonMax takes a unique approach to cybersecurity by recognizing that most victims are unprepared for cyber attacks and focusing on building relationships to explain risks and solutions. The website outlines the company's risk resiliency and proactive prevention services and partnerships, with the goal of eradicating cybercrime one client at a time as threats continue rising by 35% annually.
Innovate for Cyber Resilience

The document discusses cybersecurity challenges facing utilities organizations and lessons that can be learned from leading organizations. It finds that 94% of utilities spend over 20% of budgets on advanced technologies but investments are still failing for 77% of organizations. Leading organizations are 4 times better at stopping attacks, 4 times better at detecting breaches faster, 3 times better at remediation, and 2 times better at reducing impacts. The key lessons are to prioritize speed, choose technologies to turbo-charge operations, scale capabilities, train more staff, and collaborate more while sustaining existing investments and security basics.
Future-proofing the Internet of Things

New survey finds that over 50% of companies will increase investments in the Internet of Things over the next two years. How is this transforming business models? This infographic recommends the three actions companies should take to prepare for a future with the IoT. Find out more here: http://bit.ly/1RgN17w
American Tower small cell solutions

American Tower is the largest wireless infrastructure company in the US. It has nearly 150,000 communication sites worldwide and over 100,000 points of presence for the top four US carriers. The document discusses American Tower's capabilities in designing, building, operating and managing wireless infrastructure solutions for enterprises. This includes providing in-building wireless networks through technologies like oDAS, iDAS and SmartPoles to address connectivity issues within buildings and venues facing capacity constraints. American Tower offers benefits like being a single point of contact and aligning its goals with property owners to help carriers and property owners meet their wireless needs.
KPN Ventures research series: cyber security investment landscape

Research report by KPN Ventures on investments in cyber security. In cooperation with data partners Dealroom.co and Deloitte.
Cyberstates 2018 - Michigan

Cyberstates provides comprehensive data, trending, and analysis of the tech workforce, tech economic impact, tech wages, innovation, occupation characteristics, and more. Cyberstates provides insights into the trends driving growth at the national level, state level, and the top metro areas in the United States. Visit www.cyberstates.org to access the full report.
State of cybersecurity report 2020- Post Covid 19

How strong is your cyber response? Post COVID-19 has changed how we work, shop, and interact. Lockdowns accelerated the rise of remote work, which was already gaining traction within many industries.
21 Cybersecurity Companies You Need to Know.pptx

Cybersecurity guards against cyber-attacks on Internet-connected systems, including hardware, software, and data.
Cyber security investments 2021

We found that while cyber security was named as the topmost future tech adoption for organizations in 2019, cyber security is now the second tech priority for 2021 but with a higher budget than previously allocated. We also discovered that cloud security currently holds more importance with CISOs, CTOs and CIOs than data security and privacy.
More Related Content
What's hot
iot-bringing-trust-to-iot[1]![iot-bringing-trust-to-iot[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![iot-bringing-trust-to-iot[1]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The document discusses the potential of the Internet of Things (IoT) to generate $19 trillion in value over the next decade. However, it also notes that security concerns could hamper widespread adoption of IoT technologies if not addressed properly. The document advocates for a three-pronged approach to building trust in the IoT ecosystem through reliable connectivity, reliable security, and agile monetization solutions.
Cyfirma is launching its proprietary cyber intelligence analytics platform ca...

CYFIRMA is launching the cloud-based Cyber Intelligence Analytics Platform (CAP) v2.0 powered by Artificial Intelligence and Machine Learning engines, at media round table in Tokyo, Japan, on 25th July 2019.
Investing in Cybersecurity, 2020 outlook for Mexico

The document discusses investing in cybersecurity for 2020. It notes that Mexico is the 8th most targeted country by ransomware hackers. Global spending on cybersecurity services exceeds $124 billion annually from 4300 companies. Private capital investment in cybersecurity startups has grown 19% annually in recent years, with some startups raising over $100 million. However, M&A exit activity has not reflected this growth. The document suggests areas Mexico could improve in, such as supporting home-grown cybersecurity and public-private partnerships. It notes that 9 cybersecurity startups currently call Mexico home.
Networkers cyber security market intelligence report

In this report we share our insight on the recruitment of cyber security professionals including information regarding the key drivers in the cyber security market, permanent and contract recruitment trends, transferable skills, the top job titles, salaries and qualifications analysis, a heat map of skills demands/talent pools across the UK, concluding with recommendations on attracting and retaining cyber security talent.
Data Con LA 2018 Keynote - The secret to your big data success by Tim Eusterman

The document discusses how organizations can succeed with big data by integrating, automating, and orchestrating their digital business automation processes. It provides an example of how Malwarebytes leverages big data, artificial intelligence, and the cloud to protect millions of users by processing over 1.7 trillion data records per day to detect malware threats and remediate issues for their customers. The document advertises learning more at the BMC Software booth about their Control-M product and a chance to win a drone.
Cloud Computing could change mobile business

Cloud computing could change the mobile phone business in three main ways:
1) By providing scalable infrastructure resources that mobile companies can access on demand, reducing costs compared to building their own data centers.
2) Allowing mobile companies to more easily expand into new markets around the world without establishing their own local infrastructure first.
3) Potentially opening up new revenue opportunities for mobile companies by leveraging cloud-based services like artificial intelligence and analytics.
INFOGRAPHIC - 6 Reasons Why Cyber Security is Top Priority in 2019 for INDIA

India's cybersecurity is not different from that of the rest of the world. There are a host of reasons to pay utmost consideration to India's cybersecurity in 2019. This post speaks it all - the top 6 reasons why Cyber Security should be Digital India's foremost priority. Have a look:
Dutch Cyber Security Investment Landscape 2020

The number of cyber security companies in the Netherlands has risen sharply over the last decade, growing from 23 companies in 2000 to over 172 companies in 2020. However, the number of new companies founded each year has slowed in recent years. Amsterdam and Zuid-Holland are the largest hubs for cyber security companies. Seed-stage funding has dominated investment activity, though the average size of seed rounds has fluctuated between €0.3 million and €1 million from 2015 to 2020. Threat intelligence companies have raised the most capital on average per round despite identity and access management and public safety companies receiving more total rounds of funding. The largest exits include acquisitions valued over €100 million.
Growth Codes 

http://www.ericsson.com/unplug/growth/
How operators turn data growth into
profitable revenue growth.
Over the past year, we’ve talked to customers all over the world about our UNPLUG! Logics – smart ways of creating mobile broadband value that are inspired by models from other industries. We started UNPLUG! by discussing business before moving onto technology – and we’ve had a great response. Now it’s time for the third phase of the campaign – it’s time to focus on growth.
European Smart Home Investment Landscape

European smart home investments peaked in 2018 but have since declined, impacted by COVID-19. While the number of deals fell after 2018, average deal sizes increased. The UK secured the most deals, followed by Germany. Most funding went to security/safety, energy management and voice recognition companies. Major investors included corporate giants and VC funds, though crowdfunding also played a role. Notable acquirers were from the US, seeking to expand their smart home presence in Europe. The global market is projected to grow substantially, led by smart speakers, though COVID-19 has slowed 2020 growth.
[Webinar] The impact of innovation and technology for businesses in 2018![[Webinar] The impact of innovation and technology for businesses in 2018](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar] The impact of innovation and technology for businesses in 2018](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This document outlines key themes from Somo's 2018 webinar on digital transformation. It discusses 6 major trends: 1) Interface Humanization, 2) Owning Data, 3) Contextual Relevance, 4) Monopoly Integration, 5) Immersive Engagement, and 6) Culture Reset. For each trend, it identifies accelerators, enabling technologies, and examples of companies demonstrating these concepts. The overall message is that businesses must prepare for continuous mobile evolution and innovation in order to stay relevant in 2018 and beyond.
TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy

TeleSign’s Findings on the Future of Digital Identity
Guillaume Bourcy, Data Growth and Strategy at TeleSign
COVID-19, A sign of What’s to Come: Accelerated Digital Transformation brings vulnerabilities, even with basic mitigation practice.
How Fraud is Endemic: Shifting from offline to online increases the need to establish trusted digital identities in real-time.
Today weaknesses, myth and reality of current solutions: Evolving government regulations have a serious impact on global industries.
Mitigating friction, while adhering to regulation and enhanced security processes, can be challenging.
Rising need for Ubiquity: A single, reliable partner to enable engagement and provide security insights.
Industrial Control Cybersecurity for Critical National Infrastructure 

Accelerating the implementation and increasing the cybersecurity posture among energy companies
throughout Europe and North America.
SonMax Launches its portfolio of Cyber Security, Risk Advisory and Big Data S...

SonMax, a leading cybersecurity company, has launched a new website at www.sonmax.com along with enhanced services. The new website features a modern design and easy-to-understand content to help clients better understand cybersecurity risks and solutions. SonMax takes a unique approach to cybersecurity by recognizing that most victims are unprepared for cyber attacks and focusing on building relationships to explain risks and solutions. The website outlines the company's risk resiliency and proactive prevention services and partnerships, with the goal of eradicating cybercrime one client at a time as threats continue rising by 35% annually.
Innovate for Cyber Resilience

The document discusses cybersecurity challenges facing utilities organizations and lessons that can be learned from leading organizations. It finds that 94% of utilities spend over 20% of budgets on advanced technologies but investments are still failing for 77% of organizations. Leading organizations are 4 times better at stopping attacks, 4 times better at detecting breaches faster, 3 times better at remediation, and 2 times better at reducing impacts. The key lessons are to prioritize speed, choose technologies to turbo-charge operations, scale capabilities, train more staff, and collaborate more while sustaining existing investments and security basics.
Future-proofing the Internet of Things

New survey finds that over 50% of companies will increase investments in the Internet of Things over the next two years. How is this transforming business models? This infographic recommends the three actions companies should take to prepare for a future with the IoT. Find out more here: http://bit.ly/1RgN17w
American Tower small cell solutions

American Tower is the largest wireless infrastructure company in the US. It has nearly 150,000 communication sites worldwide and over 100,000 points of presence for the top four US carriers. The document discusses American Tower's capabilities in designing, building, operating and managing wireless infrastructure solutions for enterprises. This includes providing in-building wireless networks through technologies like oDAS, iDAS and SmartPoles to address connectivity issues within buildings and venues facing capacity constraints. American Tower offers benefits like being a single point of contact and aligning its goals with property owners to help carriers and property owners meet their wireless needs.
KPN Ventures research series: cyber security investment landscape

Research report by KPN Ventures on investments in cyber security. In cooperation with data partners Dealroom.co and Deloitte.
Cyberstates 2018 - Michigan

Cyberstates provides comprehensive data, trending, and analysis of the tech workforce, tech economic impact, tech wages, innovation, occupation characteristics, and more. Cyberstates provides insights into the trends driving growth at the national level, state level, and the top metro areas in the United States. Visit www.cyberstates.org to access the full report.
State of cybersecurity report 2020- Post Covid 19

How strong is your cyber response? Post COVID-19 has changed how we work, shop, and interact. Lockdowns accelerated the rise of remote work, which was already gaining traction within many industries.
What's hot (20)
Cyfirma is launching its proprietary cyber intelligence analytics platform ca...

Cyfirma is launching its proprietary cyber intelligence analytics platform ca...
Investing in Cybersecurity, 2020 outlook for Mexico

Investing in Cybersecurity, 2020 outlook for Mexico
Networkers cyber security market intelligence report

Networkers cyber security market intelligence report
Data Con LA 2018 Keynote - The secret to your big data success by Tim Eusterman

Data Con LA 2018 Keynote - The secret to your big data success by Tim Eusterman
INFOGRAPHIC - 6 Reasons Why Cyber Security is Top Priority in 2019 for INDIA

INFOGRAPHIC - 6 Reasons Why Cyber Security is Top Priority in 2019 for INDIA
[Webinar] The impact of innovation and technology for businesses in 2018![[Webinar] The impact of innovation and technology for businesses in 2018](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar] The impact of innovation and technology for businesses in 2018](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar] The impact of innovation and technology for businesses in 2018
TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy

TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy
Industrial Control Cybersecurity for Critical National Infrastructure 

Industrial Control Cybersecurity for Critical National Infrastructure
SonMax Launches its portfolio of Cyber Security, Risk Advisory and Big Data S...

SonMax Launches its portfolio of Cyber Security, Risk Advisory and Big Data S...
KPN Ventures research series: cyber security investment landscape

KPN Ventures research series: cyber security investment landscape
Similar to Military Cyber Security Market 2019-2029
21 Cybersecurity Companies You Need to Know.pptx

Cybersecurity guards against cyber-attacks on Internet-connected systems, including hardware, software, and data.
Cyber security investments 2021

We found that while cyber security was named as the topmost future tech adoption for organizations in 2019, cyber security is now the second tech priority for 2021 but with a higher budget than previously allocated. We also discovered that cloud security currently holds more importance with CISOs, CTOs and CIOs than data security and privacy.
Epebinu 2CyberSecurity On Microsoft BreachingFirst Draft Of 

Epebinu 2
CyberSecurity On Microsoft Breaching
First Draft Of Paper Two
Olatunde Michael Epebinu
CDF 281
Professor Stuart Denrich
4/11/21
Cyber Security
Background Information on Microsoft
Microsoft is a company engaged in supporting, licensing, and developing a wide variety of software services and products. The company's aggressive strategies in the software market are some of the factors that have contributed to the company's success in multiple locations. Investing in the mobile phone and gaming market has contributed to the large market share the company has secured worldwide. However, the company has also been exposed to cybersecurity issues like many other software companies. Understanding the nature of cybersecurity experience at Microsoft is essential for creating and designing better mitigation measures for the company in the future.
The company's investment in creating and distributing Windows Mobile OS is among the most brilliant assets the company has made. This Mobile Os are used by numerous sellers such as LG, Samsung, and HTC. Releases such as the Xbox 360 and the Xbox are among the successful moves the company has had in the video game market. Another milestone, the company, made is acquiring Skype in 2011 to compete with other communication software such as Google's Voice and Apple's Facetime. The diversification strategies utilized by the company have also contributed to its widespread market share. For instance, investing in cloud computing software such as the Windows Azure platform has increased the brand's position and market share because consumers can create various computing infrastructures (Gregory, 2019). The company has continued to engage its employees and stakeholders in enjoying significant amounts of profits.
Mission
Microsoft's mission is to empower organizations and individuals worldwide in achieving more (Gregory, 2019). This empowerment of individuals and organizations is attained through the development of a variety of computing products.
Organizational Structure
The company's organizational structure can be defined as a product type divisional organizational structure. This is because the company utilizes a system containing divisions based on organizational outputs or the software's nature and hardware products. Besides the most dominant structural design: product type divisions, its organizational structure is also divided according to global corporate groups and geographic segments. Product type divisions involve the uses of output or products as the primary criterion for grouping personnel and the resources they need. For instance, the Intelligent Cloud products division was created as a self-contained division to enhance its product innovation capacity (Lombardo, 2018). Other product type divisions include personal computing, intelligent cloud, and the departments that address business and productivity processes.
Global corporate groups define the company's organizational structure based on th ...
Cyber security market 

The cyber security market is estimated to reach $269 billion by 2026, growing at a CAGR of 12.7%. In 2017, the enterprise security segment dominated the market. North America was the largest contributor to market revenue in 2017. The growing need for data protection and increasing cyber threats is driving market growth, while complex device security challenges and use of pirated solutions are hindering it. The healthcare industry is also increasingly adopting cyber security due to rising attacks.
Cyber security market 

The cyber security market is estimated to exceed $269 billion by 2026, growing at a CAGR of 12.7%. The enterprise segment currently dominates the market. North America contributes the most to market revenue. Increasing cyber threats and attacks are driving demand for cyber security solutions across many industries and regions. The healthcare industry remains vulnerable due to limited budgets, but adoption is expected to rise with greater awareness and affordable options. The Asia Pacific region is projected to experience the fastest growth.
Cyber security market 

The cyber security market is estimated to exceed $269 billion by 2026, growing at a CAGR of 12.7%. The enterprise segment currently dominates the market. North America contributes the most to market revenue. Increasing cyber threats and attacks are driving demand for cyber security solutions across many industries and regions. The healthcare industry remains vulnerable due to limited budgets, but adoption is expected to rise with greater awareness and affordable options. Asia-Pacific is projected to experience the fastest growth.
Jim kaskade biography (updated)

- Jim Kaskade is a passionate executive with 20 years of experience leading high-growth companies. Most recently, he served as CEO of Janrain, a digital identity security company, guiding it to profitability and exiting via acquisition by Akamai.
- He has experience leading teams and businesses of all sizes, from startups to $1B divisions of large corporations. He is skilled at business transformations, turnarounds, and hypergrowth.
- Prior to Janrain, he held leadership roles at several other technology companies, including CSC, Infochimps, SIOS, and others, where he successfully grew the businesses, some via acquisition.
Trend Micro Solutions Overview

A brief overview presentation of Trend Micro that includes our history, growth story, and financials. It also covers how Trend Micro’s artfully combines proven foresight, XGen™ security, and passionate people to enable us to deliver market leading solutions to our customers and partners alike.
The Trailblazing Cybersecurity Leaders to Watch in 2024 (1) (1).pdf

A distinguished executive in enterprise technology, cybersecurity, and services, Simon Chassar has an impressive track record spanning over two decades. Boasting international experience, Simon has been at the forefront of leading sales and business operations in the SaaS, software, hardware, and IT sectors.
Securing the C-Suite: Cybersecurity Perspectives from the Boardroom

The document summarizes the findings of a survey of over 700 C-suite executives from 29 countries and 18 industries regarding their perspectives on cybersecurity. Some key findings include: 75% of CxOs believe a comprehensive cybersecurity program is important; however, over half may be overstating the likelihood of a significant cybersecurity incident. Additionally, while CxOs acknowledge some risks, they understate risks from insiders and overstate risks from external threats. The C-suites were clustered into three groups based on their cybersecurity effectiveness: not prepared, progressing, and cybersecure. The cybersecure C-suites were more likely to have robust cybersecurity governance and collaboration.
Cyber security market 1

The global cyber security market is forecast to exceed $269.76 billion by 2026, growing at a CAGR of 13.1%. In 2017, the enterprise security segment dominated the market. North America was the largest market, led by the US. Growing cyber threats, BYOD trends, and demand from small businesses are driving market growth. However, use of pirated solutions and device security complexities may hinder the market. The healthcare industry is also increasingly adopting cyber security due to rising attacks.
Webinar - How to Become a Cyber-threat Intelligence Analyst

The document discusses how to become a cyber-threat intelligence analyst. It describes the role of an analyst in helping organizations understand vulnerabilities and prepare for potential threats. It outlines the skills needed such as technical expertise, analytical abilities, and experience with intelligence tools. Sample report structures and current job demand in the field are also summarized.
Ibm

IBM is an international technology company with subsidiaries around the world. The company's core values are dedication to client success, innovation that benefits both IBM and the world, and trust in all relationships. IBM's mission is to deliver business value to clients through integrated IT solutions while shifting to higher-value software and services. The company focuses on growth markets, analytics, industry solutions, and cloud/data center technologies. IBM has a global distribution strategy and targets markets for growth, analytics, cloud/data center solutions, and smarter planet initiatives.
Microsoft Diversification Strategy Final

Microsoft has diversified its business across various industries including software, hardware, online services and more. It reorganized into three divisions focused on platforms and services, business solutions, and entertainment/devices. This diversification strategy was in response to market changes and helped Microsoft expand beyond its core desktop software business into new growth areas as the IT industry evolved. Continued diversification will be important for Microsoft to adapt to future industry shifts.
The 10 Fastest Growing Cyber Security Companies of 2017

The 10 Fastest Growing Cyber Security Companies of 2017Insights success media and technology pvt ltd
- Cybersecurity spending has grown significantly over the past decade, from $3.5 billion in 2004 to an estimated $120 billion in 2017, driven largely by increasing cybercrime.
- Many large companies have significantly increased their cybersecurity budgets in response, including Bank of America which has an unlimited budget for cybersecurity, JPMorgan Chase which doubled its budget to $500 million, and Microsoft which invests over $1 billion annually.
- However, small and medium businesses are particularly vulnerable as they bear 72% of cyber attacks but often lack the resources of larger companies to implement robust cybersecurity programs. Highground Cyber aims to help small and mid-market CEOs protect their companies through comprehensive cybersecurity solutions.2009 Ingram Corp Overview

Ingram Micro is the world's largest technology distributor, providing products and services to customers in over 150 countries. In the first quarter of 2009, Ingram Micro saw worldwide sales decline 21% to $6.75 billion due to macroeconomic softness. However, the company improved working capital management and ended the quarter with over $1 billion in cash. Looking ahead, Ingram Micro is focused on competitive costs, higher margin businesses, and profitability.
Global Cybersecurity Market (2017 - 2022) 

The global cybersecurity market is expected to witness high adoption, owing to rapid digitalization, higher spending on information security, and the advent of 5G. Various industrial and commercial sectors are implementing cybersecurity solutions to safeguard their data. The market is anticipated to expand at a compound annual growth rate (CAGR) of 11.6% during the period of 2017 to 2022. Read More: https://www.researchonglobalmarkets.com/global-cybersecurity-market.html
Roadmap of Cyber-security from On-Prem to Cloud Journey - Trend Micro

The session theme is "Roadmap of Cyber-security from On-Prem to Cloud Journey".
The session focuses how security information and event management can help enterprises to collects data from the heterogeneous landscape to have incident response plans and have automation in the entire security operations framework.
The session will be handled by Mr. Kanchan Mallick, Regional Head for Eastern India,Nepal, Bhutan and Bangladesh, Trendmicro India Private Ltd.
Mr. Mallick has an experience of total 19 years in the IT Security, Information security domain, Cyber Security consulting field, especially in the areas of presales activities, Techno-marketing, Account sales activities, Channel sales & Product positioning and other managerial areas.
Women in Technology Leadership

Women in Technology Leadership Latest IT news In mid-March of last year, the World Health Organization officially declared the world was facing a pandemic, and countries rushed to enact measures to stem the spread. A popular measure to combat the pandemic was switching companies to remote work. However, with little time to make the transition, many companies had no time to enact proper security measures, leaving them vulnerable to a number of new security risks. One of the most common were attacks against the protocols used by employees to access corporate resources remotely. RDP is perhaps the most popular remote desktop protocol and is used to access Windows or servers. After the switch to remote work, bruteforce attacks against this protocol skyrocketed. In a bruteforce attack, attackers test different usernames and passwords until the correct combination is found-and they gain access to the corporate resources. Over the past year, while the total number of bruteforce attacks has ebbed and flowed, they have continued to increase when compared to pre-pandemic levels. Visit on varindia official site https://www.varindia.com/ to know more. According to Kaspersky’s telemetry, when the world went into lockdown in March 2020, the total number of bruteforce attacks against RDP jumped from 93.1 million worldwide in February 2020 to 277.4 million 2020 in March—a 197 percent increase. The numbers in India went from 1.3 million (1363953) in Feb 2020 to 3.3 million (3301848) in March 2020. From April 2020 onward, monthly attacks never dipped below 300 million, and they reached a new high of 409 million attacks worldwide in November 2020. The highest number of attacks 4.5 million (4586533) in India was recorded in July 2020. In February 2021—nearly one year from the start of the pandemic—there were 377.5 million brute-force attacks—a far cry from the 93.1 million witnessed at the beginning of 2020. India alone witnessed 9.04 million (9048791) attacks in Feb 2021.
The total number of attacks in India from Feb-Dec 2020 was around 37 million (37664893), while the total number of attacks recorded in India during Jan & Feb 2021 are around 15 million (15804209).
Data trends: Visualizing the global cloud industry in 2023

At Bessemer, we surveyed 405 cloud companies as a status check for the private cloud computing industry, tracking their financial performance, artificial intelligence (AI) adoption, leadership priorities, and biggest challenges.
We aimed to answer the question: Where does the cloud industry stand in 2023, the year where pressures to drive profitable growth intensified and AI eclipsed every business conversation and captivated the world?
According to Bessemer Partner Byron Deeter, the global cloud industry is stronger than ever. “How do you think AI is delivered? Tens of thousands of GPUs working together in the cloud,” said Byron. “Our 2023 Cloud 100 applicants have never been stronger — proof that AI is the next horizon of cloud.”
While our Cloud 100 Benchmarks act as an industry yardstick for best-in-class private cloud performance, this survey widens the aperture by more than 4x to assess performance of private cloud companies of every stage and scale.
In 35 charts, we visualize the quantitative and qualitative trends moving the private cloud industry across 23 countries and 114 cities.
Five cloud industry insights for 2023
The top five cloud companies voted most likely to IPO next are Stripe, Databricks, Canva, Klavyio, and Snyk.
San Francisco is the cloud industry epicenter in terms of headquarters and hiring: 52% of cloud companies reside in California, with 21% of companies headquartered in San Francisco.
AI has already taken over SaaS: By the end of the year, 86% of cloud companies surveyed will have an AI-driven feature.
Cloud leaders ranked setting competitive differentiation in the product and go-to-market strategy as the biggest challenge facing their companies. Driving profitable growth was ranked as the leading objective whereas fundraising was ranked one of the lowest priorities for 2023.
Cloud companies are still well funded: A majority of surveyed cloud companies have raised over $100 million or more in total funding. More than half of the surveyed companies have less than $50 million on the balance sheet, whereas almost a third have $100 million or more. Of the cloud companies that have raised $1 billion or more, over 70% have more than $300 million on the balance sheet.
Read the full report: https://www.bvp.com/atlas/data-trends-visualizing-the-global-cloud-industry-in-2023
Similar to Military Cyber Security Market 2019-2029 (20)
Epebinu 2CyberSecurity On Microsoft BreachingFirst Draft Of 

Epebinu 2CyberSecurity On Microsoft BreachingFirst Draft Of
The Trailblazing Cybersecurity Leaders to Watch in 2024 (1) (1).pdf

The Trailblazing Cybersecurity Leaders to Watch in 2024 (1) (1).pdf
Securing the C-Suite: Cybersecurity Perspectives from the Boardroom

Securing the C-Suite: Cybersecurity Perspectives from the Boardroom
Webinar - How to Become a Cyber-threat Intelligence Analyst

Webinar - How to Become a Cyber-threat Intelligence Analyst
The 10 Fastest Growing Cyber Security Companies of 2017

The 10 Fastest Growing Cyber Security Companies of 2017
Roadmap of Cyber-security from On-Prem to Cloud Journey - Trend Micro

Roadmap of Cyber-security from On-Prem to Cloud Journey - Trend Micro
Data trends: Visualizing the global cloud industry in 2023

Data trends: Visualizing the global cloud industry in 2023
Recently uploaded
Company Valuation webinar series - Tuesday, 4 June 2024

This session provided an update as to the latest valuation data in the UK and then delved into a discussion on the upcoming election and the impacts on valuation. We finished, as always with a Q&A
2022 Vintage Roman Numerals Men Rings

Discover timeless style with the 2022 Vintage Roman Numerals Men's Ring. Crafted from premium stainless steel, this 6mm wide ring embodies elegance and durability. Perfect as a gift, it seamlessly blends classic Roman numeral detailing with modern sophistication, making it an ideal accessory for any occasion.
https://rb.gy/usj1a2
The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...

The Radar reflects input from APCO’s teams located around the world. It distils a host of interconnected events and trends into insights to inform operational and strategic decisions. Issues covered in this edition include:
Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...

Explore the fascinating world of the Gemini Zodiac Sign. Discover the unique personality traits, key dates, and horoscope insights of Gemini individuals. Learn how their sociable, communicative nature and boundless curiosity make them the dynamic explorers of the zodiac. Dive into the duality of the Gemini sign and understand their intellectual and adventurous spirit.
Dpboss Matka Guessing Satta Matta Matka Kalyan Chart Satta Matka

Dpboss Matka Guessing Satta Matta Matka Kalyan Chart Satta Matka➒➌➎➏➑➐➋➑➐➐Dpboss Matka Guessing Satta Matka Kalyan Chart Indian Matka
Dpboss Matka Guessing Satta Matta Matka Kalyan Chart Indian Matka Indian satta Matka Dpboss Matka Kalyan Chart Matka Boss otg matka Guessing Satta Creative Web Design Company in Singapore

At Techbox Square, in Singapore, we're not just creative web designers and developers, we're the driving force behind your brand identity. Contact us today.
Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

CALL 8867766396 SATTA MATKA | DPBOSS | KALYAN MAIN BAZAR | FAST MATKA | DPBOSS GUESSING | TARA MATKA | KALYAN CHART | MATKA BOSS
Understanding User Needs and Satisfying Them

https://www.productmanagementtoday.com/frs/26903918/understanding-user-needs-and-satisfying-them
We know we want to create products which our customers find to be valuable. Whether we label it as customer-centric or product-led depends on how long we've been doing product management. There are three challenges we face when doing this. The obvious challenge is figuring out what our users need; the non-obvious challenges are in creating a shared understanding of those needs and in sensing if what we're doing is meeting those needs.
In this webinar, we won't focus on the research methods for discovering user-needs. We will focus on synthesis of the needs we discover, communication and alignment tools, and how we operationalize addressing those needs.
Industry expert Scott Sehlhorst will:
• Introduce a taxonomy for user goals with real world examples
• Present the Onion Diagram, a tool for contextualizing task-level goals
• Illustrate how customer journey maps capture activity-level and task-level goals
• Demonstrate the best approach to selection and prioritization of user-goals to address
• Highlight the crucial benchmarks, observable changes, in ensuring fulfillment of customer needs
2024-6-01-IMPACTSilver-Corp-Presentation.pdf

IMPACT Silver is a pure silver zinc producer with over $260 million in revenue since 2008 and a large 100% owned 210km Mexico land package - 2024 catalysts includes new 14% grade zinc Plomosas mine and 20,000m of fully funded exploration drilling.
Easily Verify Compliance and Security with Binance KYC

Use our simple KYC verification guide to make sure your Binance account is safe and compliant. Discover the fundamentals, appreciate the significance of KYC, and trade on one of the biggest cryptocurrency exchanges with confidence.
Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...

Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Schedule Unveiled
Brian Fitzsimmons on the Business Strategy and Content Flywheel of Barstool S...

On episode 272 of the Digital and Social Media Sports Podcast, Neil chatted with Brian Fitzsimmons, Director of Licensing and Business Development for Barstool Sports.
What follows is a collection of snippets from the podcast. To hear the full interview and more, check out the podcast on all podcast platforms and at www.dsmsports.net
Structural Design Process: Step-by-Step Guide for Buildings

The structural design process is explained: Follow our step-by-step guide to understand building design intricacies and ensure structural integrity. Learn how to build wonderful buildings with the help of our detailed information. Learn how to create structures with durability and reliability and also gain insights on ways of managing structures.
Zodiac Signs and Food Preferences_ What Your Sign Says About Your Taste

Know what your zodiac sign says about your taste in food! Explore how the 12 zodiac signs influence your culinary preferences with insights from MyPandit. Dive into astrology and flavors!
Industrial Tech SW: Category Renewal and Creation

Every industrial revolution has created a new set of categories and a new set of players.
Multiple new technologies have emerged, but Samsara and C3.ai are only two companies which have gone public so far.
Manufacturing startups constitute the largest pipeline share of unicorns and IPO candidates in the SF Bay Area, and software startups dominate in Germany.
-- June 2024 is National Volunteer Month --

Check out our June display of books on voluntary organisations
Recently uploaded (20)
Company Valuation webinar series - Tuesday, 4 June 2024

Company Valuation webinar series - Tuesday, 4 June 2024
The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...

The APCO Geopolitical Radar - Q3 2024 The Global Operating Environment for Bu...
Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...

Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...
Dpboss Matka Guessing Satta Matta Matka Kalyan Chart Satta Matka

Dpboss Matka Guessing Satta Matta Matka Kalyan Chart Satta Matka
Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...
Easily Verify Compliance and Security with Binance KYC

Easily Verify Compliance and Security with Binance KYC
Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...

Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...
Brian Fitzsimmons on the Business Strategy and Content Flywheel of Barstool S...

Brian Fitzsimmons on the Business Strategy and Content Flywheel of Barstool S...
Structural Design Process: Step-by-Step Guide for Buildings

Structural Design Process: Step-by-Step Guide for Buildings
Zodiac Signs and Food Preferences_ What Your Sign Says About Your Taste

Zodiac Signs and Food Preferences_ What Your Sign Says About Your Taste
Military Cyber Security Market 2019-2029
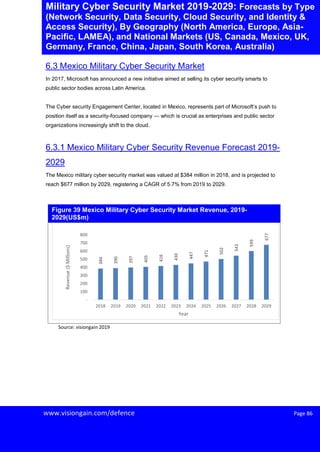
- 1. Page 86Www.visiongain.com/defence Page 86 Military Cyber Security Market 2019-2029: Forecasts by Type (Network Security, Data Security, Cloud Security, and Identity & Access Security), By Geography (North America, Europe, Asia- Pacific, LAMEA), and National Markets (US, Canada, Mexico, UK, Germany, France, China, Japan, South Korea, Australia) 6.3 Mexico Military Cyber Security Market In 2017, Microsoft has announced a new initiative aimed at selling its cyber security smarts to public sector bodies across Latin America. The Cyber security Engagement Center, located in Mexico, represents part of Microsoft’s push to position itself as a security-focused company — which is crucial as enterprises and public sector organizations increasingly shift to the cloud. 6.3.1 Mexico Military Cyber Security Revenue Forecast 2019- 2029 The Mexico military cyber security market was valued at $384 million in 2018, and is projected to reach $677 million by 2029, registering a CAGR of 5.7% from 2019 to 2029. Figure 39 Mexico Military Cyber Security Market Revenue, 2019- 2029(US$m) Source: visiongain 2019 384 390 397 405 416 430 447 471 502 543 599 677 - 100 200 300 400 500 600 700 800 2018 2019 2020 2021 2022 2023 2024 2025 2026 2027 2028 2029 Revenue($Millions) Year
- 2. Page 138Www.visiongain.com/defence Page 138 Military Cyber Security Market 2019-2029: Forecasts by Type (Network Security, Data Security, Cloud Security, and Identity & Access Security), By Geography (North America, Europe, Asia- Pacific, LAMEA), and National Markets (US, Canada, Mexico, UK, Germany, France, China, Japan, South Korea, Australia) 7.4 IBM Corporation 7.4.1 Company overview International Business Machines (IBM) Corporation is one of the leading and most established companies when it comes to the IT sector. The company has produced many innovations and has gifted the IT sector in beautiful ways from hardware, middleware and software along with consulting services as well. IBM is a major player in the IT and cyber security sector as well. Being in the cyber security business for more than 40 years, IBM has been offering detailed and effective solutions via its rich product AD services portfolio in the cyber security department. This has allowed IBM to give effective enterprise IT security solutions throughout the course of their long history. Snapshot Description Year of Inception 1911 Key Executives Virginia M Rometty (Chairman, President & Chief Executive Officer) James J Kavanaugh (Chief Financial Officer & Senior Vice President) Primary Business Computer Integrated Systems Geographical Presence North America, Latin America, Asia-Pacific, Europe, and Middle East & Africa Overall Financial Status (Operating Revenue in million) • 2018: 79,591 • 2017: 79,139 • 2016: 79,919 Source: Company website 7.4.2 IBM Corporation Cyber Security Overview Despite declining revenues across the company, IBM has performed strongly in the cyber security market. This has been partly down to IBM’s strengths in cloud security and security analytics businesses. IBM revenue in the cyber security market totalled approximately $1439m, resulting in a market share of 1.8%. IBM’s strong performance in the cyber security software market helps to mitigate poor performance in traditional markets like enterprise software and hardware, a trend across wholesale IT companies involved in cyber security. Table 45 IBM Corporation Company Snapshot