The document discusses ethical considerations regarding the unauthorized practice of law, particularly focusing on issues of metadata, cloud computing, and social media in legal practice. It outlines potential risks associated with electronic communications that may inadvertently disclose confidential information and highlights the responsibilities of attorneys in managing these risks. Additionally, it examines the evolving landscape of legal ethics in relation to technology and the implications for client confidentiality and attorney advertising.

![35
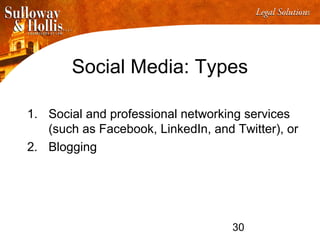
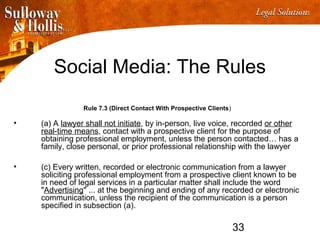
Social Media: The Rules
Rule 7.4 (Communications of Fields of Practice)
• A lawyer may communicate the fact that the lawyer does or does
not practice in particular fields of law.
• A lawyer shall not state or imply that the lawyer is a specialist
except as follows:
– ["patent attorney" "proctor in admiralty“] or
– a lawyer who is certified as a specialist in a particular field of law
by an organization that has been accredited by the American
Bar Association may hold himself or herself out as a specialist
certified by such organization.
• Can state concentration or limitation of practice](https://image.slidesharecdn.com/kmo-pficlepresentationfirstamericanpptc0818829-2xa5f95-150201165121-conversion-gate02/85/Look-Before-You-Leap-Unauthorized-Practice-of-the-Law-Supervision-of-Non-Lawyer-Assistants-and-Ethical-Issues-in-the-Electronic-Age-35-320.jpg)
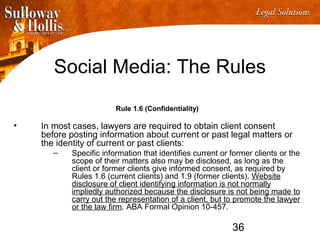
![38
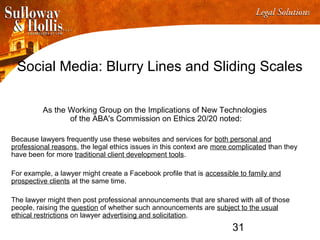
Social Media:
Any rules implicated by the following (real) Facebook posts
on a law firm’s Facebook page ?
Law Tip #38: "Jail blows and the food sucks." [Redacted law firm name’s] client
Law Tip #31:
When your bond conditions include "no possession of weapons" that includes a
handgun
Law Tip #29:
Try not to make your drug ring too successful or it will be charged as organized
crime which is just as bad as it sounds.
Law Tip #25:
Offering your prescription (even though they may very well need it) is Attempted
Distribution. Giving your prescription drug (even without payment) is Distribution.
Forcing them to take it with a gun to their head is a whole other ballpark. Don't do
any of the above
Law Tip #22: Don't talk to police. They are not your friend](https://image.slidesharecdn.com/kmo-pficlepresentationfirstamericanpptc0818829-2xa5f95-150201165121-conversion-gate02/85/Look-Before-You-Leap-Unauthorized-Practice-of-the-Law-Supervision-of-Non-Lawyer-Assistants-and-Ethical-Issues-in-the-Electronic-Age-38-320.jpg)
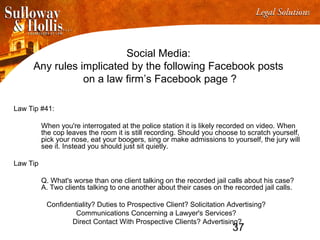
![42
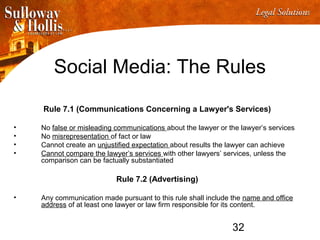
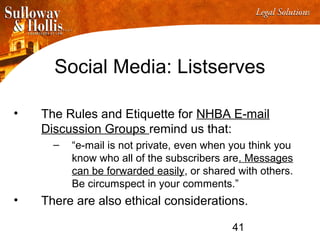
Social Media: Listserves
• Oregon State Bar Formal Opinion No. 2011-184 (March 2011)
– Framing a question as a hypothetical is not a perfect solution,
however. Lawyers faces a significant risk of violating [Rule] 1.6
when posing hypothetical questions if the facts provided permit
persons outside the lawyer’s firm to determine the client’s
identity.
– Where the facts are so unique or where other circumstances
might reveal the identity of the consulting lawyer’s client even
without the client being named, the lawyer must first obtain the
client’s informed consent for the disclosures.
– Obvious advice? Sure, but regular readers of the NHBA Real
Property Law Section listserv see how some of these messages
come to the line.](https://image.slidesharecdn.com/kmo-pficlepresentationfirstamericanpptc0818829-2xa5f95-150201165121-conversion-gate02/85/Look-Before-You-Leap-Unauthorized-Practice-of-the-Law-Supervision-of-Non-Lawyer-Assistants-and-Ethical-Issues-in-the-Electronic-Age-42-320.jpg)