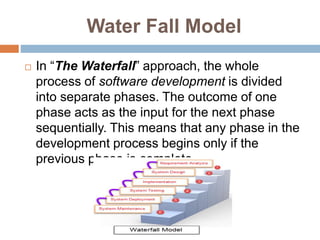
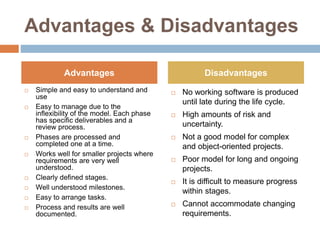
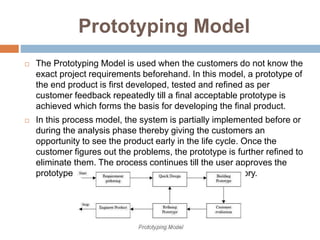
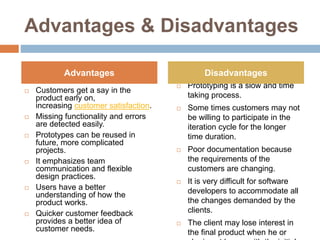
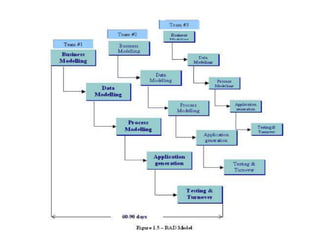
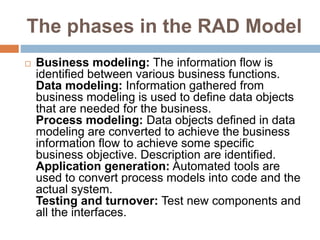
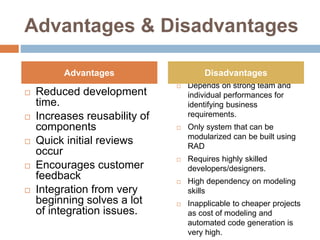
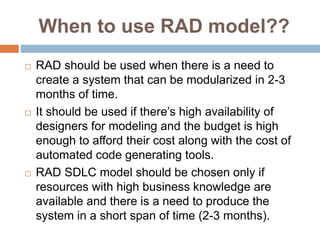
The document discusses three software development process models: the Waterfall model, Prototyping model, and Rapid Application Development (RAD) model. The Waterfall model involves dividing the development process into separate sequential phases. The Prototyping model involves iteratively developing prototypes based on customer feedback. The RAD model involves developing components in parallel on a time-boxed basis and assembling them into a working prototype.