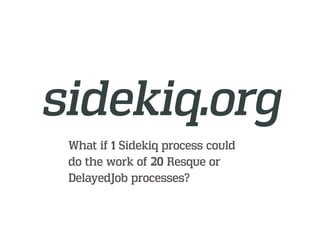
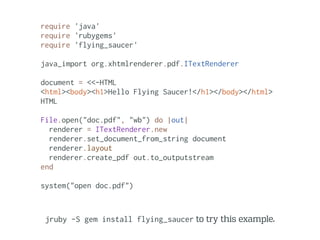
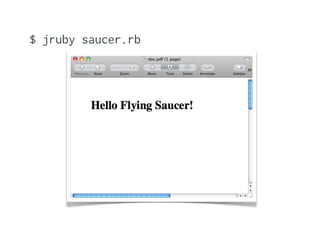
This document discusses using JRuby to run Ruby code on the Java Virtual Machine (JVM). Some key points:
- JRuby runs nearly all pure Ruby code and 92% of the Ruby spec suite by compiling Ruby code to JVM bytecode.
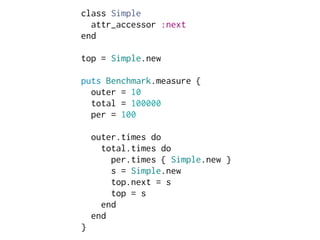
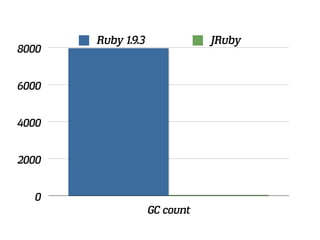
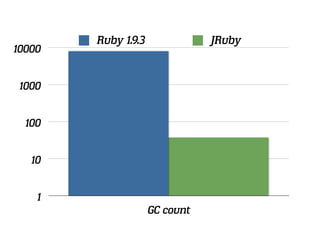
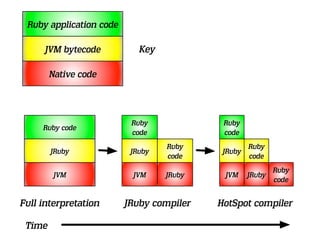
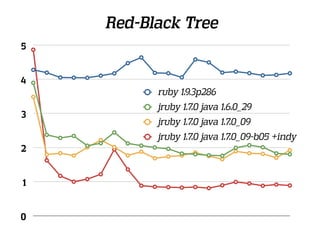
- Performance of JRuby has improved significantly with Java 7 and the HotSpot JIT compiler. Benchmarks show a 3-4x speedup over MRI Ruby for some algorithms.
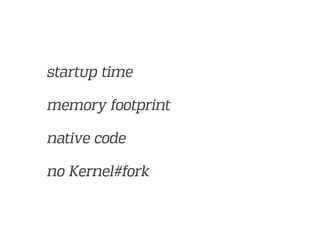
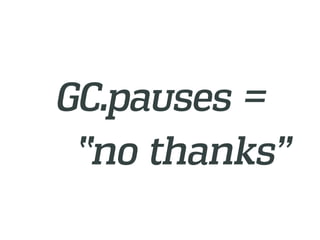
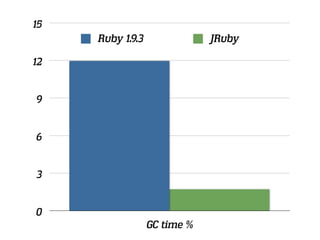
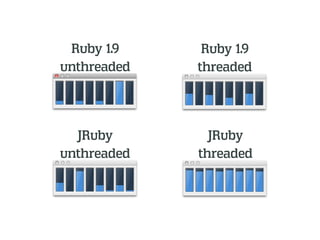
- Using the JVM gives JRuby features like real threads, memory management without garbage collection pauses, and the ability to directly call Java libraries from Ruby.
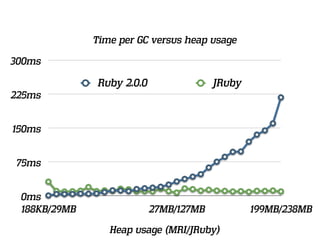
- The JRuby compiler compiles Ruby code to JVM bytecode which is further optimized by the HotSpot












![# call
p[x]](https://image.slidesharecdn.com/boulderruby20121030-121030233358-phpapp02/85/JRuby-Boulder-Ruby-32-320.jpg)

![fizzbuzz = -> k { -> f { -> f { -> x { f[-> y { x[x][y] }] }[-> x {
f[-> y { x[x][y] }] }] }[-> f { -> l { -> x { -> g { -> b { b }[-> p {
p[-> x { -> y { x } } ] }[l]][x][-> y { g[f[-> l { -> p { p[-> x { ->
y { y } } ] }[-> p { p[-> x { -> y { y } } ] }[l]] }[l]][x][g]][-> l {
-> p { p[-> x { -> y { x } } ] }[-> p { p[-> x { -> y { y } } ] }[l]]
}[l]][y] }] } } } }][k][-> x { -> y { -> f { f[x][y] } } }[-> x { -> y
{ x } }][-> x { -> y { x } }]][-> l { -> x { -> l { -> x { -> x { -> y
{ -> f { f[x][y] } } }[-> x { -> y { y } }][-> x { -> y { -> f {
f[x][y] } } }[x][l]] } }[l][f[x]] } }] } }[-> f { -> x { f[-> y {
x[x][y] }] }[-> x { f[-> y { x[x][y] }] }] }[-> f { -> m { -> n { -> b
{ b }[-> m { -> n { -> n { n[-> x { -> x { -> y { y } } }][-> x { -> y
{ x } }] }[-> m { -> n { n[-> n { -> f { -> x { n[-> g { -> h {
h[g[f]] } }][-> y { x }][-> y { y }] } } }][m] } }[m][n]] }
}[m][n]][-> x { -> l { -> x { -> x { -> y { -> f { f[x][y] } } }[-> x
{ -> y { y } }][-> x { -> y { -> f { f[x][y] } } }[x][l]] } }[f[-> n {
-> p { -> x { p[n[p][x]] } } }[m]][n]][m][x] }][-> x { -> y { -> f {
f[x][y] } } }[-> x { -> y { x } }][-> x { -> y { x } }]] } } }][-> p {
-> x { p[x] } }][-> p { -> x {p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[
p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[
p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[p[
p[p[p[p[p[p[p[p[p[p[x]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]
]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]]} }]][-> n { -> b {
b }[-> n { n[-> x { -> x { -> y { y } } }][-> x { -> y { x } }] }[-> f
{ -> x { f[-> y { x[x][y] }] }[-> x { f[-> y { x[x][y] }] }] }[-> f {
-> m { -> n { -> b { b }[-> m { -> n { -> n { n[-> x { -> x { -> y { y
} } }][-> x { -> y { x } }] }[-> m { -> n { n[-> n { -> f { -> x {
n[-> g { -> h { h[g[f]] } }][-> y { x }][-> y { y }] } } }][m] }](https://image.slidesharecdn.com/boulderruby20121030-121030233358-phpapp02/85/JRuby-Boulder-Ruby-35-320.jpg)

![INVOKEDYNAMIC
[bootstrapMethod]
bootstrapMethod():
Call Site
CallSite (once)
target
Method
Handle](https://image.slidesharecdn.com/boulderruby20121030-121030233358-phpapp02/85/JRuby-Boulder-Ruby-37-320.jpg)
![LAMBDA
p[x]](https://image.slidesharecdn.com/boulderruby20121030-121030233358-phpapp02/85/JRuby-Boulder-Ruby-39-320.jpg)

![import org.jruby.embed.ScriptingContainer;
public class EmbedJRuby {
public static void main(String[] args) {
ScriptingContainer container = new ScriptingContainer();
container.runScriptlet("puts 'Hello from Ruby'");
}
}
(defn -main
"Call JRuby!"
[& args]
(doto (org.jruby.embed.ScriptingContainer.)
(.runScriptlet "puts 'Hello from Ruby!'")))](https://image.slidesharecdn.com/boulderruby20121030-121030233358-phpapp02/85/JRuby-Boulder-Ruby-50-320.jpg)

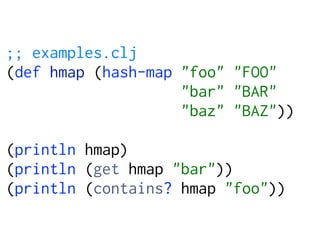
![# ruby
Java::clojure.main.main(["./examples.clj"])](https://image.slidesharecdn.com/boulderruby20121030-121030233358-phpapp02/85/JRuby-Boulder-Ruby-53-320.jpg)