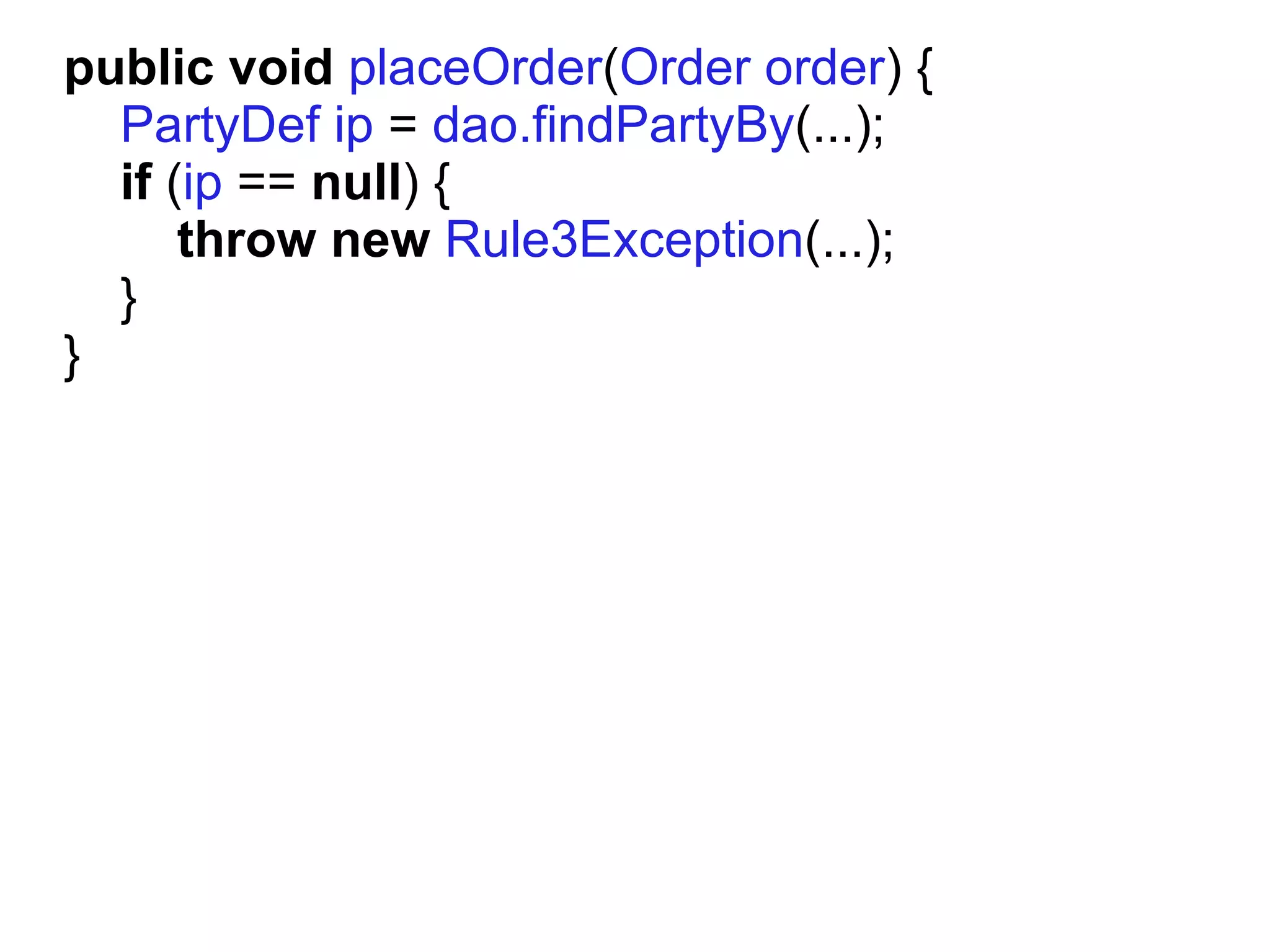
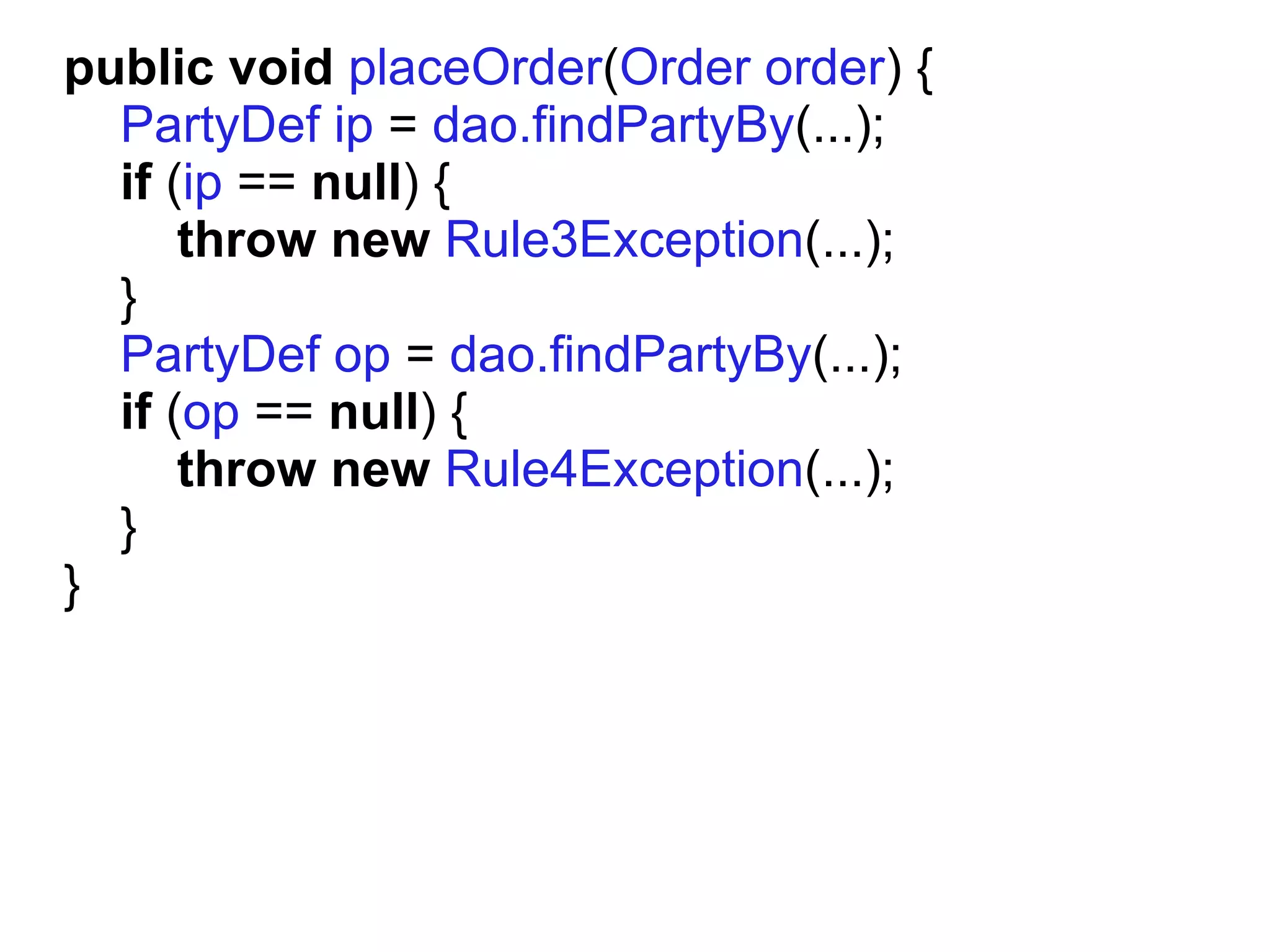
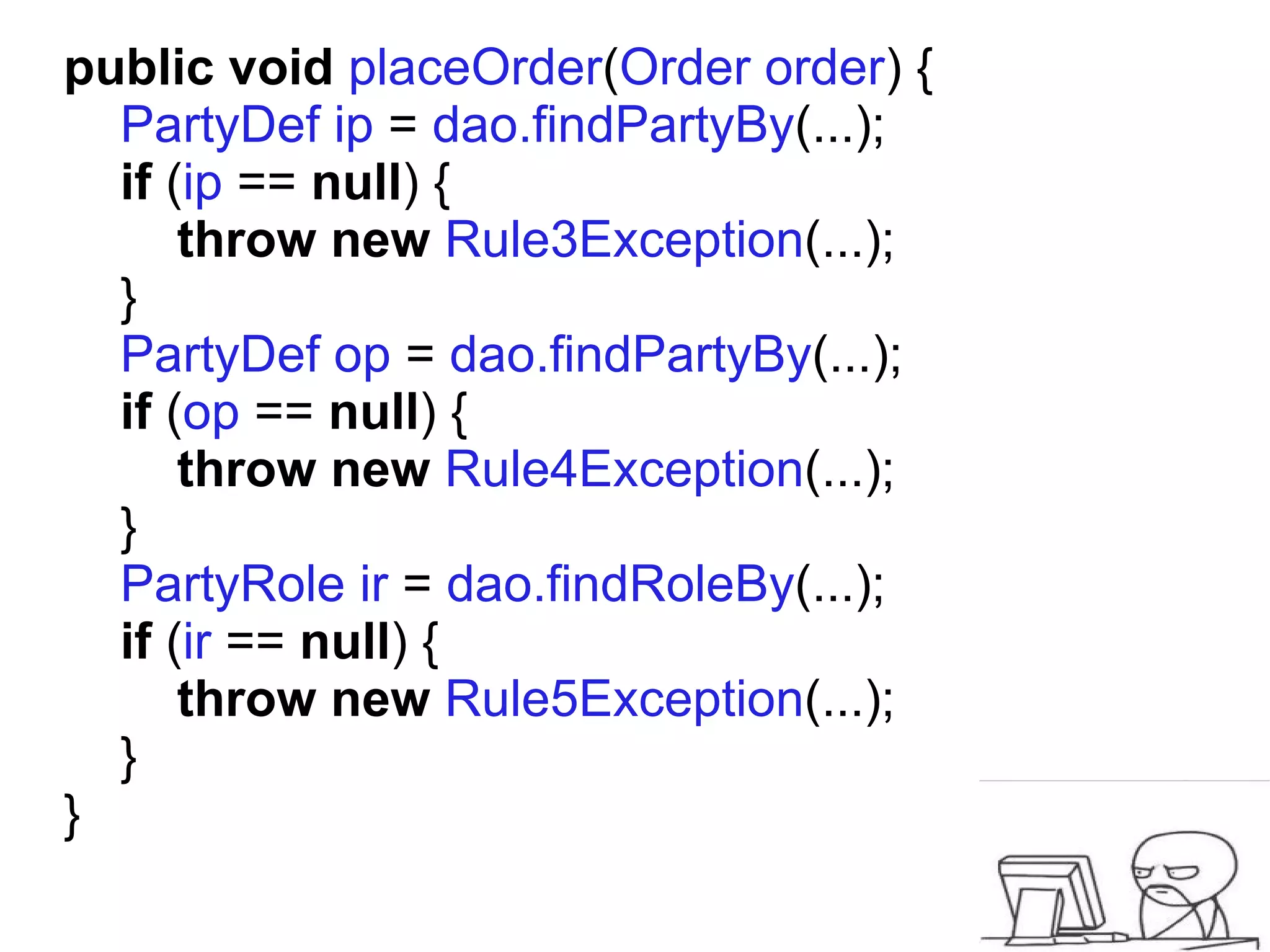
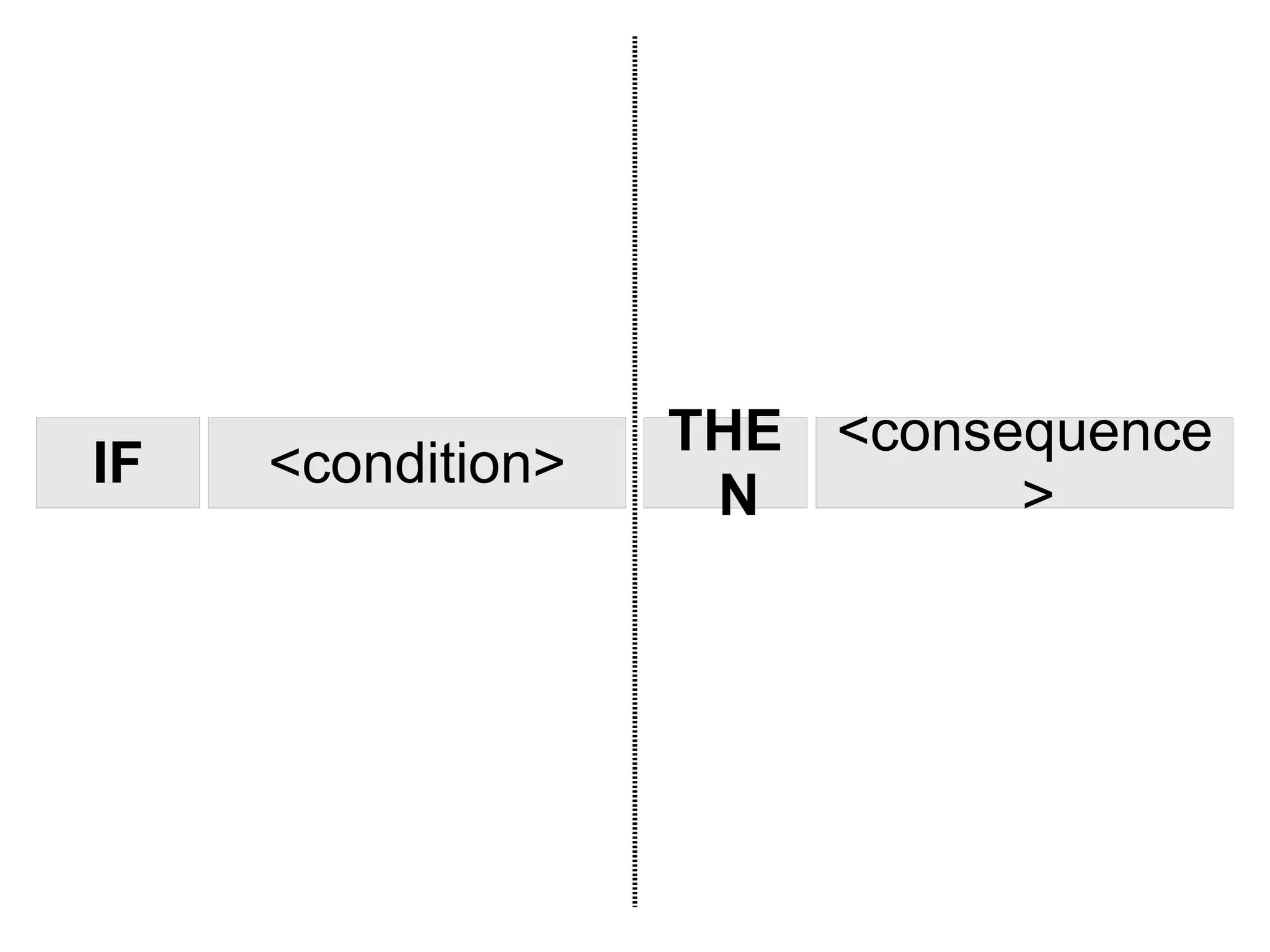
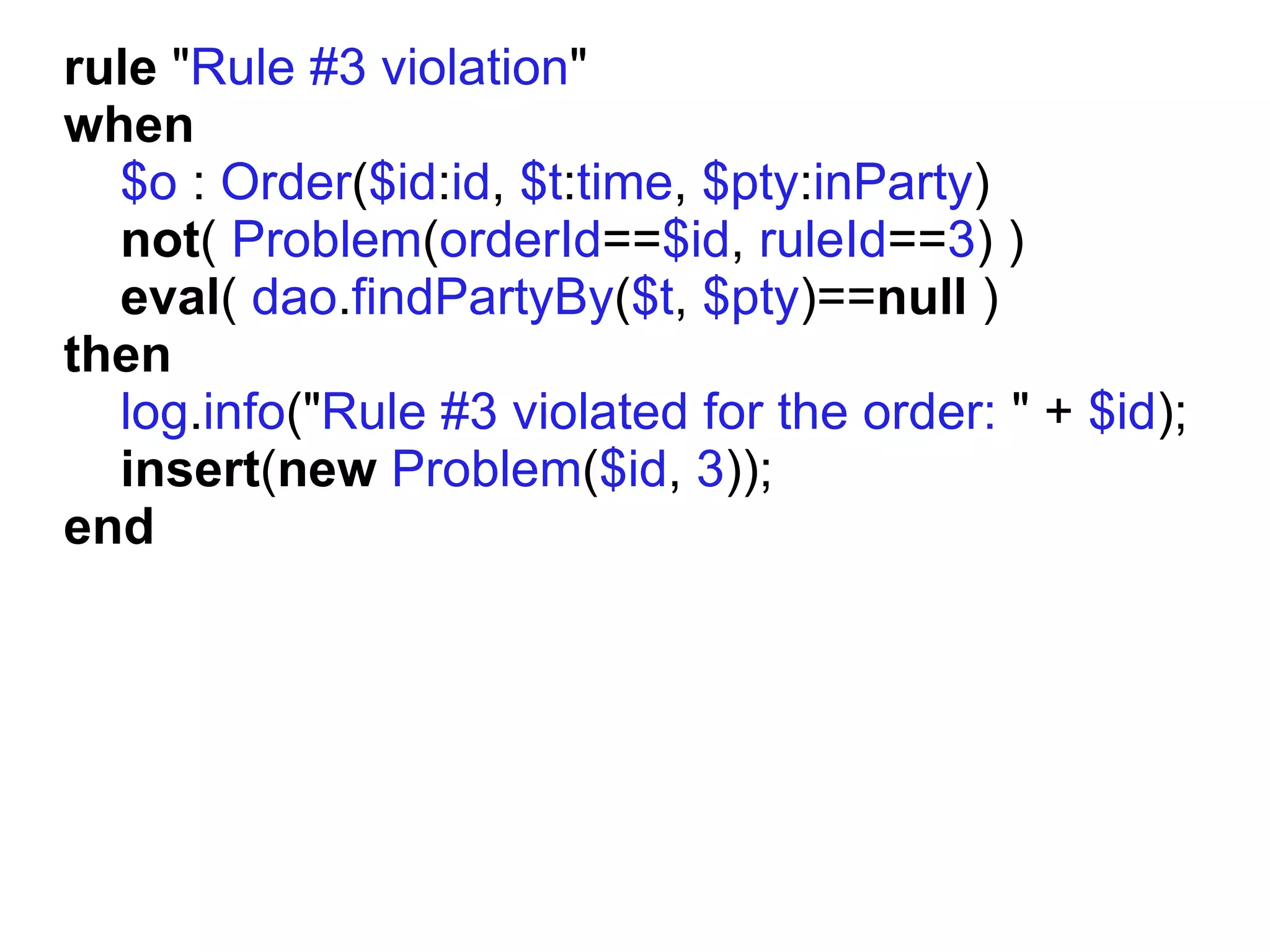
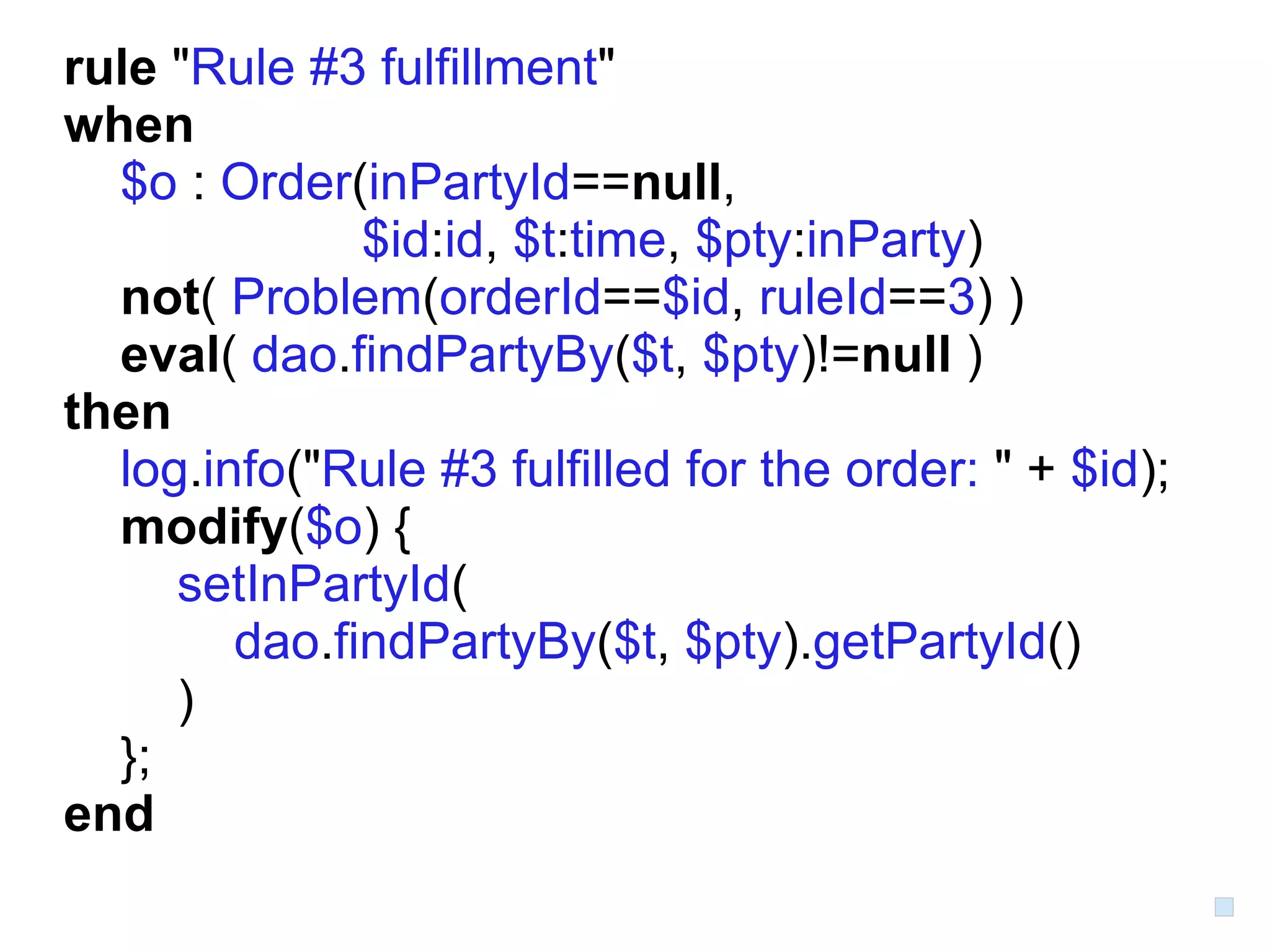
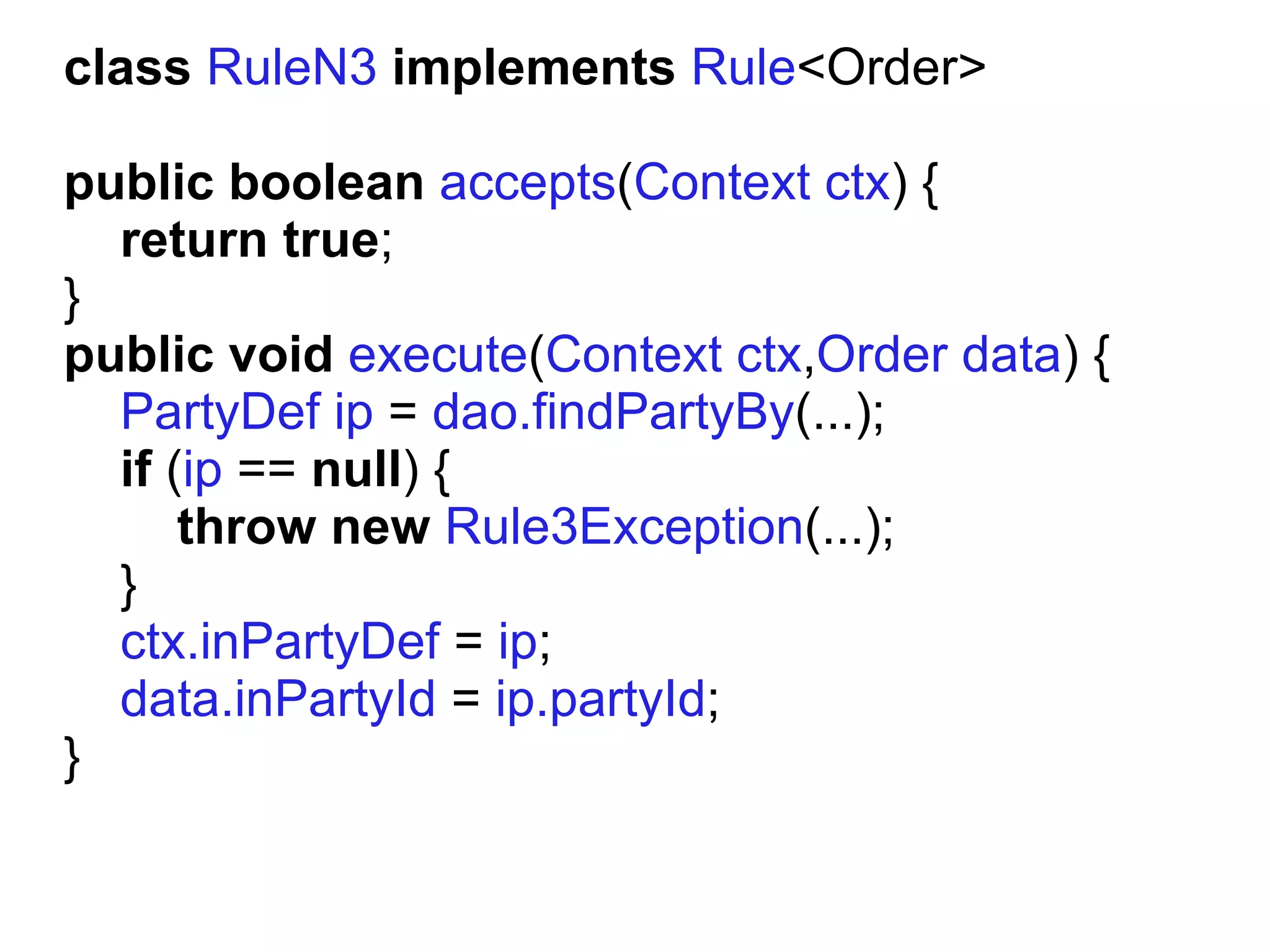
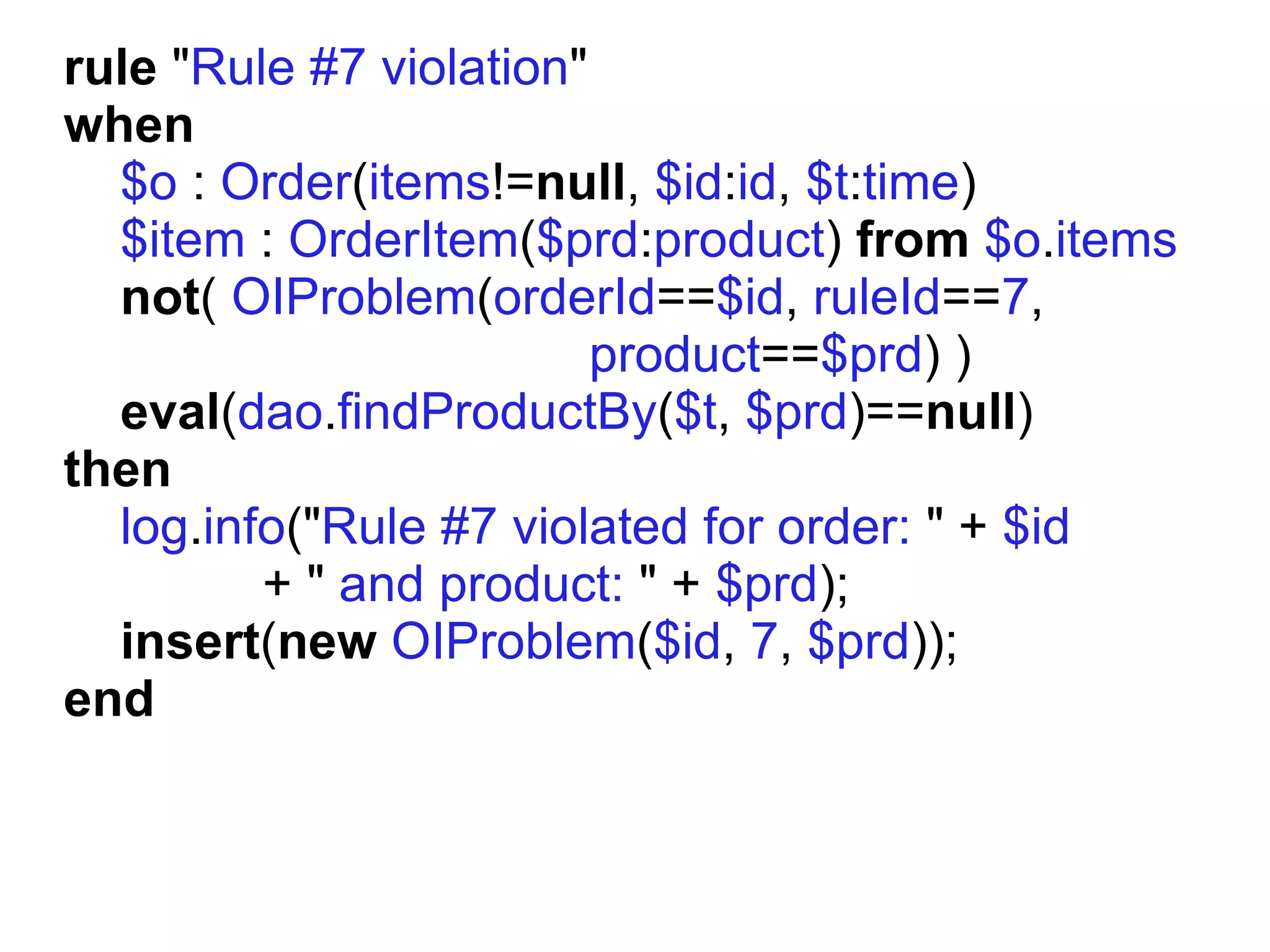
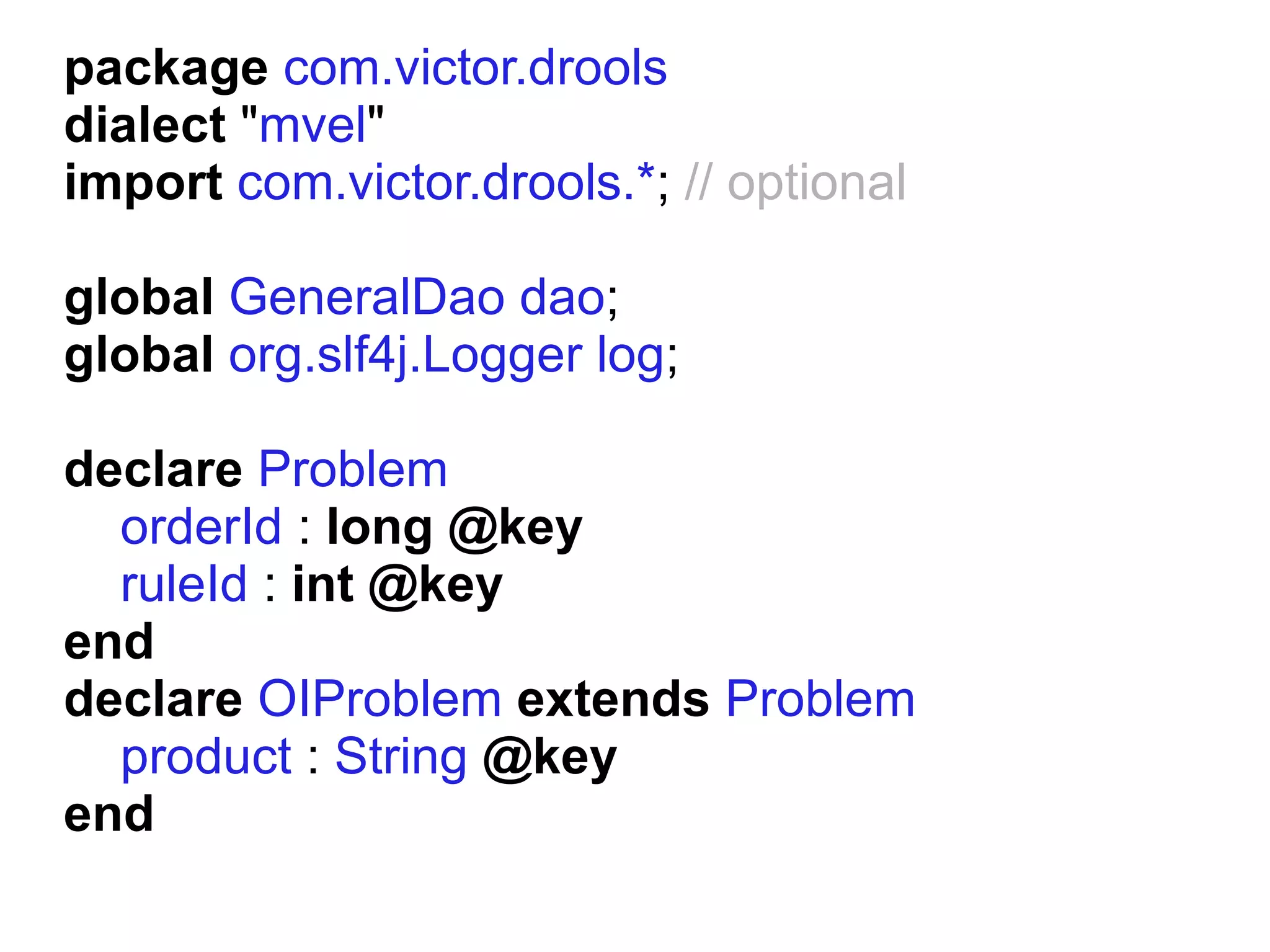
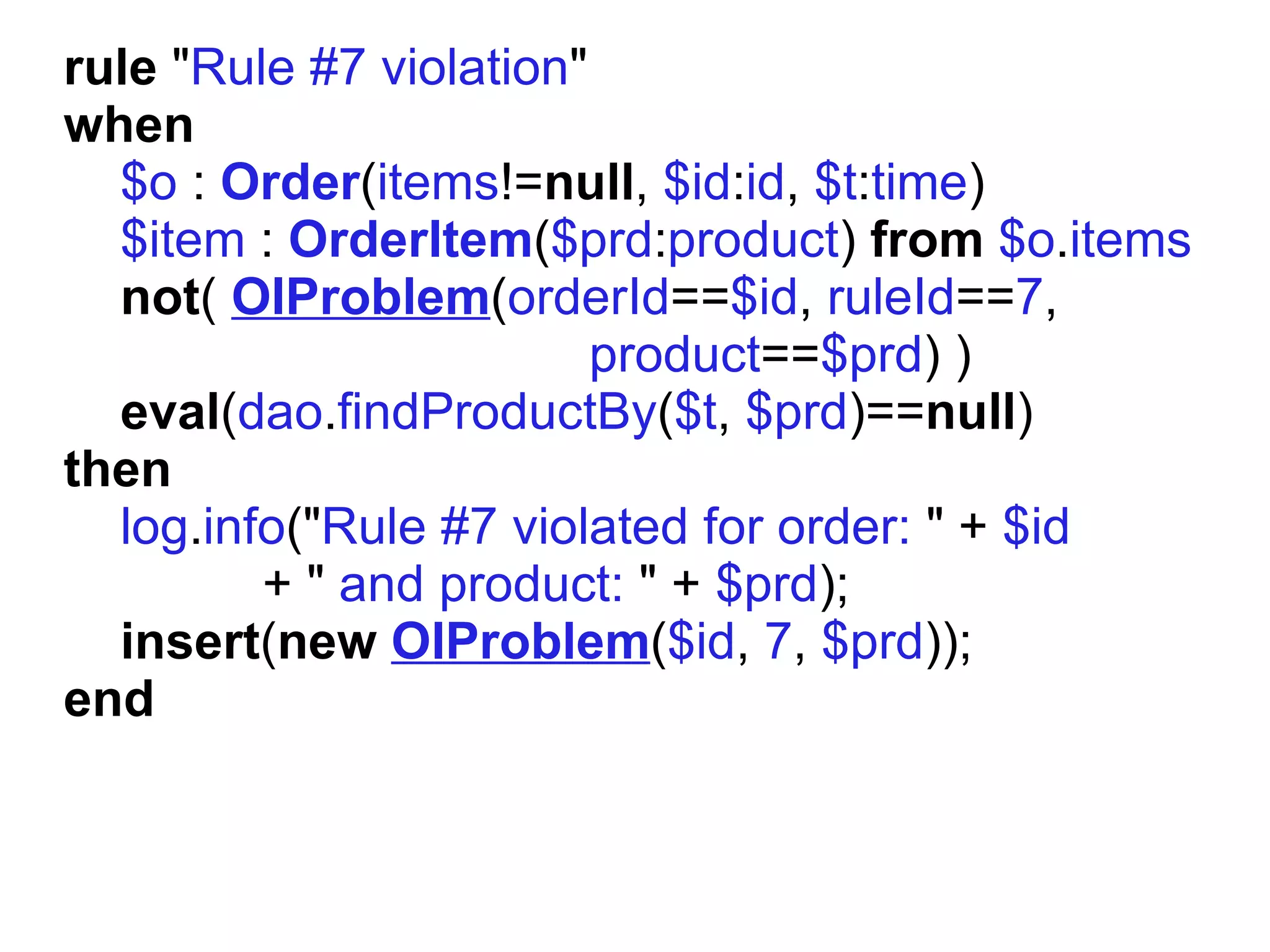
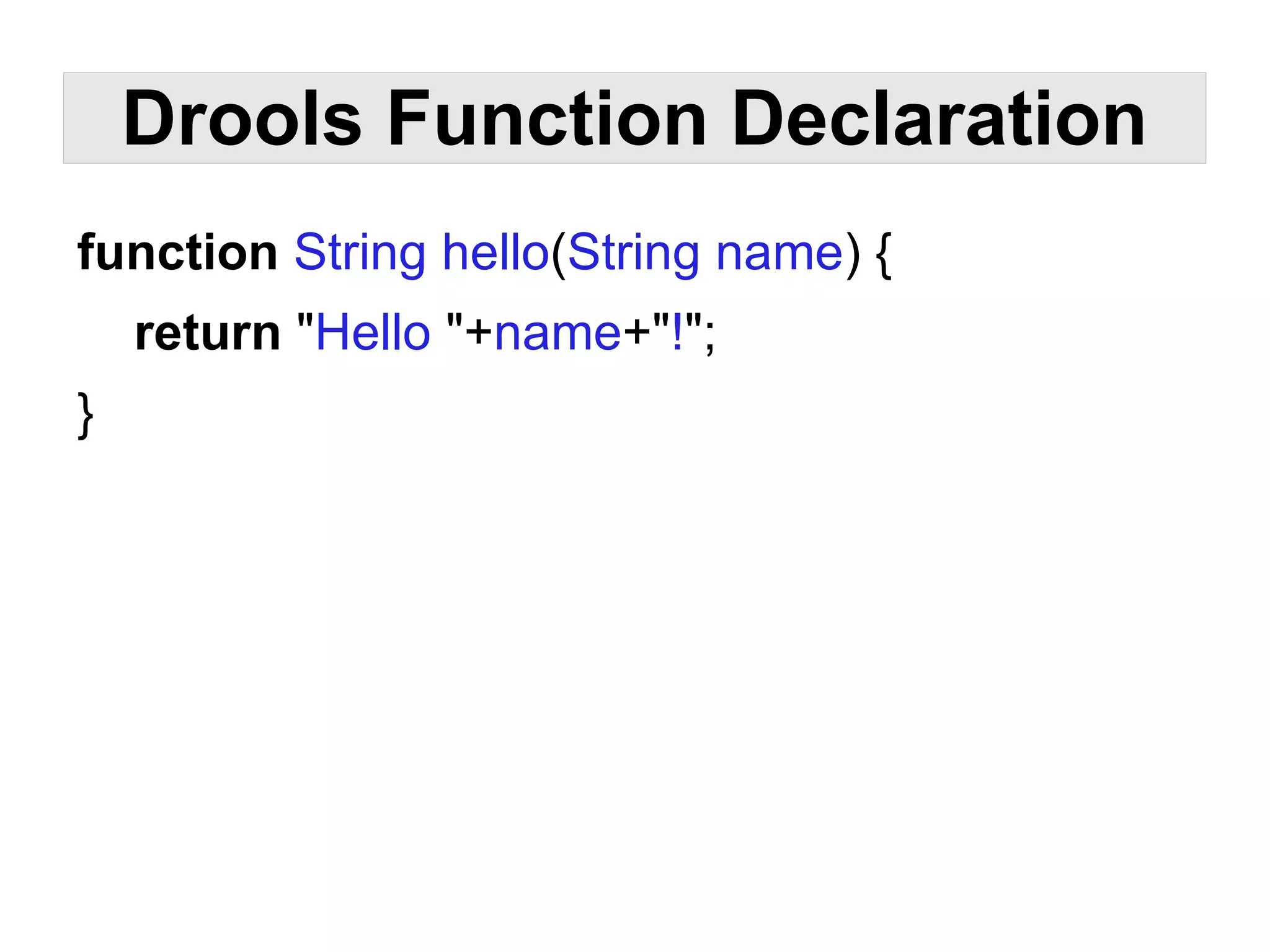
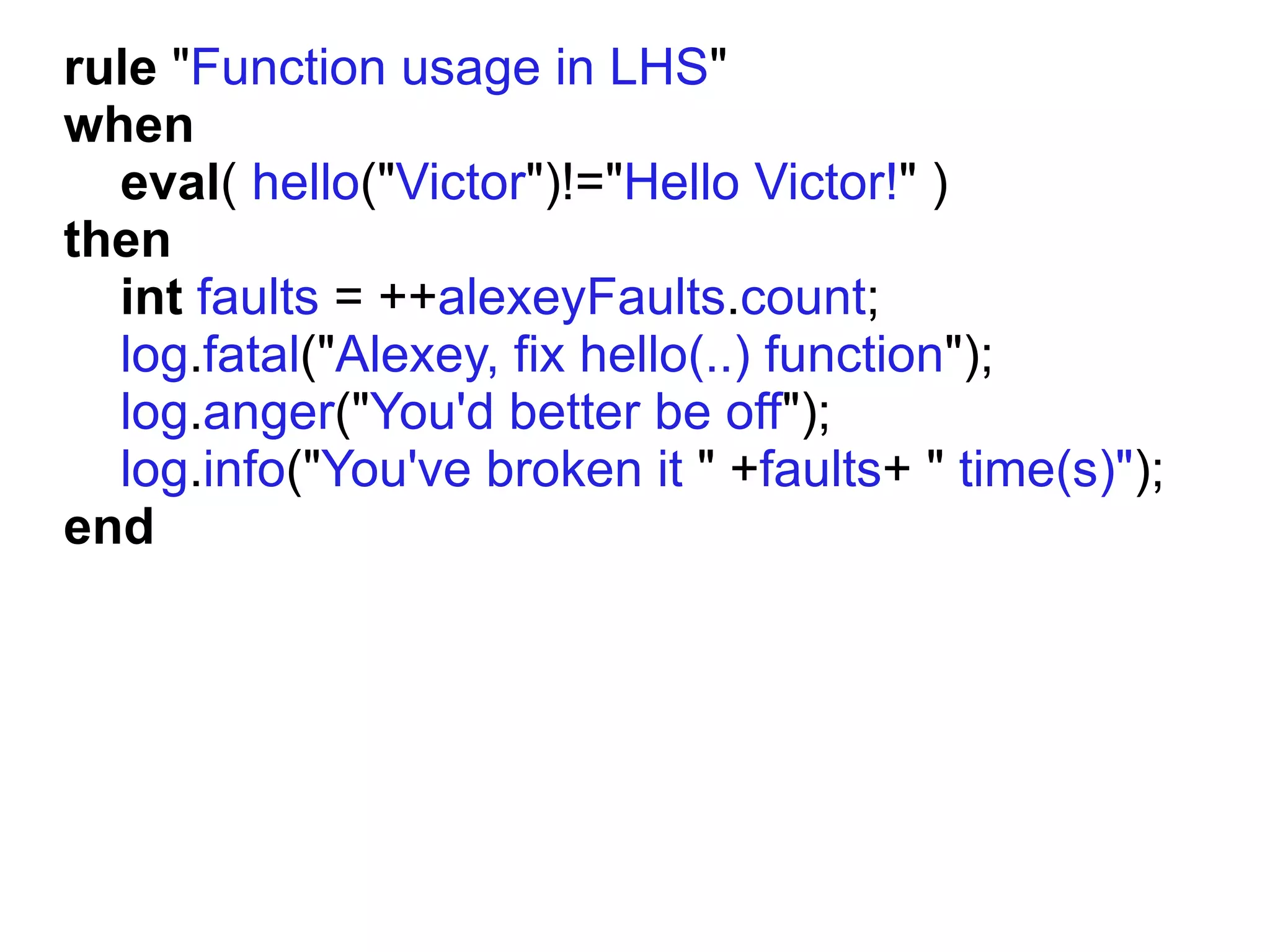
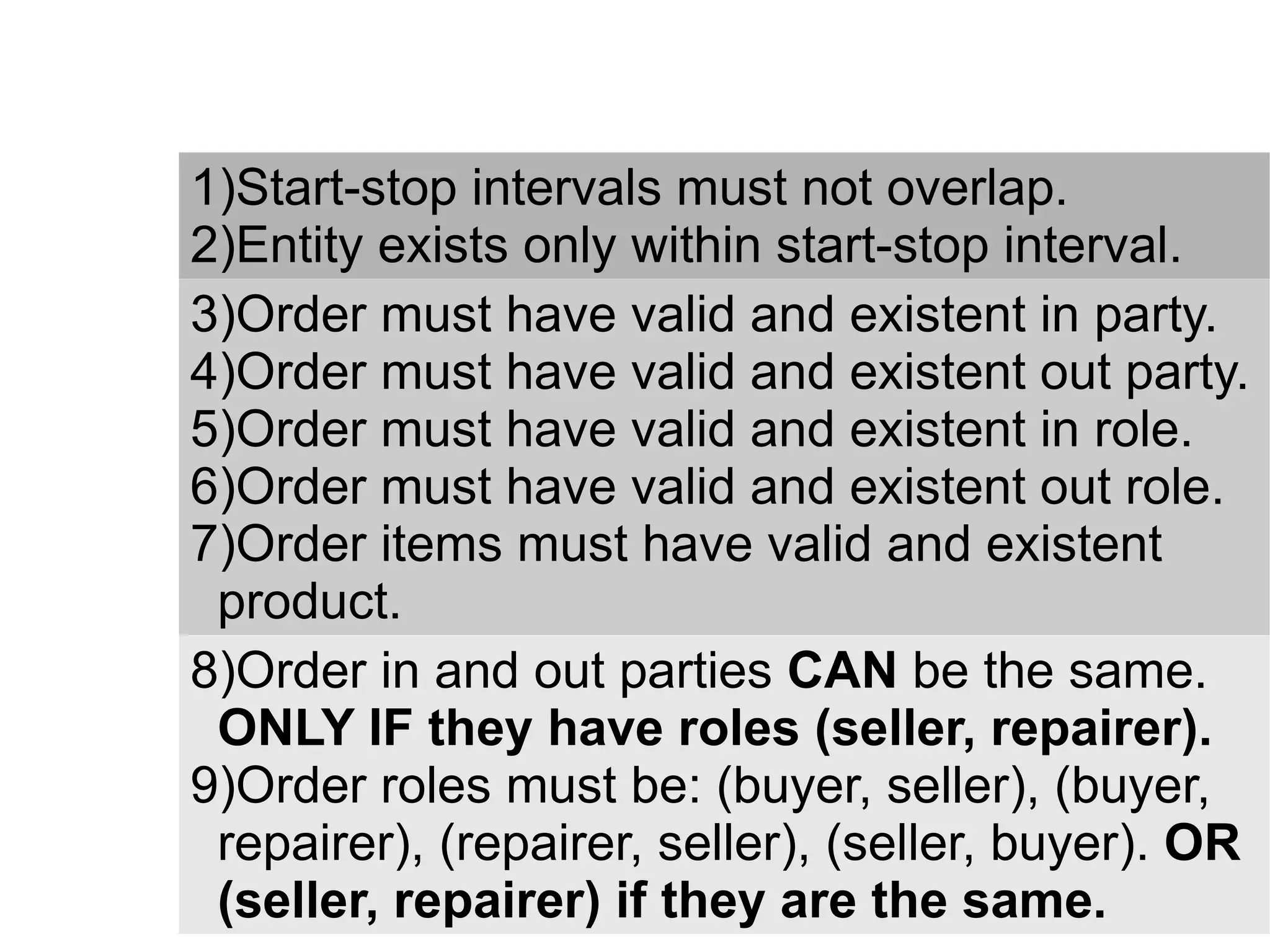
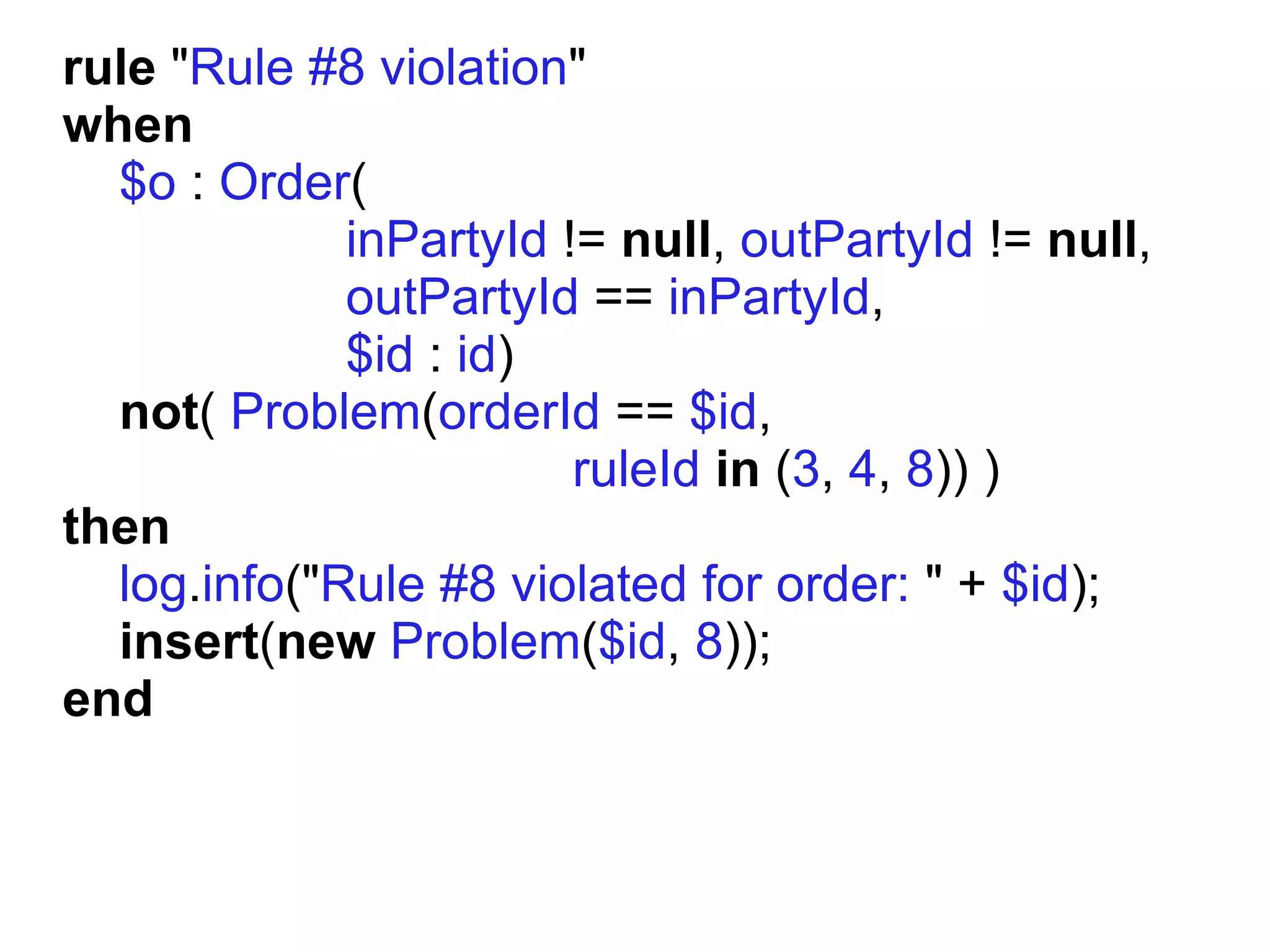
The document describes how JBoss Drools can be used to model business rules and requirements by defining rules using a domain-specific language that can validate objects like orders against the defined rules. Drools provides features like declarative rule patterns, object mapping, functions, queries, and templates to define complex validation logic in a more readable way compared to implementing the same logic in Java. Drools also supports defining metadata, classes and integrating with a rules engine and working memory to efficiently execute rules on facts.







![Drools Class Declaration
declare ExampleClass // Class name
[extends ParentExampleClass] // Inheritance
@stringMetadata("I am String") // Metadata
@dateMetadata(01-Jan-1970)
propertyName1 : ValidType, // Properties
propertyName2 : AnotherValidType](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-67-2048.jpg)

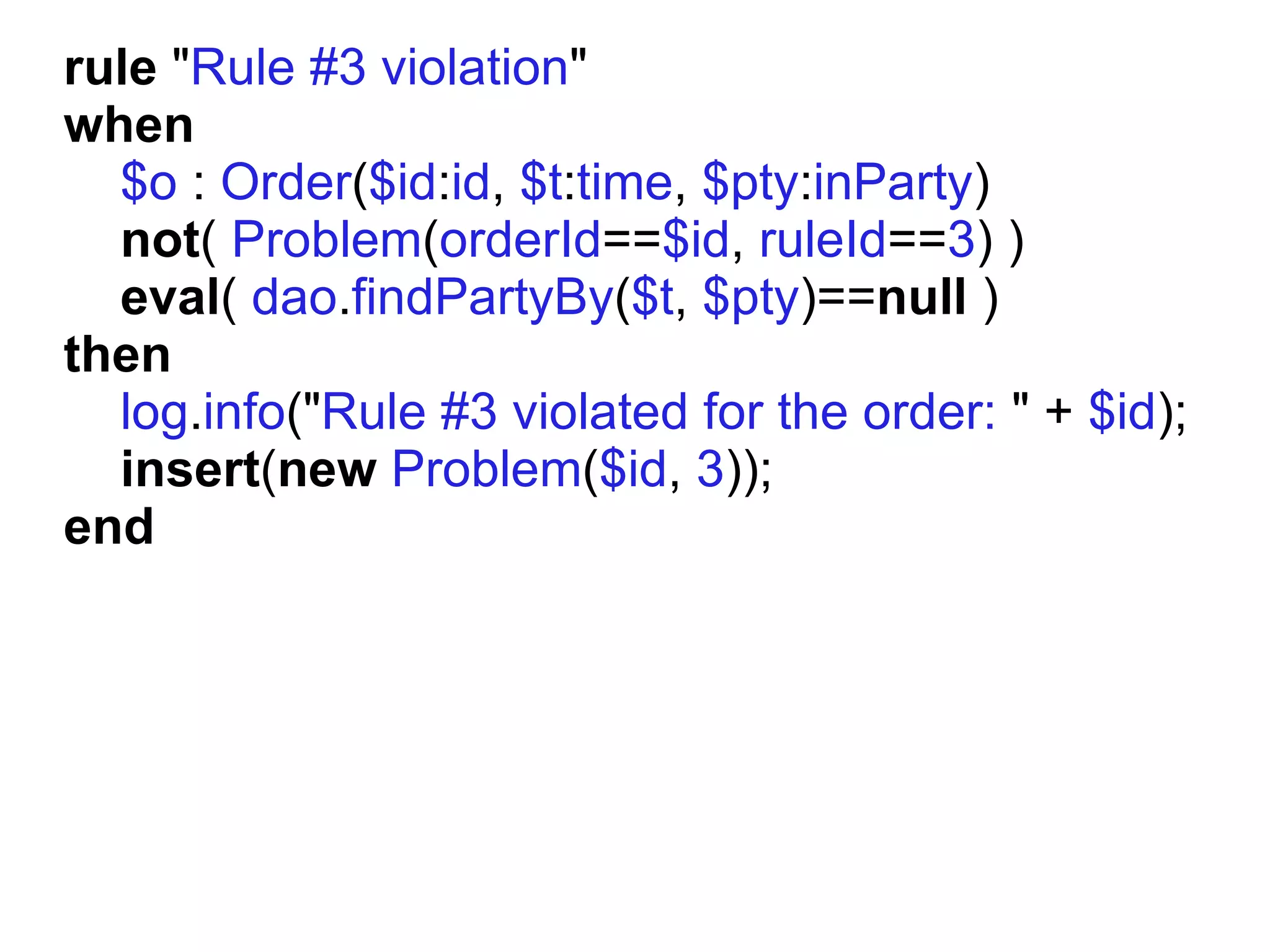
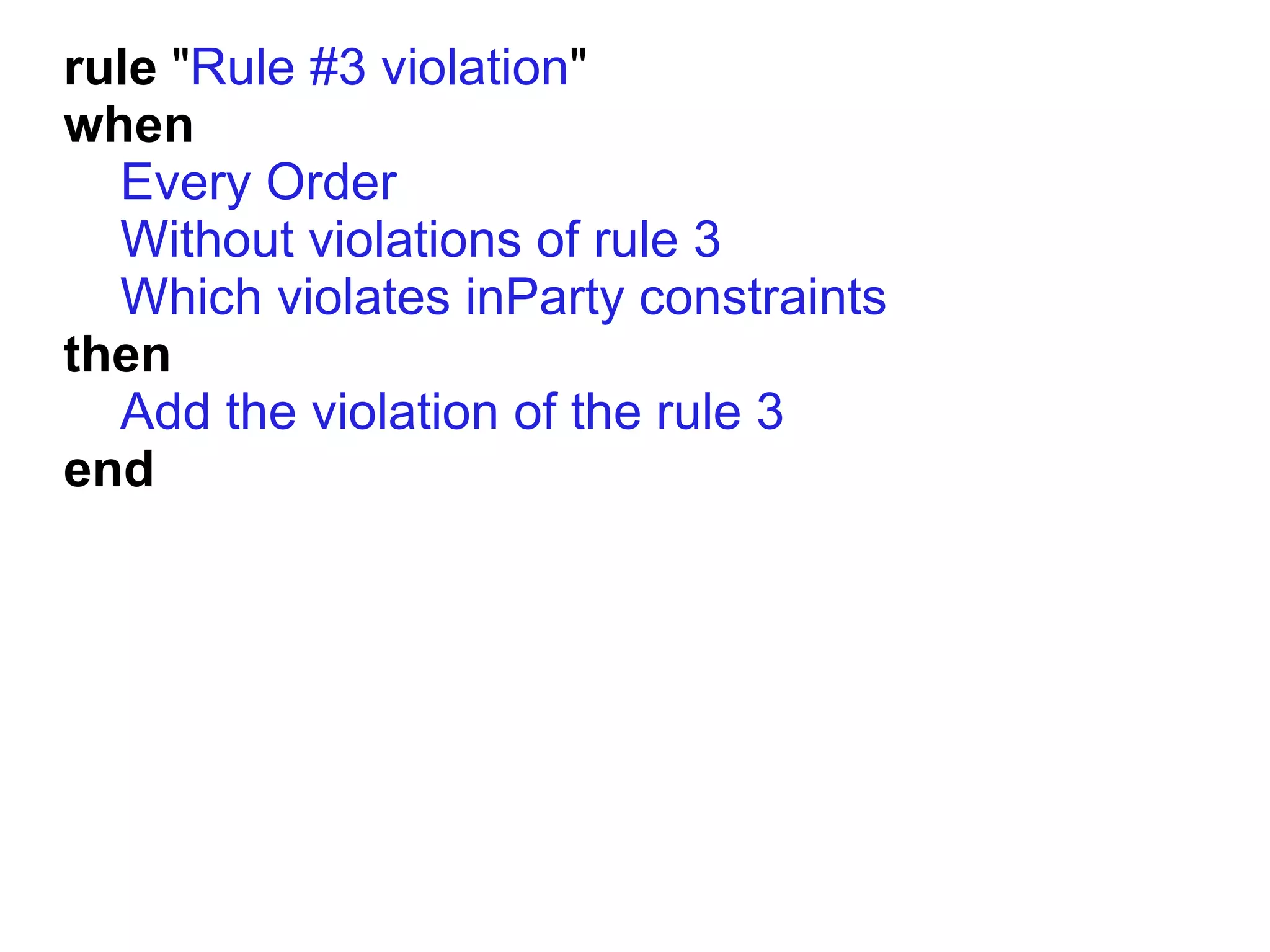
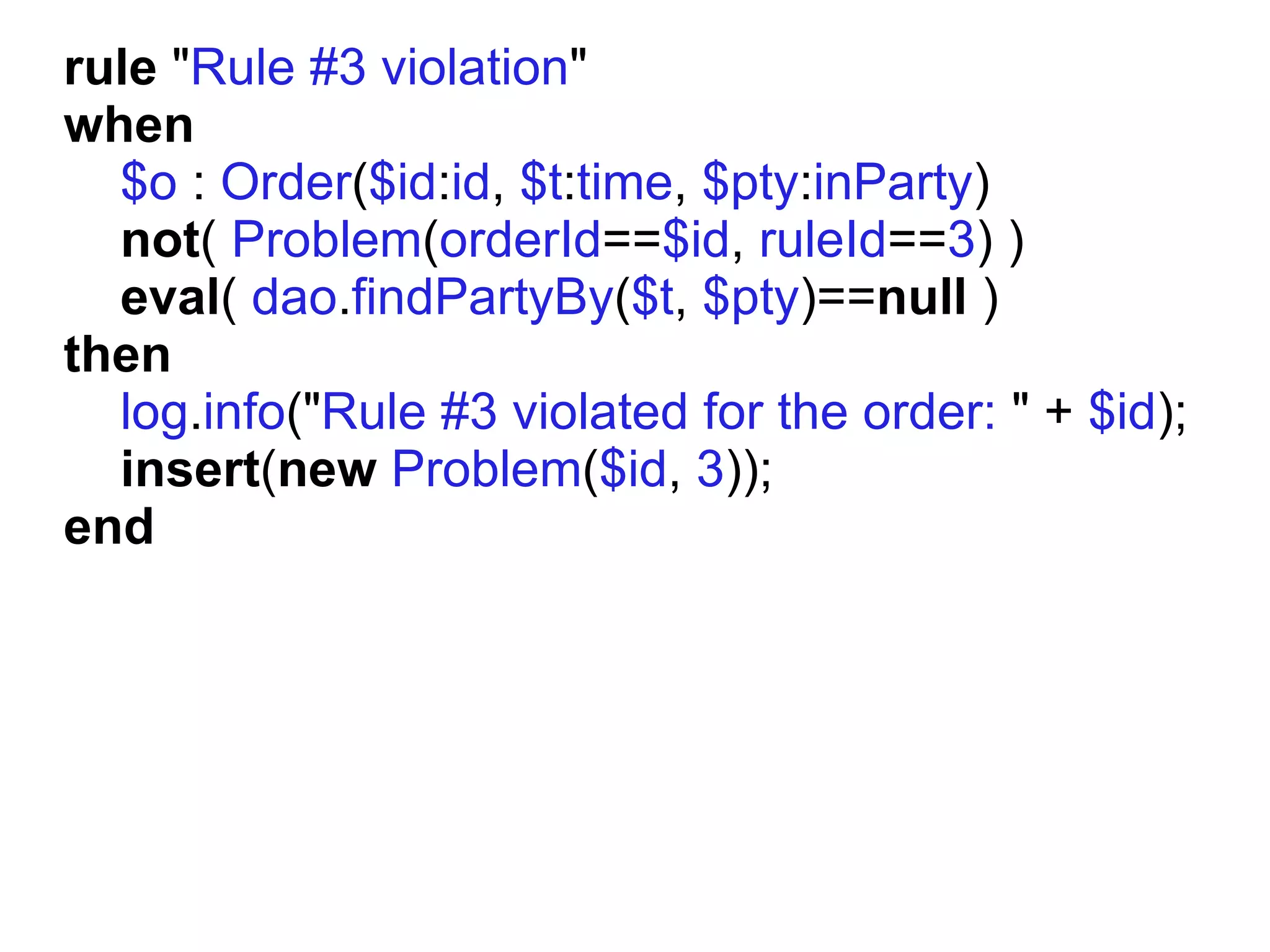
![[when] Every Order = $o : Order($id:id, $t:time,
$inPty:inParty)
[when] Without violations of rule {ruleNumber} =
not(Problem(orderId==$id, ruleId=={ruleNumber}))
[when] Which violates inParty constraints =
eval( dao.findPartyBy($t, $inPty) == null )
[then] Add the violation of the rule {ruleNumber} =
log.info("Rule #" + {ruleNumber} + " violated for
order: " + $id); insert(new Problem($id,
{ruleNumber}));](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-78-2048.jpg)
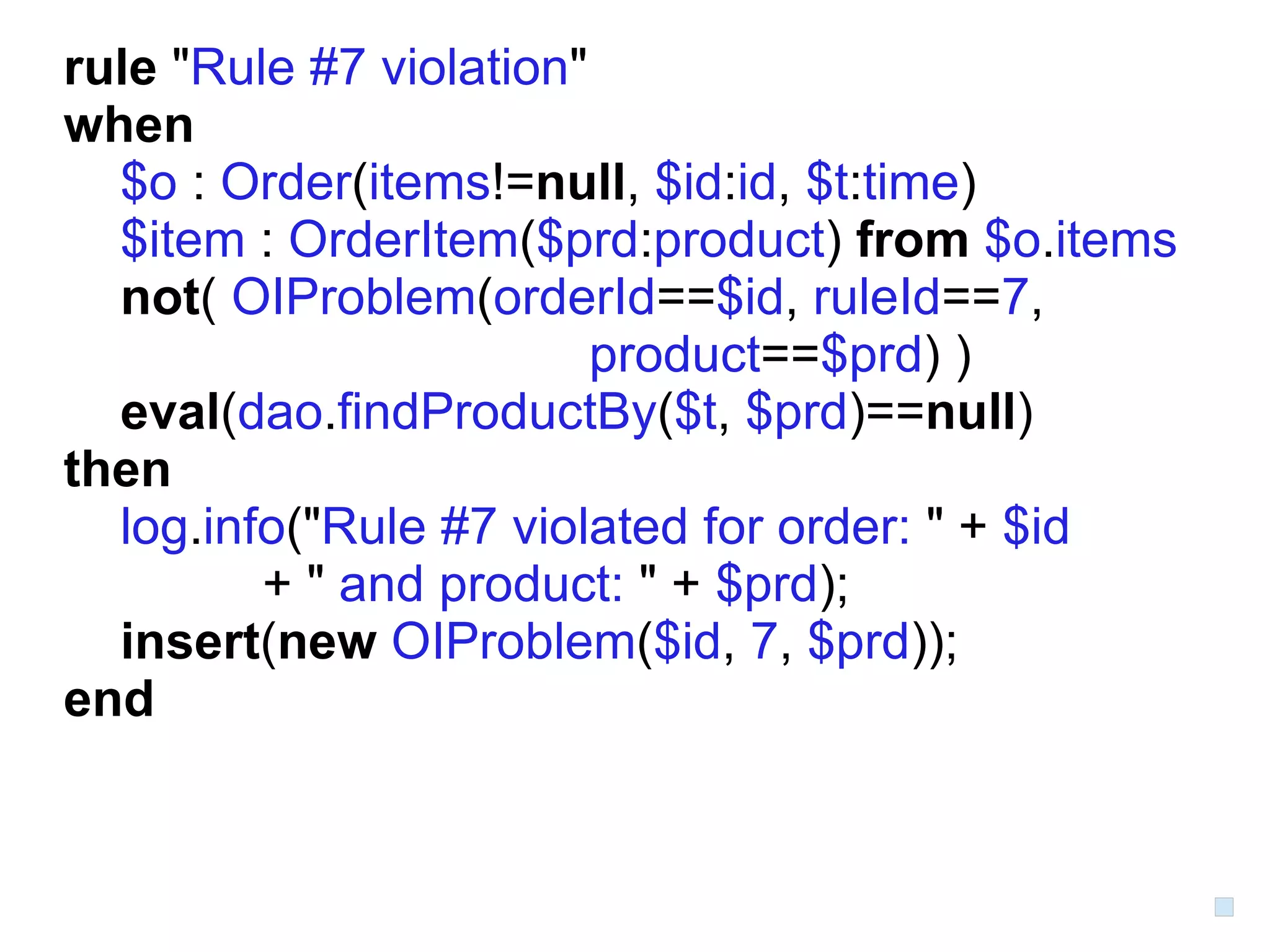
![[when] Every Order = $o : Order($id:id, $t:time,
$inPty:inParty)
[when] Without violations of rule {ruleNumber} =
not(Problem(orderId==$id, ruleId=={ruleNumber}))
[when] Which violates inParty constraints =
eval( dao.findPartyBy($t, $inPty) == null )
[then] Add the violation of the rule {ruleNumber} =
log.info("Rule #" + {ruleNumber} + " violated for
order: " + $id); insert(new Problem($id,
{ruleNumber}));](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-80-2048.jpg)
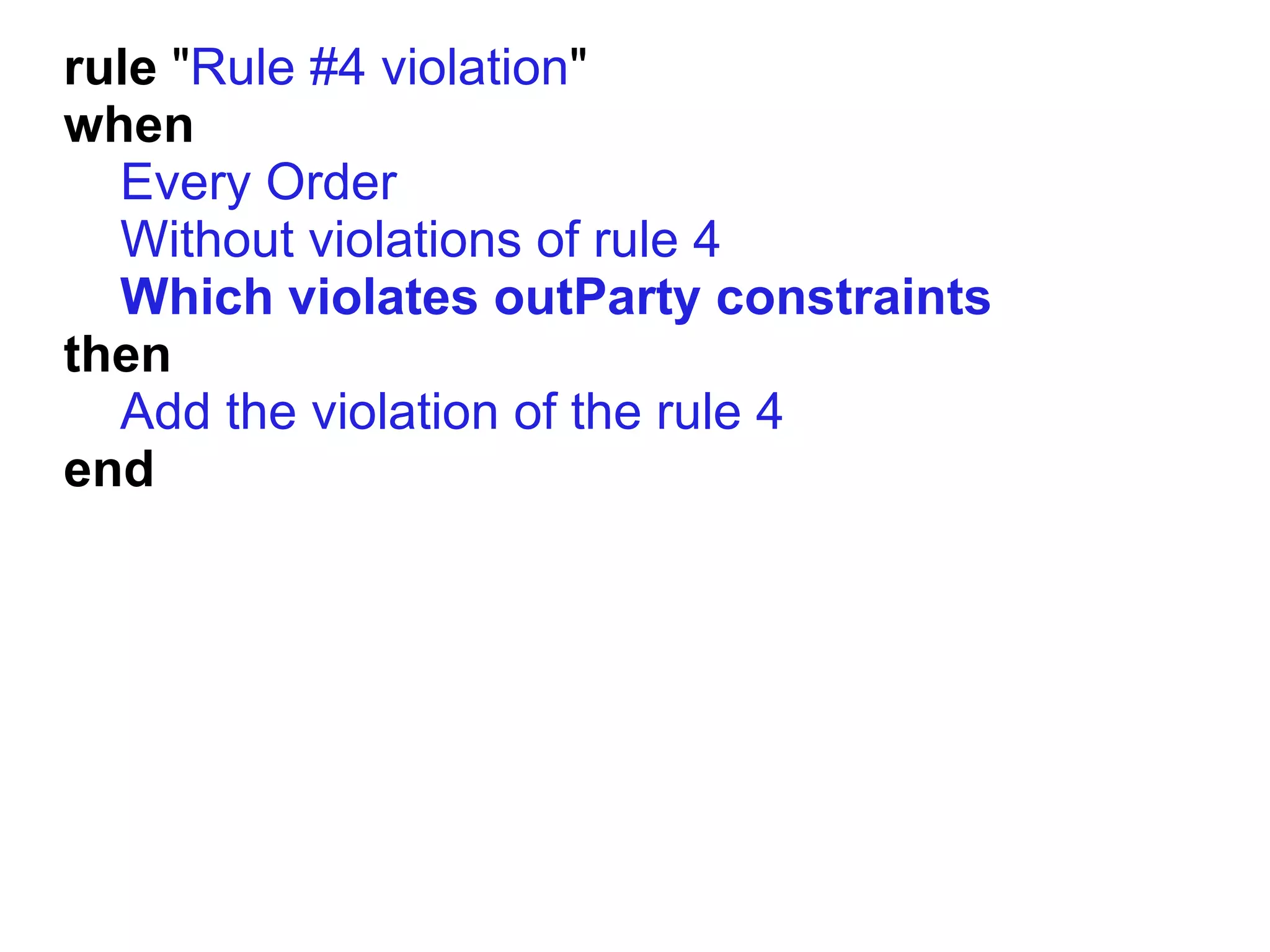
![[when] Every Order = $o : Order($id:id, $t:time,
$inPty:inParty,$outPty:outParty)
[when] Without violations of rule {ruleNumber} =
not(Problem(orderId==$id, ruleId=={ruleNumber}))
[when] Which violates inParty constraints =
eval( dao.findPartyBy($t, $inPty) == null )
[when] Which violates outParty constraints =
eval( dao.findPartyBy($t, $outPty) == null )
[then] Add the violation of the rule {ruleNumber} =
log.info("Rule #" + {ruleNumber} + " violated for
order: " + $id); insert(new Problem($id,
{ruleNumber}));](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-81-2048.jpg)



![[when] Every Order =
[when] Without violations of rule {N} =
[when] Which violates inParty constraints =
[when] Which violates outParty constraints =
[then] Add the violation of the rule {N} =](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-89-2048.jpg)
![[when] Every Order =
[when] - which has items = items != null
[when] And every OrderItem =
[when] Without violations of rule {N} =
[when] Which violates inParty constraints =
[when] Which violates outParty constraints =
[when] Without violations of order item rule {N} =
[when] Which violates product constraints =
[then] Add the violation of the rule {N} for order
item =
[then] Add the violation of the rule {N} =](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-90-2048.jpg)
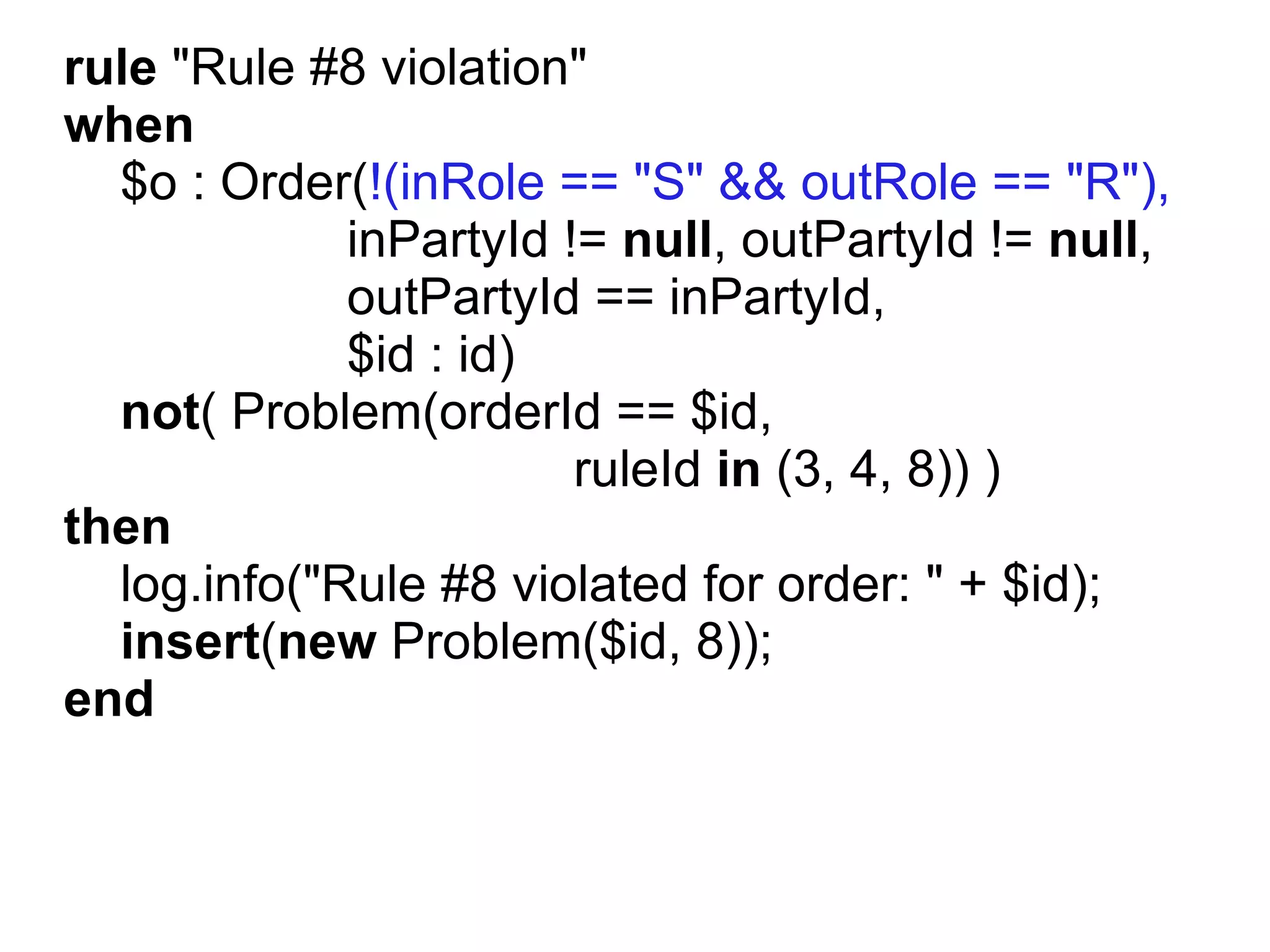
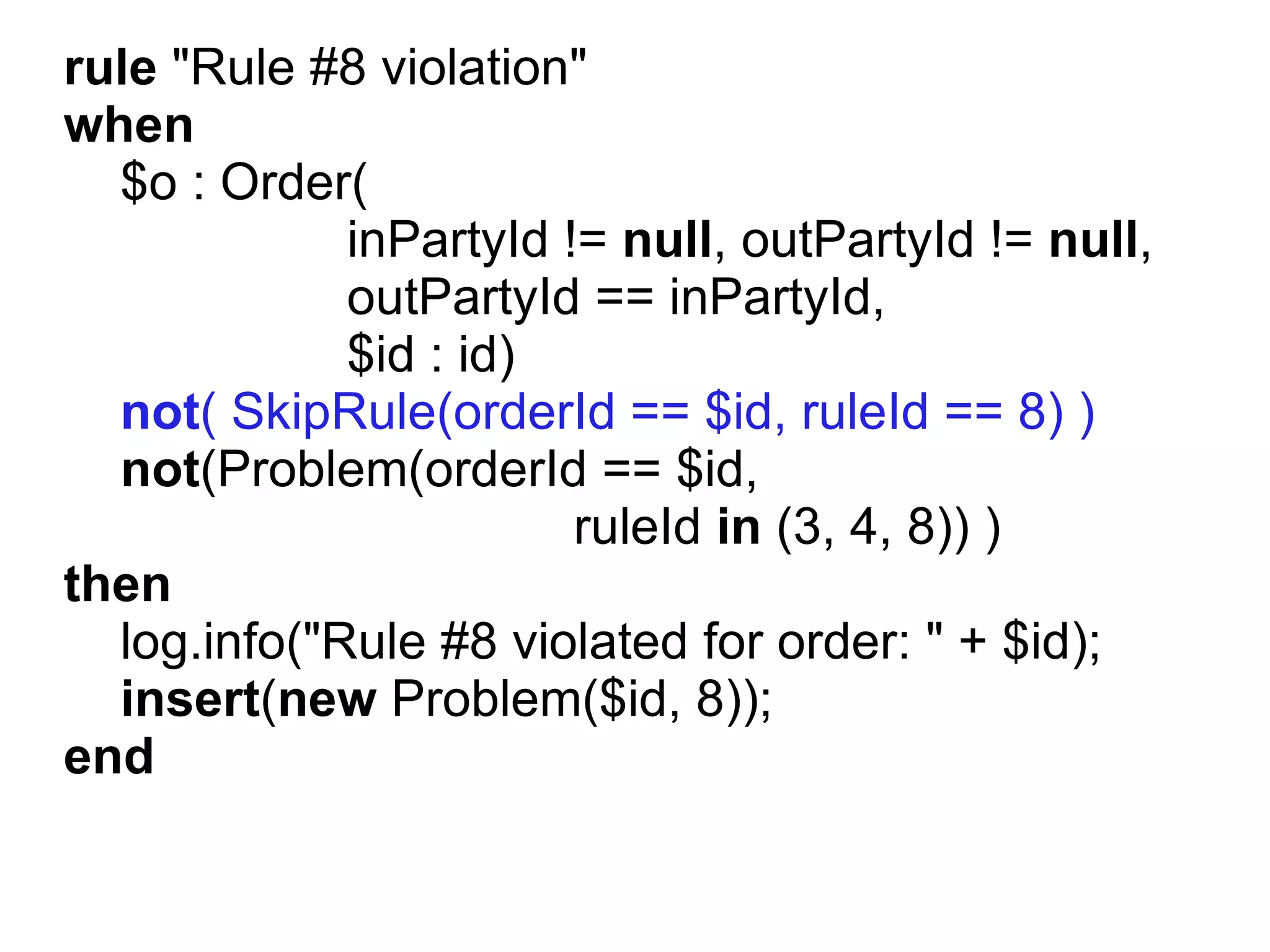
![rule "Rule #8 violation"
when
Every Order
- with inPartyId
- with outPartyId
- where inPartyId equals outPartyId
- and inRole not "S" and outRole not "R"
Without violations of rules [3,4,8]
then
Add the violation of the rule 8
end](https://image.slidesharecdn.com/drools-120419174045-phpapp02/75/JBoss-Drools-97-2048.jpg)