Embed presentation
Download as KEY, PPTX


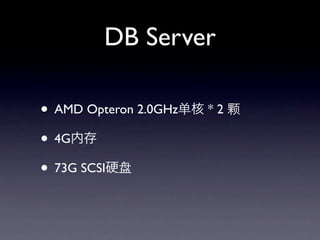

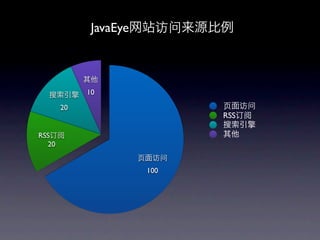

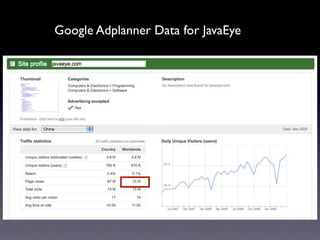
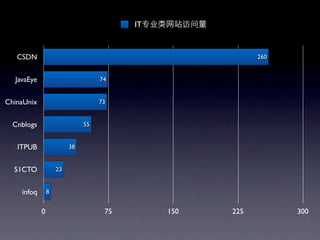
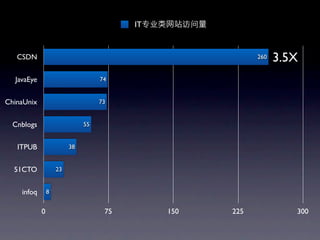
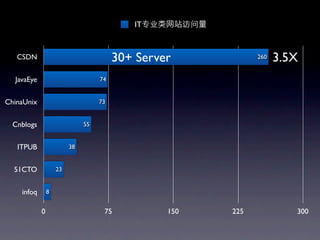
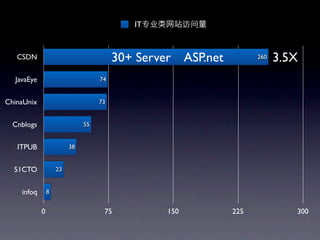
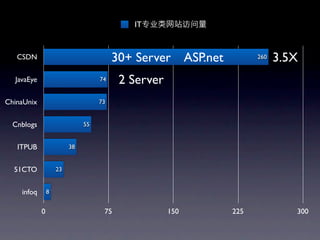
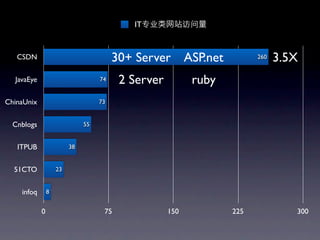
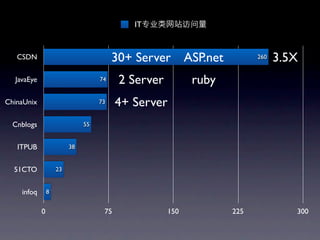
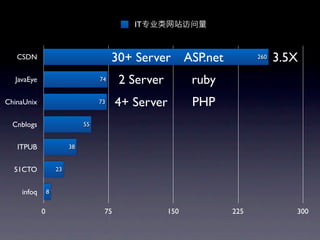
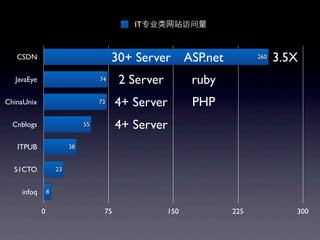
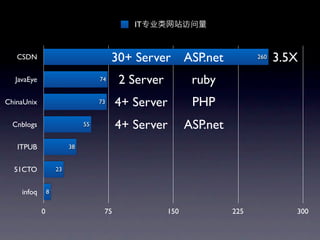
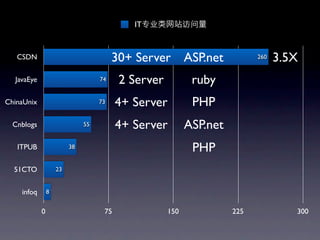
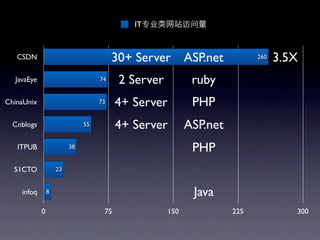
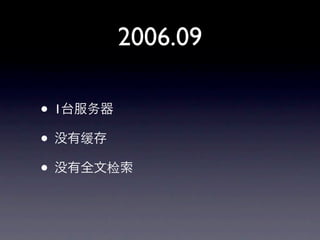
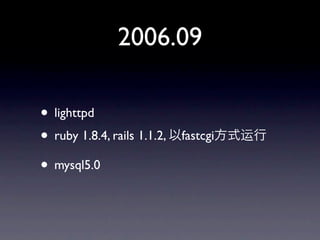
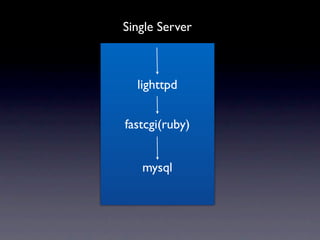
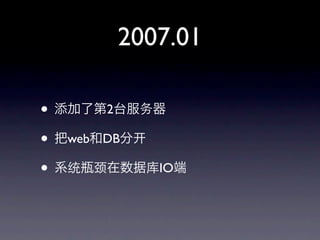
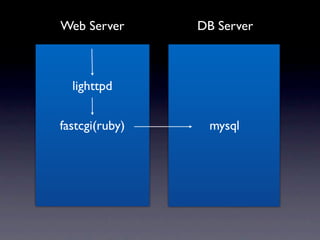
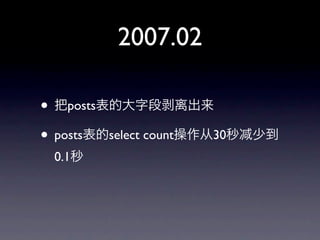
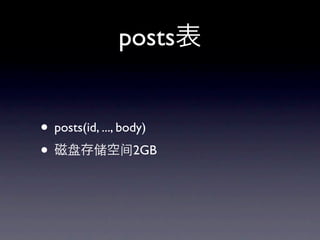
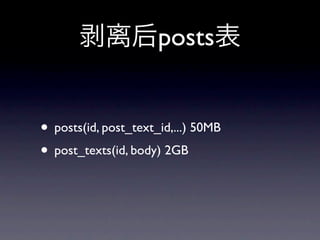
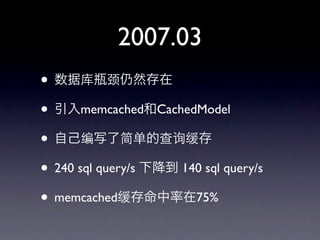
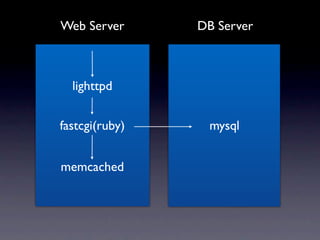
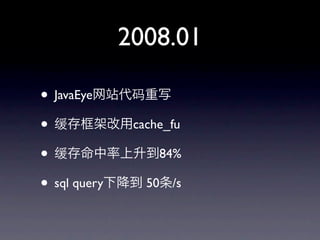
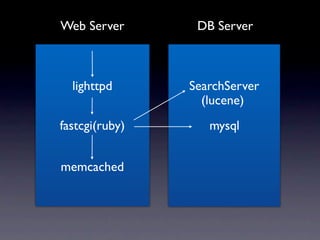
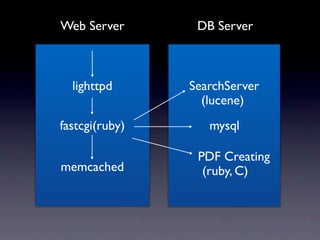
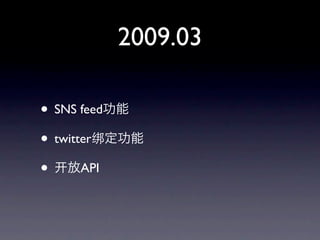
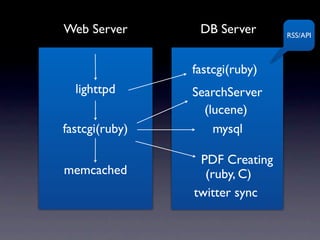
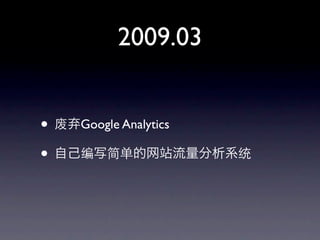
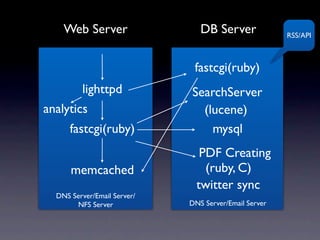
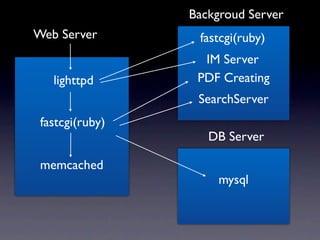
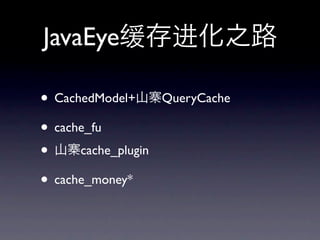

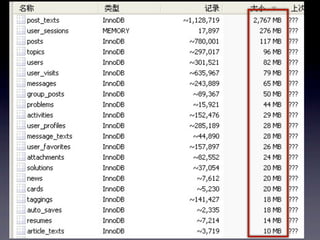
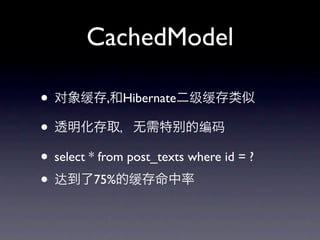
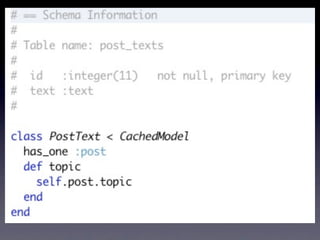

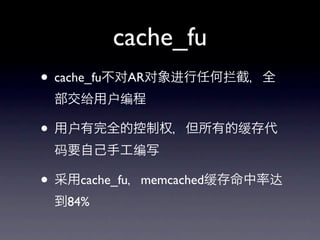

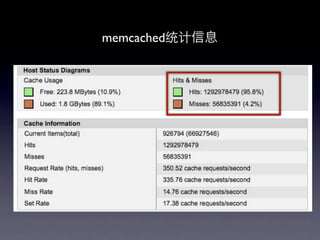
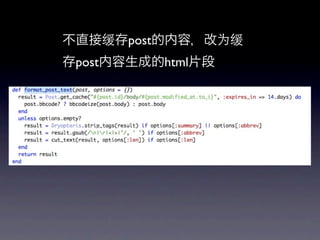
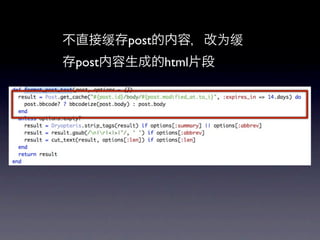
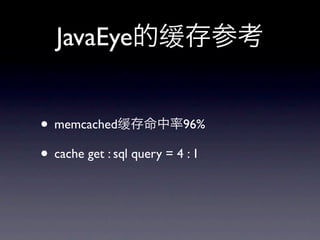
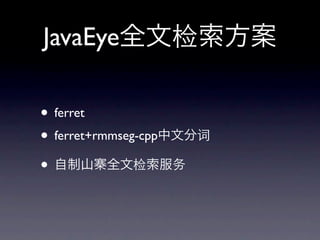
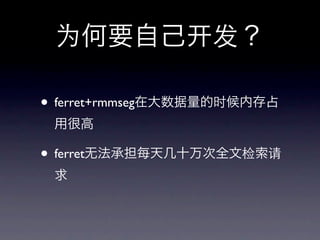
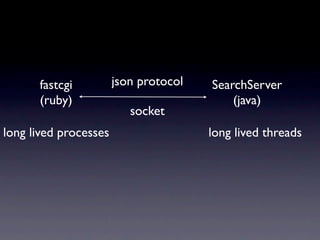
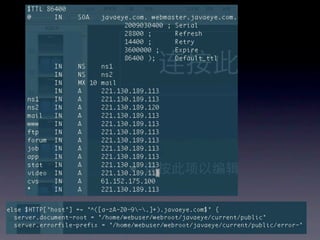
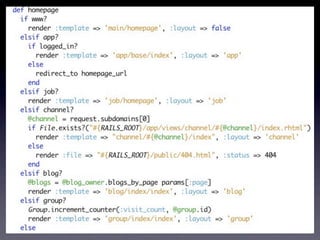

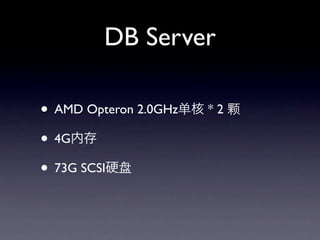
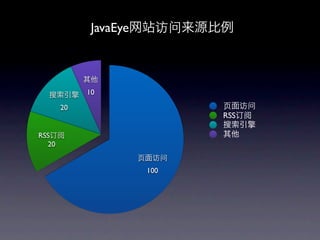
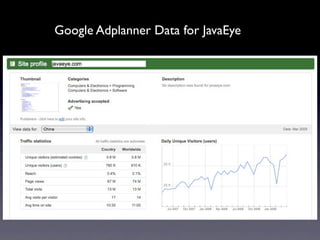
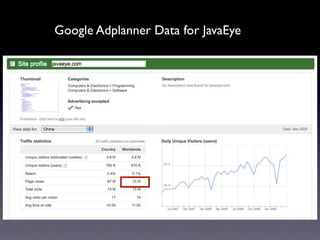
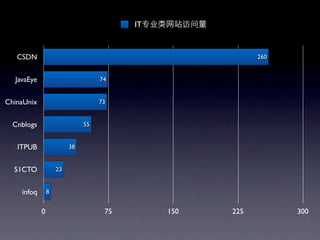
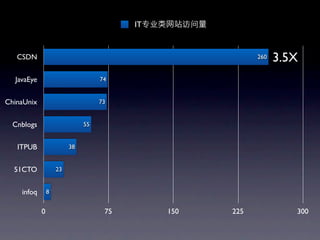
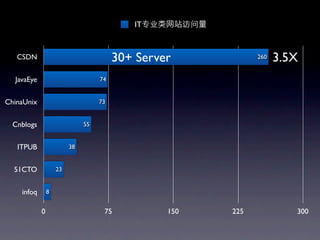
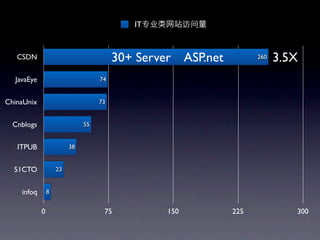
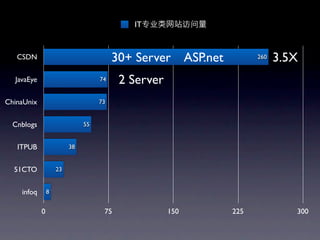
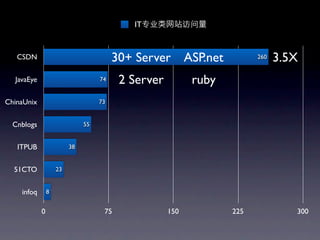
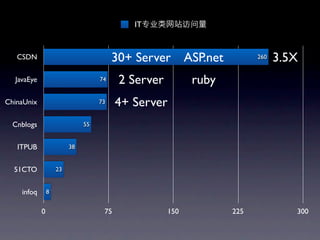
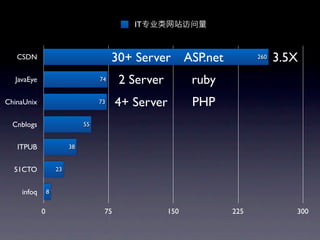
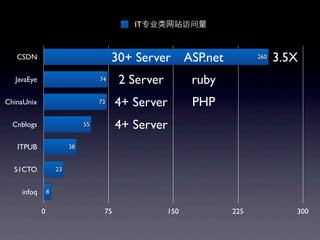
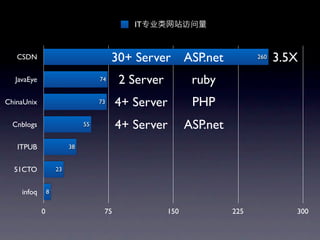
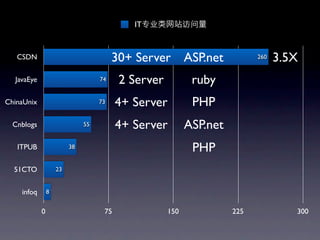
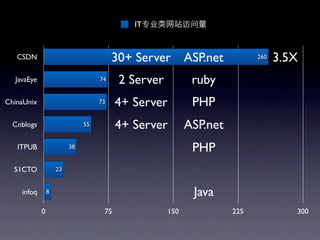
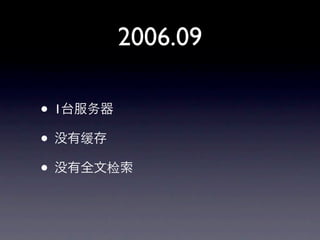
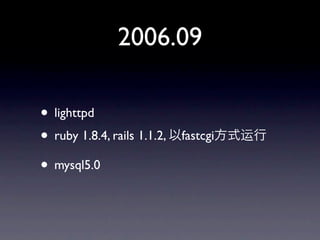
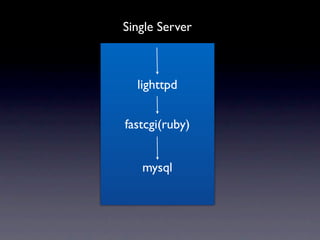
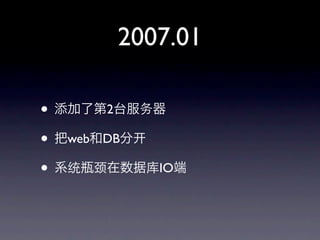
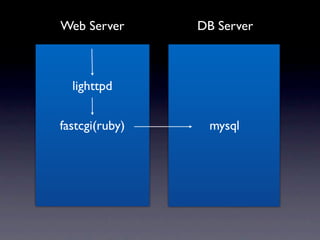
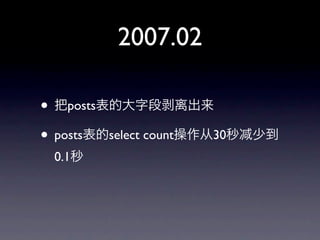
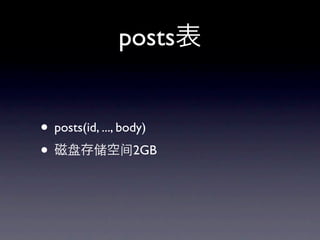
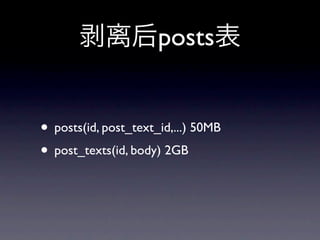
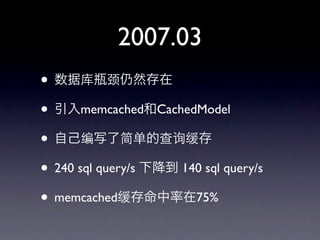
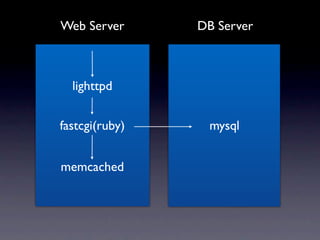
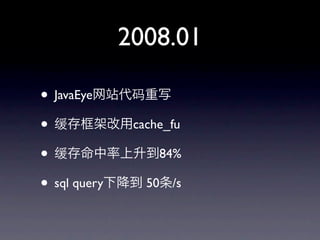
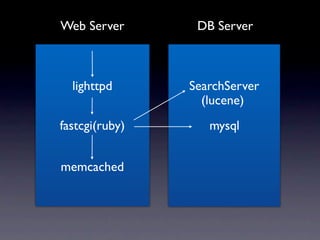
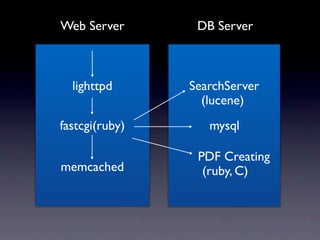
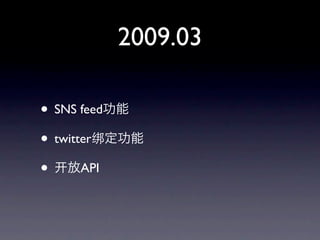
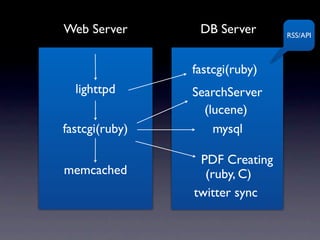
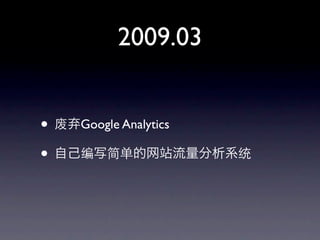
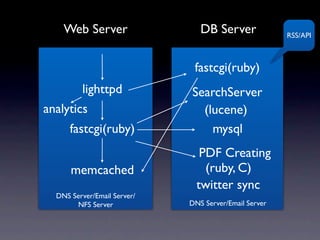
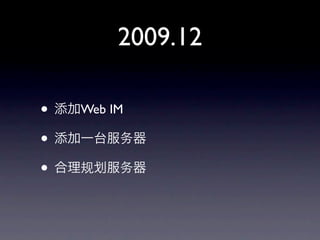
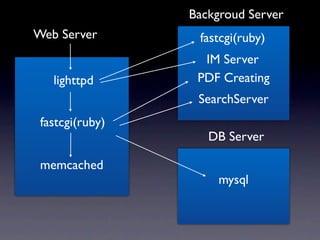
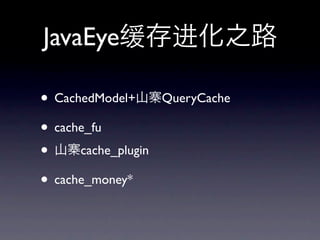
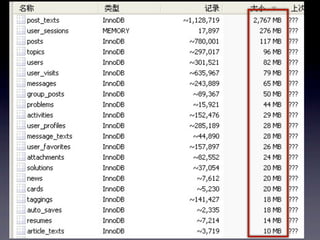
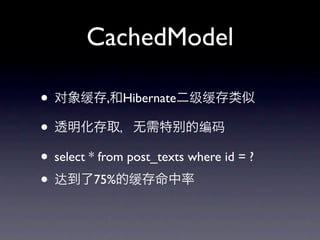
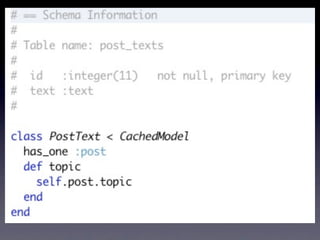
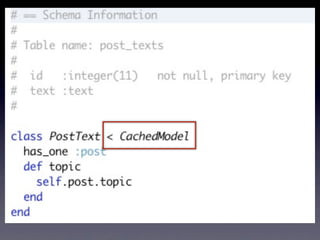
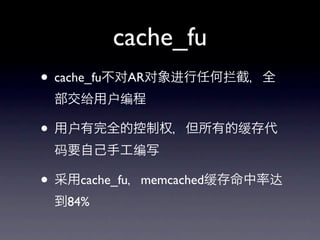
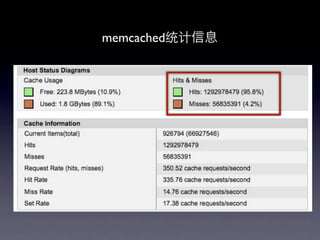
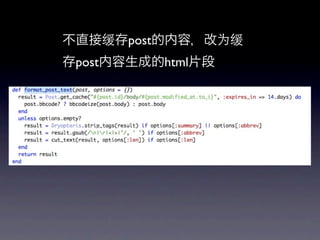
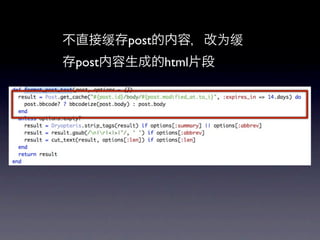
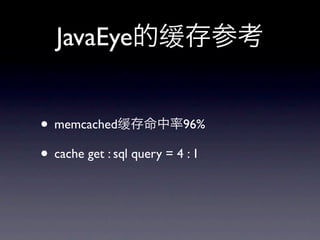
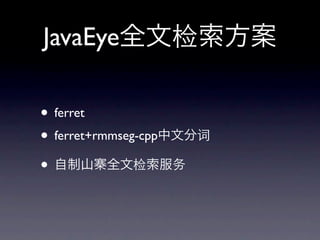
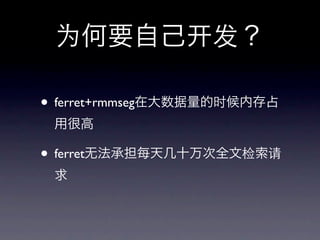
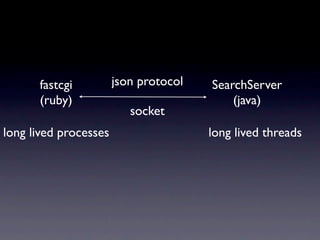
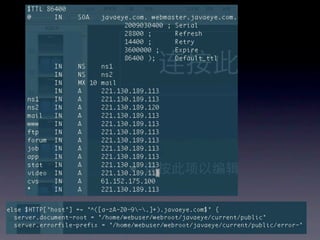
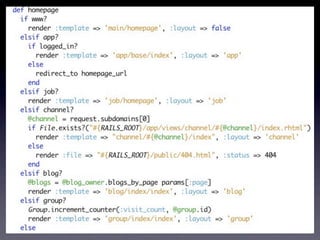
The document discusses JavaEye, a popular Chinese technical blog. It describes the evolution of JavaEye's architecture over time from a single server running Ruby on Rails to a more complex distributed system with front-end web servers, backend application servers, a search server, database servers, and caching. It highlights the technologies used at each stage, including Lighttpd, Memcached, and search tools like Ferret and Lucene, and how caching improved performance by reducing SQL queries.