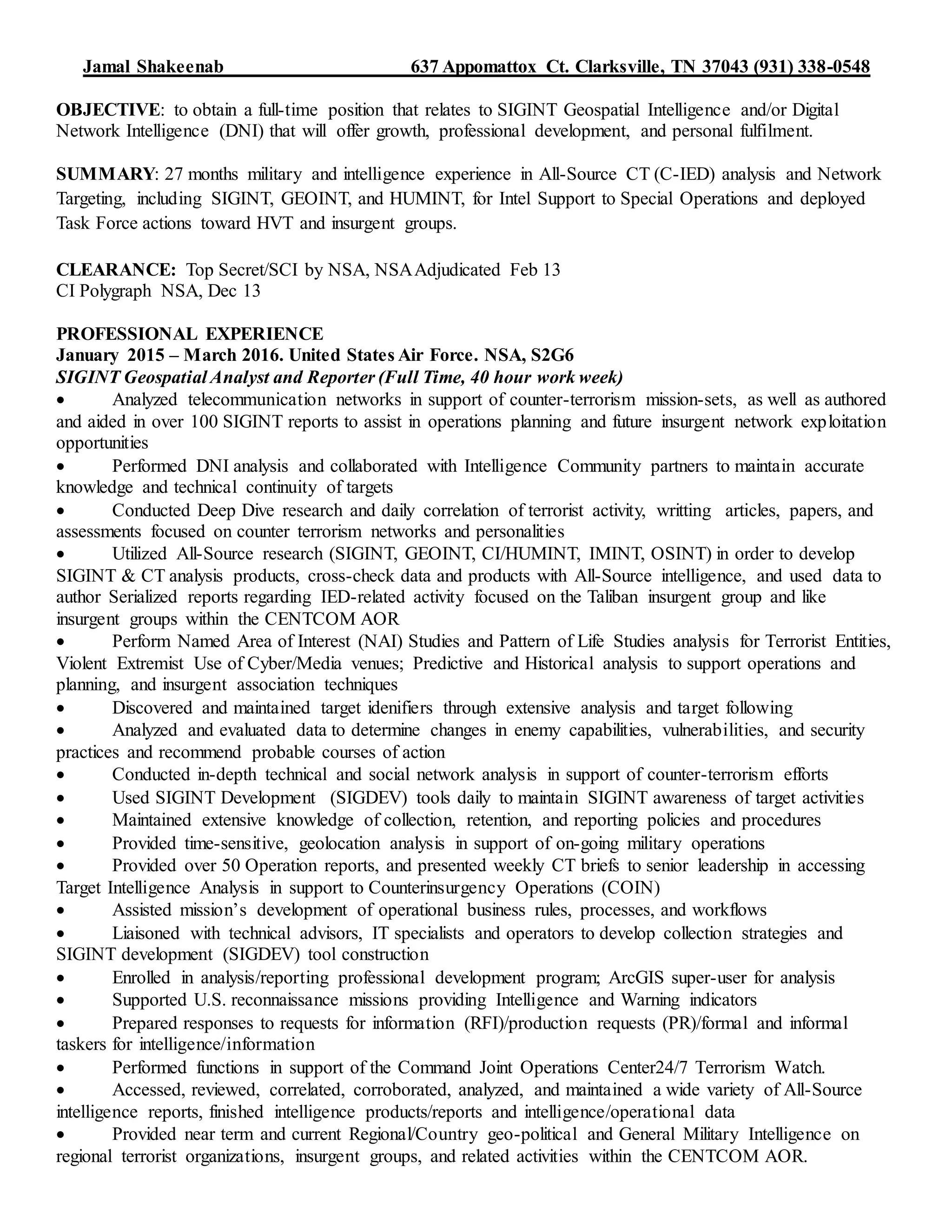
Jamal Shakeenab provides his resume, which details over 2 years of experience conducting signals intelligence analysis, geospatial intelligence analysis, and digital network intelligence analysis to support counterterrorism operations while serving in the United States Air Force and Air National Guard. He holds a Top Secret/SCI security clearance and has analyzed communications networks, conducted technical and social network analysis, and authored over 100 intelligence reports.