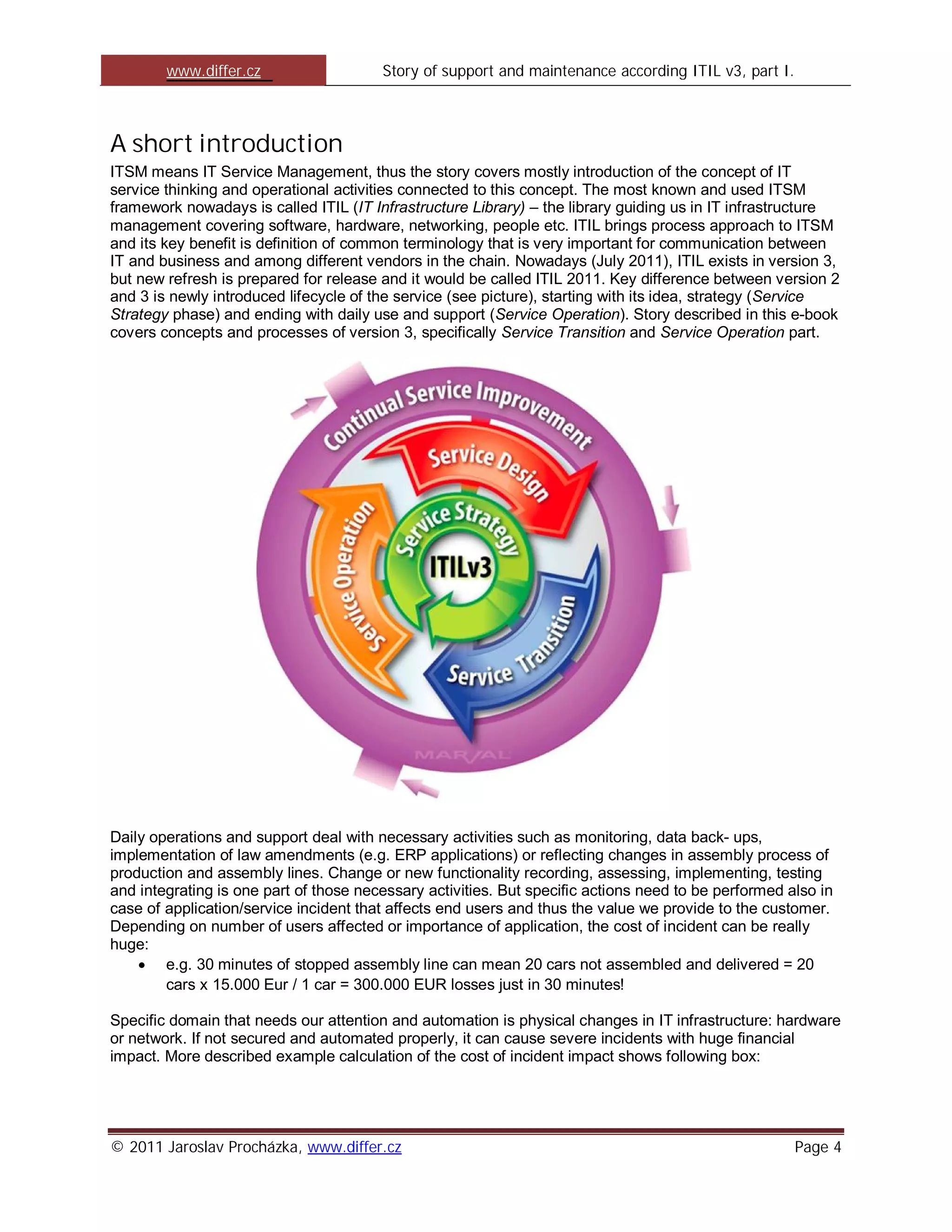
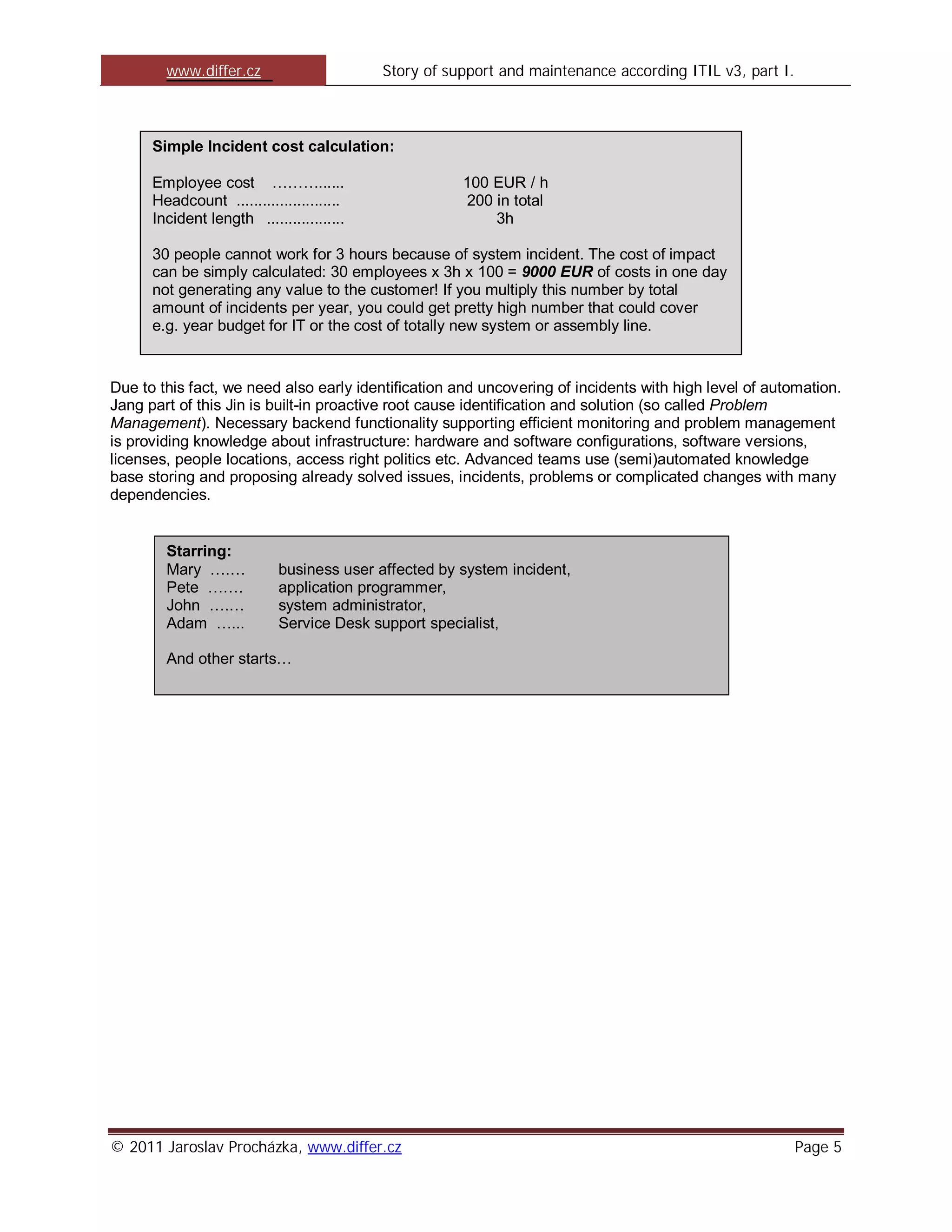
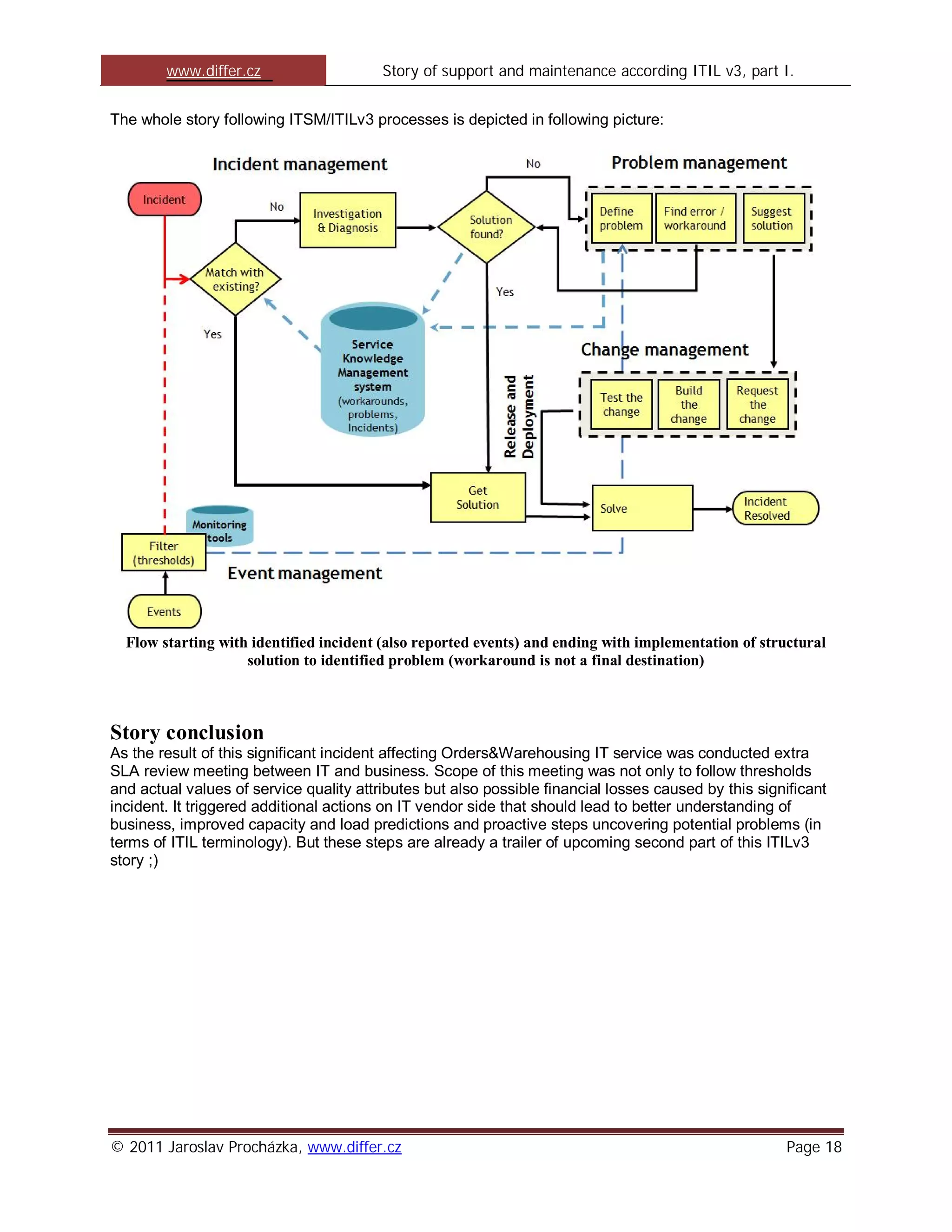
The document is part one of a story that aims to summarize ITIL v3 concepts related to IT service management in an accessible way. It introduces the concepts of incident management and problem management in ITIL and how addressing incidents efficiently can save a company money by minimizing downtime. It sets up a scenario where a business user is affected by a system incident and support is needed to resolve the issue and identify the root cause. The story aims to illustrate ITIL processes and terminology to help diverse audiences better understand IT service management.