Introduction to Cybersecurity-certificate - Cisco SIgn
•
0 likes•41 views
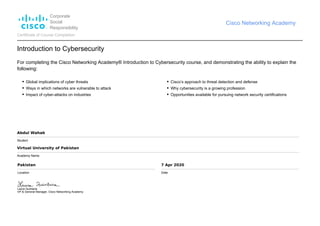
Global implications of cyber threats Ways in which networks are vulnerable to attack Impact of cyber-attacks on industries Cisco’s approach to threat detection and defense Why cybersecurity is a growing profession Opportunities available for pursuing network security certifications
Report
Share
Report
Share
Download to read offline
Recommended
Certificate of Course Completion "Introduction to Cybersecurity" powered by C...

Introduction to Cybersecurity
Recommended
Certificate of Course Completion "Introduction to Cybersecurity" powered by C...

Introduction to Cybersecurity
Intro to cybersecurity

• Global implications of cyber threats
• Ways in which networks are vulnerable to attack
• Impact of cyber-attacks on industries
• Cisco’s approach to threat detection and defense
• Why cybersecurity is a growing profession
• Opportunities available for pursuing network security certifications
Network Security Expert (NSE) 2 The Evolution of Cybersecurity

Network Security Expert (NSE) 2 The Evolution of Cybersecurity powered by Fortinet
Fortinet Network Security Expert Level 1: Certified Associate

Fortinet Network Security Expert Level 1: Certified Associate
Issued: November 2020
Expires: November 2022
Wireless Technology and Standards

Learnt WLAN standards and the technical aspects of Wireless Technologies
EC-Council Certified Network Defender

The Ultimate Certification for Network Administrators
A vendor-neutral, hands-on, instructor-led, comprehensive network security certification training program.
The program prepares network administrators on network security technologies and operations to attain Defense-in-Depth Network security preparedness.
Scientology Online Communication Course.pdf

Communication is one activity in life that everyone shares. It is one of the most important parts of understanding. And if you want to improve your understanding, be more successful, be a happier person and help make others around you happier, you need to communicate well.
Things taught in this course:
How to communicate with another so they listen and understand what you are saying.
The exact formula of successful communication—and how to vastly improve your ability to communicate with anyone.
Tools you can use to correct any communication failures you have with another.
I AM UNSTOPPABLE - FKRI Certificate.

I got his certificate from Fahad Khan in recognition of my contribution to Transforming Youth into Leaders.
Introduction to IoT - CISCO Certificate 

Explain how IoT and Digital Transformation are positively impacting businesses and governments
Explain the importance of software and data for digital businesses and society.
Explain the benefits of automation and artificial intelligence for digital transformation.
Explain the concepts of Intent Based Networking.
Explain the need for enhanced security in the digitized world.
More Related Content
What's hot
Intro to cybersecurity

• Global implications of cyber threats
• Ways in which networks are vulnerable to attack
• Impact of cyber-attacks on industries
• Cisco’s approach to threat detection and defense
• Why cybersecurity is a growing profession
• Opportunities available for pursuing network security certifications
Network Security Expert (NSE) 2 The Evolution of Cybersecurity

Network Security Expert (NSE) 2 The Evolution of Cybersecurity powered by Fortinet
Fortinet Network Security Expert Level 1: Certified Associate

Fortinet Network Security Expert Level 1: Certified Associate
Issued: November 2020
Expires: November 2022
Wireless Technology and Standards

Learnt WLAN standards and the technical aspects of Wireless Technologies
EC-Council Certified Network Defender

The Ultimate Certification for Network Administrators
A vendor-neutral, hands-on, instructor-led, comprehensive network security certification training program.
The program prepares network administrators on network security technologies and operations to attain Defense-in-Depth Network security preparedness.
What's hot (18)
Network Security Expert (NSE) 2 The Evolution of Cybersecurity

Network Security Expert (NSE) 2 The Evolution of Cybersecurity
Fortinet Network Security Expert Level 1: Certified Associate

Fortinet Network Security Expert Level 1: Certified Associate
More from Abdul Wahab
Scientology Online Communication Course.pdf

Communication is one activity in life that everyone shares. It is one of the most important parts of understanding. And if you want to improve your understanding, be more successful, be a happier person and help make others around you happier, you need to communicate well.
Things taught in this course:
How to communicate with another so they listen and understand what you are saying.
The exact formula of successful communication—and how to vastly improve your ability to communicate with anyone.
Tools you can use to correct any communication failures you have with another.
I AM UNSTOPPABLE - FKRI Certificate.

I got his certificate from Fahad Khan in recognition of my contribution to Transforming Youth into Leaders.
Introduction to IoT - CISCO Certificate 

Explain how IoT and Digital Transformation are positively impacting businesses and governments
Explain the importance of software and data for digital businesses and society.
Explain the benefits of automation and artificial intelligence for digital transformation.
Explain the concepts of Intent Based Networking.
Explain the need for enhanced security in the digitized world.
Networking Essentials - CISCO Certificate

• Explain how end-user devices and local networks interact with the global Internet.
• Explain the requirements for network connectivity.
• Build a small network using an integrated network router.
• Explain the importance of IP addressing.
• Explain how the protocols of the TCP/IP suite enable network communication
• Configure an integrated wireless router and wireless clients to connect securely to the Internet.
• Configure basic network security.
• Build a simple computer network using Cisco devices.
• Troubleshoot common network issues found in home and small business networks.
Get Connected

For completing the Cisco Networking Academy® Get Connected course, and demonstrating the ability to do the following:
Identify different types of computer systems, internal components and
external devices.
Understand the structure of the directories in Microsoft Windows, and
how to work with files and folders using a text editor.
Understand computer networks, as well as browse and search the
Internet, and use email. Create and use various types of social media accounts, including Facebook, LinkedIn, and YouTube.
Identify common problems and implement simple solutions for hardware, software and networks
More from Abdul Wahab (6)
Recently uploaded
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Recently uploaded (20)
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Introduction to Cybersecurity-certificate - Cisco SIgn
- 1. Corporate Social Responsibility Cisco Networking Academy Certificate of Course Completion Introduction to Cybersecurity For completing the Cisco Networking Academy® Introduction to Cybersecurity course, and demonstrating the ability to explain the following: Global implications of cyber threats Ways in which networks are vulnerable to attack Impact of cyber-attacks on industries Cisco’s approach to threat detection and defense Why cybersecurity is a growing profession Opportunities available for pursuing network security certifications Abdul Wahab Student Virtual University of Pakistan Academy Name Pakistan Location 7 Apr 2020 Date Laura Quintana VP & General Manager, Cisco Networking Academy