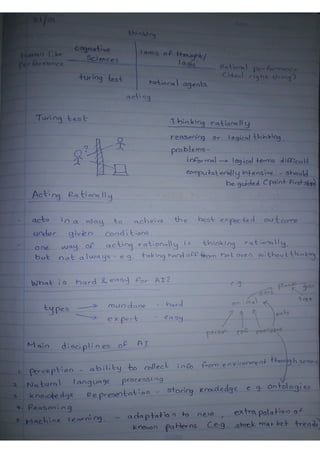
Intelligent systems note
•
1 like•60 views
My written notes of Intelligent systems course as a Bsc. engineering undergraduate of University of Moratuwa.
Report
Share
Report
Share
Download to read offline
Recommended
Software Requirement Specification

The document provides a software requirement specification for a marble factory management system. The system aims to automate the manual processes currently used by The New Fine Marble Factory. Key features include login management, stock process management, adding and dropping employees, and billing management. The system will allow admin access to manage stock records, add or remove inventory items, update employee records, and view all bills. It seeks to save time by automating activities like generating reports and tracking inventory levels.
SENG 6270 - Software-Requirement-Specifications

This document is a software requirements specification for a reprints ordering system. It describes the purpose, scope and functions of the system. The system will allow customers to order photo reprints by selecting options like quantity, size, finish and processing time. It will automatically calculate the total cost and apply any discounts. The document defines requirements for user interfaces, functions, and behaviors of the system. Key requirements include validating user inputs, updating costs in real-time, applying discounts, and generating receipts. The system will be a windows application with a single screen for data entry and order processing.
SOFTWARE REQUIREMENT SPECIFICATION FOR PROJECT

This document provides a project report on developing a "Gate Point Application" android app to provide exam preparation materials for the GATE exam. The app will provide learning content and practice tests for subjects like computer science and electrical engineering. It will also include a syllabus and latest news about the GATE exam. The report outlines the software requirements, including functional requirements like different home screen buttons and sliding menus, as well as non-functional requirements. It presents data flow diagrams and design approaches like the iterative waterfall model. Gantt and PERT charts are also proposed to track the project schedule and dependencies between tasks.
Software engineering project(srs)!!

Jet Messenger v1.0 is a peer to peer LAN messenger which needs no dedicated server for connections and messaging.
Water management portal

The document is a software requirements specification for a Water Management Portal. It includes sections that provide an introduction and overview, describe the overall system and specific requirements. The introduction describes the purpose of creating a web application to allow users to report water-related issues, view information, and allow city employees to update statuses. The overall description outlines the system interfaces, hardware requirements, communication methods, and constraints. It also includes use case and entity relationship diagrams. The specific requirements section describes use cases for different user types: visitors, administrators, city employees and residents.
Software Requirement Specification For Smart Internet Cafe

The document is a software requirements specification for a Smart Internet Cafe (SIC) system. It outlines requirements across many sections - introduction and document conventions, overall descriptions of the system and its users/environment, external interface requirements including the user interface, system features like authentication and monitoring, and non-functional requirements such as performance, security, and special user needs. The SIC will provide secure internet access and account/usage monitoring for clients of internet cafes and college computer labs.
Srs2 Job Portal

The document provides a software requirements specification for an online job portal being developed by Avachromians. It outlines the purpose, scope, and overall functions of the system. The system will allow job seekers to search and apply for jobs listed by employers. It will also give employers the ability to list available positions and view applicant resumes. The document defines requirements through use case descriptions and diagrams to illustrate how the different users will interact with the system.
Project Plan And Srs Final

1. The team will spend an estimated 120 days developing the system through initial planning, requirements gathering, design, and testing.
2. Key tasks include writing requirements documents, developing use cases, designing system architecture, and creating test plans and cases.
3. Significant time is allocated for requirements analysis, documentation, reviews, and addressing risks to ensure the system meets stakeholder needs.
Recommended
Software Requirement Specification

The document provides a software requirement specification for a marble factory management system. The system aims to automate the manual processes currently used by The New Fine Marble Factory. Key features include login management, stock process management, adding and dropping employees, and billing management. The system will allow admin access to manage stock records, add or remove inventory items, update employee records, and view all bills. It seeks to save time by automating activities like generating reports and tracking inventory levels.
SENG 6270 - Software-Requirement-Specifications

This document is a software requirements specification for a reprints ordering system. It describes the purpose, scope and functions of the system. The system will allow customers to order photo reprints by selecting options like quantity, size, finish and processing time. It will automatically calculate the total cost and apply any discounts. The document defines requirements for user interfaces, functions, and behaviors of the system. Key requirements include validating user inputs, updating costs in real-time, applying discounts, and generating receipts. The system will be a windows application with a single screen for data entry and order processing.
SOFTWARE REQUIREMENT SPECIFICATION FOR PROJECT

This document provides a project report on developing a "Gate Point Application" android app to provide exam preparation materials for the GATE exam. The app will provide learning content and practice tests for subjects like computer science and electrical engineering. It will also include a syllabus and latest news about the GATE exam. The report outlines the software requirements, including functional requirements like different home screen buttons and sliding menus, as well as non-functional requirements. It presents data flow diagrams and design approaches like the iterative waterfall model. Gantt and PERT charts are also proposed to track the project schedule and dependencies between tasks.
Software engineering project(srs)!!

Jet Messenger v1.0 is a peer to peer LAN messenger which needs no dedicated server for connections and messaging.
Water management portal

The document is a software requirements specification for a Water Management Portal. It includes sections that provide an introduction and overview, describe the overall system and specific requirements. The introduction describes the purpose of creating a web application to allow users to report water-related issues, view information, and allow city employees to update statuses. The overall description outlines the system interfaces, hardware requirements, communication methods, and constraints. It also includes use case and entity relationship diagrams. The specific requirements section describes use cases for different user types: visitors, administrators, city employees and residents.
Software Requirement Specification For Smart Internet Cafe

The document is a software requirements specification for a Smart Internet Cafe (SIC) system. It outlines requirements across many sections - introduction and document conventions, overall descriptions of the system and its users/environment, external interface requirements including the user interface, system features like authentication and monitoring, and non-functional requirements such as performance, security, and special user needs. The SIC will provide secure internet access and account/usage monitoring for clients of internet cafes and college computer labs.
Srs2 Job Portal

The document provides a software requirements specification for an online job portal being developed by Avachromians. It outlines the purpose, scope, and overall functions of the system. The system will allow job seekers to search and apply for jobs listed by employers. It will also give employers the ability to list available positions and view applicant resumes. The document defines requirements through use case descriptions and diagrams to illustrate how the different users will interact with the system.
Project Plan And Srs Final

1. The team will spend an estimated 120 days developing the system through initial planning, requirements gathering, design, and testing.
2. Key tasks include writing requirements documents, developing use cases, designing system architecture, and creating test plans and cases.
3. Significant time is allocated for requirements analysis, documentation, reviews, and addressing risks to ensure the system meets stakeholder needs.
Software Requirements Specification on Student Information System (SRS on SIS)

The document summarizes the inception phase of requirements engineering for developing a Student Information System for the Institute of Information Technology at the University of Dhaka. Key activities in the inception phase included identifying stakeholders such as students, faculty, administrators and alumni; eliciting their requirements through discussions; identifying common and conflicting requirements; and prioritizing requirements to develop an initial set of requirements for the system.
Software Requirements specification for database design of music school manag...

Software Requirements specification for database design of music school manag...Amali Matharaarachchi
This is a sample Software requirement specification (SRS) for a management information system(MIS). SRS for student database management system

This document is a software requirements specification for a student management portal being developed for LNMIIT. It outlines the purpose, scope, functions, users and operating environment of the system. The key functions are to maintain student records and grades, allow students to view their information, and give medical officers and coaches access to relevant health and sports data of students. It will be a web-based system built using Java, PHP and MySQL that can be accessed by around 20 staff, 1 administrator and 150 students concurrently.
Software requirement specification

This document provides a software requirements specification (SRS) for an office automation system. It describes the purpose of the system as automating processes in a college office such as managing student, employee, and transaction data. The SRS outlines functional requirements for modules including attendance, courses, fees, donations, exams, profiles, and reports. It also provides technical requirements for the system such as the needed software (VB.NET and SQL Server), hardware specifications, and user characteristics. Diagrams are included showing the login process and main navigation levels of the system.
Tour guidance srs (Software Requirements Specification)

The document provides a software requirement specification for a mobile framework that generates tour plans to adaptively guide tourists in Sri Lanka. It describes the functional and non-functional requirements of the framework, including use cases for admins to manage users and view feedback, and for users to login, register preferences, get trip suggestions, make payments, and provide feedback. ER and class diagrams are also included to model the business domain.
Data Flow Diagram Example

The document provides steps and an example for creating data flow diagrams (DFDs). It explains that DFDs are constructed at multiple levels, starting with the context level diagram identifying external entities and processes. Then a level 0 diagram identifies sub-processes, and lower level diagrams show actual data flows and data stores. The example demonstrates creating DFDs to model the processes of a lemonade stand at different levels of detail.
Dfd examples

The document describes data flow diagrams (DFDs), including how they differ from flowcharts by showing the flow of data rather than control flow. It then provides steps for creating DFDs using an example of a lemonade stand: 1) List activities, 2) Create a context-level DFD identifying sources and sinks, 3) Create a level 0 DFD identifying subprocesses, and 4) Create level 1 DFDs decomposing subprocesses and identifying data stores.
Payroll Management System SRS

Here is the easy presentation of Software Requirements Specification Model on "Payroll Management System" for employees of a company. It is important for Developing the software for mentioned system. More information you can find after opening the document.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Full-RAG: A modern architecture for hyper-personalization

Mike Del Balso, CEO & Co-Founder at Tecton, presents "Full RAG," a novel approach to AI recommendation systems, aiming to push beyond the limitations of traditional models through a deep integration of contextual insights and real-time data, leveraging the Retrieval-Augmented Generation architecture. This talk will outline Full RAG's potential to significantly enhance personalization, address engineering challenges such as data management and model training, and introduce data enrichment with reranking as a key solution. Attendees will gain crucial insights into the importance of hyperpersonalization in AI, the capabilities of Full RAG for advanced personalization, and strategies for managing complex data integrations for deploying cutting-edge AI solutions.
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
More Related Content
Viewers also liked
Software Requirements Specification on Student Information System (SRS on SIS)

The document summarizes the inception phase of requirements engineering for developing a Student Information System for the Institute of Information Technology at the University of Dhaka. Key activities in the inception phase included identifying stakeholders such as students, faculty, administrators and alumni; eliciting their requirements through discussions; identifying common and conflicting requirements; and prioritizing requirements to develop an initial set of requirements for the system.
Software Requirements specification for database design of music school manag...

Software Requirements specification for database design of music school manag...Amali Matharaarachchi
This is a sample Software requirement specification (SRS) for a management information system(MIS). SRS for student database management system

This document is a software requirements specification for a student management portal being developed for LNMIIT. It outlines the purpose, scope, functions, users and operating environment of the system. The key functions are to maintain student records and grades, allow students to view their information, and give medical officers and coaches access to relevant health and sports data of students. It will be a web-based system built using Java, PHP and MySQL that can be accessed by around 20 staff, 1 administrator and 150 students concurrently.
Software requirement specification

This document provides a software requirements specification (SRS) for an office automation system. It describes the purpose of the system as automating processes in a college office such as managing student, employee, and transaction data. The SRS outlines functional requirements for modules including attendance, courses, fees, donations, exams, profiles, and reports. It also provides technical requirements for the system such as the needed software (VB.NET and SQL Server), hardware specifications, and user characteristics. Diagrams are included showing the login process and main navigation levels of the system.
Tour guidance srs (Software Requirements Specification)

The document provides a software requirement specification for a mobile framework that generates tour plans to adaptively guide tourists in Sri Lanka. It describes the functional and non-functional requirements of the framework, including use cases for admins to manage users and view feedback, and for users to login, register preferences, get trip suggestions, make payments, and provide feedback. ER and class diagrams are also included to model the business domain.
Data Flow Diagram Example

The document provides steps and an example for creating data flow diagrams (DFDs). It explains that DFDs are constructed at multiple levels, starting with the context level diagram identifying external entities and processes. Then a level 0 diagram identifies sub-processes, and lower level diagrams show actual data flows and data stores. The example demonstrates creating DFDs to model the processes of a lemonade stand at different levels of detail.
Dfd examples

The document describes data flow diagrams (DFDs), including how they differ from flowcharts by showing the flow of data rather than control flow. It then provides steps for creating DFDs using an example of a lemonade stand: 1) List activities, 2) Create a context-level DFD identifying sources and sinks, 3) Create a level 0 DFD identifying subprocesses, and 4) Create level 1 DFDs decomposing subprocesses and identifying data stores.
Payroll Management System SRS

Here is the easy presentation of Software Requirements Specification Model on "Payroll Management System" for employees of a company. It is important for Developing the software for mentioned system. More information you can find after opening the document.
Viewers also liked (8)
Software Requirements Specification on Student Information System (SRS on SIS)

Software Requirements Specification on Student Information System (SRS on SIS)
Software Requirements specification for database design of music school manag...

Software Requirements specification for database design of music school manag...
Tour guidance srs (Software Requirements Specification)

Tour guidance srs (Software Requirements Specification)
Recently uploaded
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Full-RAG: A modern architecture for hyper-personalization

Mike Del Balso, CEO & Co-Founder at Tecton, presents "Full RAG," a novel approach to AI recommendation systems, aiming to push beyond the limitations of traditional models through a deep integration of contextual insights and real-time data, leveraging the Retrieval-Augmented Generation architecture. This talk will outline Full RAG's potential to significantly enhance personalization, address engineering challenges such as data management and model training, and introduce data enrichment with reranking as a key solution. Attendees will gain crucial insights into the importance of hyperpersonalization in AI, the capabilities of Full RAG for advanced personalization, and strategies for managing complex data integrations for deploying cutting-edge AI solutions.
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Recently uploaded (20)
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
UiPath Test Automation using UiPath Test Suite series, part 5

UiPath Test Automation using UiPath Test Suite series, part 5
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Full-RAG: A modern architecture for hyper-personalization

Full-RAG: A modern architecture for hyper-personalization
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024