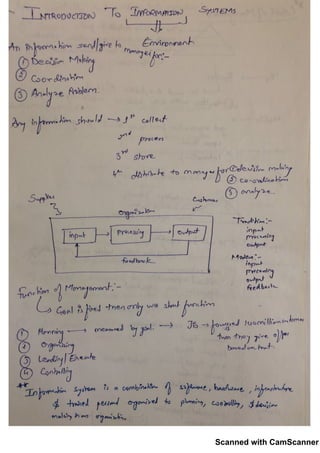
Information System for Managers
•
2 likes•242 views
Contact me if you need any help regarding the Document Email: krishna.khandelwal2010@yahoo.com LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Report
Share
Report
Share
Download to read offline
Recommended
Yag d champ #notes

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $86.57. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Percubaan ups terengganu matematik kertas 1

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $86.27. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Sanjiv bhatt fs

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $63.78. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Pdf riesgos laborales

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $63.27. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Lateral earth pressure

This document appears to be a scanned collection of pages containing text and images. As it is a scan, the document quality makes it difficult to clearly discern the specific content and meaning across all pages. In summary, the document seems to be a multi-page scan containing mixed information that is not easily interpretable due to the scan quality.
MATERIAL ENTREGADO POR EL PROFESOR

This document appears to be a scanned receipt from a restaurant. It shows the date, various food and drink items ordered, subtotals, taxes, and a total amount due. The receipt contains details of a meal purchased at a restaurant on a specific date but does not provide any additional context or information.
Methods for analyzing genome at DNA/RNA/Protein level

This document appears to be a scanned collection of pages containing text and images. As it is a scan, the document quality makes it difficult to clearly discern the specific content and meaning. In summary, the document seems to be a multi-page scan containing mixed information that is unclear due to the scan quality.
Organizational behaviour 01

Contact me if you need to any help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Recommended
Yag d champ #notes

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $86.57. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Percubaan ups terengganu matematik kertas 1

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $86.27. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Sanjiv bhatt fs

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $63.78. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Pdf riesgos laborales

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $63.27. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
Lateral earth pressure

This document appears to be a scanned collection of pages containing text and images. As it is a scan, the document quality makes it difficult to clearly discern the specific content and meaning across all pages. In summary, the document seems to be a multi-page scan containing mixed information that is not easily interpretable due to the scan quality.
MATERIAL ENTREGADO POR EL PROFESOR

This document appears to be a scanned receipt from a restaurant. It shows the date, various food and drink items ordered, subtotals, taxes, and a total amount due. The receipt contains details of a meal purchased at a restaurant on a specific date but does not provide any additional context or information.
Methods for analyzing genome at DNA/RNA/Protein level

This document appears to be a scanned collection of pages containing text and images. As it is a scan, the document quality makes it difficult to clearly discern the specific content and meaning. In summary, the document seems to be a multi-page scan containing mixed information that is unclear due to the scan quality.
Organizational behaviour 01

Contact me if you need to any help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Chemistry module 5

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $86.37. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
“Rupturas Democráticas?” Arlete Moysés Rodrigues

O atual período histórico precisa ser ainda profundamente analisado para podermos compreender as experiências, os avanços e/ou fracassos da democracia no Brasil.
Catalouge BJS 2020 compressed view

This document appears to be a scanned receipt from a grocery store listing various purchased items without any additional context or explanation provided. It contains over a dozen pages of scanned product barcodes and prices, but no other useful information can be gleaned from the visual content alone.
NuevoDocumento 2020-03-23 22.24.34.pdf

This document appears to be a scanned receipt from a restaurant. It shows the date, various food and drink items ordered, subtotals, taxes, and a total amount due of $63.78. The receipt contains details of a meal purchased including appetizers, entrees, drinks and dessert for multiple guests.
Symmetric key cryptography by Divya

This document appears to be a scanned collection of pages containing text and images. As it is a scan, the document quality makes it difficult to clearly discern all of the content. In summary, the document seems to contain various passages of text across multiple pages but the specifics cannot be determined due to the scan quality.
Ht module-3

This document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, along with applicable taxes and a total amount due of $86.61. The receipt details a work lunch for several people that included dishes, drinks, and dessert. It provides a dated record of transaction at the restaurant.
La descripcion

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.82. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining transaction at the specified restaurant on the given date.
Biaxial state of stresses and Mohr Circle

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.82. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining transaction at the specified restaurant on the given date.
Mean Median Mode & Box Plot

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.82. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining experience at the restaurant for multiple guests.
Janjang Add Maths 

The document appears to be a scanned receipt from a restaurant in San Francisco. It shows the date, various food and drink items ordered, discounts applied, subtotals, taxes, and a total amount due of $167.76. The receipt contains details of a meal at the restaurant but does not provide any additional context around the purpose or participants of the meal.
Ac fr ogbaoeh0qqsd3_wm8x0_uju4_twwibo-cr1cvo5rlpcmemqvoqv32nnefwdtcxfiywflq82...

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.78. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining experience at the restaurant for multiple guests.
Marketing management

Contact me if you need to help regarding document
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Diagnostic complete ppt

The document appears to be a scanned receipt from a grocery store listing various food and household items purchased totaling $123.45. It includes the store name, date, time of purchase, payment method and signature of the cashier. The receipt provides details of the transaction including item names, quantities, prices and total amount paid.
MPF denuncia organizador de “tomataço” conta Gilmar Mendes

The document appears to be a scanned receipt from a grocery store listing various food and household items purchased totaling $123.45. It includes the store name, date, time of purchase, payment method and signature of the cashier. The receipt provides details of the transaction including item names, quantities, prices and total amount paid.
Shear Stresses in Beams

Calculation of Moment of Inertia for various section, Problems on bending stresses, and concept of shear stresses in beams
Organizational behaviour 02

Contact me if you need to help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Interview Techniques - While applying for job

The document provides tips for job applicants on preparing resumes and following up with recruiters. It advises to ensure resumes are free of flaws, tailored to each job, and highlight relevant skills and keywords. Cover letters should specifically address why the applicant fits the role. When following up, timing is important - wait 1-2 weeks before contacting a recruiter, as responses can take longer for junior versus senior roles, and non-responses may mean the applicant is not the top candidate. Recruiters may also keep profiles on file without immediate openings.
Interview Techniques - Before applying for job

Networking through friends and former colleagues is the best way to look for opportunities, rather than randomly searching online or sending unsolicited emails. It is important to have the right skills for the job and understand how your skills align with the company's needs and vision. Candidates should thoroughly review all social media profiles and ensure information is consistent across platforms, as many employers will research candidates online and unprofessional content could deter hiring.
Interview Techniques - After the Interview

Changing expectations after an interview reflects badly on the candidate and increases chances of rejection. Proper market research on prevailing rates for the role and location is important before an interview to avoid expressing unrealistic expectations during negotiations. Candidates should also follow up if not contacted after an interview, thank recruiters for their time, and stay connected on professional networks even if not selected in order to maintain positive relationships.
Interview Techniques - During the interview

This document provides tips for phone interviews and in-person interactions. For phone interviews, candidates should keep an relaxed tone, take notes of their questions, and avoid multitasking. During interactions, candidates should prepare about themselves and the company, do research on the company, remain humble and polite without seeming nervous. Candidates should ask the right questions without dominating the conversation. For in-person interviews, candidates should make eye contact, arrive on time, dress neatly to convey seriousness, avoid unkempt appearance, and remain attentive with an appropriate energy level.
Analysis of Quarterly Results

This document tell you information for how to analyze the quarter results of the company. Quarter results published by company , in which they showcase their performance to shareholders and analyst.
Stocks - Corporate Action

This documents tell about various stocks corporate action such as Rights issue, Bonus Share, Stocks Split, Dividend and Share Buyback.
More Related Content
What's hot
Chemistry module 5

This document appears to be a scanned receipt from a restaurant. It lists various food and drink items purchased, applicable taxes, and a total amount due of $86.37. The receipt includes the restaurant's name, address, phone number, and what appears to be a signature from the customer at the bottom.
“Rupturas Democráticas?” Arlete Moysés Rodrigues

O atual período histórico precisa ser ainda profundamente analisado para podermos compreender as experiências, os avanços e/ou fracassos da democracia no Brasil.
Catalouge BJS 2020 compressed view

This document appears to be a scanned receipt from a grocery store listing various purchased items without any additional context or explanation provided. It contains over a dozen pages of scanned product barcodes and prices, but no other useful information can be gleaned from the visual content alone.
NuevoDocumento 2020-03-23 22.24.34.pdf

This document appears to be a scanned receipt from a restaurant. It shows the date, various food and drink items ordered, subtotals, taxes, and a total amount due of $63.78. The receipt contains details of a meal purchased including appetizers, entrees, drinks and dessert for multiple guests.
Symmetric key cryptography by Divya

This document appears to be a scanned collection of pages containing text and images. As it is a scan, the document quality makes it difficult to clearly discern all of the content. In summary, the document seems to contain various passages of text across multiple pages but the specifics cannot be determined due to the scan quality.
Ht module-3

This document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, along with applicable taxes and a total amount due of $86.61. The receipt details a work lunch for several people that included dishes, drinks, and dessert. It provides a dated record of transaction at the restaurant.
La descripcion

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.82. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining transaction at the specified restaurant on the given date.
Biaxial state of stresses and Mohr Circle

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.82. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining transaction at the specified restaurant on the given date.
Mean Median Mode & Box Plot

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.82. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining experience at the restaurant for multiple guests.
Janjang Add Maths 

The document appears to be a scanned receipt from a restaurant in San Francisco. It shows the date, various food and drink items ordered, discounts applied, subtotals, taxes, and a total amount due of $167.76. The receipt contains details of a meal at the restaurant but does not provide any additional context around the purpose or participants of the meal.
Ac fr ogbaoeh0qqsd3_wm8x0_uju4_twwibo-cr1cvo5rlpcmemqvoqv32nnefwdtcxfiywflq82...

The document appears to be a scanned receipt from a restaurant in New York City listing various food and drink items purchased, with a total amount due of $167.78. It includes the restaurant's name, date, time, table number, and lists items such as cocktails, appetizers, entrees, desserts, and a 20% service charge. The receipt provides details of a dining experience at the restaurant for multiple guests.
Marketing management

Contact me if you need to help regarding document
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Diagnostic complete ppt

The document appears to be a scanned receipt from a grocery store listing various food and household items purchased totaling $123.45. It includes the store name, date, time of purchase, payment method and signature of the cashier. The receipt provides details of the transaction including item names, quantities, prices and total amount paid.
MPF denuncia organizador de “tomataço” conta Gilmar Mendes

The document appears to be a scanned receipt from a grocery store listing various food and household items purchased totaling $123.45. It includes the store name, date, time of purchase, payment method and signature of the cashier. The receipt provides details of the transaction including item names, quantities, prices and total amount paid.
Shear Stresses in Beams

Calculation of Moment of Inertia for various section, Problems on bending stresses, and concept of shear stresses in beams
Organizational behaviour 02

Contact me if you need to help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
What's hot (16)
Ac fr ogbaoeh0qqsd3_wm8x0_uju4_twwibo-cr1cvo5rlpcmemqvoqv32nnefwdtcxfiywflq82...

Ac fr ogbaoeh0qqsd3_wm8x0_uju4_twwibo-cr1cvo5rlpcmemqvoqv32nnefwdtcxfiywflq82...
MPF denuncia organizador de “tomataço” conta Gilmar Mendes

MPF denuncia organizador de “tomataço” conta Gilmar Mendes
More from Krishna Khandelwal
Interview Techniques - While applying for job

The document provides tips for job applicants on preparing resumes and following up with recruiters. It advises to ensure resumes are free of flaws, tailored to each job, and highlight relevant skills and keywords. Cover letters should specifically address why the applicant fits the role. When following up, timing is important - wait 1-2 weeks before contacting a recruiter, as responses can take longer for junior versus senior roles, and non-responses may mean the applicant is not the top candidate. Recruiters may also keep profiles on file without immediate openings.
Interview Techniques - Before applying for job

Networking through friends and former colleagues is the best way to look for opportunities, rather than randomly searching online or sending unsolicited emails. It is important to have the right skills for the job and understand how your skills align with the company's needs and vision. Candidates should thoroughly review all social media profiles and ensure information is consistent across platforms, as many employers will research candidates online and unprofessional content could deter hiring.
Interview Techniques - After the Interview

Changing expectations after an interview reflects badly on the candidate and increases chances of rejection. Proper market research on prevailing rates for the role and location is important before an interview to avoid expressing unrealistic expectations during negotiations. Candidates should also follow up if not contacted after an interview, thank recruiters for their time, and stay connected on professional networks even if not selected in order to maintain positive relationships.
Interview Techniques - During the interview

This document provides tips for phone interviews and in-person interactions. For phone interviews, candidates should keep an relaxed tone, take notes of their questions, and avoid multitasking. During interactions, candidates should prepare about themselves and the company, do research on the company, remain humble and polite without seeming nervous. Candidates should ask the right questions without dominating the conversation. For in-person interviews, candidates should make eye contact, arrive on time, dress neatly to convey seriousness, avoid unkempt appearance, and remain attentive with an appropriate energy level.
Analysis of Quarterly Results

This document tell you information for how to analyze the quarter results of the company. Quarter results published by company , in which they showcase their performance to shareholders and analyst.
Stocks - Corporate Action

This documents tell about various stocks corporate action such as Rights issue, Bonus Share, Stocks Split, Dividend and Share Buyback.
Portfolio strategy

Different type of strategy followed by investor to invest in stocks market. basically 3 type of strategy generally followed which are Dividend Investing , Buy and Hold Investing and Trend Investing
Economic Moat

An economic moat refers to a company's ability to maintain competitive advantages and protect its profits and market share from competitors over the long run. The document outlines several types of economic moats that can provide advantages, including high switching costs for customers, efficient scaling, low cost production, network effects from larger user bases, and strong intangible assets like patents and trademarks.
Personal Finance

This document talks about how to manage money,do budgeting,tracking expenses and creating investment portfolio.
Financial Derivative

This document tell about Basics of Financial Derivatives.It Focus on Forwards , Futures , Option - Call Option and Put Options, and Swaps
Leverage

Financial Management - Leverage
For Academics Use
For Any queries please contact the email id mentioned in file
Logistics regression

Logistics Regression
MBA , Business Analysis Problems ,For Academics Use
For any queries contact at below email id
krishna.khandelwal2010@yahoo.com
Multiple Regression

Business Analytics , MBA , Academics use only , Multiple Regression
For Any Queries , Contact at below email id
krishna.khandelwal2010@yahoo.com
Factor Analysis

Factor Analysis Numerical and Solution , MBA , Analytics , Data Analysis , Marketing Analytics , Business Analytics , For Academics use only.
For any Queries
Email me at : krishna.khandelwal2010@yahoo.com
Rupee vs dollar

Weakening Rupee Impact in Indian Economy. Industries which get impact due to weak rupee or strong rupee.
MBA , Placements, Academics Use ,
RBI and Indian Govt Tussle 

The document summarizes tensions between the Reserve Bank of India (RBI) and the Indian government over several issues: interest rates, dividend payments, loan restructuring, regulation of public sector banks, corrective action for struggling banks, payments regulation, board appointments, liquidity support for non-banking financial companies, foreign exchange reserves, and more. Key points of contention have been the RBI's refusal to cut interest rates as desired by the government, lower than expected dividend payments from the RBI to the government, and the RBI's regulatory actions around struggling banks which put pressure on the government.
Consumer market

Contact me if you need any help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Marketing Management - Pricing

Contact me if you need any help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
Introduction to product

This document appears to be a scanned receipt from a restaurant showing the date, various food and drink items ordered, prices, tax amount, and total due. It provides details of a dining experience at a restaurant including multiple menu items that were purchased and the overall cost of the meal including tax. The receipt shows a breakdown of the charges for accounting purposes.
Market positioning

Contact me if you need any help
Email: krishna.khandelwal2010@yahoo.com
LinkedIn: https://www.linkedin.com/in/krishna-khandelwal-57656a85/
More from Krishna Khandelwal (20)
Recently uploaded
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
AWS Cloud Cost Optimization Presentation.pptx

This presentation provides valuable insights into effective cost-saving techniques on AWS. Learn how to optimize your AWS resources by rightsizing, increasing elasticity, picking the right storage class, and choosing the best pricing model. Additionally, discover essential governance mechanisms to ensure continuous cost efficiency. Whether you are new to AWS or an experienced user, this presentation provides clear and practical tips to help you reduce your cloud costs and get the most out of your budget.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Azure API Management to expose backend services securely

How to use Azure API Management to expose backend service securely
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on integration of Salesforce with Bonterra Impact Management.
Interested in deploying an integration with Salesforce for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Astute Business Solutions | Oracle Cloud Partner |

Your goto partner for Oracle Cloud, PeopleSoft, E-Business Suite, and Ellucian Banner. We are a firm specialized in managed services and consulting.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI, built on the robust SAP Business Technology Platform (SAP BTP), is the latest and most advanced version of our AI development, reaffirming our commitment to delivering top-tier AI solutions. Skybuffer AI harnesses all the innovative capabilities of the SAP BTP in the AI domain, from Conversational AI to cutting-edge Generative AI and Retrieval-Augmented Generation (RAG). It also helps SAP customers safeguard their investments into SAP Conversational AI and ensure a seamless, one-click transition to SAP Business AI.
With Skybuffer AI, various AI models can be integrated into a single communication channel such as Microsoft Teams. This integration empowers business users with insights drawn from SAP backend systems, enterprise documents, and the expansive knowledge of Generative AI. And the best part of it is that it is all managed through our intuitive no-code Action Server interface, requiring no extensive coding knowledge and making the advanced AI accessible to more users.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
FREE A4 Cyber Security Awareness Posters-Social Engineering part 3

Free A4 downloadable and printable Cyber Security, Social Engineering Safety and security Training Posters . Promote security awareness in the home or workplace. Lock them Out From training providers datahops.com
Recently uploaded (20)
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Azure API Management to expose backend services securely

Azure API Management to expose backend services securely
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Astute Business Solutions | Oracle Cloud Partner |

Astute Business Solutions | Oracle Cloud Partner |
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
FREE A4 Cyber Security Awareness Posters-Social Engineering part 3

FREE A4 Cyber Security Awareness Posters-Social Engineering part 3
WeTestAthens: Postman's AI & Automation Techniques

WeTestAthens: Postman's AI & Automation Techniques