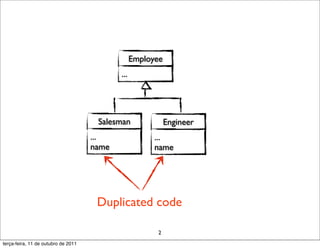
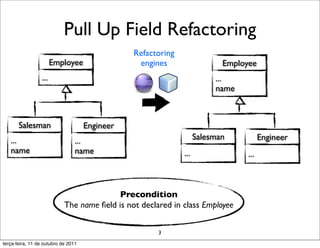
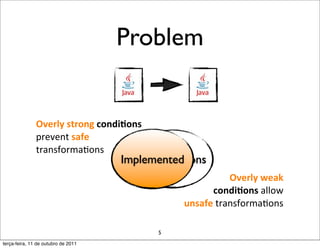
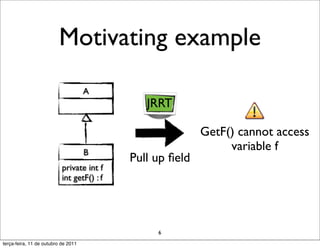
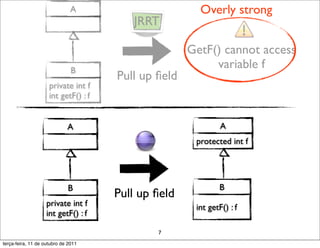
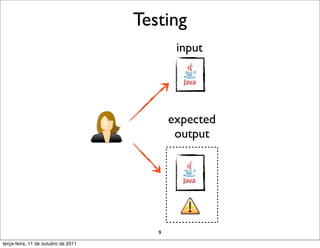
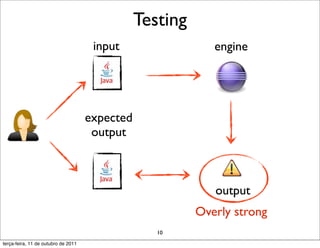
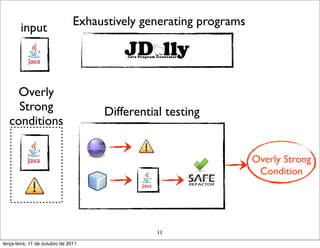
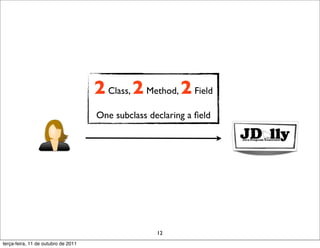
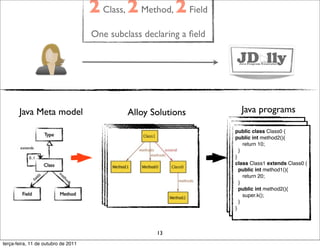
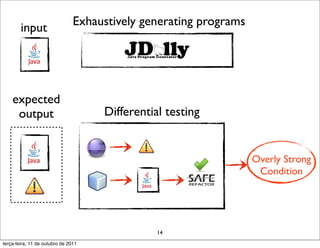
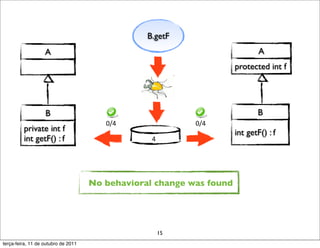
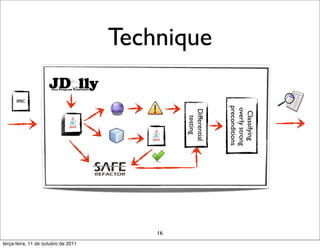
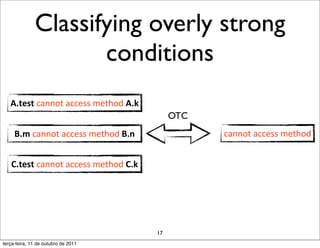
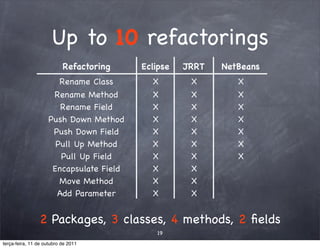
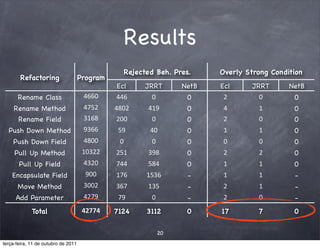
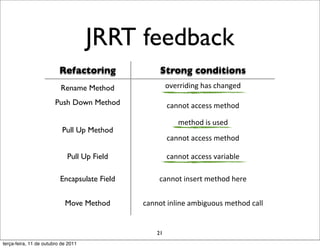
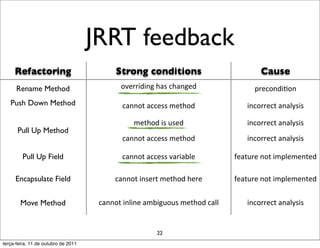
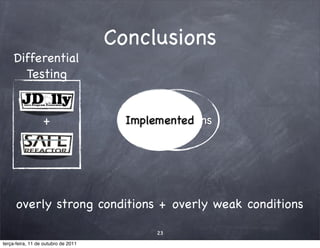
The document discusses the identification of overly strong conditions in refactoring implementations, which can lead to unsafe transformations and difficulties in specifying preconditions. It evaluates methods across multiple refactoring engines, highlighting issues found through differential testing. The authors present conclusions regarding the balance of strong and weak preconditions in refactoring processes.