Hazard Assesments
•Download as DOC, PDF•
1 like•196 views
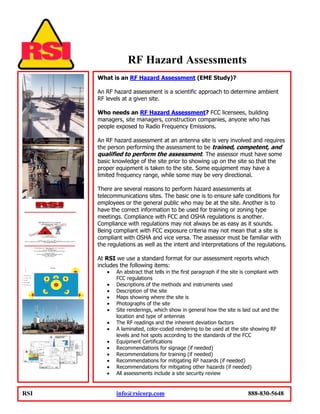
An RF hazard assessment determines ambient RF levels at a site. FCC licensees, building managers, and others with people exposed to RF emissions may need an assessment. Assessments require a trained assessor using specialized equipment. Assessments ensure safety for employees and the public, and compliance with FCC and OSHA regulations. RSI's assessment reports include RF readings, site maps and photos, recommendations, and a site security review.
Report
Share
Report
Share
Recommended
Lieblingskaro Katalog 2012/2013

Lieblingskaro-Katalog 2012/2013: Kinderzimmer-Einrichtung, Bettwäsche und Spielzeug im Karo-Look. Designed und hergestellt in Berlin, Deutschland.
Recommended
Lieblingskaro Katalog 2012/2013

Lieblingskaro-Katalog 2012/2013: Kinderzimmer-Einrichtung, Bettwäsche und Spielzeug im Karo-Look. Designed und hergestellt in Berlin, Deutschland.
Wac 2011 Overview And Highlights

Overview and Highlights of Wireless Applications\' Services and Software offerings.
Wac 2011 Overview And Highlights

Wireless Applications, Corp. - 2011 Highlighted Products and Services
Wac Software Services 2011

Wireless Applications, Corp. provides valuable products and
services for cellular, PCS, and broadband wireless industries.
ATI Laser RADAR and Applications Training for Advanced Students Course Sampler

Major technology advancements in Laser Radar (LADAR) have made a profound new impact on future mobile, airborne and space-based missions. In an effort to cope with problems such as target clutter, battlefield commanders require a new breed of LADAR, consisting of new programs such as Jigsaw and True 3D Flash. New LADAR systems and applications are currently in development, and will be based on entirely new technology, which has not been feasible until just now. These new LADAR technologies will support the Service-wide drive for a Single Integrated Air Picture (SIAP), which provides military forces access to reliable information about ground, air, space or undersea threats in any given theater of operations to achieve total theater air dominance. Developmental challenges are vast for LADAR and opportunities for industry involvement appear to be endless.
Review the steps found in business process engineering. Review the.docx

Review the steps found in business process engineering. Review the lesson presentation and assigned readings. Post the step you think could be altered and explain why. Respond to the following and, if appropriate, include personal experiences as part of your answer:
• Briefly summarize the steps in business process engineering.
• Identify one step that you think can be altered and describe how you would change it.
• Explain your reasoning for the altering this step and how it would affect the end result of the business process.
(Optional) Use the Internet to research the airline industry. Select an airline company. Be sure to identify where its major activities fall within Porter's generic value chain.
Post at least two activities (processes) of the airline under the correct value chain activity below and justify why it belongs in that activity.
• Inbound Logistics (Primary Activity)
• Operations/Manufacturing (Primary Activity)
• Outbound Logistics (Primary Activity)
• Sales & Marketing (Primary Activity)
• Customer Service (Primary Activity)
• Procurement (Support Activity)
• Technology (Support Activity)
• Human Resources (Support Activity)
• Accounting & Finance (Support Activity)
Network Security
Due date:
Week 6, 14th April
ASSESSMENT
Weighting:
80%
1
Length:
N/A
Question 1 (5 marks)
Note: for this question, you need to download a PCAP file located in the course Moodle web site.
Peter is the Network Security Manager for a small spare parts business. The organisation uses an e-sales application to provide a front-end for its e-sales business. Customers are complaining that in the last two or three days the system has become very slow, taking them longer than normal to place their orders. This information has been corroborated by staff complaining that they are not happy with the slow response of the system to complete their daily activities. Peter suspects that the system has been the target of criminal hands and before he starts responding to the attack, he decides to investigate the issue a little further. First, he reviews the firewall logs and notices something abnormal in the type of traffic directed to a number of internal hosts including the organisation’s web server. Curious about this traffic, Peter uses Wireshark to capture a trace of the traffic. [A section of this trace can be accessed from the course Moodle web site].
Based on the above fictional scenario and the provided PCAP:
(a) Identify the anomaly in the traffic this organisation is going through (1/2 Mark). What sort of evidence do you have to make this claim? (1. 0 Marks).
(b) What sort of utility or tool do you think the “attacker” is using to conduct this attack? (1/2 mark)
(c) Provide the IP address of the host used by the perpetrator (1/2 Mark). Based on this information, what can you tell about the profile of this individual? Explain why (1.5 Marks).
(d) What Wireshark filter do you think Peter used to produce the given PCAP? Explain why (1 Mar ...
Wireless Applications Corp 2010 Overview

Wireless Applications, Corp. Overview and Highlight Presentation
RF Training Fundamentals

https://www.enoinstitute.com/product/rf-training-fundamentals-workshop/ - RF Training Fundamentals; RF, also known as Radio Frequency is incorporated into almost everything that transmits or receives a radio wave which including amateur radio, Cell Phones: GSM, CDMA, UMTS, LTE, LTE-Advanced, Wi-Fi, Bluetooth, Zigbee, RFID, NFC, medical devices, GPS, Microwave, Satellite Communications, Radar, Public Safety and more. RF Training course gives you the expertise needed to plan, design, optimize and manage effective and reliable RF and wireless solutions. An in-depth knowledge of mathematics, physics and general electronics theory is covered.
RF Training - RESOURCES:
RF Training Study Guide by Klaus Finkenzeller - Hardcover/Amazon
RF Training Study Guide by U.S. Navy - Paperback/Amazon
RF Training Study Guide by Naval Education & Training Center - Paperback/Amazon
RF Training Study Guide by Klaus Finkenzeller – Paperback/Amazon
RF Training Prep Guide by Cotter Sayre – Paperback/Amazon
RF Training Study Guide by bWHITE SANDS MISSILE RANGE, NEVADA TEST SITE, et al - Loose Leaf/Amazon
RF Training Study Guide by Naval Education and Training Command - Amazon Paperback
RF Training Study Guide by United States Navy - Paperback/Kindle Amazon
RF Training Study Guide by U.S. Navy – Kindle/ Amazon
RF Training Study Guide by Edward Balkovich – Paperback / Amazon
RF Training Study Guide by U.S. Navy – Loose Leaf/ Amazon
Radio Frequency Training Study Guide by ARRL Inc. and Walter Banzhaf WB1ANE - Kindle/Paperback/ Amazon
Radio Frequency Training Study Guide by ZHOU ZHI PING ZHU SUN ZI WEN – Paperback/Amazon
Radio Frequency by U.S. Air Force Kindle /Paperback/ Amazon
Radio Frequency Training by Lamont V. Blake and Maurice W. Long – Paperback/ Kindle/Amazon
Radio Frequency Training Study Guide by Patrick J. Sweeney - Paperback/Amazon
CSSLP Certification Training by Mark Brown, Sam Patadia, et al. – Kindle/Paperback/Amazon
CSSLP Certification Training by Headquarters Department of the Army – Paperback/Amazon
RF TRAINING FUNDAMENTALS WORKSHOP – CUSTOMIZE It::
We can adapt this training course to your group’s background and work requirements at little to no added cost.
If you are familiar with some aspects of this RF Training Fundamentals course, we can omit or shorten their discussion.
We can adjust the emphasis placed on the various topics or build the training around the mix of technologies of interest to you (including technologies other than those included in this outline).
If your background is nontechnical, we can exclude the more technical topics, include the topics that may be of special interest to you (e.g., as a manager or policy-maker), and present the RF Training Fundamentals course in manner understandable to lay audiences.
WAC, Its Dirt Simple

Its Dirt Simple. We have both wireless Telecom consulting services and Software tools that rival all. Over the many years of development, we invite you to see just what might excite you, whether you own the company, work for the company or invest in it.
Just out our Telecom API Suite and see how easy it is to take our tools and integrate straight into your products.
IntroductionThe capstone project is a �structured walkthrough� pen.pdf

Introduction
The capstone project is a structured walkthrough penetration test of a fictional
company, Artemis, Incorporated (Artemis). A structured walkthrough is an
organized procedure for a group of peers to review and discuss the technical
aspects of various IT, IT Security, and IT Audit work products. The major objectives
of a structured walkthrough are to find errors and to improve the quality of the
product or service to be delivered.
This document provides a comprehensive overview of the project and the expected
deliverables.
Overview
You work for a firm specializing in cybersecurity consulting, namely penetration tests,
vulnerability assessments, and regulatory compliance. Artemis has hired your firm to
perform an external penetration test. In preparation for this engagement, you must lead
your team of new pen-testers in a structured walkthrough of the entire test so that:
a) Everyone on the team knows what to do.
b) The amount of time allotted for the actual test is utilized as efficiently as
possible.
c) The clients expectations are met or exceeded.
To accomplish this task, you must perform the following five phases:
1. Perform simulated reconnaissance of the client.
2. Simulate target identification and scans against the external network.
3. Simulate the identification of vulnerabilities.
4. Based on the above, assess the threats and make recommendations.
5. Create two mock reports for the client: An Executive Summary for the clients
senior management, and a Detailed Technical Report for the clients IT staff.
This project is an excellent addition to your portfolio as it demonstrates your
understanding of critical security issues and your skills in identifying and analyzing
threats and vulnerabilities. The project also allows you to speak knowledgeably about
the entire process of performing a pen test, using your project as a reference point.
Each phase will include its own deliverable(s). A full description of what is required can
be found under each phase.
Directions
When planning penetration tests, consulting firms always sit down with the clients key
stakeholders to confirm scope and approach, identify the clients concerns, and set
expectations regarding the outcome. To this end, you have been provided with an
overview of the client and an overview of the clients IT environment. This information is
critical because all risks must be evaluated within their context. The example below
illustrates this concept:
Technically Accurate Artemis web application does not restrict or filter user uploads
by file type. This is a vulnerability that could allow threat actors to connect remotely,
execute arbitrary code, and then elevate their privileges within the application.
With context Artemis RFQ/RFP web application does not restrict or filter user uploads
by file type. This is a vulnerability that could allow threat actors to connect remotely,
execute arbitrary code, and then elevate their privileges within the application. In this
instan.
More Related Content
Similar to Hazard Assesments
Wac 2011 Overview And Highlights

Overview and Highlights of Wireless Applications\' Services and Software offerings.
Wac 2011 Overview And Highlights

Wireless Applications, Corp. - 2011 Highlighted Products and Services
Wac Software Services 2011

Wireless Applications, Corp. provides valuable products and
services for cellular, PCS, and broadband wireless industries.
ATI Laser RADAR and Applications Training for Advanced Students Course Sampler

Major technology advancements in Laser Radar (LADAR) have made a profound new impact on future mobile, airborne and space-based missions. In an effort to cope with problems such as target clutter, battlefield commanders require a new breed of LADAR, consisting of new programs such as Jigsaw and True 3D Flash. New LADAR systems and applications are currently in development, and will be based on entirely new technology, which has not been feasible until just now. These new LADAR technologies will support the Service-wide drive for a Single Integrated Air Picture (SIAP), which provides military forces access to reliable information about ground, air, space or undersea threats in any given theater of operations to achieve total theater air dominance. Developmental challenges are vast for LADAR and opportunities for industry involvement appear to be endless.
Review the steps found in business process engineering. Review the.docx

Review the steps found in business process engineering. Review the lesson presentation and assigned readings. Post the step you think could be altered and explain why. Respond to the following and, if appropriate, include personal experiences as part of your answer:
• Briefly summarize the steps in business process engineering.
• Identify one step that you think can be altered and describe how you would change it.
• Explain your reasoning for the altering this step and how it would affect the end result of the business process.
(Optional) Use the Internet to research the airline industry. Select an airline company. Be sure to identify where its major activities fall within Porter's generic value chain.
Post at least two activities (processes) of the airline under the correct value chain activity below and justify why it belongs in that activity.
• Inbound Logistics (Primary Activity)
• Operations/Manufacturing (Primary Activity)
• Outbound Logistics (Primary Activity)
• Sales & Marketing (Primary Activity)
• Customer Service (Primary Activity)
• Procurement (Support Activity)
• Technology (Support Activity)
• Human Resources (Support Activity)
• Accounting & Finance (Support Activity)
Network Security
Due date:
Week 6, 14th April
ASSESSMENT
Weighting:
80%
1
Length:
N/A
Question 1 (5 marks)
Note: for this question, you need to download a PCAP file located in the course Moodle web site.
Peter is the Network Security Manager for a small spare parts business. The organisation uses an e-sales application to provide a front-end for its e-sales business. Customers are complaining that in the last two or three days the system has become very slow, taking them longer than normal to place their orders. This information has been corroborated by staff complaining that they are not happy with the slow response of the system to complete their daily activities. Peter suspects that the system has been the target of criminal hands and before he starts responding to the attack, he decides to investigate the issue a little further. First, he reviews the firewall logs and notices something abnormal in the type of traffic directed to a number of internal hosts including the organisation’s web server. Curious about this traffic, Peter uses Wireshark to capture a trace of the traffic. [A section of this trace can be accessed from the course Moodle web site].
Based on the above fictional scenario and the provided PCAP:
(a) Identify the anomaly in the traffic this organisation is going through (1/2 Mark). What sort of evidence do you have to make this claim? (1. 0 Marks).
(b) What sort of utility or tool do you think the “attacker” is using to conduct this attack? (1/2 mark)
(c) Provide the IP address of the host used by the perpetrator (1/2 Mark). Based on this information, what can you tell about the profile of this individual? Explain why (1.5 Marks).
(d) What Wireshark filter do you think Peter used to produce the given PCAP? Explain why (1 Mar ...
Wireless Applications Corp 2010 Overview

Wireless Applications, Corp. Overview and Highlight Presentation
RF Training Fundamentals

https://www.enoinstitute.com/product/rf-training-fundamentals-workshop/ - RF Training Fundamentals; RF, also known as Radio Frequency is incorporated into almost everything that transmits or receives a radio wave which including amateur radio, Cell Phones: GSM, CDMA, UMTS, LTE, LTE-Advanced, Wi-Fi, Bluetooth, Zigbee, RFID, NFC, medical devices, GPS, Microwave, Satellite Communications, Radar, Public Safety and more. RF Training course gives you the expertise needed to plan, design, optimize and manage effective and reliable RF and wireless solutions. An in-depth knowledge of mathematics, physics and general electronics theory is covered.
RF Training - RESOURCES:
RF Training Study Guide by Klaus Finkenzeller - Hardcover/Amazon
RF Training Study Guide by U.S. Navy - Paperback/Amazon
RF Training Study Guide by Naval Education & Training Center - Paperback/Amazon
RF Training Study Guide by Klaus Finkenzeller – Paperback/Amazon
RF Training Prep Guide by Cotter Sayre – Paperback/Amazon
RF Training Study Guide by bWHITE SANDS MISSILE RANGE, NEVADA TEST SITE, et al - Loose Leaf/Amazon
RF Training Study Guide by Naval Education and Training Command - Amazon Paperback
RF Training Study Guide by United States Navy - Paperback/Kindle Amazon
RF Training Study Guide by U.S. Navy – Kindle/ Amazon
RF Training Study Guide by Edward Balkovich – Paperback / Amazon
RF Training Study Guide by U.S. Navy – Loose Leaf/ Amazon
Radio Frequency Training Study Guide by ARRL Inc. and Walter Banzhaf WB1ANE - Kindle/Paperback/ Amazon
Radio Frequency Training Study Guide by ZHOU ZHI PING ZHU SUN ZI WEN – Paperback/Amazon
Radio Frequency by U.S. Air Force Kindle /Paperback/ Amazon
Radio Frequency Training by Lamont V. Blake and Maurice W. Long – Paperback/ Kindle/Amazon
Radio Frequency Training Study Guide by Patrick J. Sweeney - Paperback/Amazon
CSSLP Certification Training by Mark Brown, Sam Patadia, et al. – Kindle/Paperback/Amazon
CSSLP Certification Training by Headquarters Department of the Army – Paperback/Amazon
RF TRAINING FUNDAMENTALS WORKSHOP – CUSTOMIZE It::
We can adapt this training course to your group’s background and work requirements at little to no added cost.
If you are familiar with some aspects of this RF Training Fundamentals course, we can omit or shorten their discussion.
We can adjust the emphasis placed on the various topics or build the training around the mix of technologies of interest to you (including technologies other than those included in this outline).
If your background is nontechnical, we can exclude the more technical topics, include the topics that may be of special interest to you (e.g., as a manager or policy-maker), and present the RF Training Fundamentals course in manner understandable to lay audiences.
WAC, Its Dirt Simple

Its Dirt Simple. We have both wireless Telecom consulting services and Software tools that rival all. Over the many years of development, we invite you to see just what might excite you, whether you own the company, work for the company or invest in it.
Just out our Telecom API Suite and see how easy it is to take our tools and integrate straight into your products.
IntroductionThe capstone project is a �structured walkthrough� pen.pdf

Introduction
The capstone project is a structured walkthrough penetration test of a fictional
company, Artemis, Incorporated (Artemis). A structured walkthrough is an
organized procedure for a group of peers to review and discuss the technical
aspects of various IT, IT Security, and IT Audit work products. The major objectives
of a structured walkthrough are to find errors and to improve the quality of the
product or service to be delivered.
This document provides a comprehensive overview of the project and the expected
deliverables.
Overview
You work for a firm specializing in cybersecurity consulting, namely penetration tests,
vulnerability assessments, and regulatory compliance. Artemis has hired your firm to
perform an external penetration test. In preparation for this engagement, you must lead
your team of new pen-testers in a structured walkthrough of the entire test so that:
a) Everyone on the team knows what to do.
b) The amount of time allotted for the actual test is utilized as efficiently as
possible.
c) The clients expectations are met or exceeded.
To accomplish this task, you must perform the following five phases:
1. Perform simulated reconnaissance of the client.
2. Simulate target identification and scans against the external network.
3. Simulate the identification of vulnerabilities.
4. Based on the above, assess the threats and make recommendations.
5. Create two mock reports for the client: An Executive Summary for the clients
senior management, and a Detailed Technical Report for the clients IT staff.
This project is an excellent addition to your portfolio as it demonstrates your
understanding of critical security issues and your skills in identifying and analyzing
threats and vulnerabilities. The project also allows you to speak knowledgeably about
the entire process of performing a pen test, using your project as a reference point.
Each phase will include its own deliverable(s). A full description of what is required can
be found under each phase.
Directions
When planning penetration tests, consulting firms always sit down with the clients key
stakeholders to confirm scope and approach, identify the clients concerns, and set
expectations regarding the outcome. To this end, you have been provided with an
overview of the client and an overview of the clients IT environment. This information is
critical because all risks must be evaluated within their context. The example below
illustrates this concept:
Technically Accurate Artemis web application does not restrict or filter user uploads
by file type. This is a vulnerability that could allow threat actors to connect remotely,
execute arbitrary code, and then elevate their privileges within the application.
With context Artemis RFQ/RFP web application does not restrict or filter user uploads
by file type. This is a vulnerability that could allow threat actors to connect remotely,
execute arbitrary code, and then elevate their privileges within the application. In this
instan.
Similar to Hazard Assesments (20)
Proposal to Manage the Upgrade of the IT Infrastructure for PPESA

Proposal to Manage the Upgrade of the IT Infrastructure for PPESA
ATI Laser RADAR and Applications Training for Advanced Students Course Sampler

ATI Laser RADAR and Applications Training for Advanced Students Course Sampler
Conducting site surveys for wlan performance and reliability

Conducting site surveys for wlan performance and reliability
Review the steps found in business process engineering. Review the.docx

Review the steps found in business process engineering. Review the.docx
IntroductionThe capstone project is a �structured walkthrough� pen.pdf

IntroductionThe capstone project is a �structured walkthrough� pen.pdf
More from Maranda_Barnes
More from Maranda_Barnes (7)
Hazard Assesments
- 1. RF Hazard Assessments What is an RF Hazard Assessment (EME Study)? An RF hazard assessment is a scientific approach to determine ambient RF levels at a given site. Who needs an RF Hazard Assessment? FCC licensees, building managers, site managers, construction companies, anyone who has people exposed to Radio Frequency Emissions. An RF hazard assessment at an antenna site is very involved and requires the person performing the assessment to be trained, competent, and qualified to perform the assessment. The assessor must have some basic knowledge of the site prior to showing up on the site so that the proper equipment is taken to the site. Some equipment may have a limited frequency range, while some may be very directional. There are several reasons to perform hazard assessments at telecommunications sites. The basic one is to ensure safe conditions for employees or the general public who may be at the site. Another is to have the correct information to be used for training or zoning type meetings. Compliance with FCC and OSHA regulations is another. Compliance with regulations may not always be as easy as it sounds. Being compliant with FCC exposure criteria may not mean that a site is compliant with OSHA and vice versa. The assessor must be familiar with the regulations as well as the intent and interpretations of the regulations. At RSI we use a standard format for our assessment reports which includes the following items: An abstract that tells in the first paragraph if the site is compliant with FCC regulations Descriptions of the methods and instruments used Description of the site Maps showing where the site is Photographs of the site Site renderings, which show in general how the site is laid out and the location and type of antennas The RF readings and the inherent deviation factors A laminated, color-coded rendering to be used at the site showing RF levels and hot spots according to the standards of the FCC Equipment Certifications Recommendations for signage (if needed) Recommendations for training (if needed) Recommendations for mitigating RF hazards (if needed) Recommendations for mitigating other hazards (if needed) All assessments include a site security review RSI info@rsicorp.com 888-830-5648
- 2. Introducing The Latest in RF Safety From Site Compliance Plus A Secure Database Tracking System designed to provide you, your clients, your vendors, and your field personnel with up to date RF/FCC/OSHA records on all of your sites. SC+ is not just a database program. It is also a communications system allowing approved personnel access to real time information in the field. Have a tech going up to one of your sites and need to get a color map of the site’s “hot spots” for the employees’ safety? Have the tech go to SC+ online with his or her own User ID and Password and download the information needed prior to accessing the site. It’s simple, easy, and affordable. Great for contractors preparing to work on the site. Access to the program can be set up on a person by person basis, so you control who has access to specific information. You can view all your sites or only one individual site. Perhaps you are co- located or on another site owner’s property and would like others to have access to the latest information regarding your system on that site and its relation to RF Hazards. Assign them access to the program so that they can see real time information regarding your systems. Need to get an overview on all your sites? Just log on and take a look at your entire portfolio. Site Compliance Plus Innovation and Organization For more information contact RSI at 888-830-5648 or info@rsicorp.com