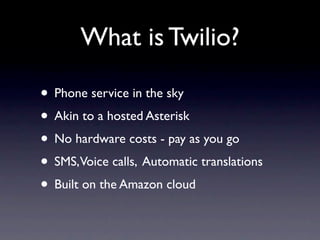
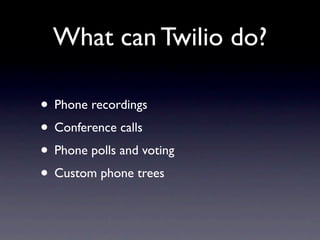
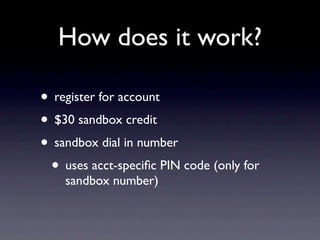
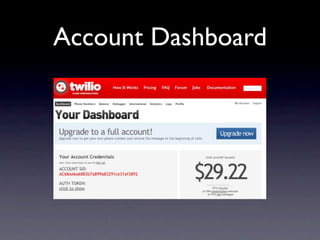
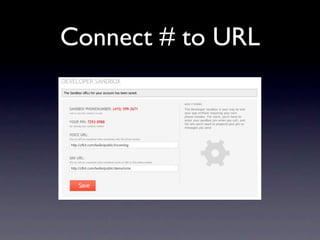
The document provides an introduction to Twilio, a cloud-based phone service allowing users to manage SMS, voice calls, and other communication features without hardware costs. Michael Kimsal discusses the capabilities and limitations of Twilio, including phone polls, custom phone trees, and its new open-source framework OpenVBX. The document also includes a brief overview of how to interact with the Twilio API using PHP code and provides additional resources for developers.







![Twilio POST to you...
$_POST[‘CallGuid’]
$_POST[‘Caller’]
$_POST[‘Called’]
$_POST[‘CallStatus’]
$_POST[‘CallerCity’]
and more...
http://www.twilio.com/docs/api/2008-08-01/twiml/twilio_request](https://image.slidesharecdn.com/intrototwilio-100628065735-phpapp02/85/Getting-Started-with-Twilio-14-320.jpg)