The report delves into the research and findings on trusted secure operating systems, focusing on the Flask (Flux Advanced Security Kernel) security architecture. It discusses the evolution of distributed operating systems, the historical significance of security in computing, and the modern requirements for operating systems. The document outlines the key components of the Flask architecture, including the object manager, security server, and access vector cache.









![ECE 579S - September 2010
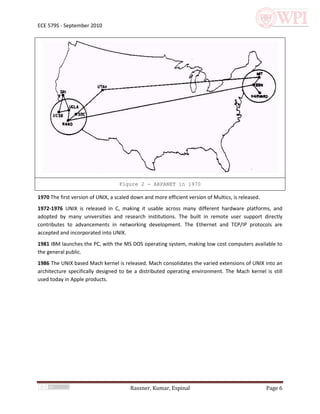
and unload policies. The security server plays a central role in revocation of polices for a process. When
a policy is revoked or updated, it notifies the object manager, which in turn updates its internal state.
The AVC also intercepts the notification and updates or invalidates the cache for the policy that is
revoked or updated. AVC then calls the registered entry points to begin the migration of the change to
other system components. For example, when a file system would like to know when permission on a
file object has been revoked. A registered callback notifies the affected file system (system components)
of the change. Finally object manager sends a response to the Security server indicating that policy
revocation or update is complete.
5 SELinux
SELinux is a strong and flexible implementation of Flask on top of a Linux system. It provides means of
implementing MAC and MLS, and more precisely, it implements a Bell-LaPadula access model. This is
done by extending the Linux Security Modules extensions of the Linux Kernel, SELinux itself been
integrated into the mainline 2.6 series of Linux Kernels. I is becoming a standard for trusted Linux
deployments for current and future platforms (including Android [Shabial2010]).
Some of its characteristics (originating from its implementation of Flask) include a separation of
protection (enforcement) from security (policy). It also implements a reliable, trusted MAC/MLS model
via trusted channels and type enforcement. SELinux provides mechanisms for the polyinstantiation of
resources, and relies on extended attributes for implementing flexible security policies of variable
granularity and role-based access control. Most importantly, it is backward compatible. That is,
applications that run on a standard Linux distribution can run on a SELinux base without compilation
(provided security policies are in place for it.)
5.1 Architecture
SELinux being an implementation of Flask, it relies on security contexts for labeling of subjects and
objects. Everything that can be a subject (namely a process) has a security context associated to it, and
so does everything that can be accessed as a resource (namely via file handle). This is illustrated in
Figure 7.
Rassner, Kumar, Espinal Page 14](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-14-320.jpg)
![ECE 579S - September 2010
Figure 7 - Security Context usage in SELinux.
In Figure 7, subjects requesting access to an object do so through the mediation of the Security
Enforcement Module. This in turn enforces security policies when accessing objects on the subjects’
behalf. The Security Context of each participant (as well as the SIDs) is used as input for policy
evaluation and enforcement.
5.1.1 LSM Architecture
The LSM architecture (as presented in Figure 8 [Wright2002]) illustrates the role of LSM for the
implementation of Flask architecture. After the standard DAC security evaluation takes place, a system
call is intercepted by a LSM hook which consults a Policy Engine (a LSM Module) for allowing or denying
the call to continue. What we can gather from this process is that
1. The active security model is the sum of the existing DAC and the security model(s) implemented by
the policy engine, and
2. The security model(s) implemented by the later take precedence over DAC policies.
Rassner, Kumar, Espinal Page 15](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-15-320.jpg)
![ECE 579S - September 2010
Figure 8 - LSM Architecture (High Level View)
5.1.2 Kernel and User Space
On a SELinux system, a Flask object managers can run either in user space or in kernel space. On the
other hand, security services run in kernel/privilege space at all times. As shown in Figure 9
[Caplan2007], user-space object managers mediate access to resources via a SELinux filesystem
following the tradition of representing resources as files/file handles. The file system in turn runs within
the LSM module and closely interacts with security server.
Rassner, Kumar, Espinal Page 16](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-16-320.jpg)
![ECE 579S - September 2010
Figure 9 - Kernel view of a SELinux LSM Module
Other object managers that reside within the kernel space must communicate with the security server
via LSM hooks. Kernel-space object managers are expected to act accordingly. That is, they are trusted
upon enforcing the access decisions computed by the security server. User-space object managers on
the other hand, implicitly enforce access decisions by returning a file handle to a resource as returned
by the SELinux filesystem (or an error if the resource is denied). In other words, enforcement of access
decisions by user-space object managers actually takes place within the SELinux filesystem. In other
words, enforcement always occurs in kernel space [Caplan2007].
5.2 Capabilities
SELinux capabilities extend to the implementation of extremely flexible security policies as well as
mechanisms for implementing trusted Bell-LaPadula security models. These are presented next.
5.2.1 Policy Flexibility
SELinux provides mechanism for flexible, variable granularity security policies by making use of file
system extended attributes as security contexts. A SELinux system (0) enforces a specific format in
Rassner, Kumar, Espinal Page 17](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-17-320.jpg)
![ECE 579S - September 2010
extended attributes so that they represent security contexts as security labels. These labels, though
being policy-independent, are used as inputs during evaluation of security policies. Labels can be used
for defining roles, category and sensitivity (need-to-know) labels than can be associated to both subjects
(users and associated processes) and objects (any resource representable as a file handle.)
A typical security context encoded in extended attributes might take the form of the user (or domain
type label), role if any, type (when applied as an object label), and at least one category. The following is
an example:
user:role:type:sensitivity[:category,...][-sensitivity[:category,...]]
Example 1 - Security context format as encoded in extended attributes
When a category is missing, SELinux applies a default category according to the policy profile(s) in place.
In this case, either explicitly or by a given policy profile; a missing category does not provide access by
default.
5.2.2 Trusted MAC/MLS
The usage of labels in a security context is a fundamental part in the implementation of a trusted
mandatory access control and multi-level security model. For a trusted MAC/MLS to exist, SELinux
provides mechanisms for trusted paths and type enforcement [Losccoco1998]. Trusted paths, an
implementation of Flask client and server identification, are implemented at the IPC level. It ensures
that no spoofing of user or server occurs. It guarantees an absence of tampering.
Type enforcement is implemented in SELinux by providing mechanisms of least privilege. There is no
access by default; there is no notion of super user or sticky bits as implemented in standard Unix
implementations; and it gives precedence to MAC over DAC during security policy evaluation
[Caplan2007].
With type enforcement, SELinux implements a state machine that governs trusted transitions from one
operation to the next. A subject cannot perform an action on a object unless there is a relation, a
transition, between the domain (the label associated to the subject) and the type of the object (the label
associated to the object’s security context.) An example of this is found in 0.
allow user_t bin_t : file {read execute getattr};
Example 2 - Associating a domain (user_t) to a type (bin_t) of file resources
for read, execute and view of attributes.
5.3 Domain Transition
At the core of type enforcement lays the mechanism of domain transition. Just as specified in Flask, a
subject of a given domain should be able to replace its effective security context (and domain) when
executing an operation on a type. A typical example is an unprivileged login process allowing a user to
change its entry in /etc/shadow (a privileged resource.)
Rassner, Kumar, Espinal Page 18](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-18-320.jpg)
![ECE 579S - September 2010
In typical UNIX systems, this is implemented by setting a sticky bit on the program performing the
operation, in this case /usr/bin/passwd. The net effect is that the calling, unprivileged process creates a
new process with the effective id of the passwd owner (in this case root). This elevation of access rights
is illustrated in 0 [Caplan2007]
Figure 10 - Elevation of access rights for changing an entry in /etc/shadow
The problem with this approach is that it does not follow the principle of least privilege. The new
executed process in step three (Figure 10) obtains the same access rights as root. An erroneous or
malicious change on passwd would allow it to access anything root can. This is more than what is
required, which is limited to access a single resource (/etc/shadow) for a very specific purpose (a
password change.)
With SELinux, type enforcement is used for achieving least privilege by enforcing state transitions
defined a priori in the SELinux policy profiles.
Rassner, Kumar, Espinal Page 19](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-19-320.jpg)
![ECE 579S - September 2010
Figure 11 - Elevation of access rights (limited to least privilege) via
domain transitions.
In Figure 11 [Caplan2007], a SELinux policy defines a set of state transitions which permit a process to
change its domain to one limited for accessing the required resource and nothing more. In this example,
the user as a domain user_t associated to its security context. Furthermore, its domain is first associated
to the type associated to the /usr/bin/passwd program (in this case, passswd_exec_t).
However (and not illustrated in the figure), passwd_exec_t cannot access the desire resource
(/etc/shadow) unless it runs on a security context containing a specific passwd_t domain. A user
requires a transition from its user_t domain into the passwd_t domain to carry this operation. This is
achieved by second step of associating the passwd_t domain to the passwd_exec_t type as an entry
point. The entry point is the association that permits the domain transition to take place.
The last part of the required policy configuration is the association of the user domain (user_t) to the
passwd_t domain. This mechanism enforces the types and domains associations as well as eliminates
the need for running processes as root when accessing privilege resources.
This, in combination with trusted paths previously mentioned are the mechanisms with which SELinux
implements trusted MAC/MLS security models.
5.4 Additional Notes
LSM is a partial implementation of Flask, and as a result, same limitations apply to SELinux (or any other
implementation based on LSM architecture.) The most prominent feature missing is the ability to revoke
access rights when a process is in progress. That is, a process cannot be aborted once its access rights
are already revoked. This is a feature expected for implementation in the near future.
Other LSM-based kernel modules exist for implementing Flask. Most notably are TOMOYO Linux (in the
Linux Kernel mainline since 2.6.30); SMACK (Simplified Mandatory Access Control Kernel) and AppArmor
Rassner, Kumar, Espinal Page 20](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-20-320.jpg)

![ECE 579S - September 2010
References
[1] http://www.multicians.org/
[2] http://www.computerhistory.org/timeline/
[3] http://www.seas.upenn.edu/about-seas/eniac/operation.php
[4] http://library.thinkquest.org/27887/gather/history/internet.shtml
[5] P. A. Loscocco, S. D. Smalley, P. A. Muckelbauer, R. C. Taylor, S. J. Turner, and J. F. Farrell.
The Inevitability of Failure: The Flawed Assumption of Security in Modern Computing Environments.
In Proceedings of the 21st National Information Systems Security Conference, pages 303-314, Oct. 1998.
[6] R. Spencer, S. Smalley, P. Loscocco, M. Hibler, D. Andersen, and J. Lepreau.
The Flask Security Architecture: System Support for Diverse Security Policies.
In Proceedings of the Eighth USENIX Security Symposium, pages 123-139, Aug. 1999.
[7] A comparison of secure UNIX operating systems, Wong, R.M., Computer Security Applications
Conference, 1990., Proceedings of the Sixth Annual (0-8186-2105-2) 1990. p.333-333
[8] Issues in secure distributed operating system design., Wong, Raymond M., Digest of Papers - IEEE
Computer Society International Conference, Feb 1989. p.338-341
[9] Kain, R. Y. and Landwehr, C. E. 1987. On Access Checking in Capability-Based Systems. IEEE Trans.
Softw. Eng. 13, 2 (Feb. 1987), 202-207.
[10] Casey, T.A., Jr.; Vinter, S.T.; Weber, D.G.; Varadarajan, R.; Rosenthal, D.; , "A secure distributed
operating system," Security and Privacy, 1988. Proceedings., 1988 IEEE Symposium on , vol., no., pp.27-
38, 18-21 Apr 1988
[11] Mike Accetta, Robert Baron, William Bolosky, David Golub, Richard Rashid, Avadis Tevanian, and
Michael Young. Mach: A new kernel foundation for UNIX development. In Proceedings of the Summer
1986 USENIX Conference. pages 93-112. Atlanta, GA. June9-13. 1986.
[12] Gregory, M. and Loscocco, P. (2007) 'Using the flask security architecture to facilitate risk adaptable
access controls', Third Annual Security Enhanced Linux Symposium, National Information Assurance
Research Laboratory, 14-15 March, Wyndham Hotel, Baltimore, MD, USA,
[13] Red Hat Enterprise Linux 4: Red Hat SELinux Guide,
http://www.redhat.com/docs/manuals/enterprise/RHEL-4-Manual/selinux-guide/selg-chapter-
0013.html
*14+ Jones, Tim. “Anatomy of Security-Enhanced Linux (SELinux),”
http://www.ibm.com/developerworks/linux/library/l-selinux/
Rassner, Kumar, Espinal Page 22](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-22-320.jpg)
![ECE 579S - September 2010
[Shabial2010] Securing Android-Powered Mobile Devices Using SELinux. Asaf Shabial, Yuval Fledel and
Yuval Elovigi, IEEE Computer and Reliability Societies, May/June 2010.
[Wright2002] Wright et al “Linux Security Module Framework”, Usenix 2002.
[Jones2008] Anatomy of Security-Enhanced Linux (SELinux) Architecture and implementation, M. Tim
Jones, Consultant Engineer, Emulex Corp. 2008. http://www.ibm.com/developerworks/linux/library/l-
selinux/
[Caplan2007] SELinux by Example, Caplan, MacMillan, Mayer. Prentice Hall, 2007
[Loscocco1998] The Inevitability of Failure: The Flawed Assumption of Security in Modern Computing
Environments. Loscocco et al. Usenix, 1998.
Rassner, Kumar, Espinal Page 23](https://image.slidesharecdn.com/flask-selinuxrassnerkumarespinal-100926115816-phpapp01/85/Flask-Flux-Advanced-Security-Kernel-A-Project-Report-23-320.jpg)