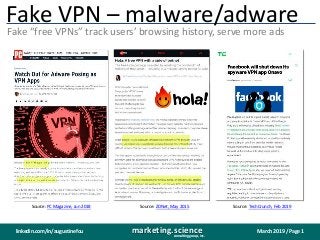
Fake vp ns for malware botnets and adware
•Download as PPTX, PDF•
0 likes•553 views
What is truly free? Well, not free VPNs. They make money by collecting the sites users visit and other info to sell as data for more ads or targeting.
Report
Share
Report
Share
Recommended
Alternative to ANA's end to end supply chain transparency study v final

Alternative to ANA's end to end supply chain transparency study v finalDr. Augustine Fou - Independent Ad Fraud Researcher
Impact of Loss of 3P Cookies on Publishers' Ad Revenue

Impact of Loss of 3P Cookies on Publishers' Ad RevenueDr. Augustine Fou - Independent Ad Fraud Researcher
Recommended
Alternative to ANA's end to end supply chain transparency study v final

Alternative to ANA's end to end supply chain transparency study v finalDr. Augustine Fou - Independent Ad Fraud Researcher
Impact of Loss of 3P Cookies on Publishers' Ad Revenue

Impact of Loss of 3P Cookies on Publishers' Ad RevenueDr. Augustine Fou - Independent Ad Fraud Researcher
Checking abnormal referrer traffic in google analytics

Checking abnormal referrer traffic in google analyticsDr. Augustine Fou - Independent Ad Fraud Researcher
Four types of digital ad spend updated august 2020

Four types of digital ad spend updated august 2020Dr. Augustine Fou - Independent Ad Fraud Researcher
FouAnalytics DIY site media analytics fraud detection baked in

FouAnalytics DIY site media analytics fraud detection baked inDr. Augustine Fou - Independent Ad Fraud Researcher
Investigating digital ad fraud spi virtual meeting

Investigating digital ad fraud spi virtual meetingDr. Augustine Fou - Independent Ad Fraud Researcher
More Related Content
More from Dr. Augustine Fou - Independent Ad Fraud Researcher
Checking abnormal referrer traffic in google analytics

Checking abnormal referrer traffic in google analyticsDr. Augustine Fou - Independent Ad Fraud Researcher
Four types of digital ad spend updated august 2020

Four types of digital ad spend updated august 2020Dr. Augustine Fou - Independent Ad Fraud Researcher
FouAnalytics DIY site media analytics fraud detection baked in

FouAnalytics DIY site media analytics fraud detection baked inDr. Augustine Fou - Independent Ad Fraud Researcher
Investigating digital ad fraud spi virtual meeting

Investigating digital ad fraud spi virtual meetingDr. Augustine Fou - Independent Ad Fraud Researcher
More from Dr. Augustine Fou - Independent Ad Fraud Researcher (20)
Checking abnormal referrer traffic in google analytics

Checking abnormal referrer traffic in google analytics
Four types of digital ad spend updated august 2020

Four types of digital ad spend updated august 2020
FouAnalytics DIY site media analytics fraud detection baked in

FouAnalytics DIY site media analytics fraud detection baked in
Investigating digital ad fraud spi virtual meeting

Investigating digital ad fraud spi virtual meeting
Recently uploaded
Recently uploaded (16)
Development Lifecycle.pptx for the secure development of apps

Development Lifecycle.pptx for the secure development of apps
Reggie miller choke t shirtsReggie miller choke t shirts

Reggie miller choke t shirtsReggie miller choke t shirts
TORTOGEL TELAH MENJADI SALAH SATU PLATFORM PERMAINAN PALING FAVORIT.

TORTOGEL TELAH MENJADI SALAH SATU PLATFORM PERMAINAN PALING FAVORIT.
Thank You Luv I’ll Never Walk Alone Again T shirts

Thank You Luv I’ll Never Walk Alone Again T shirts
Production 2024 sunderland culture final - Copy.pptx

Production 2024 sunderland culture final - Copy.pptx
The Use of AI in Indonesia Election 2024: A Case Study

The Use of AI in Indonesia Election 2024: A Case Study
Cyber Security Services Unveiled: Strategies to Secure Your Digital Presence

Cyber Security Services Unveiled: Strategies to Secure Your Digital Presence
Fake vp ns for malware botnets and adware
- 1. March 2019 / Page 1marketing.scienceconsulting group, inc. linkedin.com/in/augustinefou Fake VPN – malware/adware Fake “free VPNs” track users’ browsing history, serve more ads Source: PC Magazine, Jun 2018 Source: ZDNet, May 2015 Source: TechCrunch, Feb 2019
