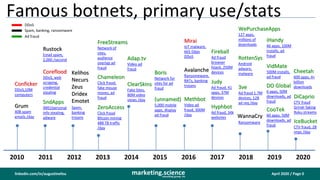
Botnets used for ad fraud spam ddos attacks
•
0 likes•517 views
many botnets are known, some are dismantled; but the question is what are botnets mainly used for? use the color coding to decide for yourself
Report
Share
Report
Share
Download to read offline
Recommended
Ad fraud is cash out for hacking

why do hackers hack? of course, it's fun for them. But they hack to make tons of money with their unique skillset. How does hacking connect to ad fraud? Here are a few examples.
Your current digital just plain sucks, why?

marketers assume their digital marketing is working as expected; but if they looked more closely at analytics, they may see that some of those assumptions are not valid -- i.e. they are not getting what they thought they paid for. Take a closer look yourself.
Ground Truth real safari vs fake safari

Data from FouAnalytics, on-site measurement and in-ad measurement was compared to DBM exchange data for 26 exchanges, 7.5 trillion impressions (30 day period) to analyze browser market share -- specifically Safari/iOS.
Findings include: 1) bots pretending to be Safari/iOS outnumber real Safari users 5 to 1, and 2) there is a 1.5X average surplus of Safari impressions available on exchanges compared to unique cookies.
Ad fraud update for publishers Feb 2020

Has ad fraud gone up or down in recent years? Have publishers gotten out of danger yet? Have a read and you decide.
Not dirty LITTLE secret but Elephant in the Room

putting aside ad fraud for a moment, what's the elephant in the room? we're talking about your digital marketing. Do you think it is working? How do you know?
What CFEs can do about digital ad fraud

certified fraud examiners can apply their investigative techniques to help identify and root out ad fraud too; no specialized tech is required.
2021 update on ad fraud brand safety privacy

digital ad fraud is as rampant as ever; new ripples caused by privacy regulations are starting to affect the market. and more BS from trade associations pretending to be doing something
History and Impact of Digital Ad Fraud

presentation on the impact of digital ad fraud on marketers and publishers
Recommended
Ad fraud is cash out for hacking

why do hackers hack? of course, it's fun for them. But they hack to make tons of money with their unique skillset. How does hacking connect to ad fraud? Here are a few examples.
Your current digital just plain sucks, why?

marketers assume their digital marketing is working as expected; but if they looked more closely at analytics, they may see that some of those assumptions are not valid -- i.e. they are not getting what they thought they paid for. Take a closer look yourself.
Ground Truth real safari vs fake safari

Data from FouAnalytics, on-site measurement and in-ad measurement was compared to DBM exchange data for 26 exchanges, 7.5 trillion impressions (30 day period) to analyze browser market share -- specifically Safari/iOS.
Findings include: 1) bots pretending to be Safari/iOS outnumber real Safari users 5 to 1, and 2) there is a 1.5X average surplus of Safari impressions available on exchanges compared to unique cookies.
Ad fraud update for publishers Feb 2020

Has ad fraud gone up or down in recent years? Have publishers gotten out of danger yet? Have a read and you decide.
Not dirty LITTLE secret but Elephant in the Room

putting aside ad fraud for a moment, what's the elephant in the room? we're talking about your digital marketing. Do you think it is working? How do you know?
What CFEs can do about digital ad fraud

certified fraud examiners can apply their investigative techniques to help identify and root out ad fraud too; no specialized tech is required.
2021 update on ad fraud brand safety privacy

digital ad fraud is as rampant as ever; new ripples caused by privacy regulations are starting to affect the market. and more BS from trade associations pretending to be doing something
History and Impact of Digital Ad Fraud

presentation on the impact of digital ad fraud on marketers and publishers
Still nothing but ad fraud 2021 dr augustine fou

In 2021 some marketers are still asking whether ad fraud is real and whether it is pervasive. This serves as a simple reminder of some of the evidence collected over the years.
Investigating digital ad fraud spi virtual meeting

Investigating digital ad fraud spi virtual meetingDr. Augustine Fou - Independent Ad Fraud Researcher
digital ad fraud is what form of crime? counterfeit goods, computer crimes, wire fraud, securities fraud, money laundering? you decideHidden Costs in Digital Media Supply Path

How many of these hidden costs were you aware of?
Without even talking about digital ad fraud, there are other costs in the digital ad supply path that eat up most of every dollar that advertisers spend in digital. There are known costs of 60 - 70% extracted by adtech middlemen.
Fake Everything 2019 Update

Ellen Pao was right. I have seen and documented the fake stuff since at least 2013. In digital, virtually unlimited fake accounts, fake traffic, fake users, fake ad impressions, etc. can be created. How many of the 50 slides in this deck were you familiar with?
State of Digital Ad Fraud Q2 2018

Ad fraud is at its all time high; both in rate and in dollars. Here's the evidence, you decide for yourself.
How to Use FouAnalytics For Marketers

FouAnalytics is an alternative to Google Analytics, but with fraud and bot detection baked in. Marketers can use FouAnalytics to look at their own campaigns, find the domains and apps that are eating up their budgets fraudulently, and turn them off, while the campaign is still running. How does that compare to your blackbox fraud detection that just gives you a percent IVT number?
Fraud by Browser Study

bots are pretending to be Safari browser because more marketers are targeting iOS devices, seeking to show ads to more affluent customers.
Digital Fraud Viewability Benchmarks Q4 2020

digital ad fraud, viewability, ad blocking benchmarks for Q 2020; directly measured across a wide variety of campaigns and sites
Digital Ad Fraud FAQ Question 1

a colleague asked this question - "Publishers claim to only have 0.2-1% IVT on their sites. Can it be possible?” I answered in 22 slides.
In app fraud vs app install fraud

app install fraud categories are exactly mirror image to in-app fraud categories
Entire ecosystem supporting ad fraud 2018

“In addition to the ad fraud itself, bad guys make money by selling the “picks and shovels” too – e.g. bots, traffic, clicks, malware, fake apps, etc. They have an entire ecosystem to extract value. What follows are just a few examples, scratching the surface.”
Why Fraud detection doesn't work

Everyone is paying for fraud detection, but without enough technical knowledge, they don't realize the fraud detection doesn't work or is easily tricked by the bad guys. So what's worse is that the people paying for fraud detection have a false sense of security and take their eyes off of the obvious fraud that is still getting through.
Digital ad fraud is an iceberg

what you can't see will kill your marketing campaigns. Bot detection (also known as GIVT, IVT, NHT) catches bots. But most ad fraud is not from bots any more. Most of the fraud is missed by detection and still gets through unless you analyze the data and remove it yourself.
Ad Tech Organized Crime

An entire ecosystem set up to support fraud. There are no laws against ad fraud; but other laws may apply. Time to take a closer look.
FouAnalytics DIY site media analytics fraud detection baked in

FouAnalytics DIY site media analytics fraud detection baked inDr. Augustine Fou - Independent Ad Fraud Researcher
FouAnalytics - site analytics and media analytics for practitioners to detect fraud and take action themselves - on-site tags and in-ad tags measure sites and ad impressions, respectivelyDigital Media Trust Collaborative

The original idea of the digital media trust collaborative is was sharing threat intelligence to more quickly remove fraudulent domains and apps from media buys.
Four types of digital ad spend updated august 2020

Four types of digital ad spend updated august 2020Dr. Augustine Fou - Independent Ad Fraud Researcher
from the IAB FY 2019 advertising revenue report, we show that CPM and CPC ads represent 92% of all digital spend; these are the favorite targets of fraudtersHow Bad Measurements Harm Good Publishers

Bad measurements by ad tech providers are causing irreparable harm to good publishers. Here are just a few scenarios to illustrate the problem.
Cyber Crime and Security

Details about cyber crime, ways to protect cyber crime and Wannacry Ransomware attack details.
More Related Content
What's hot
Still nothing but ad fraud 2021 dr augustine fou

In 2021 some marketers are still asking whether ad fraud is real and whether it is pervasive. This serves as a simple reminder of some of the evidence collected over the years.
Investigating digital ad fraud spi virtual meeting

Investigating digital ad fraud spi virtual meetingDr. Augustine Fou - Independent Ad Fraud Researcher
digital ad fraud is what form of crime? counterfeit goods, computer crimes, wire fraud, securities fraud, money laundering? you decideHidden Costs in Digital Media Supply Path

How many of these hidden costs were you aware of?
Without even talking about digital ad fraud, there are other costs in the digital ad supply path that eat up most of every dollar that advertisers spend in digital. There are known costs of 60 - 70% extracted by adtech middlemen.
Fake Everything 2019 Update

Ellen Pao was right. I have seen and documented the fake stuff since at least 2013. In digital, virtually unlimited fake accounts, fake traffic, fake users, fake ad impressions, etc. can be created. How many of the 50 slides in this deck were you familiar with?
State of Digital Ad Fraud Q2 2018

Ad fraud is at its all time high; both in rate and in dollars. Here's the evidence, you decide for yourself.
How to Use FouAnalytics For Marketers

FouAnalytics is an alternative to Google Analytics, but with fraud and bot detection baked in. Marketers can use FouAnalytics to look at their own campaigns, find the domains and apps that are eating up their budgets fraudulently, and turn them off, while the campaign is still running. How does that compare to your blackbox fraud detection that just gives you a percent IVT number?
Fraud by Browser Study

bots are pretending to be Safari browser because more marketers are targeting iOS devices, seeking to show ads to more affluent customers.
Digital Fraud Viewability Benchmarks Q4 2020

digital ad fraud, viewability, ad blocking benchmarks for Q 2020; directly measured across a wide variety of campaigns and sites
Digital Ad Fraud FAQ Question 1

a colleague asked this question - "Publishers claim to only have 0.2-1% IVT on their sites. Can it be possible?” I answered in 22 slides.
In app fraud vs app install fraud

app install fraud categories are exactly mirror image to in-app fraud categories
Entire ecosystem supporting ad fraud 2018

“In addition to the ad fraud itself, bad guys make money by selling the “picks and shovels” too – e.g. bots, traffic, clicks, malware, fake apps, etc. They have an entire ecosystem to extract value. What follows are just a few examples, scratching the surface.”
Why Fraud detection doesn't work

Everyone is paying for fraud detection, but without enough technical knowledge, they don't realize the fraud detection doesn't work or is easily tricked by the bad guys. So what's worse is that the people paying for fraud detection have a false sense of security and take their eyes off of the obvious fraud that is still getting through.
Digital ad fraud is an iceberg

what you can't see will kill your marketing campaigns. Bot detection (also known as GIVT, IVT, NHT) catches bots. But most ad fraud is not from bots any more. Most of the fraud is missed by detection and still gets through unless you analyze the data and remove it yourself.
Ad Tech Organized Crime

An entire ecosystem set up to support fraud. There are no laws against ad fraud; but other laws may apply. Time to take a closer look.
FouAnalytics DIY site media analytics fraud detection baked in

FouAnalytics DIY site media analytics fraud detection baked inDr. Augustine Fou - Independent Ad Fraud Researcher
FouAnalytics - site analytics and media analytics for practitioners to detect fraud and take action themselves - on-site tags and in-ad tags measure sites and ad impressions, respectivelyDigital Media Trust Collaborative

The original idea of the digital media trust collaborative is was sharing threat intelligence to more quickly remove fraudulent domains and apps from media buys.
Four types of digital ad spend updated august 2020

Four types of digital ad spend updated august 2020Dr. Augustine Fou - Independent Ad Fraud Researcher
from the IAB FY 2019 advertising revenue report, we show that CPM and CPC ads represent 92% of all digital spend; these are the favorite targets of fraudtersHow Bad Measurements Harm Good Publishers

Bad measurements by ad tech providers are causing irreparable harm to good publishers. Here are just a few scenarios to illustrate the problem.
What's hot (20)
Investigating digital ad fraud spi virtual meeting

Investigating digital ad fraud spi virtual meeting
FouAnalytics DIY site media analytics fraud detection baked in

FouAnalytics DIY site media analytics fraud detection baked in
Four types of digital ad spend updated august 2020

Four types of digital ad spend updated august 2020
Similar to Botnets used for ad fraud spam ddos attacks
Cyber Crime and Security

Details about cyber crime, ways to protect cyber crime and Wannacry Ransomware attack details.
Cyber crimes Challenges in Global and Oman

The presentation which covers the latest threats in Cyberspace and ongoing cybercrimes challenges to the investigator's in Global and Oman.
Cyber Security

We need to Aware about Cyber Security, Because Cyber Security is Everyone's Responsibility. Here I Upload PPT with some interesting Facts,Figure,News Paper Cutting Images and Many More. And If you Like this then Hit Like Button. Thank You!
AI and IoT - A New Era of Cybercrimes | Cyberroot Risk Advisory (CR Group)

Expansion of AI technology and IoT has altered the course of technological invasion throughout the world.
Cyber crime

This is a presentation about Cyber crime . i think This slide well prepared .if its help any student ,That's why i upload this slide..thank you
Five cyber threats to be careful in 2018

It is not true that people are safe from hackers because they only target big companies for money and other purposes. Every person using debit or credit cards, doing online transactions, using the internet can get affected by cyber threats. You may lose money before even recognizing the situation. Simple mistakes from users open the entry for virus and malware coded by hackers.
What are cybercrimes? How cybercrime works?

Today is the time of the internet, computers, and digital technology.
And, in this age of the Internet, we spend much of our lives online. However, there are many reasons why the internet is so fun and popular.
Getting the latest news through various websites, talking to our loved ones from anywhere, chatting and communicating via video call, shopping online through the internet, getting accurate information on any subject, watching videos for entertainment, playing online games, and online bills. Today it has become possible to do almost all kinds of work like payment easily through the internet.
Honestly, I think the internet is a contribution to us
Simply, if there is no complete internet for one day, it can have a lot of impact on public life.
At any given time, billions of people are active on the Internet and use various websites or applications to access the Internet on their mobile phones or computers.
In this case, there are many people who use computers and the internet to steal their personal information, cheat, and extort money from these "online traffic" or "online internet users" through various illegal means. More other crimes.
Thus, the crimes of cheating, privacy, and data theft or misuse of data online through a mobile, computer, and internet are called cyber crime or cybercrime. And, those who commit this kind of cybercrime are called cybercriminals. There are different types of cybercrime on the internet. This means that cybercriminals can deceive you through various illegal means online. You may be the next victim if you are not careful when using the Internet.
What are cybercrimes?
pypt.pptx.shshjsjdjjdhdhhdhdhdhdhhdhdjdjdjdjjrejjr

This is a PPT of SOCIAL MEDIA THREATS AND THEIR PREVENTION. This is help full for learning. Thanks.
Social media offers an outlet for people to connect, share life experiences, pictures and video. But too much sharing—or a lack of attention to impostors—can lead to a compromise of business and personal accounts.
Attackers often use social media accounts during the reconnaissance phase of a social engineering or phishing attack. Social media can give attackers a platform to impersonate trusted people and brands or the information they need carry out additional attacks, including social engineering and phishing.
Protecting Data Privacy

Presented by RUDI LUMANTO, ID-SIRTII in Indonesia Information Security Forum 2012
Similar to Botnets used for ad fraud spam ddos attacks (20)
AI and IoT - A New Era of Cybercrimes | Cyberroot Risk Advisory (CR Group)

AI and IoT - A New Era of Cybercrimes | Cyberroot Risk Advisory (CR Group)
pypt.pptx.shshjsjdjjdhdhhdhdhdhdhhdhdjdjdjdjjrejjr

pypt.pptx.shshjsjdjjdhdhhdhdhdhdhhdhdjdjdjdjjrejjr
More from Dr. Augustine Fou - Independent Ad Fraud Researcher
Forensic Auditing of Digital Media.pdf

Techniques to verify your digital media with or without specialized tools.
Digital ad dollars trickle down chart

how the money flows from the advertisers through the ad tech intermediaries to longtail, fraud, and fake sites, with the help of botnets and traffic sellers
Bad guys optimize ad fraud efficiency

bad guys started with fake websites, then moved to loading ads only to save time and bandwidth; now they are simply faking bid requests and flooding exchanges
Alternative to ANA's end to end supply chain transparency study v final

Alternative to ANA's end to end supply chain transparency study v finalDr. Augustine Fou - Independent Ad Fraud Researcher
The ANA RFP for an update to the supply chain transparency study from the ISBA in 2020 is not even asking the right questions; here's my view. Impact of Loss of 3P Cookies on Publishers' Ad Revenue

Impact of Loss of 3P Cookies on Publishers' Ad RevenueDr. Augustine Fou - Independent Ad Fraud Researcher
Previous studies that addressed the impact of losing third party (“3P”) cookies on ad revenue did not clearly differentiate between the impact on ad tech intermediaries versus on publishers. Instead of “advertiser CPMs” (what advertisers pay) this study uses “media CPMs” (what the publishers get) to better isolate the impact of tracking vs no tracking on publishers.Programmatic reach analysis 2021

most buyers who buy in programmatic channels think they are getting enormous "reach" -- i.e. their ads are shown on many sites; but this data shows the exact opposite is true. Their ads are being shown on a small number of sites (less than 1,000); the buyers might as well have bought more direct from good publishers.
Browser and OS Share Jan 2021

OS and browser share in the U.S. for smartphone, desktop, and tablet; plus details on iOS and Safari version distribution
Checking abnormal referrer traffic in google analytics

Checking abnormal referrer traffic in google analyticsDr. Augustine Fou - Independent Ad Fraud Researcher
Using Google Analytics to find abnormal traffic and fraud; this is a how-to, to get hourly charts instead of daily rolled-up or averaged data, which hides the fraud. Digital ad dollars trickle down chart

how marketers' digital budgets trickle down into the pockets of middlemen and criminals
Marketer Outcomes Study

When marketers buy from good publishers and pay HIGHER CPMs, they get better outcomes and marketing efficiency, despite the higher CPM. This is because there are human audiences that visit those good publishers' sites.
Site analytics click location research

analytics shows you where users clicked when navigating the site. desktop clicks should be different from mobile clicks
More from Dr. Augustine Fou - Independent Ad Fraud Researcher (12)
Alternative to ANA's end to end supply chain transparency study v final

Alternative to ANA's end to end supply chain transparency study v final
Impact of Loss of 3P Cookies on Publishers' Ad Revenue

Impact of Loss of 3P Cookies on Publishers' Ad Revenue
Checking abnormal referrer traffic in google analytics

Checking abnormal referrer traffic in google analytics
Recently uploaded
重新申请毕业证书(RMIT毕业证)皇家墨尔本理工大学毕业证成绩单精仿办理

不能毕业办理【RMIT毕业证【微信176555708】皇家墨尔本理工大学文凭学历】【微信176555708】【皇家墨尔本理工大学文凭学历证书】【皇家墨尔本理工大学毕业证书与成绩单样本图片】毕业证书补办 Fake Degree做学费单【毕业证明信-推荐信】成绩单,录取通知书,Offer,在读证明,雅思托福成绩单,真实大使馆教育部认证,回国人员证明,留信网认证。网上存档永久可查!全套服务:皇家墨尔本理工大学皇家墨尔本理工大学本科学位证成绩单真实回国人员证明 #真实教育部认证。让您回国发展信心十足#铸就十年品质!信誉!实体公司!可以视频看办公环境样板如需办理真实可查可以先到公司面谈勿轻信小中介黑作坊!
可以提供皇家墨尔本理工大学钢印 #水印 #烫金 #激光防伪 #凹凸版 #最新版的毕业证 #百分之百让您绝对满意
印刷DHL快递毕业证 #成绩单7个工作日真实大使馆教育部认证1个月。为了达到高水准高效率
请您先以qq或微信的方式对我们的服务进行了解后如果有皇家墨尔本理工大学皇家墨尔本理工大学本科学位证成绩单帮助再进行电话咨询。
国外毕业证学位证成绩单如何办理:
1客户提供办理信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:我们有专业老师帮你查询);
2开始安排制作皇家墨尔本理工大学毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)。
原版仿制(uob毕业证书)英国伯明翰大学毕业证本科学历证书原版一模一样

原版纸张【微信:741003700 】【(uob毕业证书)英国伯明翰大学毕业证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
一比一原版(SLU毕业证)圣路易斯大学毕业证成绩单专业办理

SLU毕业证原版定制【微信:176555708】【圣路易斯大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
Italy Agriculture Equipment Market Outlook to 2027

Agriculture and Animal Care
Ken Research has an expertise in Agriculture and Animal Care sector and offer vast collection of information related to all major aspects such as Agriculture equipment, Crop Protection, Seed, Agriculture Chemical, Fertilizers, Protected Cultivators, Palm Oil, Hybrid Seed, Animal Feed additives and many more.
Our continuous study and findings in agriculture sector provide better insights to companies dealing with related product and services, government and agriculture associations, researchers and students to well understand the present and expected scenario.
Our Animal care category provides solutions on Animal Healthcare and related products and services, including, animal feed additives, vaccination
国外证书(Lincoln毕业证)新西兰林肯大学毕业证成绩单不能毕业办理

退学办理新西兰林肯大学毕业证【微信176555708】学历认证怎么做:原版仿制新西兰林肯大学电子版成绩单毕业证认证【新西兰林肯大学毕业证成绩单】、新西兰林肯大学文凭证书成绩单复刻offer录取通知书、购买Lincoln圣力嘉学院本科毕业证、【新西兰林肯大学毕业证办理Lincoln毕业证书哪里买】、新西兰林肯大学 Offer在线办理Lincoln Offer新西兰林肯大学Bachloer Degree。1客户提供办理信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:微信176555708我们有专业老师帮你查询);
2开始安排制作毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)。
7完成交易删除客户资料
高精端提供以下服务:
一:新西兰林肯大学新西兰林肯大学毕业证文凭证书全套材料从防伪到印刷水印底纹到钢印烫金
二:真实使馆认证(留学人员回国证明)使馆存档
三:真实教育部认证教育部存档教育部留服网站可查
四:留信认证留学生信息网站可查
五:与学校颁发的相关证件1:1纸质尺寸制定(定期向各大院校毕业生购买最新版本毕,业证成绩单保证您拿到的是鲁昂大学内部最新版本毕业证成绩单微信176555708)
A.为什么留学生需要操作留信认证?
留信认证全称全国留学生信息服务网认证,隶属于北京中科院。①留信认证门槛条件更低,费用更美丽,并且包过,完单周期短,效率高②留信认证虽然不能去国企,但是一般的公司都没有问题,因为国内很多公司连基本的留学生学历认证都不了解。这对于留学生来说,这就比自己光拿一个证书更有说服力,因为留学学历可以在留信网站上进行查询!
B.为什么我们提供的毕业证成绩单具有使用价值?
查询留服认证是国内鉴别留学生海外学历的唯一途径但认证只是个体行为不是所有留学生都操作所以没有办理认证的留学生的学历在国内也是查询不到的他们也仅仅只有一张文凭。所以这时候我们提供的和学校颁发的一模一样的毕业证成绩单就有了使用价值。
How to Use Contact Form 7 Like a Pro.pptx

Contact Form 7 is a popular plugins for WordPress. This is an introduction into its features and usage.
2.Cellular Networks_The final stage of connectivity is achieved by segmenting...

A cellular network, frequently referred to as a mobile network, is a type of communication system that enables wireless communication between mobile devices. The final stage of connectivity is achieved by segmenting the comprehensive service area into several compact zones, each called a cell.
test test test test testtest test testtest test testtest test testtest test ...

salamsasalamlamsalamsalamsalamsalamsalamsalamsalam
一比一原版(CSU毕业证)加利福尼亚州立大学毕业证成绩单专业办理

CSU毕业证原版定制【微信:176555708】【加利福尼亚州立大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
急速办(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单原版一模一样

原版纸张【微信:741003700 】【(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
一比一原版(LBS毕业证)伦敦商学院毕业证成绩单专业办理

LBS毕业证原版定制【微信:176555708】【伦敦商学院毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
Search Result Showing My Post is Now Buried

Search results burying my post that used to rank before Google's March 2024 algorithm update.
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Brad Spiegel Macon GA’s journey exemplifies the profound impact that one individual can have on their community. Through his unwavering dedication to digital inclusion, he’s not only bridging the gap in Macon but also setting an example for others to follow.
1比1复刻(bath毕业证书)英国巴斯大学毕业证学位证原版一模一样

原版纸张【微信:741003700 】【(bath毕业证书)英国巴斯大学毕业证学位证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Internet of Things in Manufacturing: Revolutionizing Efficiency & Quality | C...

This article delves into how the Internet of Things in manufacturing is reshaping the industry, its benefits, challenges, and future prospects.
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

Ellisha Heppner, Grant Management Lead, presented an update on APNIC Foundation to the PNG DNS Forum held from 6 to 10 May, 2024 in Port Moresby, Papua New Guinea.
假文凭国外(Adelaide毕业证)澳大利亚国立大学毕业证成绩单办理

购买澳大利亚国立大学毕业证>【微信176555708】办理澳大利亚国立大学毕业证成绩单【微信176555708】Adelaide毕业证成绩单Adelaide学历证书Adelaide文凭【Adelaide毕业套号文凭网认证澳大利亚国立大学毕业证成绩单】【哪里买澳大利亚国立大学毕业证文凭Adelaide成绩学校快递邮寄信封】【开版澳大利亚国立大学文凭】Adelaide留信认证本科硕士学历认证(诚招代理)微信:176555708办理国外高校毕业证成绩单文凭学位证,真实使馆公证(留学回国人员证明)真实留信网认证国外学历学位认证雅思代考国外学校代申请名校保录开请假条改GPA改成绩ID卡
1.高仿业务:【本科硕士】毕业证,成绩单(GPA修改),学历认证(教育部认证),大学Offer,,ID,留信认证,使馆认证,雅思,语言证书等高仿类证书;
2.认证服务: 学历认证(教育部认证),大使馆认证(回国人员证明),留信认证(可查有编号证书),大学保录取,雅思保分成绩单。
3.技术服务:钢印水印烫金激光防伪凹凸版设计印刷激凸温感光标底纹镭射速度快。
办理澳大利亚国立大学澳大利亚国立大学毕业证成绩单流程:
1客户提供办理信息:姓名生日专业学位毕业时间等(如信息不确定可以咨询顾问:我们有专业老师帮你查询);
2开始安排制作毕业证成绩单电子图;
3毕业证成绩单电子版做好以后发送给您确认;
4毕业证成绩单电子版您确认信息无误之后安排制作成品;
5成品做好拍照或者视频给您确认;
6快递给客户(国内顺丰国外DHLUPS等快读邮寄)
-办理真实使馆公证(即留学回国人员证明)
-办理各国各大学文凭(世界名校一对一专业服务,可全程监控跟踪进度)
-全套服务:毕业证成绩单真实使馆公证真实教育部认证。让您回国发展信心十足!
(详情请加一下 文凭顾问+微信:176555708)欢迎咨询!
Recently uploaded (20)
Italy Agriculture Equipment Market Outlook to 2027

Italy Agriculture Equipment Market Outlook to 2027
2.Cellular Networks_The final stage of connectivity is achieved by segmenting...

2.Cellular Networks_The final stage of connectivity is achieved by segmenting...
test test test test testtest test testtest test testtest test testtest test ...

test test test test testtest test testtest test testtest test testtest test ...
guildmasters guide to ravnica Dungeons & Dragons 5...

guildmasters guide to ravnica Dungeons & Dragons 5...
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx
Internet of Things in Manufacturing: Revolutionizing Efficiency & Quality | C...

Internet of Things in Manufacturing: Revolutionizing Efficiency & Quality | C...
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024
Botnets used for ad fraud spam ddos attacks
- 1. April 2020 / Page 0marketing.scienceconsulting group, inc. linkedin.com/in/augustinefou Famous botnets, primary use/stats 2019 20202017 20182015 20162013 20142011 20122010 IceBucket CTV fraud, 2B imps /day Coreflood DDoS, web scraping, credential stealing Grum 40B spam emails /day ZeroAccess Click fraud Bitcoin mining 488 TB traffic /day Avalanche Ransomeware, RATs, banking trojans Mirai IoT malware, 665 Gbps DDoS Methbot Video ad fraud, 300M /day Hyphbot Ad fraud, 34k websites 3ve Ad fraud 1.7M devices, 12B ad req /day Conficker DDoS,10M computers Judy Ad fraud, 41 apps, 37M devices Fireball Ad fraud browser hijack, 250M devices SndApps IMEI/personal info stealing, adware Chameleon Click fraud, fake mouse moves, ad fraud Rustock Email spam, 2,000 /second RottenSys Android adware, malware WannaCry Kelihos Necurs Zeus Dridex Emotet Spam, banking trojans Ransomware WePurchaseApps 127 apps, millions of downloads Cheetah 600 apps, 4+ billion downloadsDO Global 6 apps, 50M downloads, ad fraud VidMate 500M installs, ad fraud iHandy 46 apps, 100M installs, ad fraud DiCaprio CTV fraud Grindr faking Roku streams CooTek 60 apps, 50M downloads, ad fraud ClearSkins Fake Sites, 80M video views /day Adap.tv Video ad fraud (unnamed) 5,000 mobile apps, display ad fraud Boris Network for sites for ad fraud FreeStreams Network of sites, audience overlap ad fraud DDoS Spam, banking, ransomware Ad fraud
