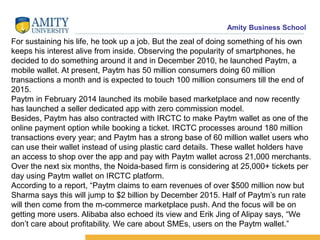
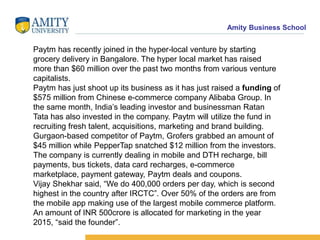
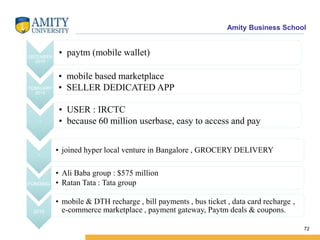
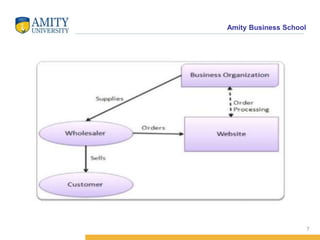
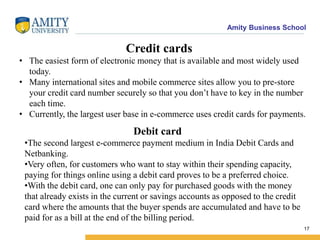
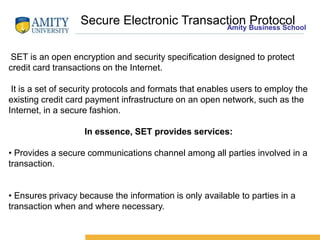
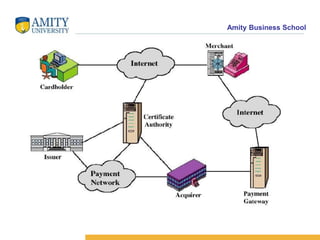
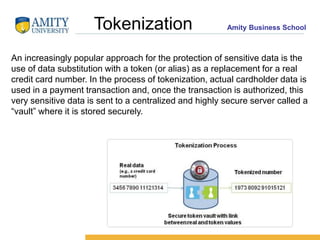
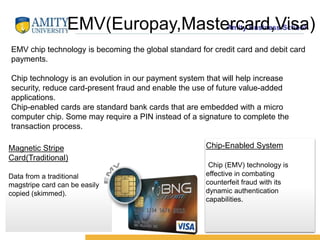
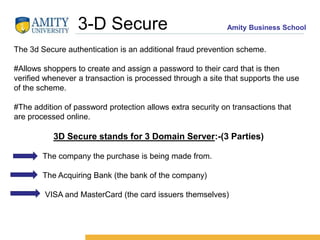
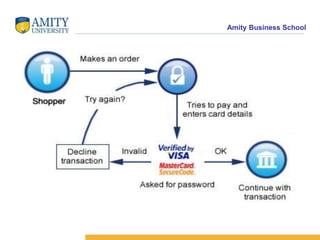
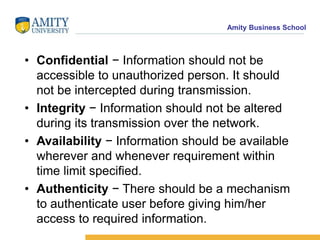
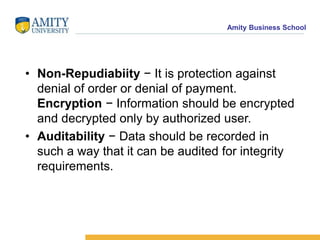
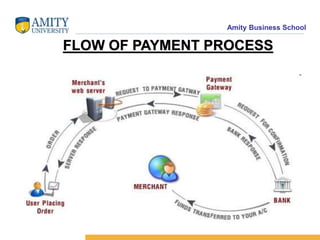
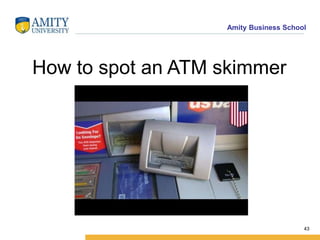
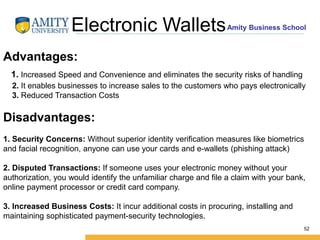
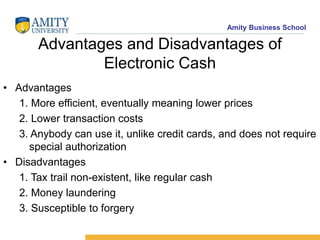
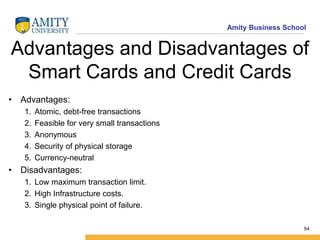
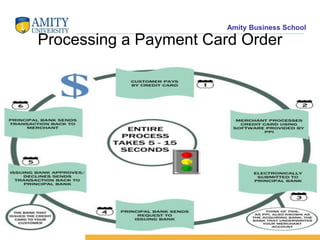
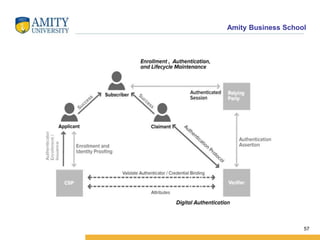
The document discusses electronic payment systems (EPS), detailing various models such as B2B, B2C, C2C, and C2B transactions, along with different payment methods including credit cards, debit cards, net banking, and mobile wallets. It also covers security measures like encryption, digital signatures, and tokenization to protect transactions, as well as potential risks involved in cyber banking and strategies to enhance security. Additionally, advancements in payment technology are highlighted, indicating a trend towards increased convenience and security in electronic transactions.


![Amity Business School
Hypertext Transfer Protocol (HTTP)
Web browsers typically use HTTP to communicate with web servers,
sending and receiving information without encrypting it. For sensitive
transactions, such as Internet e-commerce or online access to financial
accounts, the browser and server must encrypt this information. S-HTTP
is an obsolete alternative to the HTTPS protocol
for encrypting web communications carried over HTTP. HTTPS and S-
HTTP were both defined in the mid-1990s to address this need. S-HTTP
was used by Spyglass's web
server,[1] while Netscape and Microsoft supported HTTPS rather than S-
HTTP, leading to HTTPS becoming the de-facto standard mechanism for
securing web communications.
64](https://image.slidesharecdn.com/epsprojectsemester2finalpresentation-180427192017/85/Electronic-Payment-System-EPS-Presentation-64-320.jpg)