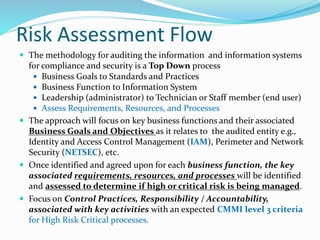
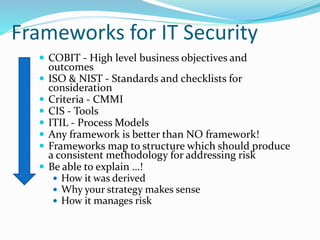
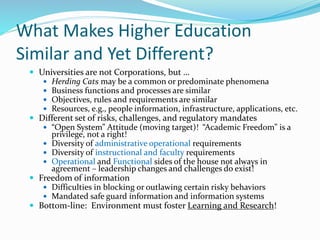
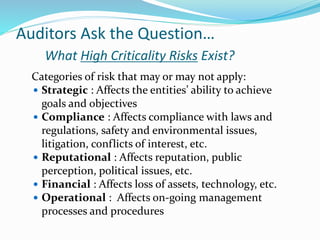
The document discusses an auditor's perspective on frameworks for information systems security in higher education. It provides an agenda for a session that will help attendees identify business goals and functions, understand critical success factors during an audit, evaluate internal control structures, and learn about available security standards and frameworks. The session guides will discuss challenges in auditing higher education from both a high and low level perspective. [END SUMMARY]

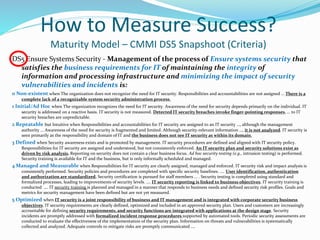
![Threats and the Facts
Privacy Right Clearinghouse
Chronology of Data Breaches 2,500,000 since January 2005
that have been reported
[www.privacyrights.org/ar/ChronDataBreaches.htm]
Ponemon –HRH 2008 Privacy Breach Index Survey (Sept 2008)
Self evaluation of overall performance of organization: -- 9%
gave an “A” -- 31% gave a “B” -- 26% gave a ”C” -- 29% gave a
“D” – 5% gave a “F” [www.HRH.com/privacy]
80 % believed their organizations experienced information
system data breaches and loss of customer and personal
information
50% Negligence, -- 29% Third-Party, 3% Hacker, --1% other
criminal activity;
36% 1 to 4 breaches involving 100 or records; 32% 5 to 8; 31%
9 or more](https://image.slidesharecdn.com/educausev4-220825222847-cbe57e17/85/Educause-V4-ppt-9-320.jpg)