Documentos de la CIA sobre el Plan Cóndor
•
0 likes•177 views
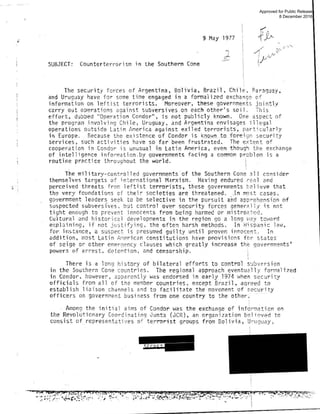
La CIA desclasifica documentos sobre la persecusión, tortura y asesinatos de líderes de izquierda durante las dictaduras de los años 70 en el Cono Sur.
Report
Share
Report
Share
Download to read offline
Recommended
cia 

1. The CIA was formed after World War 2 to centralize US intelligence gathering and analysis in response to failures like the Pearl Harbor attack.
2. The CIA was established by the National Security Act of 1947 to replace the OSS and analyze intelligence from all sources to brief policymakers.
3. The main roles of intelligence agencies like the CIA are to collect foreign intelligence, give early warning of crises, and inform policies and operations related to national security while protecting their sources and methods.
Role of CIA in Changing Strategic Operations of CIA

In American Renewal by, Steven Hook, “the first requirement of intelligence is timely delivery of relevant information to decision makers. To accomplish this mission decision makers must understand how intelligence works, take responsibility for investing in it, and share their strategies and tactics, specifies what they need and when. For its part to assist in going advantages over adversaries, intelligence has to focus on delivering enough information for the decision, not necessarily comprehensive knowledge”. The prime task assigned to CIA was to preserve the American interest and keep a sharp eye on its rivals. During cold war the greatest threat to American interest was from USSR and pro-communist states in the world. CIA carried out its clandestine services using different strategies. Assuming a power of influence in making policies according to its will, its role changed gradually from the traditional espionage activities. The conundrum of its covert operations at some time thought harmful for the state. Its transformation into a paramilitary force likely after 9/11 was also a matter of great concern. Using the advanced and bold technology CIA can operate in every state of the world. Everything beyond limitations is just devastating.
The unveiled stories about CIA during the cold war era and after 9/11 gave a clue about the influential role in shaping foreign policy. Mostly during the Democrats regime the influence of CIA and Pentagon have less influence in policy making than that of the republican regime. Along with traditional espionage CIA also operated covert actions from the beginning. From regime change to targeted manhunt and military operations CIA became quite controversial at every level. Some previous CIA officials say its function is to violate the laws of other states to gain intelligence. It shows that CIA has no moral grounds and gave no worth to any law. It even violates its own domestic law about torturing the suspected criminals. Its influence in domestic politics and FP in a democratic superpower is unjustified. The infiltration and intrusion within other states may escalate and prolong the crisis. The role of CIA in fighting war on terror and establishing peace at global level is considerable. The exploit of the policy makers by manipulating information also a concerning issue.
In Pakistan the infiltration of CIA operatives had been increased to a considerable level. It may also influence the domestic issues of Pakistan through different means. The infusion of these operatives should be refined and under the counter surveillance of Pakistani spy agency. CIA will remain quite active in Pakistan due to its geographic position and changing interest of great powers as Obama’s pivot to Asia policy. China’s surveillance also a factor for CIA to remain active in Pakistan as it may pose a threat to the American might in near future.
Intelligence Agencies, Law Enforcement, And The Prosecution Team

Jonathan M. Fredman, "Intelligence Agencies, Law Enforcement, and the Prosecution Team," 16 Yale Law and Policy Review 331 (1998).
Latin American Insurgency 2010b

Update & Perspective; Onging Insurgency in Latin America:
A Review and Perspective Concerning Emerging Tactical and Strategic Developments – Summer/Fall, 2010
Western sahara 2012 human rights report

This document summarizes the human rights situation in Western Sahara in 2012. It describes Morocco's control over most of the territory and its ongoing dispute with the Polisario Front, which seeks independence. Key human rights issues include Morocco restricting pro-independence views and associations. Credible reports indicate security forces engaged in torture, beatings and mistreatment of detainees, especially Sahrawi independence advocates. Twenty-four Sahrawis arrested in 2010 remained in detention without clear charges as of the end of 2012.
«Research services at the Motion Picture, Video and Recorded Sound Division o...

«Research services at the Motion Picture, Video and Recorded Sound Division o...Universitat de Barcelona - Facultat d’Informació i Mitjans Audiovisuals
Presentació corresponent a la conferència «Research services at the Motion Picture, Video and Recorded Sound Division of the National Archives and Records Administration (NARA): enhancing access and outreach», a càrrec de Carol Swain, arxivera de referència a la NARA. La conferència va tenir lloc a la Facultat de Biblioteconomia i Documentació de la Universitat de Barcelona el 15 de novembre de 2011.(U fouo) dhs assessment- future isil operations in the west could resemble di...

The document summarizes an intelligence assessment of a disrupted ISIL plot in Belgium in January 2015. It finds that the plot involved over 10 operatives across multiple European countries and was possibly directed by ISIL, indicating an increased capability for more complex attacks in the West. The plot's tactics, including use of firearms, IEDs, and impersonating police officers, could assist in identifying similar plots. Dispersed operations and encrypted communications posed challenges for detection.
FBI TSC

Phil Pulaski has 38 years of law enforcement experience and was the New York City Police Department’s (NYPD) Chief of Detectives where he was responsible for 3,600 personnel. During his more than 33 years serving with the NYPD, Phil Pulaski managed patrol, investigative, counterterrorism and other public safety operations. In the immediate aftermath of the September 11, 2001 terrorist attacks, Phil Pulaski managed the NYPD’s counterterrorism and weapons of mass destruction operations. He also supervised jointly with his FBI counterpart numerous terrorism related investigations including the 9-11 World Trade Center attack and October 2001 anthrax attacks. Phil Pulaski also was responsible for NYPD’s intelligence collection and analysis operations, and the daily counterterrorism deployments in NYC involving more than 300 uniformed personnel as well as aircraft and watercraft.
Recommended
cia 

1. The CIA was formed after World War 2 to centralize US intelligence gathering and analysis in response to failures like the Pearl Harbor attack.
2. The CIA was established by the National Security Act of 1947 to replace the OSS and analyze intelligence from all sources to brief policymakers.
3. The main roles of intelligence agencies like the CIA are to collect foreign intelligence, give early warning of crises, and inform policies and operations related to national security while protecting their sources and methods.
Role of CIA in Changing Strategic Operations of CIA

In American Renewal by, Steven Hook, “the first requirement of intelligence is timely delivery of relevant information to decision makers. To accomplish this mission decision makers must understand how intelligence works, take responsibility for investing in it, and share their strategies and tactics, specifies what they need and when. For its part to assist in going advantages over adversaries, intelligence has to focus on delivering enough information for the decision, not necessarily comprehensive knowledge”. The prime task assigned to CIA was to preserve the American interest and keep a sharp eye on its rivals. During cold war the greatest threat to American interest was from USSR and pro-communist states in the world. CIA carried out its clandestine services using different strategies. Assuming a power of influence in making policies according to its will, its role changed gradually from the traditional espionage activities. The conundrum of its covert operations at some time thought harmful for the state. Its transformation into a paramilitary force likely after 9/11 was also a matter of great concern. Using the advanced and bold technology CIA can operate in every state of the world. Everything beyond limitations is just devastating.
The unveiled stories about CIA during the cold war era and after 9/11 gave a clue about the influential role in shaping foreign policy. Mostly during the Democrats regime the influence of CIA and Pentagon have less influence in policy making than that of the republican regime. Along with traditional espionage CIA also operated covert actions from the beginning. From regime change to targeted manhunt and military operations CIA became quite controversial at every level. Some previous CIA officials say its function is to violate the laws of other states to gain intelligence. It shows that CIA has no moral grounds and gave no worth to any law. It even violates its own domestic law about torturing the suspected criminals. Its influence in domestic politics and FP in a democratic superpower is unjustified. The infiltration and intrusion within other states may escalate and prolong the crisis. The role of CIA in fighting war on terror and establishing peace at global level is considerable. The exploit of the policy makers by manipulating information also a concerning issue.
In Pakistan the infiltration of CIA operatives had been increased to a considerable level. It may also influence the domestic issues of Pakistan through different means. The infusion of these operatives should be refined and under the counter surveillance of Pakistani spy agency. CIA will remain quite active in Pakistan due to its geographic position and changing interest of great powers as Obama’s pivot to Asia policy. China’s surveillance also a factor for CIA to remain active in Pakistan as it may pose a threat to the American might in near future.
Intelligence Agencies, Law Enforcement, And The Prosecution Team

Jonathan M. Fredman, "Intelligence Agencies, Law Enforcement, and the Prosecution Team," 16 Yale Law and Policy Review 331 (1998).
Latin American Insurgency 2010b

Update & Perspective; Onging Insurgency in Latin America:
A Review and Perspective Concerning Emerging Tactical and Strategic Developments – Summer/Fall, 2010
Western sahara 2012 human rights report

This document summarizes the human rights situation in Western Sahara in 2012. It describes Morocco's control over most of the territory and its ongoing dispute with the Polisario Front, which seeks independence. Key human rights issues include Morocco restricting pro-independence views and associations. Credible reports indicate security forces engaged in torture, beatings and mistreatment of detainees, especially Sahrawi independence advocates. Twenty-four Sahrawis arrested in 2010 remained in detention without clear charges as of the end of 2012.
«Research services at the Motion Picture, Video and Recorded Sound Division o...

«Research services at the Motion Picture, Video and Recorded Sound Division o...Universitat de Barcelona - Facultat d’Informació i Mitjans Audiovisuals
Presentació corresponent a la conferència «Research services at the Motion Picture, Video and Recorded Sound Division of the National Archives and Records Administration (NARA): enhancing access and outreach», a càrrec de Carol Swain, arxivera de referència a la NARA. La conferència va tenir lloc a la Facultat de Biblioteconomia i Documentació de la Universitat de Barcelona el 15 de novembre de 2011.(U fouo) dhs assessment- future isil operations in the west could resemble di...

The document summarizes an intelligence assessment of a disrupted ISIL plot in Belgium in January 2015. It finds that the plot involved over 10 operatives across multiple European countries and was possibly directed by ISIL, indicating an increased capability for more complex attacks in the West. The plot's tactics, including use of firearms, IEDs, and impersonating police officers, could assist in identifying similar plots. Dispersed operations and encrypted communications posed challenges for detection.
FBI TSC

Phil Pulaski has 38 years of law enforcement experience and was the New York City Police Department’s (NYPD) Chief of Detectives where he was responsible for 3,600 personnel. During his more than 33 years serving with the NYPD, Phil Pulaski managed patrol, investigative, counterterrorism and other public safety operations. In the immediate aftermath of the September 11, 2001 terrorist attacks, Phil Pulaski managed the NYPD’s counterterrorism and weapons of mass destruction operations. He also supervised jointly with his FBI counterpart numerous terrorism related investigations including the 9-11 World Trade Center attack and October 2001 anthrax attacks. Phil Pulaski also was responsible for NYPD’s intelligence collection and analysis operations, and the daily counterterrorism deployments in NYC involving more than 300 uniformed personnel as well as aircraft and watercraft.
Jornal Macro março

O documento discute três tópicos principais: 1) a situação de falta d'água em Santo Antonio de Posse e as medidas tomadas pela prefeitura para resolver o problema, 2) eventos culturais e esportivos ocorrendo na região, como peças de teatro e competições de futsal, e 3) dicas de saúde e passeios para o final de semana na região.
Sin título 1

Este documento define y describe varios tipos de hackers y sus actividades, incluyendo white hats, black hats, samuráis, crackers, copyhackers, bucaneros, lamers, script kiddies, newbies, phreakers, spammers y otros. También describe diferentes tipos de ataques informáticos como intromisión, espionaje, interceptación, modificación, denegación de servicio, suplantación e ingeniería social. Por último, explica conceptos como entrada no autorizada en discos duros, acoso electrónico, criptografía, encriptamiento
VDE - O Software que otimiza sua produtividade

A União Europeia está preocupada com o aumento da desinformação online e propôs novas regras para combater as notícias falsas. As novas regras exigiriam que as plataformas de mídia social monitorassem o conteúdo ativamente e removessem rapidamente qualquer conteúdo considerado falso ou enganoso que possa prejudicar a saúde pública ou a segurança. No entanto, algumas organizações temem que as novas regras possam limitar a liberdade de expressão.
Fracturas

Una fractura ocurre cuando un hueso se rompe, lo que puede deberse a enfermedades óseas, impactos, caídas, accidentes de vehículos u otras fuerzas sobre el hueso. Existen fracturas cerradas donde la piel no está dañada y fracturas abiertas donde la piel también está lesionada. Los síntomas incluyen dolor intenso en la zona, deformidad, hinchazón e incapacidad de movimiento.
SBEPL-Profile

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive function. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
Apresentaã§ã£o the bridge pdf

Este documento descreve um jogo em desenvolvimento para reconstruir pontes em diferentes cidades. Os jogadores terão que escolher os materiais corretos para reconstruir as pontes de forma segura em cada nível. O jogo terá mecânicas sociais onde os jogadores podem se ajudar e competir uns com os outros.
Smsgc

Este documento describe el modelo de gestión de calidad del Hospital Universitario UANL. Incluye la historia de la calidad en el hospital, el proceso de certificación, lecciones aprendidas, desafíos persistentes y el modelo actual. El hospital ha mejorado su documentación y procesos a través de la certificación, pero todavía enfrenta desafíos como la resistencia al cambio y la rotación del personal.
Periodismo digital

Este documento introduce el periodismo digital, explicando que es el periodismo que se desarrolla principalmente en Internet. Describe las características del periodismo digital como la inmediatez, la capacidad de actualizar contenido en cualquier momento y la integración de enlaces. También discute la complementación entre medios tradicionales y digitales en el siglo 21.
Cad motoristas

Este documento fornece instruções sobre como cadastrar, consultar, alterar e remover motoristas no sistema Fusiontrak. Explica como acessar a tela de cadastro de motoristas, seu objetivo e os passos para inserir, buscar, editar e remover perfis de motoristas.
Maracy atual 09 10 13

O documento discute um projeto de estágio aplicado em psicologia organizacional que abordará o estudo do sofrimento psíquico no trabalho usando indicadores quantitativos e qualitativos. O projeto usará os conceitos de familiaridade, poder e limite subjetivo para entender a percepção dos trabalhadores sobre suas ocupações, grau de autonomia e capacidade de lidar com adversidades. O método será baseado em representações sociais e psicodinâmica do trabalho.
Cad pessoas

Este documento fornece instruções sobre como cadastrar, consultar, alterar e remover pessoas no sistema Fusiontrak. Explica como acessar a tela de cadastro de pessoas, seu objetivo e os passos para inserir, buscar, editar ou excluir registros, incluindo os campos necessários e botões para confirmar as ações. Também fornece informações de contato para obter suporte.
Gestao do sac

Este documento fornece instruções sobre como gerenciar reclamações de clientes no sistema Fusiontrak. Explica como cadastrar novos casos, consultar e editar casos existentes, e alterar o status dos casos. Também lista recursos adicionais e uma seção de perguntas frequentes.
O pequeno livro das grandes emoções

Este documento é uma coletânea de textos literários produzida pela UNESCO que contém poemas, contos, crônicas e letras de música de diversos autores brasileiros abordando temas emocionais. A introdução fornece dicas sobre como ler o livro e apreciar os diferentes gêneros literários presentes.
Copa metropolitana campanhas

O documento fornece estatísticas de campanha e artilheiros de vários times na Copa Metropolitana, incluindo número de jogos, vitórias, empates, derrotas, gols marcados e sofridos para cada time, e os principais artilheiros de cada equipe.
Apresentação1

O documento discute o conceito de pesquisa, destacando que: 1) A pesquisa está ligada a interesses sociais e políticos e deve ser um processo presente em todos os níveis educacionais; 2) A pesquisa não se resume apenas à abordagem empírica, abrangendo também os horizontes teóricos, metodológicos e da prática; 3) A pesquisa envolve tanto a descoberta quanto a criação de novos conhecimentos.
Projeto uso dos tci's na educação

Atividade relacionada ao curso: Mídia na Educação.
Consolidação e execução do Planejamento do uso dos TCI's na educação.
Learning More About Operation Condor

Operation Condor was a secret intelligence operation between the military dictatorships of Argentina, Brazil, Chile, Paraguay, and Uruguay from 1975-1977 to eliminate leftist individuals. They detained and tortured suspects in secret camps. Operation Condor extended this crackdown across South America, seeking to capture anyone who evaded the dictatorships. While the full details are still secret, reports indicate the US government privately supported Operation Condor, which launched a comprehensive attack on perceived leftist threats under the guise of national security.
Paper - Final disposition

This document discusses Operation Condor, an intelligence system between South American dictatorships in the 1970s-1980s that allowed them to seize, torture, and make political opponents disappear across borders. It analyzes the different techniques used by each dictatorship, with the Argentine junta choosing to kidnap, torture, drug, and throw opponents from planes to avoid witnesses and condemnation. The document examines how the military justified these actions through discourse portraying opponents as threats during wartime. It analyzes how this discourse was propagated by newspapers through biological metaphors positioning the military as doctors curing diseases, justifying the elimination of opponents.
More Related Content
Viewers also liked
Jornal Macro março

O documento discute três tópicos principais: 1) a situação de falta d'água em Santo Antonio de Posse e as medidas tomadas pela prefeitura para resolver o problema, 2) eventos culturais e esportivos ocorrendo na região, como peças de teatro e competições de futsal, e 3) dicas de saúde e passeios para o final de semana na região.
Sin título 1

Este documento define y describe varios tipos de hackers y sus actividades, incluyendo white hats, black hats, samuráis, crackers, copyhackers, bucaneros, lamers, script kiddies, newbies, phreakers, spammers y otros. También describe diferentes tipos de ataques informáticos como intromisión, espionaje, interceptación, modificación, denegación de servicio, suplantación e ingeniería social. Por último, explica conceptos como entrada no autorizada en discos duros, acoso electrónico, criptografía, encriptamiento
VDE - O Software que otimiza sua produtividade

A União Europeia está preocupada com o aumento da desinformação online e propôs novas regras para combater as notícias falsas. As novas regras exigiriam que as plataformas de mídia social monitorassem o conteúdo ativamente e removessem rapidamente qualquer conteúdo considerado falso ou enganoso que possa prejudicar a saúde pública ou a segurança. No entanto, algumas organizações temem que as novas regras possam limitar a liberdade de expressão.
Fracturas

Una fractura ocurre cuando un hueso se rompe, lo que puede deberse a enfermedades óseas, impactos, caídas, accidentes de vehículos u otras fuerzas sobre el hueso. Existen fracturas cerradas donde la piel no está dañada y fracturas abiertas donde la piel también está lesionada. Los síntomas incluyen dolor intenso en la zona, deformidad, hinchazón e incapacidad de movimiento.
SBEPL-Profile

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive function. Exercise causes chemical changes in the brain that may help protect against mental illness and improve symptoms.
Apresentaã§ã£o the bridge pdf

Este documento descreve um jogo em desenvolvimento para reconstruir pontes em diferentes cidades. Os jogadores terão que escolher os materiais corretos para reconstruir as pontes de forma segura em cada nível. O jogo terá mecânicas sociais onde os jogadores podem se ajudar e competir uns com os outros.
Smsgc

Este documento describe el modelo de gestión de calidad del Hospital Universitario UANL. Incluye la historia de la calidad en el hospital, el proceso de certificación, lecciones aprendidas, desafíos persistentes y el modelo actual. El hospital ha mejorado su documentación y procesos a través de la certificación, pero todavía enfrenta desafíos como la resistencia al cambio y la rotación del personal.
Periodismo digital

Este documento introduce el periodismo digital, explicando que es el periodismo que se desarrolla principalmente en Internet. Describe las características del periodismo digital como la inmediatez, la capacidad de actualizar contenido en cualquier momento y la integración de enlaces. También discute la complementación entre medios tradicionales y digitales en el siglo 21.
Cad motoristas

Este documento fornece instruções sobre como cadastrar, consultar, alterar e remover motoristas no sistema Fusiontrak. Explica como acessar a tela de cadastro de motoristas, seu objetivo e os passos para inserir, buscar, editar e remover perfis de motoristas.
Maracy atual 09 10 13

O documento discute um projeto de estágio aplicado em psicologia organizacional que abordará o estudo do sofrimento psíquico no trabalho usando indicadores quantitativos e qualitativos. O projeto usará os conceitos de familiaridade, poder e limite subjetivo para entender a percepção dos trabalhadores sobre suas ocupações, grau de autonomia e capacidade de lidar com adversidades. O método será baseado em representações sociais e psicodinâmica do trabalho.
Cad pessoas

Este documento fornece instruções sobre como cadastrar, consultar, alterar e remover pessoas no sistema Fusiontrak. Explica como acessar a tela de cadastro de pessoas, seu objetivo e os passos para inserir, buscar, editar ou excluir registros, incluindo os campos necessários e botões para confirmar as ações. Também fornece informações de contato para obter suporte.
Gestao do sac

Este documento fornece instruções sobre como gerenciar reclamações de clientes no sistema Fusiontrak. Explica como cadastrar novos casos, consultar e editar casos existentes, e alterar o status dos casos. Também lista recursos adicionais e uma seção de perguntas frequentes.
O pequeno livro das grandes emoções

Este documento é uma coletânea de textos literários produzida pela UNESCO que contém poemas, contos, crônicas e letras de música de diversos autores brasileiros abordando temas emocionais. A introdução fornece dicas sobre como ler o livro e apreciar os diferentes gêneros literários presentes.
Copa metropolitana campanhas

O documento fornece estatísticas de campanha e artilheiros de vários times na Copa Metropolitana, incluindo número de jogos, vitórias, empates, derrotas, gols marcados e sofridos para cada time, e os principais artilheiros de cada equipe.
Apresentação1

O documento discute o conceito de pesquisa, destacando que: 1) A pesquisa está ligada a interesses sociais e políticos e deve ser um processo presente em todos os níveis educacionais; 2) A pesquisa não se resume apenas à abordagem empírica, abrangendo também os horizontes teóricos, metodológicos e da prática; 3) A pesquisa envolve tanto a descoberta quanto a criação de novos conhecimentos.
Projeto uso dos tci's na educação

Atividade relacionada ao curso: Mídia na Educação.
Consolidação e execução do Planejamento do uso dos TCI's na educação.
Viewers also liked (20)
Similar to Documentos de la CIA sobre el Plan Cóndor
Learning More About Operation Condor

Operation Condor was a secret intelligence operation between the military dictatorships of Argentina, Brazil, Chile, Paraguay, and Uruguay from 1975-1977 to eliminate leftist individuals. They detained and tortured suspects in secret camps. Operation Condor extended this crackdown across South America, seeking to capture anyone who evaded the dictatorships. While the full details are still secret, reports indicate the US government privately supported Operation Condor, which launched a comprehensive attack on perceived leftist threats under the guise of national security.
Paper - Final disposition

This document discusses Operation Condor, an intelligence system between South American dictatorships in the 1970s-1980s that allowed them to seize, torture, and make political opponents disappear across borders. It analyzes the different techniques used by each dictatorship, with the Argentine junta choosing to kidnap, torture, drug, and throw opponents from planes to avoid witnesses and condemnation. The document examines how the military justified these actions through discourse portraying opponents as threats during wartime. It analyzes how this discourse was propagated by newspapers through biological metaphors positioning the military as doctors curing diseases, justifying the elimination of opponents.
Transnational organized crime its concept

Transnational organized crime (TOC) involves criminal groups that coordinate illegal activities across national borders. TOC groups use violence and corruption to traffic drugs, arms, people, toxic waste, and other illicit goods. Several international law enforcement agencies work to combat TOC, including Interpol, Europol, and the UN Office on Drugs and Crime. However, TOC remains a significant threat due to the challenges of international cooperation and the economic benefits some states and groups receive from criminal enterprises.
SLAVERY TO CIA EQUALS HUMAN TRAFFIC

This document provides definitions and context around international trafficking of women to the United States. It summarizes that an estimated 45,000-50,000 women and children are trafficked to the US annually by small crime rings and loose networks for sexual exploitation and forced labor. While traditionally coming from Southeast Asia and Latin America, victims are increasingly originating from Eastern Europe and the former Soviet Union. The document then discusses definitions of trafficking, organized crime, force, and consent in the context of US and international law.
Freedom fron Fear October 2008 First Issue. Magazine published by UNICRI and MPI

Freedom fron Fear October 2008 First Issue.
Magazine published by United Nations
Interregional Crime and Justice Research Institute
and MAX PLANCK INSTITUTE
for Foreign and International Criminal Law
Running head PROJECT PROPOSAL ON HUMAN TRAFFICKING 1PROJECT PR.docx

Running head: PROJECT PROPOSAL ON HUMAN TRAFFICKING 1
PROJECT PROPOSAL ON HUMAN TRAFFICKING 2
The Effectiveness of Anti-Human Trafficking Laws
Amber Miles
Savannah State University
Project Proposal: The Effectiveness of Anti-Human Trafficking Laws
Project Background
Human trafficking (HT) is considered and criminalized by the United Nations as a form of modern slavery. It is also considered to be a major human rights challenge for authorities both in the developed and developing economies. The crime manifests in the form of sex trafficking and labor trafficking. Early perceptions of human trafficking tended to view it as entailing sexual exploitation of women and girls. Today, the United States categorizes human trafficking as encompassing wide arrays of crimes and affecting boys and men as well (Federal Anti-Trafficking Laws, 2019). The federal government recognizes that human trafficking in the United States predominantly takes the form of domestic servitude, forced labor in construction industries, brides trafficking, and coerced working in agricultural plantations.
The United Nations defines trafficking in persons as “the recruitment, transportation, transfer, harboring or receipt of persons, by means of the threat or use of force or other forms of coercion, of abduction, of fraud, of deception, of the abuse of power or of a position of vulnerability or of the giving or receiving of payments or benefits to achieve the consent of a person having control over another person, for the purpose of exploitation” (Zimmerman & Kiss, 2017). While a lot of human trafficking takes place within the country, a recent trend in international trafficking has created cartels across the world that facilitate illegal movement of people mainly from poor, low-income countries to developed economies (Global Report on Trafficking in Persons, 2014). Countries such as the Netherlands, Romania, Nigeria, and Sierra Leone have been cited internationally as major origin and transit countries for human trafficking.
The impact of HT on individuals and economies cannot be understated. International human trafficking (IHT) is known to encompass drug trafficking. Trafficked persons are forced under threat to their lives to traffic narcotics across international borders. The risk posed to victims is immense since it not only impairs their mental capacity but also exposes them to punitive sentences if caught trafficking drugs on behalf of their controlling masters. Besides cognitive impairment and potential memory loss, victims of HT are exposed to despicable physical abuse including rape, sexual slavery, servitude, and aggravated assault resulting in bodily harm. In other instances, victims are abused and killed. Analysis by the U.S State Department of recent cases of HT indicate that a significant number of victims are children who are duped under the pretext of finding a better life abroad or in large urban centers where they cannot be easily identified.
Des.
THB_Corso Scip

The document discusses human trafficking and smuggling of migrants. It notes that while trafficking often involves smuggling, smuggling does not always lead to trafficking. Trafficking is of greater social concern due to purposes like sexual exploitation and forced labor. Trafficking and smuggling operations typically involve international criminal networks across multiple countries. Effective investigation requires international cooperation and a unified approach that considers the criminal organizations and protection of victims.
The churchwomen murders

The long arm of American law. 1st writ should stand for something, but people think it is humorous to piss on fire;stinky!
Hr report 2015 eg (2)

The document summarizes the 2015 human rights report for Equatorial Guinea. It describes numerous human rights violations throughout the country, including arbitrary arrest and detention, unlawful detention of children, and repression of fundamental freedoms. It provides details on lack of due process, suppression of freedom of expression and assembly, violations of children's rights, and restrictions on freedom of movement. Political opponents faced harassment, arrest, and banishment, while security forces committed abuses against civilians with impunity.
415610_HONDURAS-2022-HUMAN-RIGHTS-REPORT.pdf

El Departamento de Estado de Estados Unidos presentó este lunes un informe sobre las prácticas de derechos humanos en Honduras durante el año 2022, en que resaltó que la corrupción y la falta de transparencia fueron dos problemas graves en el primer año del Gobierno de la presidenta Xiomara Castro, del partido Libertad y Refundación (Libre, de izquierda).
El informe resalta, principalmente, que el 2 de febrero de 2022 el Congreso Nacional de Honduras aprobó una ley de amnistía política denominada "Ley para la reconstrucción del Estado constitucional de derecho y para que los hechos no se repitan".
La misma incluye, entre otras, la absolución de delitos penales, tales como abuso de autoridad, violación de los deberes de los funcionarios y malversación de caudales públicos.
En ese sentido, el Departamento de Estado rescató que la ley de amnistía absolvió de algunos de esos delitos a funcionarios que trabajaron durante el gobierno de Manuel Zelaya (2006-2009), quien fue derrocado por un golpe de Estado el 28 de junio de 2009 por promover un proyecto de constituyente a través de una consulta popular denominada "Cuarta Urna".
Zelaya, más conocido como "Mel", es esposo y asesor presidencial de la actual presidenta de Honduras, Xiomara Castro. Además de ser el coordinador general del Partido Libre.
Entre los funcionarios beneficiados se encuentran el exministro de la Presidencia, Enrique Flores Lanza y el exgerente de Hondutel, Marcelo Chimirri.
Se conoce que más de medio centenar de solicitudes de extinción de responsabilidad penal fueron presentadas ante los entes competentes, en tanto que dirigentes de Libre aseguran que siete mil campesinos procesados por delitos que no existen podrían resultar favorecidos.
Hasta octubre, al menos 24 acusados utilizaron la ley para que se desestimaran los casos de corrupción.
Venezuela Alert for free, fair and competitive elections (Report #18, July 2013)

Venezuela Alert for free, fair and competitive elections (Report #18, July 2013)Monitoreo Ciudadano (@yomonitoreo)
Corruption undermines Venezuelan democracy
Impunit in cases of anonymous threats agains journalists in Venezuela
Constitutional Chamber of Supreme Court favors the government
Pro-government political party physically attacks members of the Democratic Alternative and bars them from speaking in parliament
Border report update mind mix radio quintus dias 06072019

Quintus Dias updates everyone on the latest US-Mexico Border information involving Irineo Mujica, and the two big caravan organizing groups operating out of Chicago and Nevada. PUEBLO SIN FRONTERAS, CENTRO SIN FRONTERAS - TWO GROUPS SPONSORING CARAVANS
Sij 03-00167

There are four major types of global interaction and these include:
a) Communication, or the movement of information, including
the transmission of beliefs, ideas, and doctrines
b) Transportation, the movement of physical objects, including
war material and personal property as well as merchandise
c) Finance, the movement of money and instruments of credit
d) Travel and movement of persons. This includes voluntary
movement which is travel and migration as well as involuntary
movement which is human trafficking and forced migration
Assessing the impact_of_globalization_on_human_tra

Ever since contemporary globalization came on the world scene around 1990s, free movement of goods, services and ideas grew as a result of reduced barriers to international movement trade and investment. The economic flow of goods and services has gone along with movement of people across the globe. The voluntary and involuntary movement of people occurs around world and is associated with opportunities that exist out there. Communication and flow of information is in real time in the current period from one corner of the globe to the other is occurring at high speed. Beliefs, ideas and culture have been relayed fast through the Internet, Smart Phones and other Communication devices.
Intelligence Collection

Intelligence collection methods are used by U.S. intelligence agencies to gather information and protect national security. Different agencies employ various collection disciplines including signals intelligence, imagery intelligence, and human intelligence. Open source intelligence is also widely used, accounting for 80-90% of information. Intelligence collection requires balancing resources, time constraints, and the needs of different agencies to provide policymakers with needed information through diverse techniques.
Stage 3-6

This document provides an assessment of assets that could be used for a covert operation called PBSUCCESS to overthrow the communist government of Guatemalan president Jacobo Arbenz. It describes political opposition groups within Guatemala, disaffected elements within the Guatemalan military, and paramilitary forces that could be mobilized both inside and outside the country. Estimates indicate there are thousands of civilians pledged to support the operation and defections could be achieved in many military garrisons. The document evaluates intelligence sources and organizations that could coordinate the assets to execute PBSUCCESS.
Departement d'Etat: Rapport sur la Situation Droits Humains en Haiti en 2016

Ce document est de 36 pages est le rapport annuel du Département d'Etat sur la situation des droits en Haiti en 2016.
Reduce Terrorism Might Infringe.docx

Reducing terrorism is challenging and methods used can infringe on civil liberties. General measures like airport screenings affect many people, while more specific methods profile and monitor potential suspects. Some government actions that aim to reduce terrorism may violate constitutional rights to free speech, unreasonable searches/seizures, due process, and others. There is an argument that some infringement of rights is necessary to detect and reduce terrorism, though others believe infringement is not justified and measures must respect civil rights. As a forensic psychologist, one's view on this issue could impact the types of jobs they may consider.
Trafficking in persons_2012_web

The document is the 2012 Global Report on Trafficking in Persons published by the United Nations Office on Drugs and Crime (UNODC). It provides information on trafficking patterns, flows, victims, and traffickers globally and by region based on officially reported data. Key findings include that at least 136 nationalities were trafficked to 118 countries between 2007-2010, and the percentage of detected child victims increased from 20% in 2003-2006 to 27% in 2007-2010. Regional trends and challenges to effective responses are also examined, such as low conviction rates compared to other crimes. The report aims to further understanding of human trafficking to strengthen policies and criminal justice responses.
Global Report on Trafficking in Persons 2012

The document is the 2012 Global Report on Trafficking in Persons published by the United Nations Office on Drugs and Crime (UNODC). It provides information on trafficking patterns, flows, victims, traffickers and forms of exploitation globally and by region based on officially reported data from 2007-2010. Key findings include that at least 136 nationalities were trafficked to 118 countries, and the percentage of detected child victims increased from 20% in 2003-2006 to 27% in 2007-2010. Regional trends and challenges responding to trafficking are also examined, such as low conviction rates globally similar to rare crimes in some countries. The report aims to further understanding of human trafficking to inform criminal justice responses and policies.
Similar to Documentos de la CIA sobre el Plan Cóndor (20)
Freedom fron Fear October 2008 First Issue. Magazine published by UNICRI and MPI

Freedom fron Fear October 2008 First Issue. Magazine published by UNICRI and MPI
Running head PROJECT PROPOSAL ON HUMAN TRAFFICKING 1PROJECT PR.docx

Running head PROJECT PROPOSAL ON HUMAN TRAFFICKING 1PROJECT PR.docx
Venezuela Alert for free, fair and competitive elections (Report #18, July 2013)

Venezuela Alert for free, fair and competitive elections (Report #18, July 2013)
Border report update mind mix radio quintus dias 06072019

Border report update mind mix radio quintus dias 06072019
Assessing the impact_of_globalization_on_human_tra

Assessing the impact_of_globalization_on_human_tra
Departement d'Etat: Rapport sur la Situation Droits Humains en Haiti en 2016

Departement d'Etat: Rapport sur la Situation Droits Humains en Haiti en 2016
More from teleSUR TV
Láminas crecimiento económico Venezuela.pdf

Láminas del crecimiento económico que se ha registrado en Venezuela pese al bloqueo y las sanciones.
Conversación traducida de amenazas contra la periodista.pdf

María Corina Machado recibió soborno de $3.2 millones de un lobby estadounidense para entregar PDVSA a Chevron si ganaba elecciones
Denuncia realizada por la periodistas.pdf

María Corina Machado recibió soborno de $3.2 millones de un lobby estadounidense para entregar PDVSA a Chevron si ganaba elecciones
Imágenes de amenazas traducidas - Williams.pdf

María Corina Machado recibió soborno de $3.2 millones de un lobby estadounidense para entregar PDVSA a Chevron si ganaba elecciones
Imágenes de documento con firma de Juan Guaidó.pdf

María Corina Machado recibió soborno de $3.2 millones de un lobby estadounidense para entregar PDVSA a Chevron si ganaba elecciones
Imágenes de documentos originales de HSH.pdf

María Corina Machado recibió soborno de $3.2 millones de un lobby estadounidense para entregar PDVSA a Chevron si ganaba elecciones
Observatorio Lawfare: Violencia y rol EE.UU. en Ecuador.pdf

1) El documento describe el aumento de la violencia en Ecuador y los acuerdos de seguridad recientes entre Ecuador y EE.UU. En 2023 se registraron 7,800 muertes violentas en Ecuador, la tasa más alta en la historia del país. 2) EE.UU. ha incrementado su asistencia militar a Ecuador, convirtiéndolo en el principal receptor en la región con $172 millones en 2021-2022. En 2023 Ecuador y EE.UU. firmaron varios acuerdos de seguridad, incluyendo uno que otorga inmunidad al personal militar estadoun
COMUNICADO NICARAGUA.pdf

El gobierno de Nicaragua anuncia que las clases se reanudarán el miércoles 12 de octubre debido a que las observaciones de los organismos meteorológicos indican que es seguro. El gobierno y el Ministerio de Educación recomiendan a los padres garantizar las medidas de prevención y protección al llevar a los estudiantes a la escuela.
Alimentos Solidarios a Familias Cubanas.pdf

Un barco llamado Augusto C. Sandino zarpó de Puerto Arlen Siu en El Rama, Nicaragua el 18 de agosto con alimentos para familias cubanas. El barco llegará a Puerto Mariel, Cuba el 22 de agosto por la mañana llevando comida para Cuba como muestra de solidaridad del pueblo nicaragüense.
Nota Nicaragua.pdf

Nota del Gobierno de Nicaragua enviada al secretario del Departamento de Estado de EE.UU.
Argentina1.pdf

Representantes de varios partidos y movimientos políticos de izquierda en Argentina envían un saludo fraternal al pueblo de Nicaragua en el 43 aniversario de la Revolución Sandinista. Destacan que el proceso de transformación nicaragüense ha resistido los embates del imperialismo y ha elevado los indicadores sociales y democráticos a pesar de la agresión. Ratifican su solidaridad con el valiente pueblo nicaragüense, su gobierno y su revolución.
Europa.pdf

El documento celebra el 43 aniversario de la Revolución Sandinista de Nicaragua y expresa apoyo y solidaridad con el presidente Daniel Ortega, la vicepresidenta Rosario Murillo y el pueblo nicaragüense. Destaca los logros del gobierno sandinista en implementar programas sociales que han mejorado la calidad de vida de los nicaragüenses y convirtieron a Nicaragua en un país reconocido internacionalmente por sus políticas sociales. Finalmente, reafirma el apoyo del Comité Europeo de Solidaridad con la Revolución Popular Sand
Puerto Rico.pdf

El documento es una carta del Movimiento Independentista Nacional Hostosiano (MINH) de Puerto Rico al Embajador de Nicaragua en la ONU, Jaime Hermida Castillo. La carta felicita al pueblo de Nicaragua por el 43 aniversario de la Revolución Sandinista y expresa su solidaridad con la lucha del pueblo nicaragüense por construir una sociedad mejor a pesar de las adversidades. También destaca el firme apoyo de Nicaragua a la lucha por la independencia de Puerto Rico.
Yibuti.pdf

El Gobierno de Yibuti envía sus felicitaciones a Nicaragua por el aniversario del triunfo de la Revolución Sandinista
Plataforma Dominican@s por Derecho.pdf

Organizaciones de la Plataforma Dominican@s por Derecho (DXD) pidieron al Estado enfrentar las barreras administrativas que impiden la restitución de nacionalidad a miles de dominicanos.
Comunicado solidaridad Cuba.pdf

El documento expresa las condolencias del presidente de Nicaragua y su esposa al pueblo de Cuba por la tragedia en el Hotel Saratoga en La Habana, donde hubo muertos y heridos. Destaca la solidaridad del pueblo cubano al asistir a los heridos y acompañar a los familiares, lo que demuestra la unidad indisoluble del pueblo cubano y la fuerza de su revolución. Finaliza enviando amor y apoyo revolucionario a los familiares de las víctimas.
MINREX - NOTA DE PRENSA.pdf

El documento expresa el compromiso de Nicaragua con la paz mundial y los mecanismos de diálogo para lograrla. Nicaragua apoya todos los esfuerzos humanitarios que se realicen con respeto e imparcialidad ante conflictos que ponen en riesgo vidas. Nicaragua cree que excluir o suspender la participación de países en organismos internacionales viola los derechos humanos y el derecho internacional. Nicaragua continuará condenando todas las formas de conflicto y promoviendo la paz y el diálogo.
More from teleSUR TV (20)
Conversación traducida de amenazas contra la periodista.pdf

Conversación traducida de amenazas contra la periodista.pdf
Imágenes de documento con firma de Juan Guaidó.pdf

Imágenes de documento con firma de Juan Guaidó.pdf
Observatorio Lawfare: Violencia y rol EE.UU. en Ecuador.pdf

Observatorio Lawfare: Violencia y rol EE.UU. en Ecuador.pdf
Recently uploaded
A draft Ukraine-Russia treaty from April 2022

A draft Ukraine-Russia treaty from April 2022, published here in full for the first time.
Snigdha-Sreenath-Minor-v-Travancore-Devaswom-Board-WPCNO-39847-OF-2023-2024-L...

केरल उच्च न्यायालय ने 11 जून, 2024 को मंडला पूजा में भाग लेने की अनुमति मांगने वाली 10 वर्षीय लड़की की रिट याचिका को खारिज कर दिया, जिसमें सर्वोच्च न्यायालय की एक बड़ी पीठ के समक्ष इस मुद्दे की लंबित प्रकृति पर जोर दिया गया। यह आदेश न्यायमूर्ति अनिल के. नरेंद्रन और न्यायमूर्ति हरिशंकर वी. मेनन की खंडपीठ द्वारा पारित किया गया
Youngest c m in India- Pema Khandu Biography

Pema Khandu, born on August 21, 1979, is an Indian politician and the Chief Minister of Arunachal Pradesh. He is the son of former Chief Minister of Arunachal Pradesh, Dorjee Khandu. Pema Khandu assumed office as the Chief Minister in July 2016, making him one of the youngest Chief Ministers in India at that time.
Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75

Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75LUMINATIVE MEDIA/PROJECT COUNSEL MEDIA GROUP
From his beginnings with a daily newspaper, he moved easily through Newsweek magazine to cable news and, later, to the frontiers of online journalism.Essential Tools for Modern PR Business .pptx

Discover the essential tools and strategies for modern PR business success. Learn how to craft compelling news releases, leverage press release sites and news wires, stay updated with PR news, and integrate effective PR practices to enhance your brand's visibility and credibility. Elevate your PR efforts with our comprehensive guide.
在线办理(latrobe毕业证书)拉筹伯大学毕业证Offer一模一样

学校原件一模一样【微信:741003700 】《(latrobe毕业证书)拉筹伯大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
13062024_First India Newspaper Jaipur.pdf

Find Latest India News and Breaking News these days from India on Politics, Business, Entertainment, Technology, Sports, Lifestyle and Coronavirus News in India and the world over that you can't miss. For real time update Visit our social media handle. Read First India NewsPaper in your morning replace. Visit First India.
CLICK:- https://firstindia.co.in/
#First_India_NewsPaper
Recently uploaded (8)
Snigdha-Sreenath-Minor-v-Travancore-Devaswom-Board-WPCNO-39847-OF-2023-2024-L...

Snigdha-Sreenath-Minor-v-Travancore-Devaswom-Board-WPCNO-39847-OF-2023-2024-L...
Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75

Howard Fineman, Veteran Political Journalist and TV Pundit, Dies at 75
Documentos de la CIA sobre el Plan Cóndor
- 1. ' ... : 9 Hay 1977 SUBJECT: Counterterrorism in the Southern Cone I I III il The sec~rity forces of Argentina, Bol ivia , Brazil, Chile, ~araguay. and Uruguay have for some time engaged in a fonna1 i zed exchange of information on leftist terrorists . Moreover, these goverr.ments jointly c~rry out operations against subversives on each other's soil. This effort, dubbed "Operation Condor", is not pub1i c1y known. One aspect of the program involving Chile, Uruguay , and Argentina envisages i l legal operations outside Latin America against exiled terrorists, par ticul arly in Europe . Because the existence of Condor is kn.Q_wn..to.foreism security services, such activities have so far been frustrated . The extent of cooperat ion i n Condor is unusual in Latin America, even though the exchange of intelligence informaticn.by governments facing a common prcblem is a routine practice throughou t the world. i The military-controlled governments ·of the Southern Cone alI consider themselves t argets of international M.!rxism. Having endured re:~l a nd perceived threats from leftist terror ists , these governments t2li ~ve that th~ very foundati ons of their societies arethreatened..In m.ost cases, government leaders seek to be selective in the pursuit a~d apprehensi on of suspected subvers fves, b~t cont rol over security forces gener i1ly is not tight enough to prevent innocents from being harmed or mistre~t~~ Cultural and historic2l developments in the region go a l ong way tcwa rd explaining, if not justifying, the often harsh methods. In Hispanic l a1·1 , for. instance, a suspect is presumed guilty until proven innocent . In addition, most Latin A;1erican constitutions have pr-ovi s ions f or states of seige or other emer0ency clauses which greatly increase the gove rnm~nts ' powers of arrest, detention , Jn~ censorship . iI There i s a long history of bil ateral efforts to control s~bv2rsion in the Southern Cone countr ies. The reg ional approach eventual l y formal ized in Condor, however , oPpdrently was endor·sed i n early .1974 when secur ity officials f rom all of the member countries, except Brazi l, agreed to establi sh lioison channels and to facilitate the movement of secur i ty officers on government business from one country to the other; · · · Among the initial aims of Condor was the exchange of i nformation on the Revolutionary Coordinating Junta (JCR), an organization believed to consist of. representatbes of terroris t groups from Bolivia, Uruguay, Approved for Public Release 8 December 2016
- 2. . I Chile, ArgPntind, 2nd P~raguay. The JCR coordi ~~te~ ~ctivities nnd provides propJ).'lnda end logist i cal support fer i ! s member~: . Thf' ,)IJnt a has representa ti ves in Europe , and they are believed t o have been invol ve-d i n the assa ssi nat ions in Paris of the Bo li vian ambassador to France last f1ay and an Urugua~;an mil itary attache i n 1974. The attache had been involved i n the successful campaign to suppress Uruguay's terrorist Tupa~aros.a member gr oup of JCR. i Condor's overa1T campaign against subvers ion reportedly .,.,as inten- s ified l ast summer 1vhen members gathered i n Santiago t o organ ize more detailed, long-range plans. Decisions included: The development of a basic computerized data bank in San·tiago. All members will contribute information on known or suspected terrorists. Brazil ag reed to provide ·gear for "Condortel'' ··- t he group's communications network. The basic mission of Condor teams to be sent overseas reportedly was "to liquidate" top- leve l terrorist leaders. Non-terrorists ~l so were reportedl y candidat~s for assassination; Uruguayan oppositici8 politician Wilson Ferreira, i f he should travel to Europe. and some l ead~rs of /l.mnest.r Internat.ion •·;Pre tr.entioned as t ar ge ts. Ferre ira may hi'l'.'e heen rer.:oved from the 1ist , however, because he is conside red to h.1v~ good con tacts among US c:on~;res5;;Jen . A training course •t~as held in f1uenos Aires for the team headin9 o•1erseas. More recently Condon leaders 1•1ere con- s idering the di spatch of a team to London -- disguised as businessmen - - to monito r "s uspic ious activity" in Europe. Anotj]er proposal under study included the collecti(tn of material on the membership, locat~on, 2nd political acti vi t ies of human rights groups in order to identify and expose their sociulist and l·larxist connections . Similar data reportr.dly are to be coll ected on church and third-world groups. Evidence, although not conclusive, indicates that cooperation among security forces in the Sou thern Cone extends beyond legal methods . last Hay, for example, c.:r;;:ed men r dn::>acked the offices of t he Argentine Catholic Commission on Irr.mior~tion and stol e records containina i nform.Hion on thousands of refu~1ees Jnd ir.lTTii gr ants. The Ar gentine police did not investigate t he crir.e --a signal that latin refugees , princ i pally from Ch i le 2nd Uruguay were no lange. welcome. A mon th l ater . 24 Chilean and lh·uguay refu gees , m3ny of v1hom 1vere t he subjects of commissi on files, were kidnapped and tortured . After their re leas e , some of the ref11gees insisted 2 Approved for Public Release 8 December 2016
- 3. their interro0.1tors ·i'?re security officers from Chi le Dnc! Uruguay. 1 numb~r of UruquJi<1:1S 'Jere held in Buenos Ai res last swr.m>?r for t.,.m weeks and th~n fl o,.,r, to 1-:ontcvideo i n an Uruguayan plane. Uruguayan mi litary officers offered to spctre them their 1i ves if they wou1d r19n.:e to all ov1 themselves to be 'captured '' by authorities -- as if they were an armed group attempting to invade the country. Moreover, b-10 nrominent political exiles in .l'1rgenti na here killed under mysterious circumstances. Condor also is engaged in non-violent activities, including psychological ·,;a rfare and a propaganda campaign. These programs heavily use the nedio to pu bli cize crimes .and atrocities committed by terrorists. By appealing to national pride and the national conscience, these programs aim to secure· the support of the citizenry i n the hope t hey 1"ill report anything out of the ordinary in their neighborhoods. Propaganda campai~ns are constructed so that one member country publ ishes info rmation useful to another -- Hithout revealing that the beneficiary was in foct the source. For example, Bol ivia and Argentina reportedly are plann ing to launch a campaign against the Catholic Church and other religious qroups that allegedly support leftist movements~ Bolivia will col lect information on the groups and then send i t to Argentina for publication. The Condor communications system J,.JSes Member countries communicate via radio and an open channel voice ecur ty at on or s operat ons center n Buenos Aires, and compartmentation has been. increas.ed. In addition. once a Condor member has declined to participate in an operation, he · ;~ excl uded from ull f tn-ther details of that p Bolivi y not be Outside the Condor umbrella, bilateral cooperation between other security organi zations i n the region also is stron-g. · For·-example, intel l igence organi zations in Argentina , Uruguay, and Chile work together close1Y. Each security organization assigns advisers to the other countri~: primarily to identify subversives in exi le. 3 .. cate.....,. . .. -~~ Approved for Public Release 8 December 2016
