More Related Content
PDF
PDF
DOC
DOCX
PDF
Accelerating the ant colony optimization by PDF
DOC
DOCX
Viewers also liked
PDF
DOCX
DOCX
DOCX
DOCX
PDF
Some alternative ways to find m ambiguous binary words corresponding to a par... DOCX
PDF
Vulnerability scanners a proactive approach to assess web application security PDF
A S T A S42 O P E N E S P DOCX
DOC
DOCX
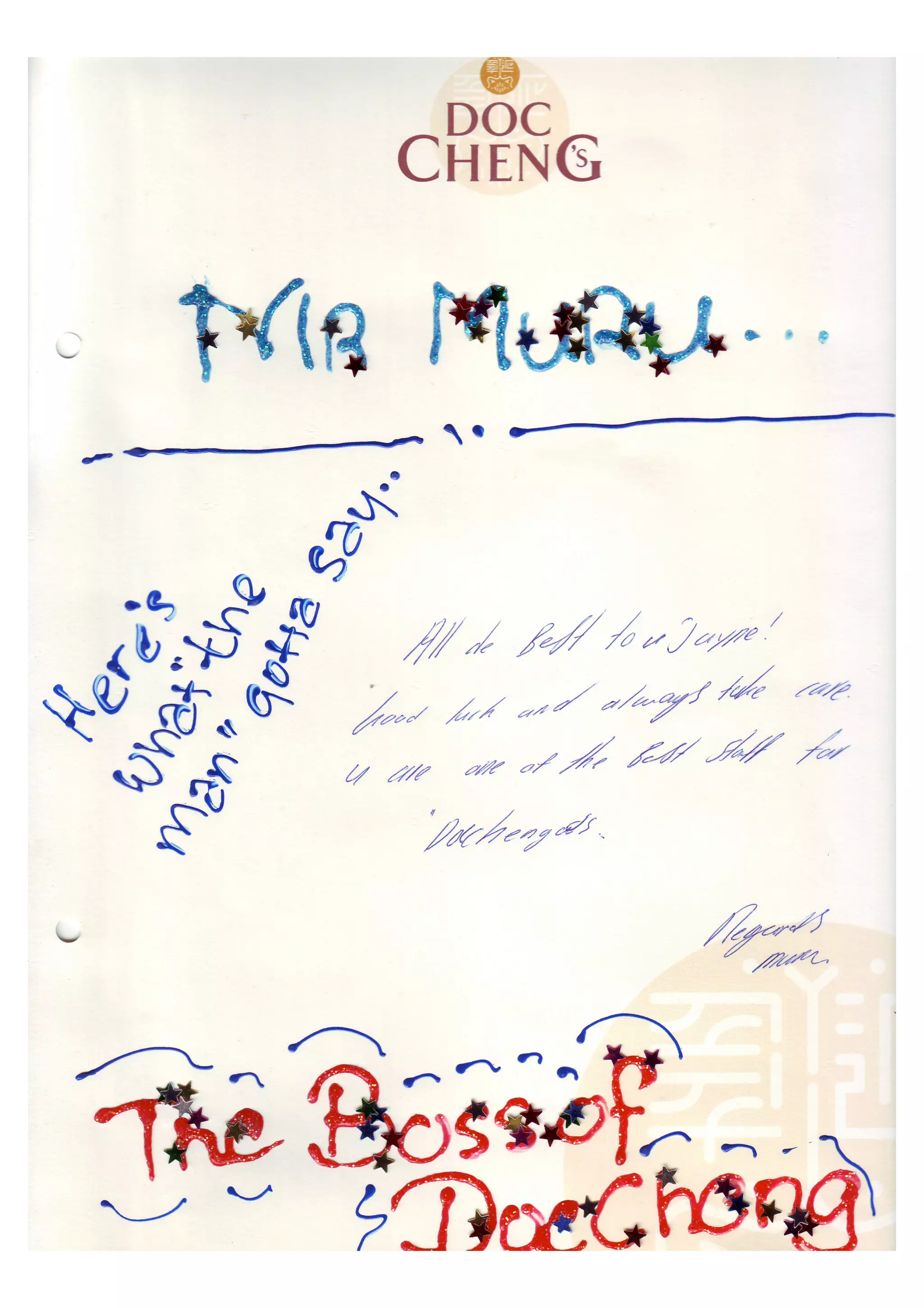
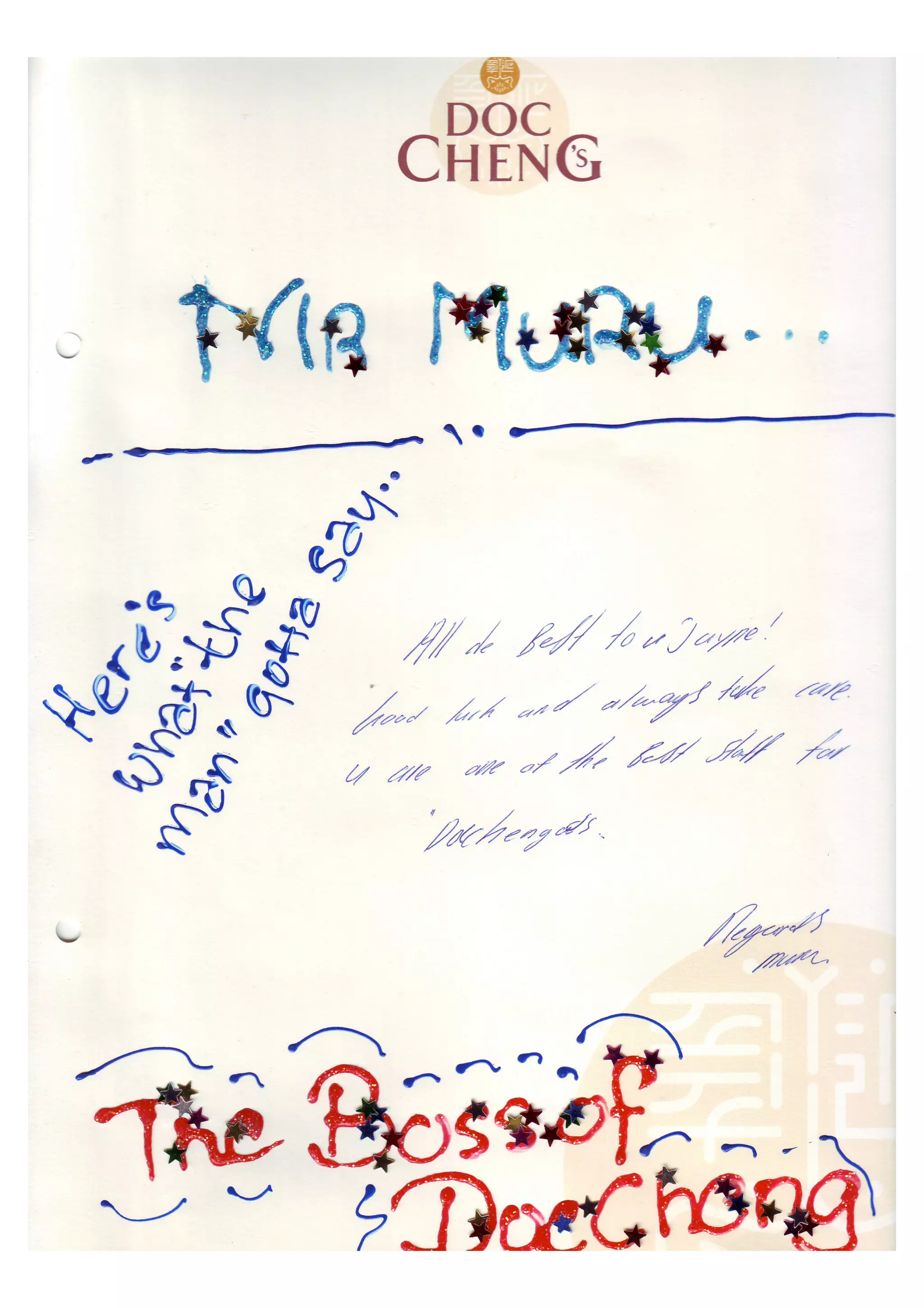
More from Jayne Goh 吴笠绮
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
Internship Evaluation Form PDF
PDF
Proposal Sustainable Shopper Traffic