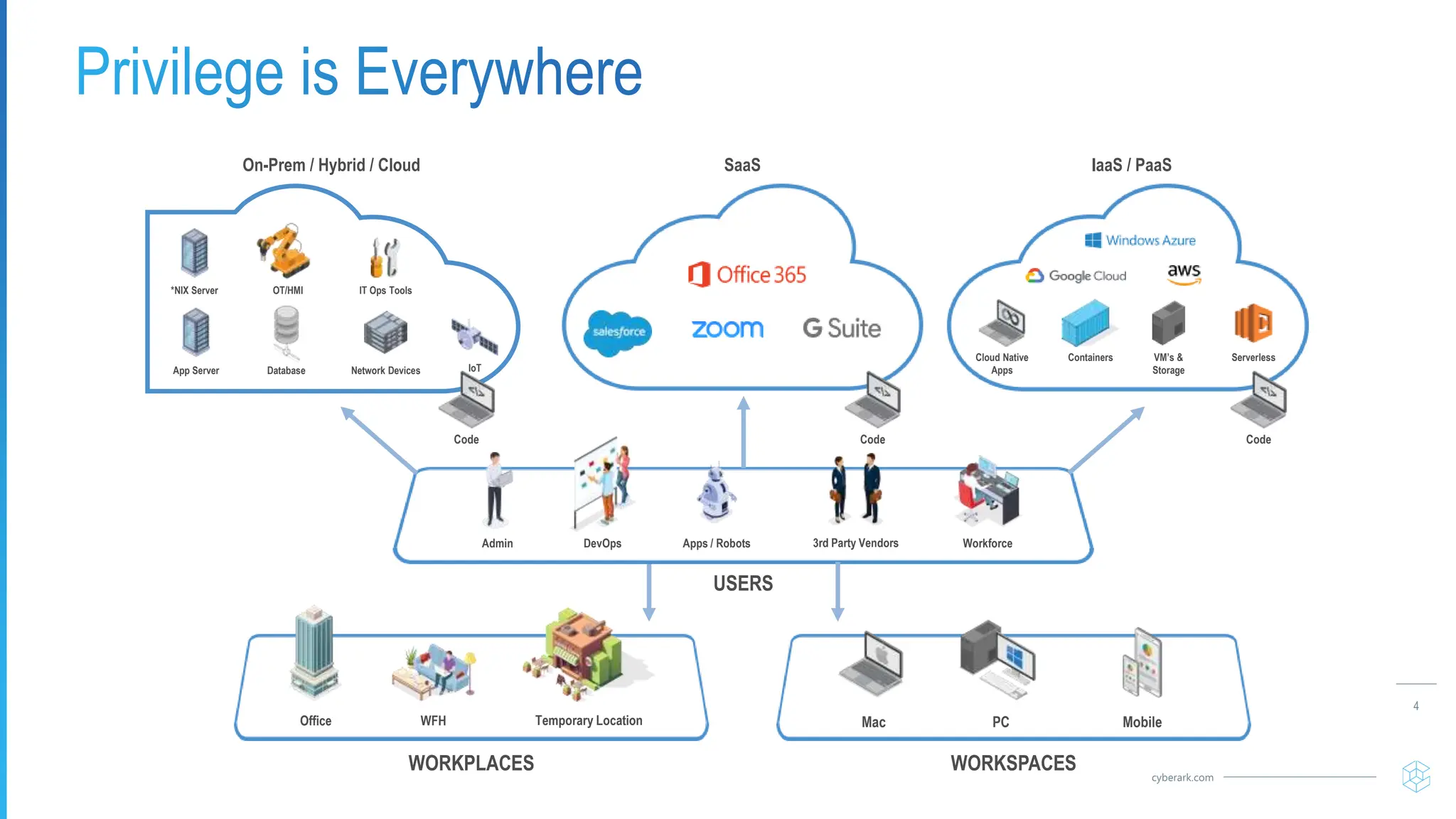
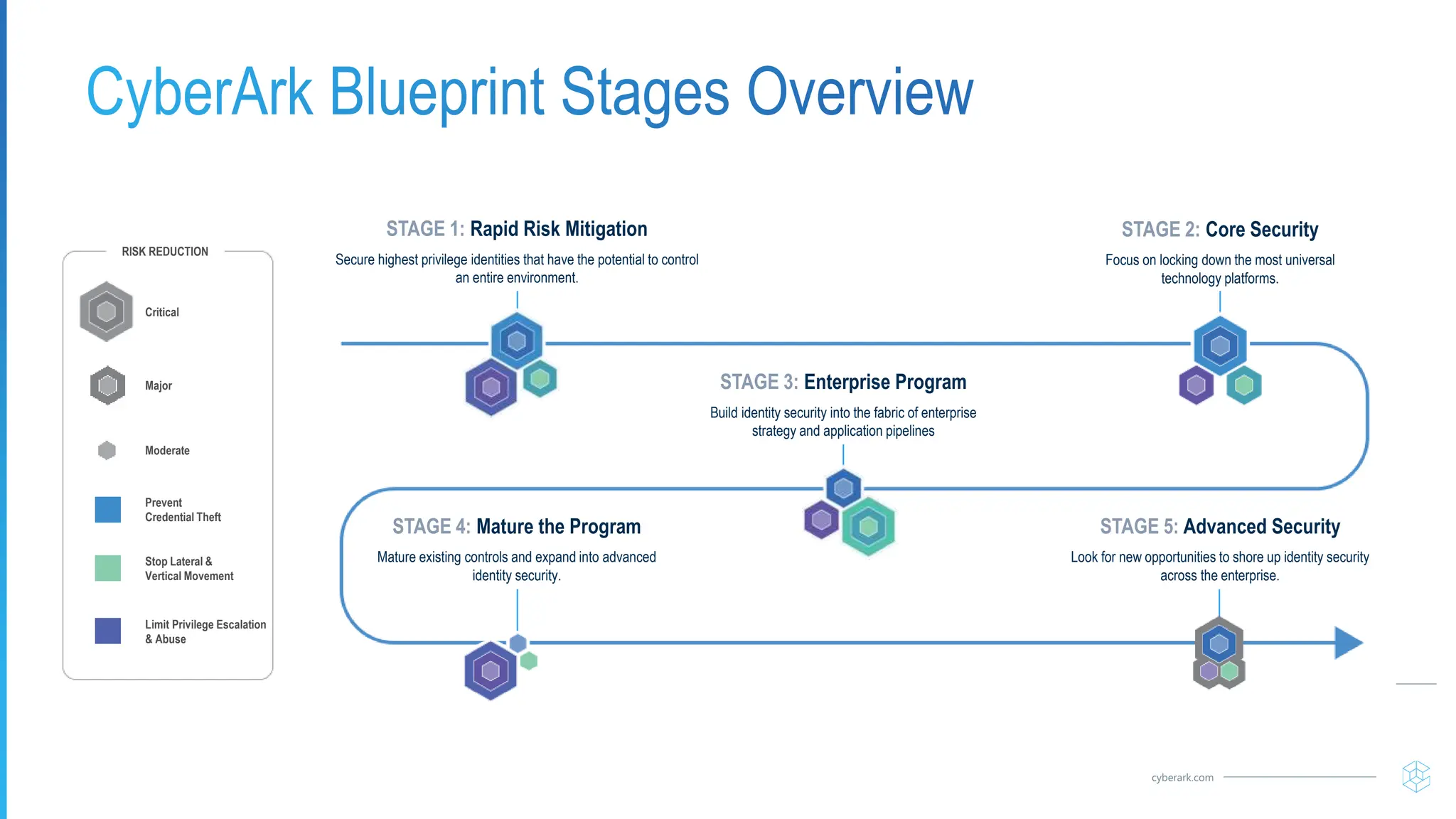
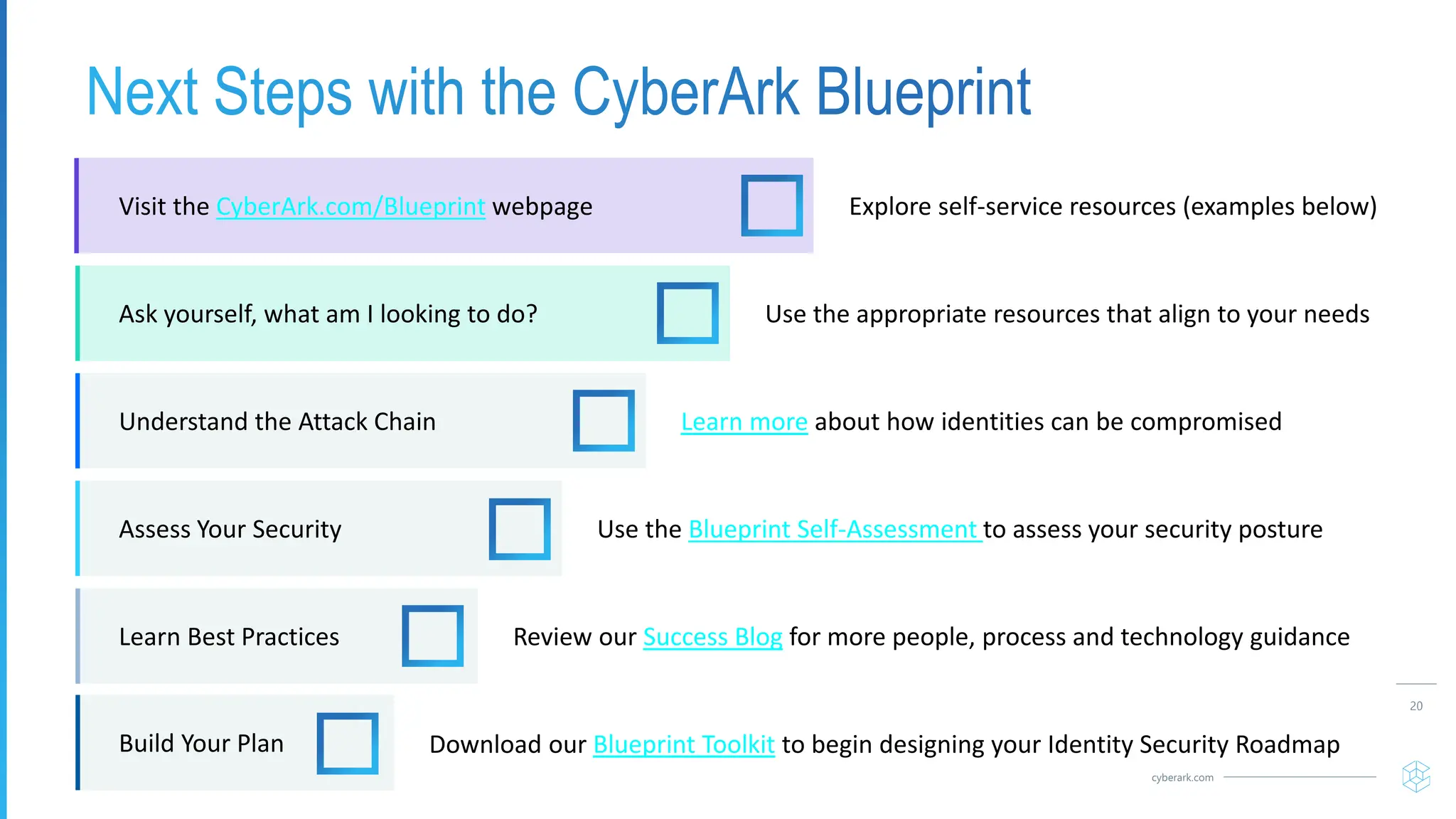
The document provides guidance on using the CyberArk Identity Security Blueprint to map a risk-based approach to identity security. It outlines the stages of the blueprint which include rapid risk mitigation of highest privilege identities, locking down core security platforms, building identity security into enterprise strategy, and maturing existing controls. It also describes understanding the identity attack chain, assessing security posture, identifying gaps, and learning best practices to drive adoption across the workforce. The blueprint toolkit and self-service resources can help design an identity security roadmap.