Diploma Project titles 2013 for CSE,IT,EEE,ECE / B.Sc, BCA Project Titles.pdf
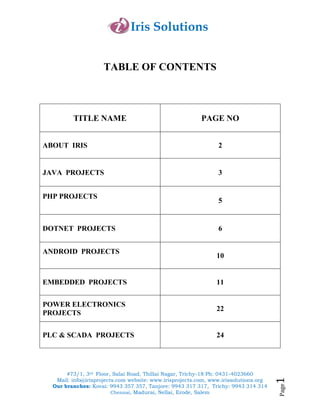
- 1. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page1 TABLE OF CONTENTS TITLE NAME PAGE NO ABOUT IRIS 2 JAVA PROJECTS 3 PHP PROJECTS 5 DOTNET PROJECTS 6 ANDROID PROJECTS 10 EMBEDDED PROJECTS 11 POWER ELECTRONICS PROJECTS 22 PLC & SCADA PROJECTS 24
- 2. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page2 About Iris "Iris Solutions - A Boon for Young Technocrats" Global presence of technocrats is no more a dream in this world. We make it possible by ensuring all the quality standards within an individual which has to be the identity of a successful technocrat. Irrespective of the technologies and the domain in which a particular project gets shaped, we support all kind of student needs in terms of monetary values as well as the time factor. Students apart from doing a particular project should know how the project is getting shaped. We are aware in making this thing to happen. Research and Development plays a vital role in enhancing one’s self development in terms of up gradation and moving forward. When you are searching for a good channel to inhibit yourself with such a platform, IRIS comes handy. Apart from providing simulation based training, we also provide industrial experts in sharing their valuable suggestions and even Industry oriented training at required cases. In short we strive hard to fulfill the student requirements in terms of each and every department of the developing their skills.
- 3. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page3 JJAAVVAATECHNOLOGY : JAVA DOMAIN : IEEE TRANSACTIONS ON NETWORKING TECHNOLOGY : JAVA DOMAIN : IEEE TRANSACTIONS ON NETWORK SECURITY S.NO CODE PROJECT TITLES 10 DJNS 01 Modeling And Detection Of Camouflaging Worm 11 DJNS 02 Internet Information Server 12 DJNS 03 A Puzzle Based Defense Strategy Against Attacks 13 DJNS 04 Image Steganography 14 DJNS 05 Optimized Resource Allocation For Software Release Planning 15 DJNS06 Worm Hole Based Anti Jamming Technique In Sensor Network TECHNOLOGY : JAVA DOMAIN : IEEE TRANSACTIONS ON DATA MINING S.NO CODE PROJECT TITLES 14 DJDM 01 Face Recognition Using Chunk IPCA 15 DJDM 02 Deriving Concept-Based User Profiles From Search Engine Logs S.NO CODE PROJECT TITLES 01 DJNW 01 Fast Recovery In Ip Networks Using Multiple Routing configurations 02 DJNW 02 Authorization Scheme For Distributed Systems 03 DJNW 03 Detecting Malicious Packet Losses 04 DJNW 04 Optimizing The Throughput Of Data-Driven Peer-To-Peer Streaming 05 DJNW 05 Two Techniques For Fast Computation Of Constrained Shortest Paths 06 DJNW 06 Sen Steel Iron Organization 07 DJNW 07 Dynamic Search Algorithm In Unstructured peer-To-peer Networks 08 DJNW 08 Weak State Routing For Large-Scale Dynamic Networks 09 DJNW 09 A Geometric Approach To Improving Active Packet Loss Measurement
- 4. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page4 16 DJDM 03 Welcome To Online E-Learning Combination Of Universities TECHNOLOGY : JAVA DOMAIN : IEEE TRANSACTIONS ON MOBILE COMPUTING S.NO CODE PROJECT TITLES 17 DJMC 01 Optimize Storage Placement In Sensor Networks 18 DJMC 02 Wardrop Routing In Wireless Networks 19 DJMC 03 Message –Efficient Location Prediction For Mobile Objects In Wireless Sensor Networks Using A Maximum Likelihood Technique 20 DJMC 04 Location-Based Spatial Query Processing In Wireless Broadcast Environments JJAAVVAA AAPPPPLLIICCAATTIIOONN PPRROOJJEECCTTSS TECHNOLOGY : JAVA DOMAIN : NON-IEEE BASED PROJECTS S.NO CODE PROJECT TITLES 1 DJNIE 01 Stock in Management System 2 DJNIE 02 Human Resource Management System 3 DJNIE 03 Medicare And Medicate Management System 4 DJNIE 04 Alumini of student Information Database Management System 5 DJNIE 05 Web Based On E-Learning 6 DJNIE 06 Online deliberation Management System 7 DJNIE 07 Text To Speech Converter 8 DJNIE 08 Quiver: Consistent Object Sharing For Edge Services 9 DJNIE 09 Measurement-Based Admission Control At Edge Routers 10 DJNIE 10 Intruder exposure In Wireless Sensor Network 11 DJNIE 12 Network Path Identification Mechanism To Defend Attacks 12 DJNIE 13 Lessening Performance Degradation In Congested Sensor Networks 13 DJNIE 13 A Precise Termination Condition Of The Probabilistic Packet Marking Algorithm
- 5. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page5 14 DJNIE 14 Adaptive Task Check pointing And Replication: Toward Efficient Fault- Tolerant Grids 15 DJNIE 15 Predictable High Performance Computing Using Feedback Control And Admission Control 16 DJNIE 16 On-Line Java Compiler With Security Editor 17 DJNIE 17 Detecting Denial –Of-Service Attacks 18 DJNIE 18 Bi-Criteria Scheduling Of Scientific Grid Workflows 19 DJNIE 19 Eight Times Acceleration Of Geospatial Data 20 DJNIE 20 Self –Reconfigurable Wireless Mesh Networks PPHHPP TECHNOLOGY : PHP DOMAIN : NON-IEEE BASED PROJECTS S.NO CODE PROJECT TITLES 1 DPNIE 01 A Flat file CMS(Content Management System 2 DPNIE 02 Easy News System 3 DPNIE 03 E-mail System 4 DPNIE 04 Online Reservation for Rent-a-Car 5 DPNIE 05 Chat Messenger 6 DPNIE 06 Dynamic Flash Movies 7 DPNIE 07 Investing Stock(Stock Management System) 8 DPNIE 08 E-Classified Search Engine 9 DPNIE 09 WAP Portal 10 DPNIE 10 Free Forum System(Tech Book) 11 DPNIE 11 E Journal System
- 6. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page6 DDOOTT NNEETT TECHNOLOGY : DOTNET DOMAIN : IEEE TRANSACTIONS ON NETWORKING TECHNOLOGY : DOTNET DOMAIN : IEEE TRANSACTIONS ON DATA MINING S.NO CODE PROJECT TITLES 01 DDNW 01 A Survey of Network Virtualization 02 DDNW 02 Security Schemes for Wireless Sensor Networks with Mobile sink 03 DDNW 03 Scalable Coordination techniques for Distributed Network Monitoring 04 DDNW 04 File Transmitting in Distributed Systems 05 DDNW 05 Minimizing File Download in an Intranet 06 DDNW 06 Correlation-based Traffic Analysis Attacks on Anonymity Networks 07 DDNW 07 Sharing Memory between Byzantine Processes using policy-enforced Tuple spaces 08 DDNW 08 Reputation-Based Resource Allocation in p2p Systems of Rational Users 09 DDNW 09 Measuring Capacity Bandwidth of Targeted Path Segments 10 DDNW 10 Multi-user Diversity Gain in Cognitive Networks S.NO CODE PROJECT TITLES 11 DDDM 01 Efficient Peer-to-Peer Keyword Searching 12 DDDM 02 Through Linking for Transfer Learning Using Web 13 DDDM 03 Filtering Data Flow for Continuous Queries 14 DDDM 04 Semantic –Aware Metadata Search File Systems
- 7. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page7 TECHNOLOGY : DOTNET DOMAIN : IEEE TRANSACTIONS ON MOBILE COMPUTING S.NO CODE PROJECT TITLES 15 DDMC 01 The Impact of Data Aggregation in Sensor Networks 16 DDMC 02 Mobiqual: QOS-Aware Load Shedding in Mobile CQ Systems 17 DDMC 03 Secure Distance –Based Localization in the Presence of Cheating Lead Nodes 18 DDMC 04 Offshore Management System TECHNOLOGY : DOTNET DOMAIN : IEEE BASED ON NETWORK SECURITY S.NO CODE PROJECT TITLES 19 DDNS 01 Managing Attack Graph Complexity Through Visual Hierarchical Aggregation 20 DDNS 02 Exploiting Predictability in Click-based Graphical Passwords 21 DDNS 03 Behavioral Characteristics of Spammers and their Network Reachability Properties 22 DDNS 04 Data-Providence Verification for Secure Hosts 23 DDNS 05 Practical Attack Graph Generation for Network Defense TECHNOLOGY : DOTNET DOMAIN : IEEE BASED ON SOFTWARE ENGINEERING S.NO CODE PROJECT TITLES 24 DDSE 01 An Evaluation of Random Testing 25 DDSE 02 Automatic Detection of Unsafe Dynamic Component Loadings TECHNOLOGY : DOTNET DOMAIN : IEEE BASED ON IMAGE PROCESSING S.NO CODE PROJECT TITLES 26 DDIP 01 High Quality Separating Reflections from Images 27 DDIP 02 Content-Based Image Retrieval by Feature Adaptation and Relevance Feedback 28 DDIP 03 De-nosing the Dermatological Image
- 8. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page8 DDOOTTNNEETT AAPPPPLLIICCAATTIIOONN PPRROOJJEECCTTSS TECHNOLOGY : DOTNET DOMAIN : NON-IEEE BASED PROJECTS S.NO CODE PROJECT TITLES 1 DDNIE 01 A Secure Recognition Based Graphical Password by Watermarking 2 DDNIE 02 Three factor Authentication Method for Banking Application 3 DDNIE 03 Personal Computer Access control using voice recognition method 4 DDNIE 04 Refactoring – Aware Software Configuration Management 5 DDNIE 05 E-Banking Management System 6 DDNIE 06 World Wide Net Ranking System 7 DDNIE 07 Online Insurance Management System 8 DDNIE 08 Virtual Knowledge Sharing 9 DDNIE 09 Financial Forecast System 10 DDNIE 10 Multilevel Marketing System 11 DDNIE 11 Grid Services for Distributed System Integration 12 DDNIE 12 Authenticated Multi-step Nearest Neighbor Search 13 DDNIE 13 Predicting Missing Items in Shopping Carts 14 DDNIE 14 Student Database Management System Using Internet and Intranet 15 DDNIE 15 Load Balancing for Parallel Applications on Distributed Systems 16 DDNIE 16 Learning and Matching of Dynamic Shape Manifolds for human action recognition 17 DDNIE 17 Minimizing File Download in an Intranet 18 DDNIE 18 High Resolution Animated Scenes from Stills 19 DDNIE 19 Personalized Retrieval of Sports Video 20 DDNIE 20 In-Image Accessibility Indication 21 DDNIE 21 Customized Online Exam using Cryptography 22 DDNIE 22 Closing the Loop in Web Page Understanding 23 DDNIE 23 Effective Collaboration with Information Sharing in Virtual Universities 24 DDNIE 24 Crack Removal Based on Edge Detection Method 25 DDNIE 25 In-Depth Packet Inspection using a Hierarchical Pattern Matching Algorithm
- 9. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page9 26 DDNIE 26 Characterizing Unstructured Overlay Topologies in Modern P2P File- Sharing Systems 27 DDNIE 27 Semantics-Based Design for Secure Web Services 28 DDNIE 28 Downloading Secured File using Multiple Servers 29 DDNIE 29 Statistical Techniques for Detecting Traffic Anomalies Through Packet Header Data 30 DDNIE 30 Distributing and Monitoring the Process in a Network 31 DDNIE 31 Visualizing Student data in Web-Based Distance Education 32 DDNIE 32 Bridging Domains using World Wide 33 DDNIE 33 Enhancing Downlink Performance in Wireless Networks by Simultaneous Multiple Packet Transmission 34 DDNIE 34 Uncertainty Modeling and Reduction in MANETS (mobile ad hoc N/W) 35 DDNIE 35 Knowledge-Based Interactive Post Mining of Association Rules using Ontologies 36 DDNIE 36 Secure Communication using Network Protocol 37 DDNIE 37 Orthogonal Data Embedding for Binary Images in Morphological Transform Domain-a high-Capacity Approach 38 DDNIE 38 Intelligent Image Enhancement and Removal of Cracks and in Digitized Paintings 39 DDNIE 39 Proactive System Based Data Transfer 40 DDNIE 40 History Based Website Access Control 41 DDNIE 41 Logoot:Undo Distributed Collaborative Editing System on p2p Networks 42 DDNIE 42 Website Ranking System 43 DDNIE 43 A Trace-Driven Approach to Evaluate the Scalability of p2p-Based Video-on-Demand Service 44 DDNIE 44 Sparse Bayesian Learning of Filters for Efficient Image Expansion 45 DDNIE 45 System Observer and Organizer in a connected network 46 DDNIE 46 Water Marking in 2-d Images 47 DDNIE 47 A Self-Repairing Tree Topology Enabling Content-Based Routing in Mobile ad hoc Networks 48 DDNIE 48 The Effect of Pairs in Program Design Tasks 49 DDNIE 49 Defense Mechanism Against DDOS Attacks 50 DDNIE 50 Online Aptitude Test based Pair Programming
- 10. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page10 AANNDDRROOIIDD TECHNOLOGY : ANDROID DOMAIN : NON-IEEE BASED PROJECTS S.NO CODE PROJECT TITLES 1 DANIE 01 Restaurant Menu Ordering System Using Smart Phones 2 DANIE 02 A Framework for Personal Mobile Commerce Pattern Mining and Prediction 3 DANIE 03 Privacy control in smart phones using semantically rich reasoning and context modeling 4 DANIE 04 RITAS: Services For Randomized Intrusion Tolerance 5 DANIE 05 Proteus: Multi-flow Diversity Routing for Wireless Networks with Cooperative Transmissions 6 DANIE 06 Cooperative Clustering Protocol For Energy Saving Of Mobile Devices 7 DANIE 07 Mob minder: Location Based Reminder on Mobiles 8 DANIE 08 Optimal Jamming Attacks and Network Defense Policies in Wireless Sensor Network 9 DANIE 09 On the Use of Mobile Phones and Biometrics for Accessing Restricted Web Services 10 DANIE 10 Implementation of Smart Video Surveillance System and Image Capturing Using Android Smart Phones with SMS Alert
- 11. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page11 EEMMBBEEDDDDEEDD TECHNOLOGY : EMBEDDED DOMAIN : ROBOTICS S.NO CODE PROJECT TITLES 1 PROB 01 Digitally secured Password enabled spray robot for agricultural application 2 PROB 02 A multi-agent MSBRT -sensory control system for intelligent security robot 3 PROB 03 Hand gesture based wheel chair movement control for the physically disabled person 4 PROB 04 Voice operated intelligent fire extinguisher vehicle for rescue operation 5 PROB 05 Highly-Toxic gas leakage detection and intimation robot for chemical industries 6 PROB 06 A novel approach of LDR & IR Based Railway Crack Detection Robot 7 PROB 07 Design and implementation of tele-operated pick and place moving robot for industrial application 8 PROB 08 Smart Tanker Robot for Security Operation In The Protected Area Via IVRS 9 PROB 09 ASK technique based fast acting intelligent surveillance robot 10 PROB 10 Microcontroller Based Wall Painting Robot For Industrial And Commercial Application 11 PROB 11 Design and Development of Human detection robot in war field 12 PROB 12 Bluetooth based robot control for metal detection application 13 PROB 13 Solar Powered Radio-Frequency Operated Robot For Physically Challenged 14 PROB 14 Ultrasonic eye based obstacle detection robot car 15 PROB 15 Development of Sensor based live human detection robot for human tracking application in landslide 16 PROB 16 Design and implementation of Automatic path finding robot using infrared sensor 17 PROB 17 Intelligent solar tracking robot for low cost power production strategies 18 PROB 18 Development Of Intelligent Spy Robot With Wireless Camera For War Field 19 PROB 19 Intelligent Touch Screen Controlled Robot
- 12. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page12 20 PROB 20 Design & development of multiple interface based fire fighting Robot 21 PROB 21 An Approach Of AT89c52 Microcontroller Operated Robotic ARM 22 PROB 22 Experimental Study On Long‐Range Navigation Behavior Of Agricultural Robots 23 PROB 23 Autonomous Robotic Patrol Vehicles 24 PROB 24 Real‐Time Human Tracking Using Fusion Sensor for Home Security Robot 25 PROB 25 Communication Jammer Robot In War Field 26 PROB 26 Autonomous Navigation Robot For Landmine Detection Application 27 PROB 27 Wireless Vision-Based Stabilization Of Indoor Micro-Helicopter 28 PROB 28 Design And Development Of Human Eye Ball Controlled Pick And Place Robot 29 PROB 29 Design And Implementation Of Embedded With Remote Control System In Industrial Robot 30 PROB 30 Low‐Cost, High‐Accuracy,State Estimation For Vehicle Collision Prevention System 31 PROB 31 High Illumination Search and Following Robot 32 PROB 32 Infrared Communication Based Real Time Pre crash Avoider For Moving Robot Car 33 PROB 33 Ultrasonic Based High Sensitive Obstacle Detection Robot 34 PROB 34 Autonomous Gas Sensitive Micro Drone 35 PROB 35 ZIGBEE Based Wireless Sensor Networks For Service Robot TECHNOLOGY : EMBEDDED DOMAIN : CONSUMER ELECTRONICS S.NO CODE PROJECT TITLES 1 PCE 01 Green House Monitoring And Control Using AT89S52 microcontroller 2 PCE 02 Programmed Bidirectional Visitor Counter For Energy Saver In Auditorium 3 PCE 03 Automatic Temperature Monitoring & Control For Cement Industries 4 PCE 04 A novel approach of Electronic Code-Lock System For Bank Security 5 PCE 05 Microcontroller operated highly sensitivity based No Doze & Drowsiness Detection System 6 PCE 06 Non-Contact RFID Reader Based Vehicle Accessing System
- 13. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page13 7 PCE 07 Multi-Home Appliance Control System Using Telephony Signal 8 PCE 08 Automatic Three Channel Industrial Fire Monitoring & Control Station 9 PCE 09 Design and Development of Life Cycle Tester For Multi-Electronic Components 10 PCE 10 Automatic Active Phase Selector For Single Phase Load From Three Phase supply 11 PCE 11 Design and Implementation of Digital Fuel Level Indicator For Vehicles 12 PCE 12 Industrial Supervisory Sensor Based Monitoring & Control System 13 PCE 13 Coin sensor Based Internet Access Control System using Microcontroller 14 PCE 14 Fabrication of Automatic oil Filling System in forging industries 15 PCE 15 Loco-Pilot Operated Voice Based Station Alerting System 16 PCE 16 Implementation of light Intensity Based head Light Brightness Control System for automotives 17 PCE 17 Microcontroller based Vehicle Cabin Safety and security System 18 PCE 18 Home security oriented Liquefied petroleum gas Leakage Detector And Alarm Indicator 19 PCE 19 Humidity Based Automatic Irrigation System for agricultural purpose 20 PCE 20 Implementation of Live Human movement Detector With Energy Saver Technique 21 PCE 21 Home Automation For Physically Challenged People Using Voice Tag 22 PCE 22 Automatic College Bell With voice control 23 PCE 23 Design and Development of Sixth Sense Based thermal power plant Security System 24 PCE 24 Illumination Based Sun-Ray Tracker for energy harvesting 25 PCE 25 A Novel approach of Automatic Elevator Control System for energy saving application in shopping mall 26 PCE 26 Wireless approach to prevent Vehicle Accident Using Eye Blink Sensor 27 PCE 27 High Sensitive LDR Based Power Saver For Street Light Control System Distance Measurement With Passive Method 28 PCE 28 Hazardous Gas And Fire Detecting Method Applied In Coal Mine 29 PCE 29 Intelligent Floor Type Car Parking System for shopping mall 30 PCE 30 Money Saver strategy based on the concept of Prepaid Energy Meter
- 14. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page14 31 PCE 31 Design of Intelligent Automatic Podium Light Control System 32 PCE 32 Mobile Phone Signal Transmission Detection and intimation system for conference hall. 33 PCE 33 Design and Development of Intelligent Car Parking System with LED Indication 34 PCE 34 Implementation of Alcohol Sensed Automatic Ignition Control for automobiles 35 PCE 35 Pre-Programmed Portable Navigation Aid For Fisherman With Weather Updates And Distress Alerting System. 36 PCE 36 Digital Wireless Intercom Facility For Colleges or industries 37 PCE 37 Digital Heart Beat Rate Monitoring System Using AT89C51 Microcontroller 38 PCE 38 Smart Digital Door Lock For The Home Automation 39 PCE 39 Radio Frequency Based Remote Industrial Appliances Control System 40 PCE 40 Timer Based Industrial Liquid Pump Controller With User-Defined Time Slots 41 PCE 41 Research and implementation on the mobile intelligent controller for consumer electronics 42 PCE 42 Enhancement Of The Complement Of An Embedded Surveillance System 43 PCE 43 Opportunities and recommendations for reducing the energy consumption for home application TECHNOLOGY : EMBEDDED DOMAIN : RFID BASED EMBEDDED S.NO CODE PROJECT TITLES 1 PRF 01 An efficient and secured authentication protocol for RFID based bank security systems 2 PRF 02 Realization of RFID module Based EB Line Change over 3 PRF 03 Design an Intelligent Unmanned Toll Collection System Using RFID Technology 4 PRF 04 Tele-Medicine Information System based on RFID technology 5 PRF 05 RFID Based Industrial Load ON/OFF Control System With Voice Announcement 6 PRF 06 Development of RFID oriented automatic password enabled Vehicle Guard security system
- 15. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page15 7 PRF 07 Non-Contact RFID Reader Based Energy Meter 8 PRF 08 RFID Based Industrial Parameters Monitoring System 9 PRF 09 The Electronic Passport And Features Of Government Issued RFID Based Identification 10 PRF 10 Implementation of Bus Identification System For Visually Impaired People 11 PRF 11 Trust Bank Locker Security And Alerting System using microcontroller with RFID technique 12 PRF 12 Microcontroller based Laptop Stolen Detection System using RFID guard 13 PRF 13 AT89C52 microcontroller based Blind Man Stick Using RFID Application 14 PRF 14 An Enhancing Campus Access Control System Based On RFID module 15 PRF 15 High Speed enabled smart card based Mobile Phone Charger for public support 16 PRF 16 Design And Implementation Of Unique National Identity Card Using RFID Technology 17 PRF 17 Electronic Card Based Electrical Energy Utilization & Money Saver 19 PRF 18 RFID Applications Strategy and Deployment in Bike Renting System TECHNOLOGY : EMBEDDED DOMAIN : BIO METRICS S.NO CODE PROJECT TITLES 1 PBMT 01 Bio-Pad Finger Print Recognition Based Human Background Checker 2 PBMT 02 Finger Print Based Automobile Security System 3 PBMT 03 Finger Print Based Medical Information System 4 PBMT 04 Industrial Automation oriented Finger Print identifier 5 PBMT 05 Development of ATM Authentication System Using Thumb Impression 6 PBMT 06 Bio-Pad oriented secured Airport Security System 7 PBMT 07 Finger Print Based DC /AC Motor speed Control System 8 PBMT 08 Voting System Using Finger Print Application 9 PBMT 09 Secured user identification for Bank Locker Security System 10 PBMT 10 Finger print based code enabled Library book tracking system
- 16. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page16 TECHNOLOGY : EMBEDDED DOMAIN : BIO MEDICAL S.NO CODE PROJECT TITLES 1 PBMD 01 Research and Implementation of remote heart rate monitoring system based on MCU 2 PBMD 02 Super-Resolution in Respiratory Synchronized Positron Emission Tomography 3 PBMD 03 Wireless Medical Interface Via Bluetooth Technology 4 PBMD 04 Atmel Based Injection Molding Machine Controller 5 PBMD 05 Effects of process and product parameters on the shape of nanosecond pulses used in high-field liquid food treatment 6 PBMD 06 Biomedical strategies: Respiratory Based Automatic Defibrillator 7 PBMD 07 Study of Body Pressure Monitoring System Using PIC16F877A For Athletes 8 PBMD 08 Design and monitoring of Coma-patient Status in hospital 9 PBMD 09 An Implementation of ECG& Body Pressure Monitoring System 10 PBMD 10 Advance Diagnostic Tool For Respiration Rate And Cough Indication Through Alarm 11 PBMD 11 Glucose Flow Level Monitoring And Alerting System 12 PBMD 12 Microcontroller oriented Bio-Muscular Stimulator TECHNOLOGY : EMBEDDED DOMAIN : GSM/GPS S.NO CODE PROJECT TITLES 1 PGP 01 Intelligent Fleet Management System With Concurrent GPS & GSM Real Time Positioning Technology 2 PGP 02 Design and Deployment of Bridge Structural Health Monitoring System Based on Wireless Sensor Network 3 PGP 03 A design of boiler temperature monitoring system based on MCU with Auto-Cooling System 4 PGP 04 Wireless Black Box Using MEMS Accelerometer And GPS Tracking For Accident Monitoring Of Vehicles 5 PGP 05 GSM Based Drowsiness & Drunken Drive Detection System Using Microcontroller 6 PGP 06 Design And Implementation Of Postpaid Electricity Bill Automation 7 PGP 07 Password Enabled Bank Locker Protection System 8 PGP 08 Train Accident Detection System Using GPS & GSM Technology
- 17. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page17 9 PGP 09 Vehicle Cabin Safety With Alcohol Detection & Ignition Control 10 PGP 10 UPS Battery Monitoring System Over GSM For High Availability Systems 11 PGP 11 A Wireless Access Multi-Motor Speed Control System Based DTMF Technology 12 PGP 12 Design of Household Appliance Control System Based on GSM 13 PGP 13 GSM Based ATM Fraud Detection system using RFID module 14 PGP 14 Micro controller Based Speed Control Of DC Motor using GSM communication 15 PGP 15 Plane Hijack Detection With Intimation Through GSM 16 PGP 16 A concept of PIR Based Live Human Detection System In Unmanned Home 17 PGP 17 GSM Technology Based Weather Monitoring System 18 PGP 18 Gas Leakage & Fire Detection Monitor. & Ctrl In Commercial Areas 19 PGP 19 A novel approach for Flood Detection And Intimation Via GSM Modem 20 PGP 20 GPS Based Automatic Root Announcement System For Visually impaired People 21 PGP 21 Single Phase Preventer Identification Through GSM Technique 22 PGP 22 Soldier Tracking System In War Field Using GSM And GPS 23 PGP 23 Border Alerting System And Intimation To Coast Guard 24 PGP 24 Human Root Tracking System By Using GPS & GSM Technology 25 PGP 25 Designing an approach for Landslide Warning System 26 PGP 26 Tracking Police Man Using RF Proximity Card and Send SMS To Control Room 27 PGP 27 Automatic Water Supply For Ship In Harbor Using Embedded System 28 PGP 28 Research of Transmission Line Tower Anti-Theft Monitoring Technique Using GSM 29 PGP 29 Electromagnetic Door Status Scrutinizing And Control 30 PGP 30 Industrial Parameter Abnormality Detection System 31 PGP 31 Study and Implementation of War Field Support And Helper Kit 32 PGP 32 GSM Based Condition Reporting System For Power Station Equipments 33 PGP 33 MEMS Based Intelligent ATM Security System 34 PGP 34 Design Of Integrated Mine Safety Monitor System Based On GSM 35 PGP 35 Hardware design of the wireless automatic meter reading system based on GPRS 36 PGP 36 GPS-GSM Integration For Enhancing Public Transportation Management Services
- 18. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page18 37 PGP 37 Unmanned Monitoring System Of Rivers And Lakes Based On WSN 38 PGP 38 SMS Based PWM Speed And Direction Control Of DC Motor 39 PGP 39 Industrial Fault Diagnose With Embedded And GSM Technology 40 PGP 40 Remote BTS multi-parameters Monitoring and Auto control system 41 PGP 41 An adaptive method developed for use in multi-sensor surveillance system TECHNOLOGY : EMBEDDED DOMAIN : ULTRASONIC S.NO CODE PROJECT TITLES 1 PUS 01 Ultrasonic Sensor Based Obstacle Detection & Accident Avoidance System 2 PUS 02 Ultrasonic Sensor With Voice Based Walking Stick 3 PUS 03 Ultrasonic Car Parking System 4 PUS 04 Ultrasonic Based Liquid Level Measurement in ONGC 5 PUS 05 Design And Implementation Of An Embedded Home Surveillance System By Use Of Ultrasonic Sensors TECHNOLOGY : EMBEDDED DOMAIN : WIRELESS S.NO CODE PROJECT TITLES 1 PWL 01 Submarine Navigation Of Catamaran In The Brim Using Wireless Technology 2 PWL 02 Multi-Sensor Array Based Industrial Security 3 PWL 03 Design and implementation of Bank Security Alerting System 4 PWL 04 Gaseous Fuel Leakage Detection in Vehicle With Automatic Safety Warning And Alerting System With VOP Using RF Technology 5 PWL 05 Wireless Oil Well Level Monitoring System in automobile industry 6 PWL 06 The research on optimal Wireless Parking Lot Status Indicator 7 PWL 07 Research on Wireless Process Data Acquisition Technology Based on Agent in Manufacturing industries 8 PWL 08 Feasibility and study of Mine Workers Safety System Using ASK Technology 9 PWL 09 Design and implementation of Bluetooth Based Voice Control Robot 10 PWL 10 An Implementation of RF & GSM Based Life Rescue System
- 19. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page19 11 PWL 11 Dc Motor Speed And Direction Control Using ASK Technology 12 PWL 12 Study of Wireless AC Motor Speed Control System 13 PWL 13 A Rail detection in unmanned Level Crossing Scrutinize And Control 14 PWL 14 Bus Arrival Detection And Automatic Announcement System For Visually impaired & Illiterate Peoples. 15 PWL 15 Wireless Communication Based Vehicle Speed Control System For student /public protection in School/College Zone 16 PWL 16 RF Based Wireless Encryption And Decryption Message Transfer System For Military Applications 17 PWL 17 Wireless Oriented Handheld Multi parameter Monitoring System 18 PWL 18 Radio-frequency based Industrial Automation System 19 PWL 19 Wireless Smart Sensor For Highway Traffic Control System With LCD Display Using RF Technology. 20 PWL 20 Reducing Risk at Automatically- Operated Level Crossings on Public Roads TECHNOLOGY : EMBEDDED DOMAIN : ZIGBEE S.NO CODE PROJECT TITLES 1 PZB 01 ZIGBEE Device Access Control And Reliable Data Transmission System 2 PZB 02 An Energy Saving Solution With Auto-Fault Control/protection System For Street Light 3 PZB 03 A ZIGBEE Based Industrial Monitoring System With Automatic Load Control Capabilities. 4 PZB 04 Pervasive Healthcare In Rural Areas 5 PZB 05 Design of Interference aware ZIGBEE building monitoring network 6 PZB 06 Highly secured Earth Quake And Landslide Warning System Using ZIGBEE Protocol 7 PZB 07 Wireless Traffic Control System For Ambulance/VIP Vehicles Based On ZIGBEE 8 PZB 08 Strategies of ZIGBEE Based Locker Security System In Bank/Industry 9 PZB 09 ZIGBEE - Research into Integrated Real-Time Located Systems for vehicle support 10 PZB 10 Study of Wireless ZIGBEE Based Soldier Tracking System 11 PZB 11 ZIGBEE Based Secured Data Transmission For Military Application
- 20. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page20 12 PZB 12 Study on electrical switching device junction parameters monitoring system based on ZIGBEE technology 13 PZB 13 ZIGBEE Source Route Technology In Home Application TECHNOLOGY : EMBEDDED DOMAIN : POWER GENERATION AND REDUCTION S.NO CODE PROJECT TITLES 1 PPG 01 Foot Step Power Generation System For Rural Energy Application To Run AC And DC Loads 2 PPG 02 Small-Scale Hydro Power Generation 3 PPG 03 Research and Development of Power Production From Waste Water 4 PPG 04 Renewable Energy Resources For Residential Applications In Coastal areas: A Modular Approach 5 PPG 05 Implementation Of Solar Inverter For Home / Garden / Street Light Applications 6 PPG 06 Power and energy production of HOME based PV modules 7 PPG 07 Hybrid Power Generation System For Non Conventional Energy Sources 8 PPG 08 Large scale integration of small wind power plant for island utility TECHNOLOGY : EMBEDDED DOMAIN : AUTOMATION S.NO CODE PROJECT TITLES 1 PAT 01 Fuel Control In Vehicles To Prevent Fuel Theft With Wireless Alerting System 2 PAT 02 ASK Based Automated Wireless Gate Control System 3 PAT 03 Supervisory Password Based Two/Four Wheelers Security System 4 PAT 04 Auto Turn OFF for Water Pump With Six Different Time Slots For Power Saving Applications 5 PAT 05 Automatic Active Phase Selector For Single Phase Load From Three Phase Supply 6 PAT 06 Sensor Based Drunken Drive Avoiding System For Automobile 7 PAT 07 Automatic Car Parking System For Apartment Building With LED Indication 8 PAT 08 Pneumatic Drill and Jig 9 PAT 09 Wireless Based Car Paint Spraying Robot 10 PAT 10 Accident Avoiding System Using Dim And Bright Of Head Light 11 PAT 11 Automated Traffic Light Control System For Air Pollution Detection In Vehicles
- 21. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page21 12 PAT 12 Application Of Modern Automation System For Protection And Optimum Use Of High Voltage System. 13 PAT 13 Automatic Metal Remover System In Industrial Conveyor 14 PAT 14 Energy Saver Strategies For Elevator in shopping mall 15 PAT 15 Moisture Based Automatic Irrigation System 16 PAT 16 Oil/ Liquid Level Alarm And Automatic Tank Filling System 17 PAT 17 Pneumatic Clutch Control System 18 PAT 18 Automatic Temperature Monitoring And A/C control System TECHNOLOGY : EMBEDDED DOMAIN : ELECTRICAL S.NO CODE PROJECT TITLES 1 PEE 01 AC Motor Speed Control Using Mini Variac With Display Unit 2 PEE 02 Fast acting Wireless DC Gear Motor Direction And Speed Control System for spinning industries 3 PEE 03 Security Integrated System Based On Wireless Access Protocol For Industrial Application 4 PEE 04 Solar Based Power Production System For Rural Energy Application To Run AC And DC Loads 5 PEE 05 A Novel Approach for Energy Utilization Based Load Sharing System 6 PEE 06 An Integrated Industrial Power Quality Management System 7 PEE 07 Design of Wireless Speed Control Of AC Motor for room 8 PEE 08 Design and implementation of low cost Power Failure Detector And Automatic Change over 9 PEE 09 An adaptive technique to improve wireless power transfer To Charge A Mobile Phone 10 PEE 10 Study of GSM Based Power Stealing Detection And Intimation System 11 PEE 11 Sub Station: Transformer Fault Detection And Wireless Announcement system 12 PEE 12 Implementation of Wireless Single Phase/Three Phase Motor Control System 13 PEE 13 Performance and analysis of substation parameters monitoring system 14 PEE 14 Dual Wireless Communication Oriented Electricity Billing Automation System
- 22. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page22 TECHNOLOGY : EMBEDDED DOMAIN : PC BASED EMBEDDED S.NO CODE PROJECT TITLES 1 PPC 01 A voice-activated dc motor control system with artificial intelligence 2 PPC 02 Supervisory Sensor Based Industrial Security System 3 PPC 03 PC Based Hi-Tech Industrial Automation With Auto / Manual Modes Of Operation 4 PPC 04 Development of PC Based Library Book Tracking System 5 PPC 05 Biometric Based Online Examination malfunction detection and alerting system to squad. 6 PPC 06 Study of Pipeline Damage Detector using microcontroller 7 PPC 07 Design an Integration of Wireless Peer to Peer Communication 9 PPC 09 Development Of Gas Leak Detection And Location System Based On Wireless Technology 10 PPC 10 PC Based Industrial Appliance Control System 11 PPC 11 Wireless Code Locking System For Machines with PC control 12 PPC 12 Patient Heart Beat/Pulse Monitoring system using microcontroller based PC control 13 PPC 13 PC Based Human Health Care Monitoring System TECHNOLOGY : EMBEDDED DOMAIN : POWER ELECTRONICS S.NO CODE PROJECT TITLES 1 PPE 01 Single-Switch High Step-Up Converters With Built-In Transformer Voltage Multiplier Cell 2 PPE 02 Soft-Switching Boost Converter With a Flyback Snubber for High Power Applications 15 PEE 15 Automatic Street Light Control With Energy Saver Technique And Fault Detection System 16 PEE 16 An approach of Industrial Data Acquisition System 17 PEE 17 Automatic Power Factor Controller Using Phase Control Method With THYRISTOR 18 PEE 18 Design of Transformer Oil Level And Temperature Monitoring System 19 PEE 19 Design and development of Speed Control of BLDC Motor 20 PEE 20 Impact of wireless communication delay on load sharing among distributed generation system
- 23. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page23 3 PPE 03 Analysis and Design of a Zero-Voltage-Switching and Zero- Current-Switching Interleaved Boost converter 4 PPE 04 Multilevel Current Waveform Generation Using Inductor Cells and H- Bridge Current-Source Inverter 5 PPE 05 High Step-Up DC-DC Converters Using Zero-Voltage Switching Boost Integration Technique and Light-Load Frequency Modulation Control 6 PPE 06 Modeling and Control of a New Three-Input DC–DC Boost Converter for Hybrid PV/FC/Battery power system 7 PPE 07 High-Efficiency MOSFET Inverter with H6-Type Configuration for Photovoltaic Non isolated AC-Module Applications 8 PPE 08 Towards a 99% Efficient Three-Phase Buck-Type PFC Rectifier for 400-V DC Distribution Systems 9 PPE 09 Improved Transformer less Inverter With Common-Mode Leakage Current Elimination for a Photovoltaic Grid-Connected Power System 10 PPE 10 Soft-Switching SEPIC Converter With Ripple-Free Input Current 11 PPE 11 Analysis of EMI Terminal Modeling of Switched Power Converters 12 PPE12 Fully Digitalized Implementation of PFC Rectifier in CCM Without ADC 13 PPE 13 A Comparative Study of a New ZCS DC–DC Full-Bridge Boost Converter With a ZVS Active - Clamp Converter 14 PPE 14 New Efficient Bridgeless Cuk Rectifiers for PFC Applications 15 PPE 15 Torque Ripple Reduction in BLDC Torque Motor With Non-ideal Back EMF 16 PPE 16 A ZVS Grid-Connected Three-Phase Inverter 17 PPE 17 High-Efficiency DC–DC Converter With Two Input Power Sources 18 PPE 18 A Safety Enhanced, High Step-Up DC–DC Converter for AC Photovoltaic Module Application 19 PPE 19 Derivation, Analysis, and Implementation of a Boost–Buck Converter- Based High-Efficiency PV Inverter 20 PPE 20 Grid-Connected Boost-Half-Bridge Photovoltaic Micro inverter System Using Repetitive Current Control and Maximum Power Point Tracking 21 PPE 21 Interleaved High Step-Up Converter With Winding-Cross-Coupled Inductors and Voltage Multiplier Cells A New Single-Phase Single-Stage Three-Level Power Factor Correction AC–DC Converter 22 PPE 22 A Three-port Flyback for PV Micro inverter Applications With Power Pulsation Decoupling Capability 23 PPE 23 Hybrid: wind-solar power generation strategies
- 24. Iris Solutions #73/1, 3rd Floor, Salai Road, Thillai Nagar, Trichy-18 Ph: 0431-4023660 Mail: info@irisprojects.com website: www.irisprojects.com, www.irissolutions.org Our branches: Kovai: 9943 357 357, Tanjore: 9943 317 317, Trichy: 9943 314 314 Chennai, Madurai, Nellai, Erode, Salem Page24 PPLLCC && SSCCAADDAA BBAASSEEDD PPRROOJJEECCTTSS For More Titles Please Visit www.irisprojects.com (Or) Feel Free To Step in Our Nearest Branch S.NO CODE PROJECT TITLES 1 DPL 01 PLC based Tank level and temperature control Automation for house 2 DPL 02 Energy monitoring system Using SCADA 3 DPL 03 PLC based Bottle filling system on conveyor 4 DPL 04 PLC based temperature control system using PID 5 DPL 05 PLC based Traffic control system 6 DPL 06 PLC based AHU controlling system in Hotels 7 DPL 07 PLC based DOL and Star & Delta control system for induction motor 8 DPL 08 PLC & VFD based speed control system for induction motor 9 DPL 09 PLC based fault rejection system on conveyor 10 DPL 10 PLC based temperature control system through MODBUS 11 DPL 11 Simulation of Power generation using PLC & SCADA 12 DPL 12 SCADA based substation monitoring system 13 DPL 13 GSM based machine monitoring system from remote 14 DPL 14 Automatic tank level controller using PLC 15 DPL 15 Home security using PLC 16 DPL16 Implementation and results of a MIMO PLC feasibility study 17 DPL 17 Miniature Vending Machine With Support Of PLC 18 DPL 18 Implementation of Dc Motor Speed Control System Using PLC 19 DPL 19 DTMF Based Agricultural Water Pump Operating System 20 DPL 20 Optimization of Dam Shutter Control Using PLC Technique