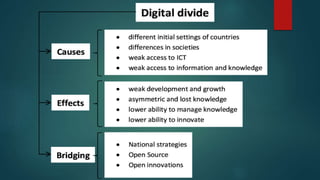
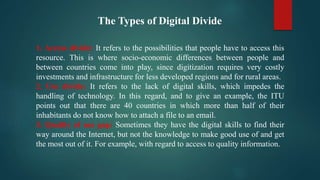
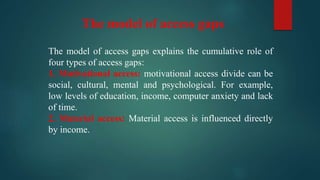
The document discusses the digital divide, which refers to unequal access to and knowledge of new technologies based on factors like income, geography, age, and social group. It notes that the divide impacts economies and increases inequality. The digital divide can be understood through factors like infrastructure access, device availability, training, user skills and content availability. Causes include low literacy, income, geographical barriers, and lack of motivation or access to technology. Ways to reduce the divide discussed include improving access through affordable internet and devices, education on technology use, and technical support. The divide is analyzed through frameworks of access gaps and types of divides.