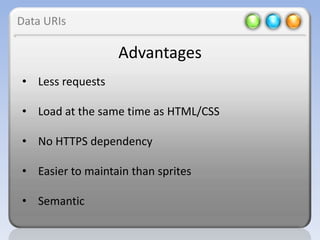
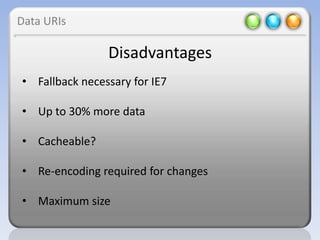
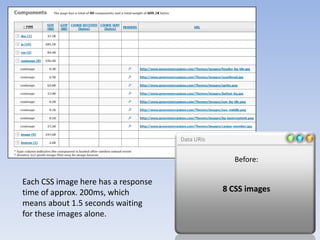
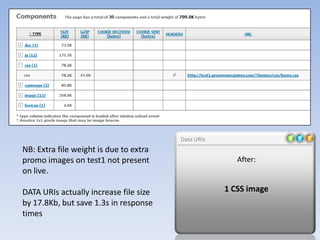
Data URIs allow embedding of resources like images, JavaScript, HTML, and CSV directly into other files and documents. They use a uniform resource identifier scheme with a base64 encoded interpretation of the resource. Most modern browsers understand data URIs so they provide a way to include resources without an additional network request.