Cyber Brochure
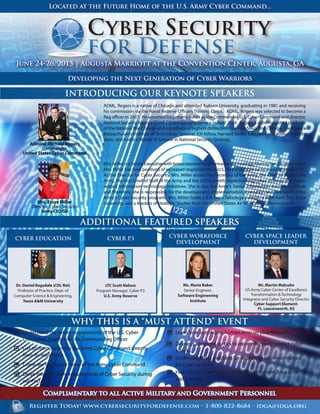
- 1. Register Today! www.cybersecurityfordefense.com • 1-800-822-8684 • idga@idga.org Admiral Michael Rogers Commander, United States Cyber Command Mrs. Essye Miller Director, Cyber Security Army CIO/G6 ADDITIONAL FEATURED SPEAKERS INTRODUCING OUR KEYNOTE SPEAKERS WHY THIS IS A “MUST ATTEND” EVENT June 24-26, 2015 | Augusta Marriott at the Convention Center, Augusta, GA Developing the Next Generation of Cyber Warriors Located at the Future Home of the U.S. Army Cyber Command... Ms. Marie Baker Senior Engineer, Software Engineering Institute CYBER WORKFORCE DEVELOPMENT Mr. Martin Malcolm US Army Cyber Center of Excellence Transformation & Technology Integrator and Cyber Security Director Cyber Support Element- Ft. Leavenworth, KS CYBER SPACE LEADER DEVELOPMENT Complimentary to all Active Military and Government Personnel LTC Scott Nelson Program Manager, Cyber P3 U.S. Army Reserve CYBER P3 ADML. Rogers is a native of Chicago and attended Auburn University, graduating in 1981 and receiving his commission via the Naval Reserve Officers Training Corps. ADML. Rogers was selected to become a flag officer in 2007. He assumed his present duties as the Commander, U.S. Cyber Command and director, National Security Agency/Chief, Central Security Service in April 2014. Rogers is a distinguished graduate of the NationalWar College and a graduate of highest distinction from the NavalWar College. He is also a Massachusetts Institute of Technology Seminar XXI fellow, Harvard Senior Executive in National Security alum, and holds a Master of Science in National Security Strategy. Mrs.MillerisaSeniorExecutivewithbroadexperienceinformationtechnology.Duringher29-yearcareer, Mrs. Miller has held positions of increased responsibility in U.S. Air Force, both tactical and strategic C4IT. As the Director for Cyber Security, Mrs. Miller assists the Secretary of the Army, the Chief of Staff of the Army, the Vice Chief of Staff of the Army and the CIO/G-6 with implementing cyber strategy and cyber- related information technology initiatives. She is also the Army's Senior Information Assurance Officer and therefore, she is responsible for the development, implementation, execution and oversight of the Army's Cyber Security program. Mrs. Miller holds a B.A. from Talladega College, a MBA from Troy State University, and a Masters of Strategic Studies from the United States Air War College, Pennsylvania. Understand the future requirements of the U.S. Cyber Command directly from its Commanding Officer Get an Introduction to the Army Cyber Command directly from its leadership Come see the future home of the Army Cyber Command Delve into the future requirements of Cyber Security during our Focus Day Learn how to mitigate human error on your Network Develop advanced tactics to more effectively predict cyber attacks Understand best practices for deploying resilience metrics for cyber systems Hear about Cyber Space Leader Development, Education, and Training Dr. Daniel Ragsdale (COL Ret) Professor of Practice, Dept. of Computer Science & Engineering, Texas A&M University CYBER EDUCATION
- 2. Register Today! www.cybersecurityfordefense.com • 1-800-822-8684 • idga@idga.org Dear Colleague, Defending Cyber Space is never an easy task. In fact, it is one of the most difficult tasks that the United States Military now faces. How do you defend against an enemy that can attack from any direction, anonymously, and can potentially cripple entire units without firing a single shot? This is the task given to the Military Cyber Commands. What's the first step? To identify training gaps and educational requirements to ensure Warfighters engaged in this fight have the knowledge to win. To simultaneously identify next generation technologies that can be successfully partnered with these Warfighters, leading to the complete domination of the battlefield. How do we accomplish this first step? By successfully communicating to both academia and industry what these requirements are so that they in turn can provide the training, education, and technology to make the Military successful. Without successfully interfacing with industry and setting a direction for the future, the Military understands that it will be forced to also be in a reactive planning state, which runs contrary to the core ideals of the Military. This event serves as an opportunity for solution providers to break through the background noise and present their unique ideas and products in an environment specifically tailored to highlighting them, while simultaneously learning about the future requirements of the Military and a variety of other topics. Meanwhile the Department of Defense gets a first hand look at some of the solutions they may have not originally considered, all in pursuit of that best value solution. Come and be apart of the future of Cyber Security. It starts now! Respectfully, Brian Wharton Conference Director Institute for Defense and Government Advancement USCYBERCOM plans, coordinates, integrates, synchronizes and conducts activities to: direct the operations and defense of specified Department of Defense information networks and; prepare to, and when directed, conduct full spectrum militarycyberspaceoperationsinordertoenableactions in all domains, ensure US/Allied freedom of action in cyberspace and deny the same to our adversaries Army Cyber Command's mission is to plan, coordinate, integrate, synchronize, direct, and conduct network operations and defense of all Army networks. When directed, Second Army will conduct cyberspace operations in support of full spectrum operations to ensure U.S. and allied freedom of action in cyberspace, and to deny the same to adversaries The mission of Fleet Cyber Command is to serve as central operational authority for networks, cryptologic/signals intelligence, information operations, cyber, electronic warfare, and space capabilities in support of forces afloat and ashore; to direct Navy cyberspace operations globally to deter and defeat aggression and to ensure freedom of action to achieve military objectives in and through cyberspace; to organize and direct Navy cryptologic operations worldwide and support information operations and space planning and operations, as directed; to execute cyber missions as directed; to direct, operate, maintain, secure, and defend the Navy's portion of the Global Information Grid. The 24th Air Force's mission is to operate, extend, and defend the Air Force Information Network, defend key mission systems, and provide full spectrum cyberspace capabilities for the joint warfighter in, through, and from cyberspace. JUNE 24-26, 2015 AUGUSTA MARRIOTT AT THE CONVENTION CENTER AUGUSTA, GA US CYBER COMMAND Register for the all access pass and hear future requirements first hand.
- 3. JUNE 24-26, 2015 AUGUSTA MARRIOTT AT THE CONVENTION CENTER AUGUSTA, GA Register Today! www.cybersecurityfordefense.com • 1-800-822-8684 • idga@idga.org Admiral Michael Rogers Commander, U.S. Cyber Command Mr. Martin Malcolm USArmyCyberCenterofExcellence Transformation&Technology IntegratorandCyberSecurityDirector Cyber Support Element- Ft. Leavenworth, KS Dr. Daniel Ragsdale (COL Ret) Professor of Practice, Dept of Computer Science & Engineering, Texas A&M University Keynote: Overview of the U.S. Cyber Command Adm. Rogers is a native of Chicago and attended Auburn University, graduating in 1981 and receiving his commission via the Naval Reserve Officers Training Corps. After serving in a variety of leadership positions, Adm. Rogers was selected to become a flag officer in 2007. Rogers' joint service both afloat and ashore has been extensive, culminating in his service as director of the Chairman's Action Group, and a leader of the JCS Joint Strategic Working Group. He assumed his present duties as Commander, U.S. Cyber Command and Director, National Security Agency/Chief, Central Security Service in April 2014. Rogers is a distinguished graduate of the National War College and a graduate of highest distinction from the Naval War College. He is also a Massachusetts Institute of Technology Seminar XXI fellow, Harvard Senior Executive in National Security alum, and holds a Master of Science in National Security Strategy. Session: Quality Cyber Education Dr. Daniel "Rags" Ragsdale was DARPA as a Program Manager from June 2011 to February 2015. His research interests include computer network operations, cyber deception, cyber security education and training, computer ethics and privacy, and network sciences. Before joining DARPA, Dr. Ragsdale served for more than a decade at the United States Military Academy at West Point where he held a variety of supervisory roles, culminating with his service as Vice Dean for Education. In this capacity, Dr. Ragsdale was the Strategic Planner and Principal Deputy toWest Point's Chief Academic Officer. A recently retired U.S. Army colonel, Dr. Ragsdale's operational assignments included combat deployments in support of Operations Urgent Fury (Grenada), Enduring Freedom (Afghanistan), and Iraqi Freedom (Iraq). In his most recent deployment, Dr. Ragsdale served as the Deputy Commander of a 2000-personTask Force responsible for the security and defense of the largest coalition based in Iraq. Session: Cyber Space Leader Development, Education, and Training Mr. Malcolm W. “Mack” Martin is the US Army Cyber Center of Excellence Transformation & Technology Integrator and the Cyber Support Element- Ft. Leavenworth, KS Director. A proven and highly accomplished Army executive leader with strategic, operational and tactical expertise in the rapidly advancing, highly dynamic cyber domain and electromagnetic spectrum (EMS). Mr. Martin is a recognized visionary and expert on the cyber domain, electronic warfare and EMS and has directed the in depth and detailed analysis to develop long term Army cyberspace and EW capabilities. Mr. Martin is a retired US Naval Flight Officer and Electronic WarfareOfficerwithoperationaldeploymentsonnuclearsubmarines,carriers and expeditionary aviation squadrons supporting coalition ground forces. CONFIRMED SPEAKERS AT A GLANCE SOME MILITARY AND ORGANIZATIONS EXPECTED TO ATTEND • U.S. Cyber Command • U.S. Army Cyber Command • U.S. Navy Cyber Command • U.S. Air Force Cyber Command • U.S. Coast Guard Cyber Command • MARFORCYBER • Fort Gordon Cyber Center of Excellence • Cyber Capabilities and Integration Directorate • TRADOC • DAPRA • CAC Support Element • 35th Signal Brigade • 7th Signal Command • Service Academy Cyber Departments • Army Research Lab • Software Engineering Institute • ESRI • Department of Homeland Security Ms.MarieBaker Senior Engineer, SoftwareEngineeringInstitute Session: State of Cyber Workforce Development Marie Baker is a Senior Engineer in the CERT Program at the Software EngineeringInstitutewheresheisamemberoftheCyberSecuritySolutions directorate. Baker operates with the Cyber Workforce Development team where she is responsible for managing the development of training assets that support federal training directives. Baker has over 15 years of experience in information technology, particularly in information security and assurance training and holds a BS degree in Computer Science from Robert Morris University and an MS in Information Technology from Carnegie Mellon University, as well as several industry certifications. BREAKDOWN OF SUBCONTRACTORS EXPECTED TO ATTEND Mrs. Essye Miller Director, Cyber Security Army CIO/G6 Keynote: Vision of Army Cyber Security Mrs. Miller is a Senior Executive with broad experience information technology. During her 29- year career, Mrs. Miller has held positions of increased responsibility in U.S. Air Force, both tactical and strategic C4IT. As the Director for Cyber Security, Mrs. Miller assists the Secretary of the Army, the Chief of Staff of the Army, the Vice Chief of Staff of the Army and the CIO/G-6 with implementing cyber strategy and cyber- related information technology initiatives. She is also the Army's Senior Information Assurance Officer and therefore, she is responsible for the development, implementation, execution and oversight of the Army's Cyber Security program. Mrs. Miller holds a B.A. from Talladega College, a MBA from Troy State University, and a Masters of Strategic Studies from the United States Air War College, Pennsylvania.
- 4. Register Today! www.cybersecurityfordefense.com • 1-800-822-8684 • idga@idga.org AGENDA AT A GLANCE FUTURE REQUIREMENTS DAY: WEDNESDAY, JUNE 24, 2015 MAIN CONFERENCE DAY 1: THURSDAY, JUNE 25, 2015 08:00 Registration 08:45 Chairperson Welcome and Opening Remarks 09:00 Workshop A: DoD Cyber Warfare of 2025 10:30 Morning Networking & Refreshment Break 10:45 Workshop B: Network Resiliency: How to Mitigate the Damage after its Done 12:15 Lunch 13:15 Workshop C: Intrusion Detection and Firewall Customization 14:45 Afternoon Refreshment Break 15:00 Workshop D: Designing the Perfect Cyber Defender Team 16:30 Chairperson Closing Remarks 16:45 End of Future Requirements Day 08:00 Registration & Coffee 08:45 Chairperson’s Welcome and Opening Remarks 09:00 Keynote: Overview of US Cyber Command 09:45 Reserved for Presentation by Fort Gordon CG 10:30 Morning Networking & Refreshment Break 11:15 Cyber Security Best Practices: Offense VS Defense 12:30 Networking Lunch 13:30 Mitigating Human Error Within Your Network 14:15 Cyber Space Leadership Development Education and Training 15:00 Afternoon Networking & Refreshment Break 15:45 Reserved for Presentation by Commandant of U.S. Army Cyber School 16:30 Resilience Metrics for Cyber Systems 17:15 Closing Remarks 17:30 End of Main Conference Day One MAIN CONFERENCE DAY 2: FRIDAY, JUNE 26, 2015 07:45 Registration & Coffee 08:30 Chairperson’s Recap of Conference Day One 08:45 Quality Cyber Education 09:30 State of Cyber Workforce Development 10:15 Morning Networking & Refreshment Break 11:00 Overcoming the Inherent Vulnerabilities of Cyber Physical Facilities 11:45 Challenges within Cyber Security 12:30 Networking Lunch 13:30 Enduring Threats in Cyber Space 14:15 Afternoon Networking & Refreshment Break 14:45 Increasing Need for Cooperation within the Cyber Community 15:30 Predicting Cyber Attacks 16:15 Chairperson’s Closing Remarks 16:30 End of Conference
- 5. Register Today! www.cybersecurityfordefense.com • 1-800-822-8684 • idga@idga.org U.S. GOVERNMENT, MILITARY, AND LAW ENFORCEMENT VENDORS, CONSULTANTS, AND SOLUTION PROVIDERS ACADEMIA, NON-PROFIT, AND FOREIGN MILITARY Package Online Registration ends June 19th 2 Day Main Conference FREETOALLMILITARYANDGOVERNMENTEMPLOYEES All Federal Employees, to include Military Personnel, will be granted free admission to our event. However, in order to logistically support this event, we must require online pre-registration. Onsite registration will not be permitted and Online Registration will close on June 19th, 2015. Future Requirements Day TEAM DISCOUNTS* Number of Attendees Savings 3-4 10% 5 or more 15% PRICING, REGISTRATION & LOCATION Augusta Marriott at the Convention Center 210th Street, Augusta, Georgia 30901, United States Website: http://www.marriott.com/hotels/ travel/agsmc-augusta-marriott-at-the- convention-center/ Phone: (706) 722-8900 LOCATION & LODGING INFORMATION REGISTER ONLINE, BY EMAIL, PHONE, FAX OR MAIL Web: www.CyberSecurityforDefense.com Email: idga@idga.org Phone:1-800-882-8684 Mail: IQPC 535 5th Avenue, 8th Floor New York, NY 10017 MAKE CHECKS PAYABLE IN U.S. DOLLARS TO: IQPC *CT residents or people employed in the state of CT must add 6.35% sales tax. Team Discounts: For information on team discounts, please contact IQPC Customer Service at 1-800-882-8684. Only one discount may be applied per registrant. Special Discounts Available: A limited number of discounts are available for the non-profit sector, government organizations and academia. For more information, please contact customer service at 1-800-882-8684. Details for making payment via EFT or wire transfer: Bank-JP Morgan Chase & Co Name on Account: Penton Learning Systems LLC dba IQPC Account # 937-332641 ABA/Routing #: 021000021 Reference: IQPC: 25113.001 Payment Policy: Payment is due in full at the time of registration and includes lunches and refreshment. Your registration will not be confirmed until payment is received and may be subject to cancellation. For IQPC’s Cancellation, Postponement and Substitution Policy, please visit www.iqpc.com/cancellation Special Dietary Needs: If you have a dietary restriction, please contact Customer Service at 1-800-882-8684 to discuss your specific needs. ©2014 IQPC. All Rights Reserved. The format, design, content and arrangement of this brochure constitute a trademark of IQPC. Unauthorized reproduction will be actionable under the Lanham Act and common law principles Please note: • IQPC reserves the right to determine who qualifies as an end user • All‘Early Bird’discounts require payment at time of registration and before the cut-off date in order to receive any discount. • Any discounts offered (including team discounts) must also require payment at the time of registration. • All discount offers cannot be combined with any other offer. • Please view our registration policy for full information about payment, cancellation, postponement, substitution and discounts. • Please note multiple discounts cannot be combined Package Register & Pay By 4/3/15 Standard Price 2 Day Main Conference $895 $1295 3 Day All-Access Pass $1,395 $1795 Future Requirements Day $595 Package Register & Pay By 4/3/15 Standard Price 2 Day Main Conference $995 $1,395 3 Day All-Access Pass $1595 $1995 Future Requirements Day $695 Branding Pass – Only 5 Passes Available Includes: • 3 Day All-Access Pass • Company Logo on event website • 50 word company or product description on event website $2995 Networking Pass – Only 5 Passes Available Includes: • 3 Day All-Access Pass • Company Logo on event website • 50 word company or product description on event website • Small roundtable to demonstrate product or service to all event attendees* $3995