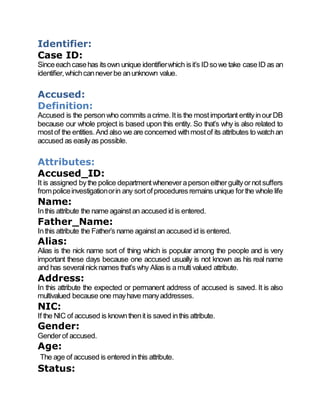
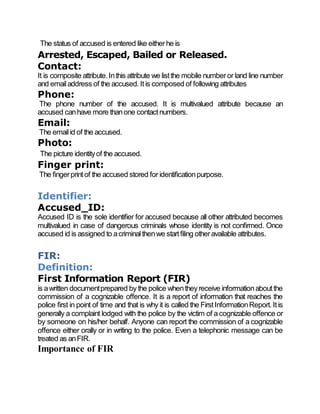
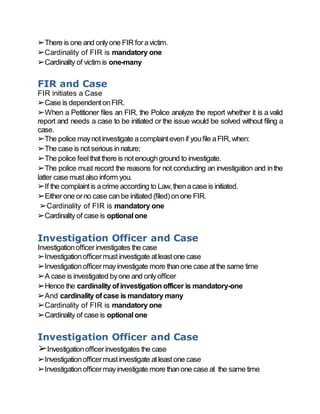
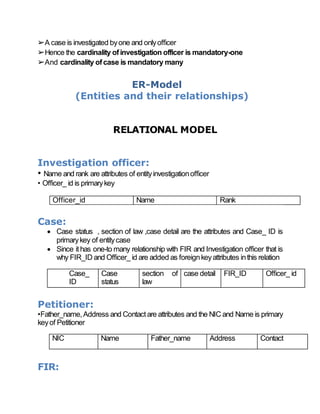
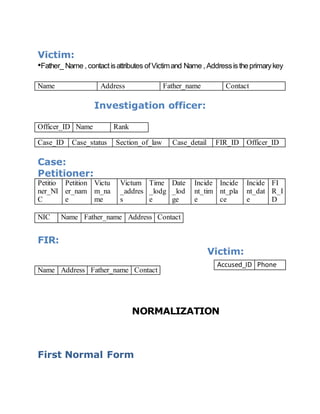
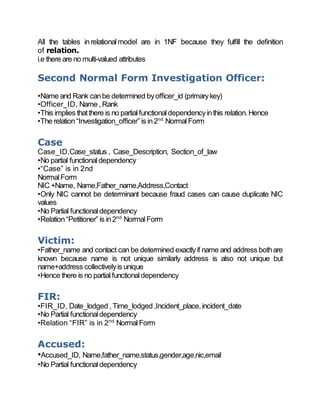
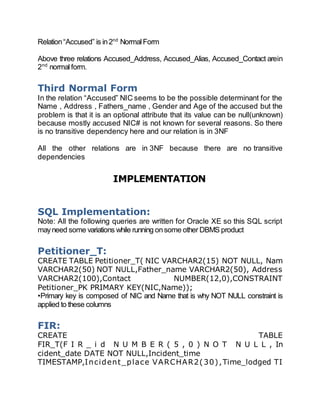
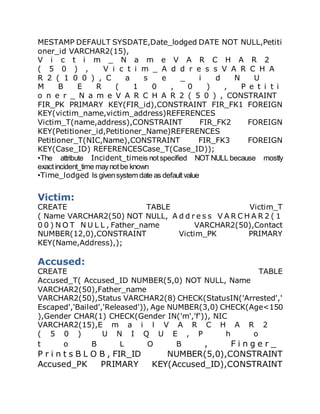
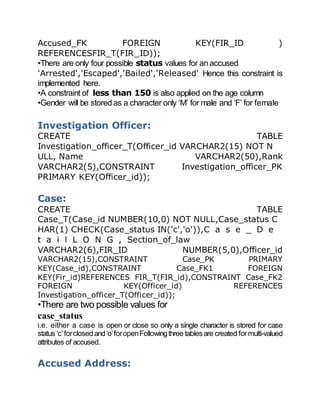
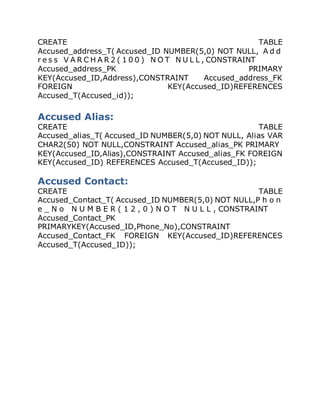
The document outlines a proposal for a Criminal Record Management System (CRMS) to improve the efficiency of police record-keeping regarding criminal cases. It details the entities involved, including petitioners, victims, accused individuals, FIRs, and investigation officers, along with their attributes and relationships. The implementation of this database system is expected to streamline the process of managing criminal records and enhance police operations.