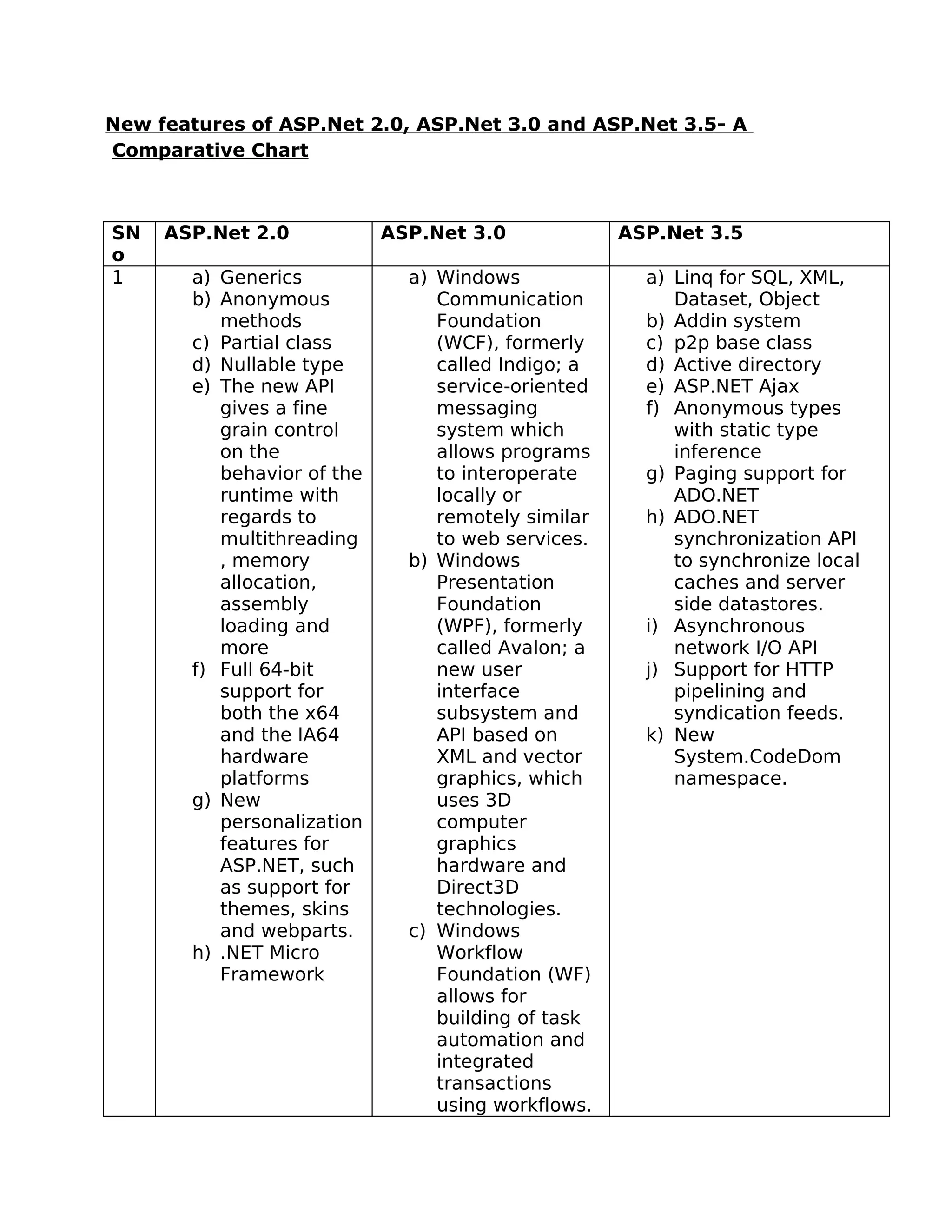
This document compares new features introduced in ASP.Net 2.0, 3.0 and 3.5. It shows features grouped by version in a table with three columns: ASP.Net 2.0, 3.0 and 3.5. Key features introduced include generics, anonymous methods and partial classes for 2.0, Windows Communication Foundation (WCF) and Windows Presentation Foundation (WPF) for 3.0, and LINQ, ASP.NET Ajax and paging support for 3.5.