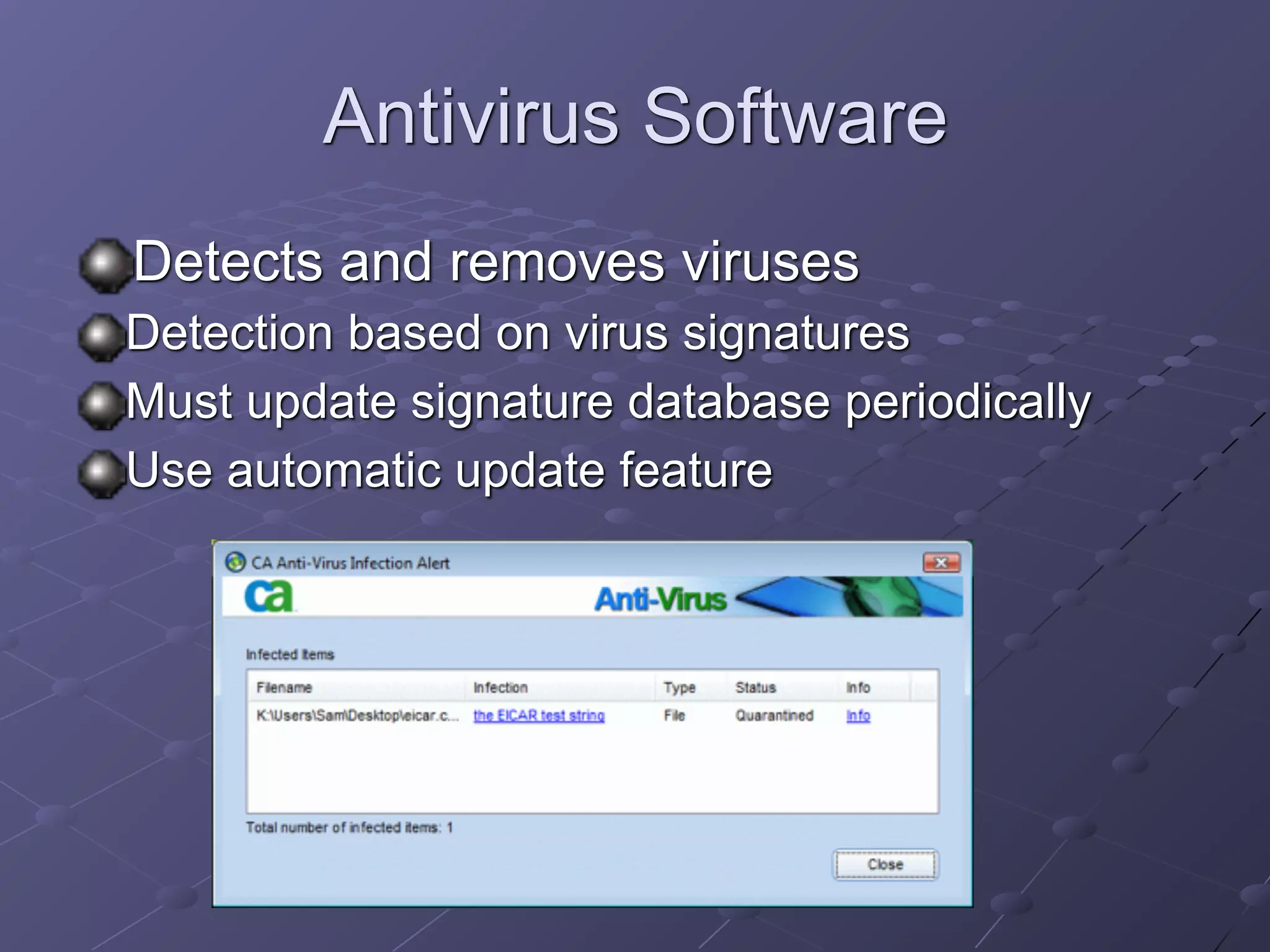
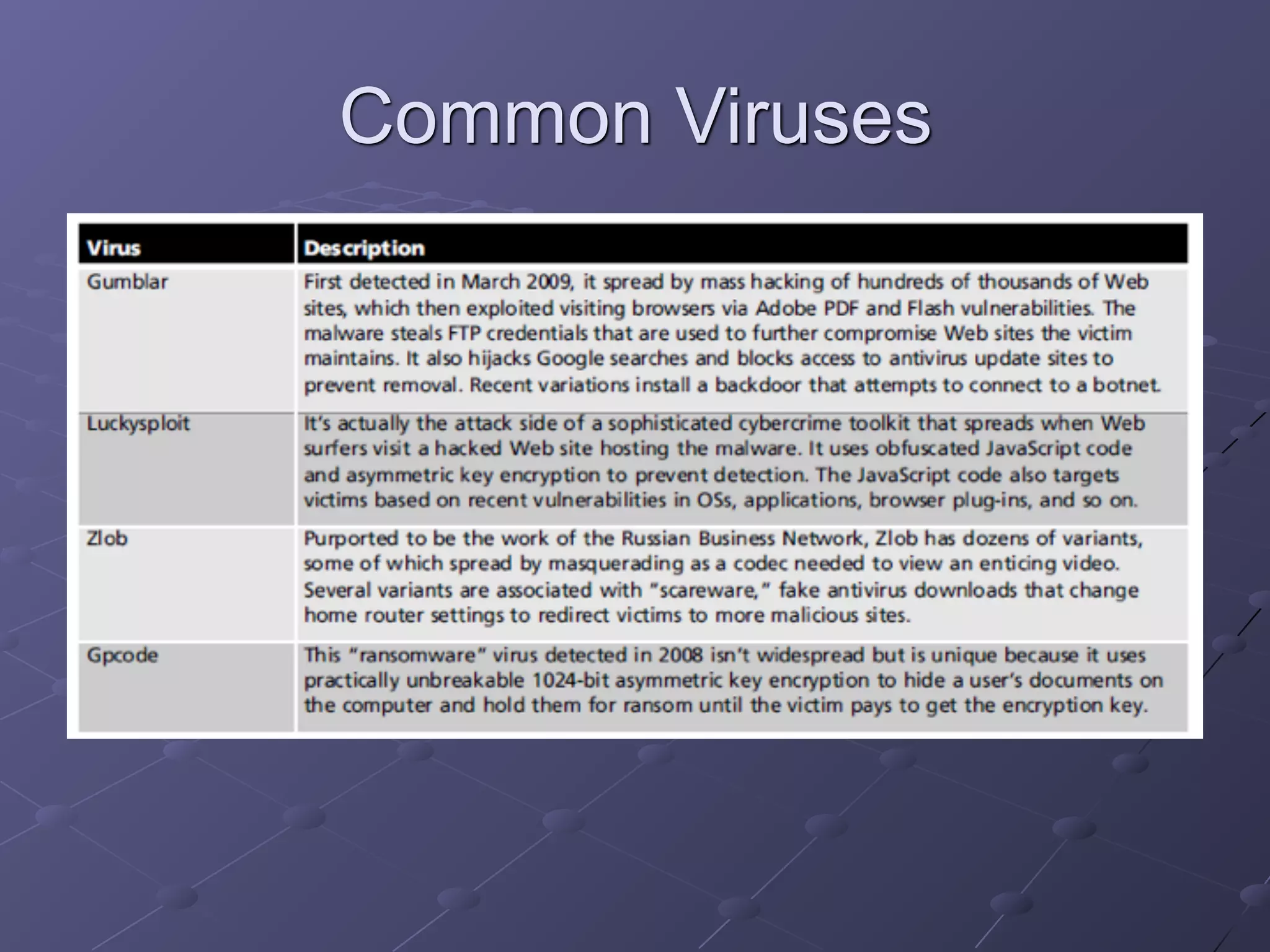
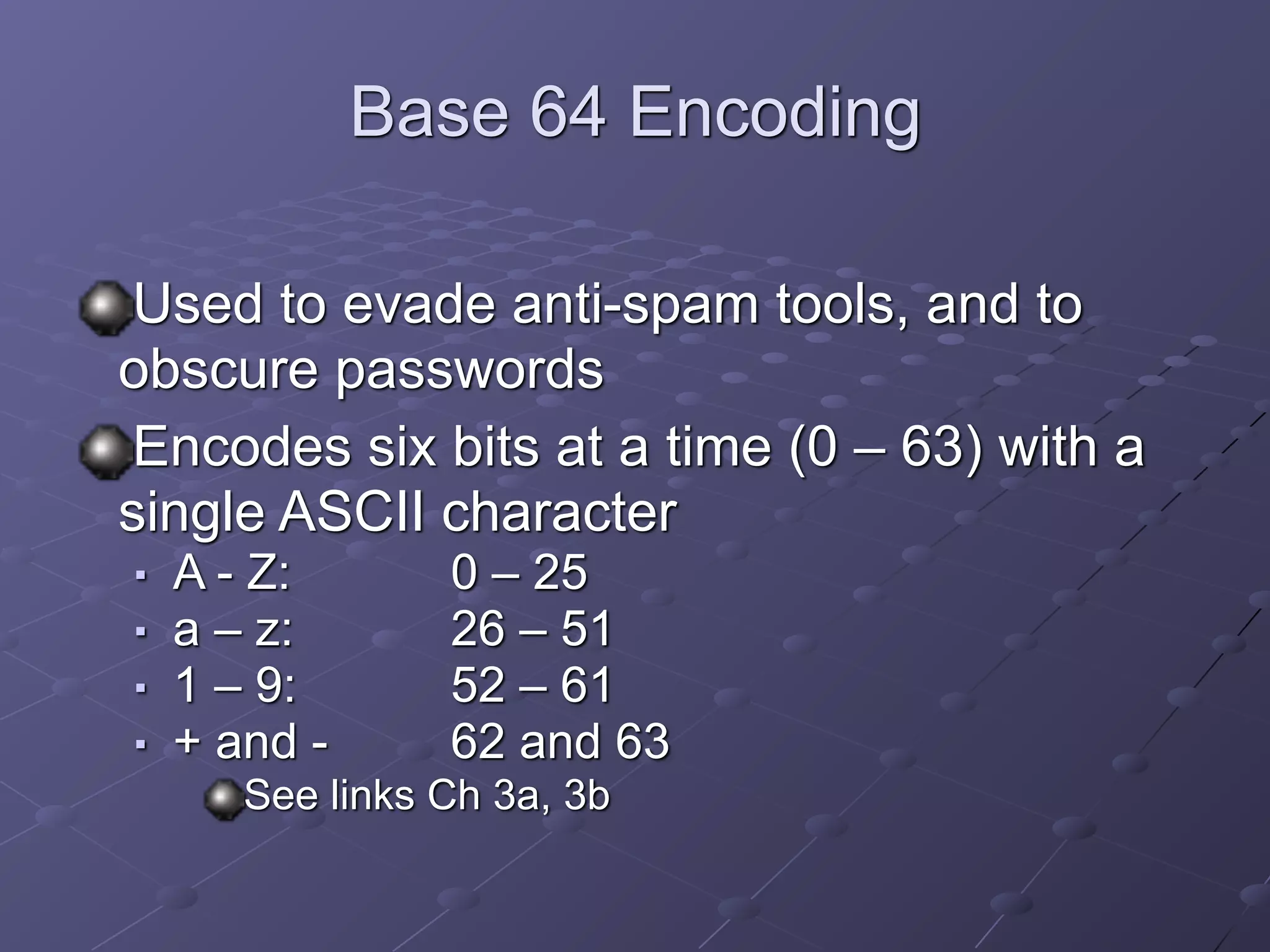
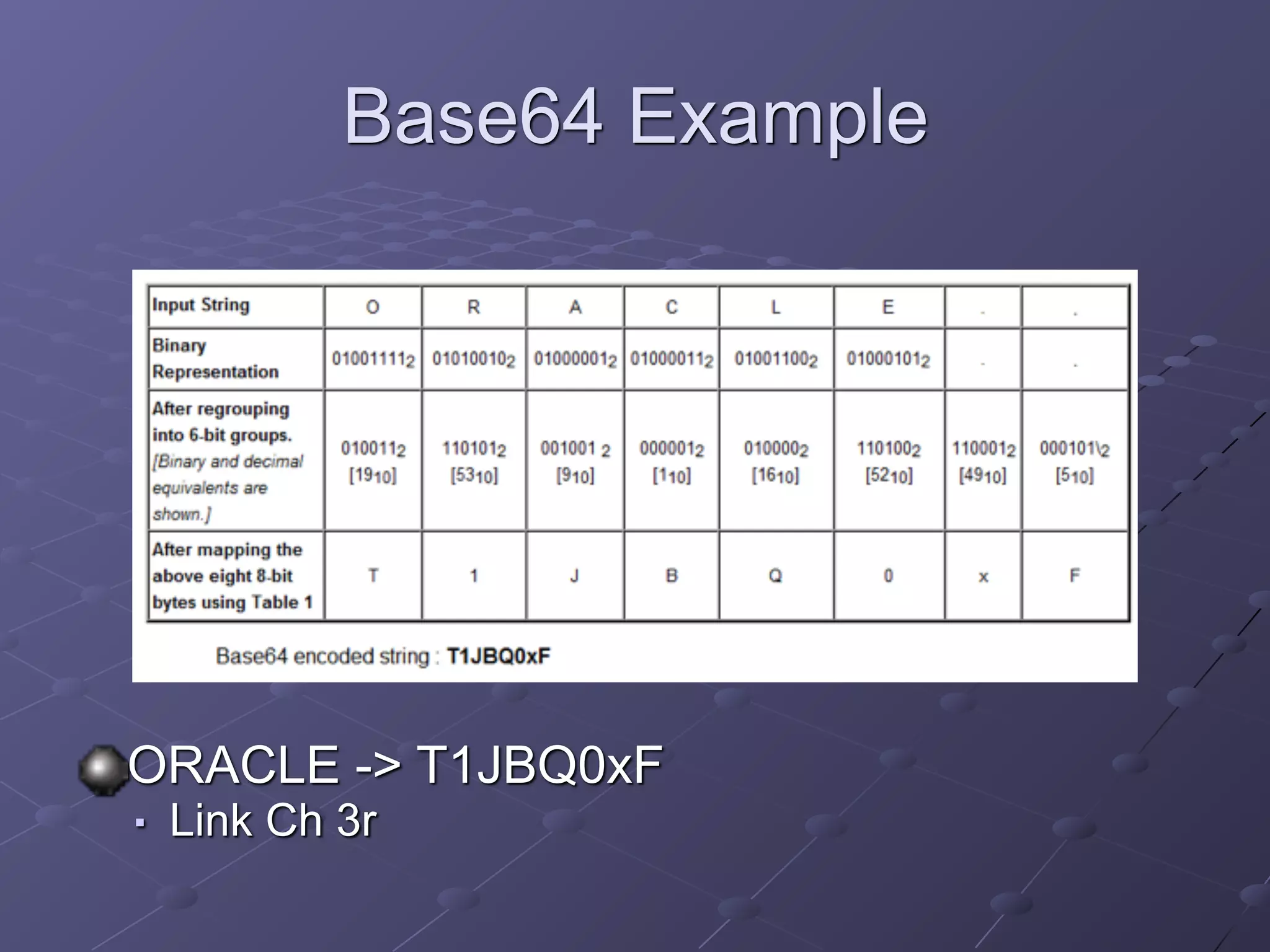
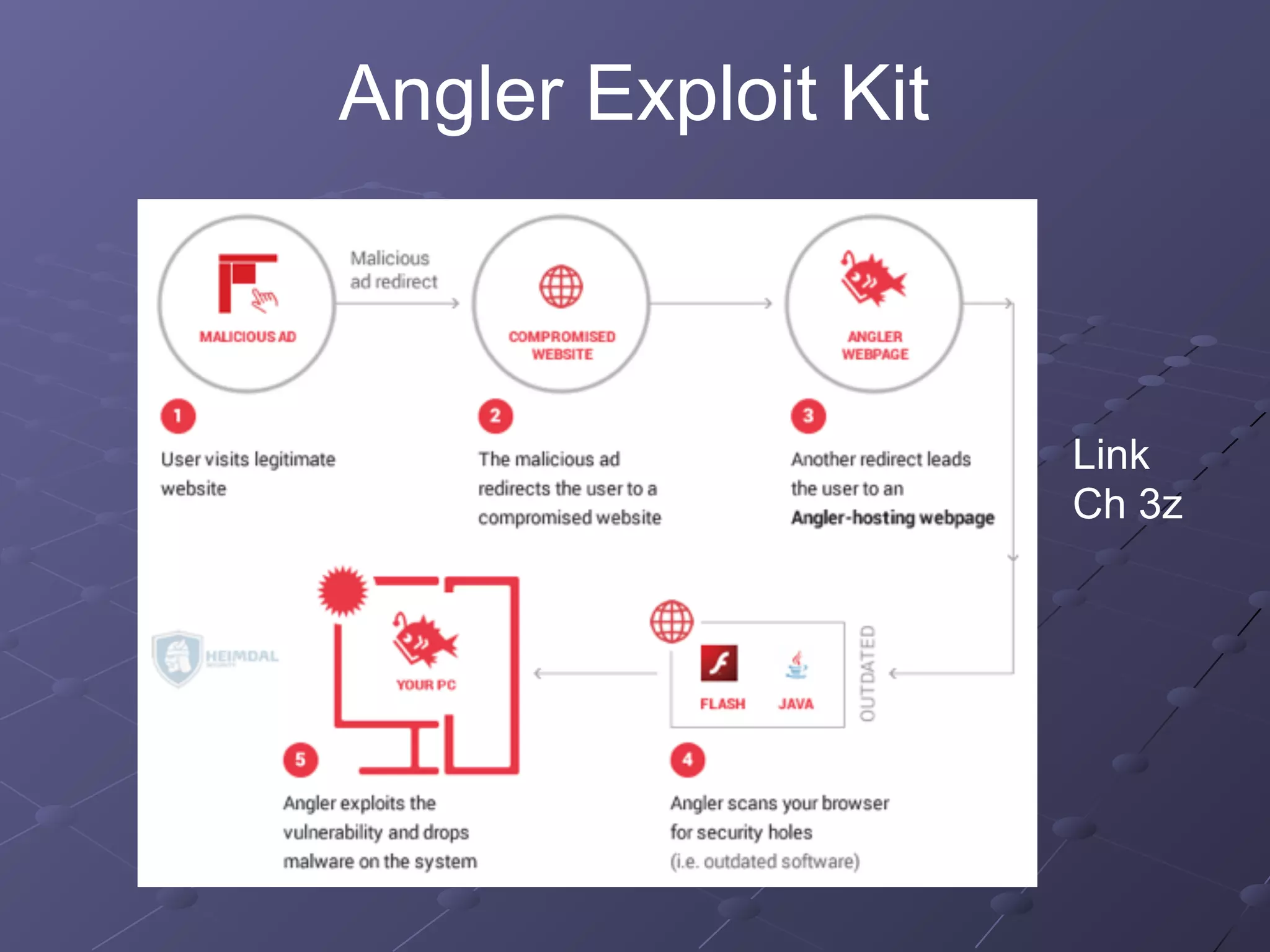
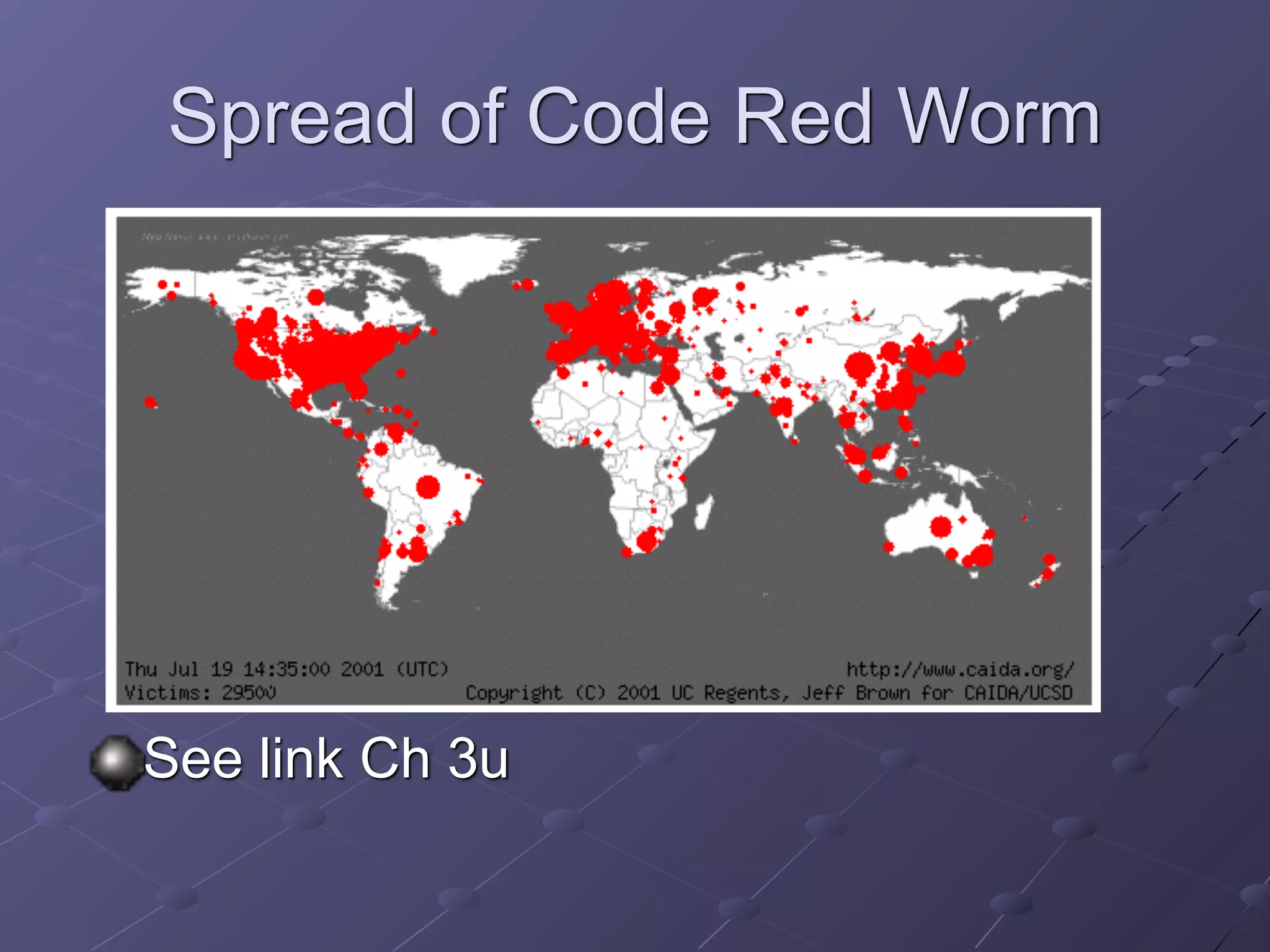
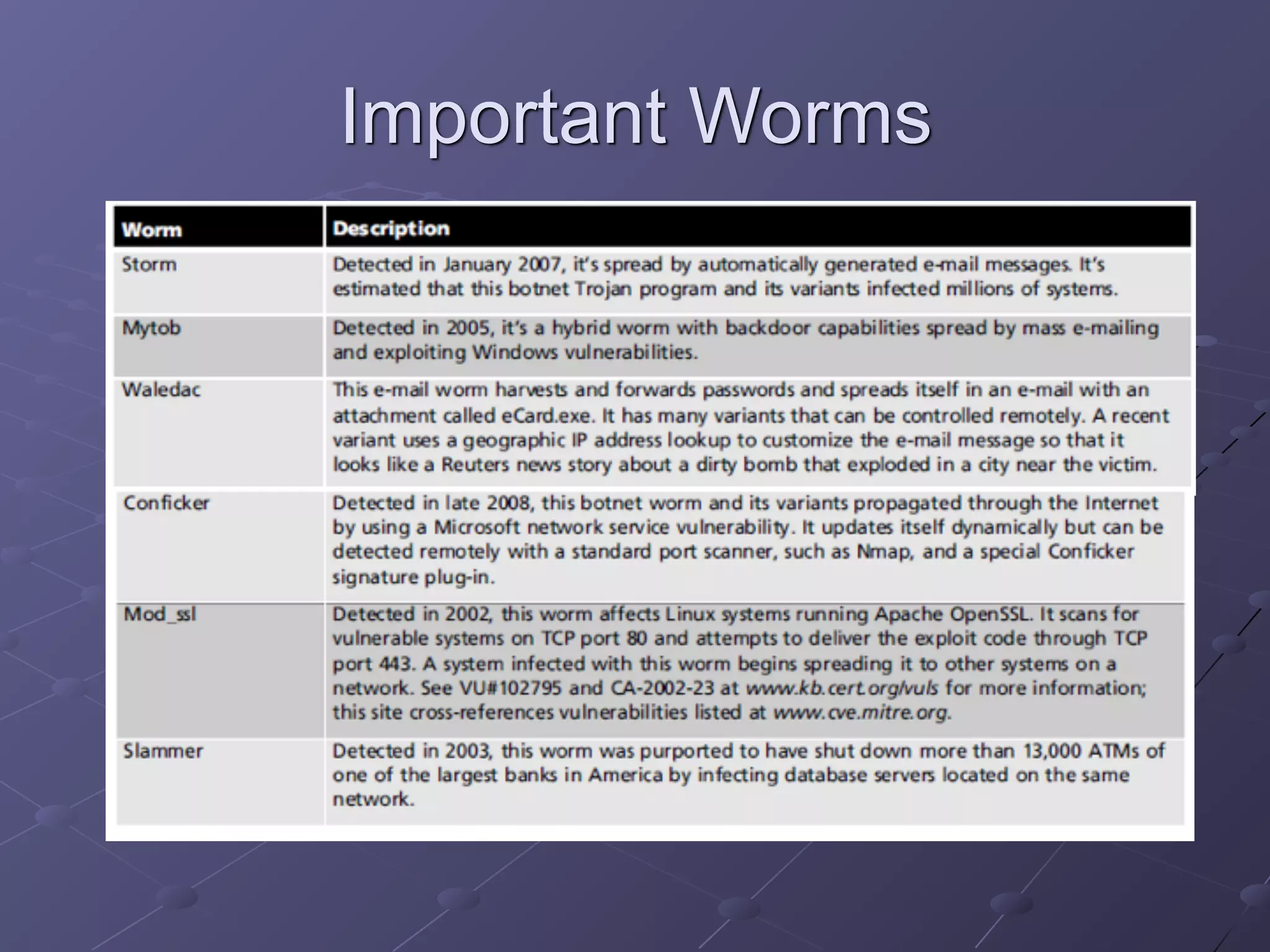
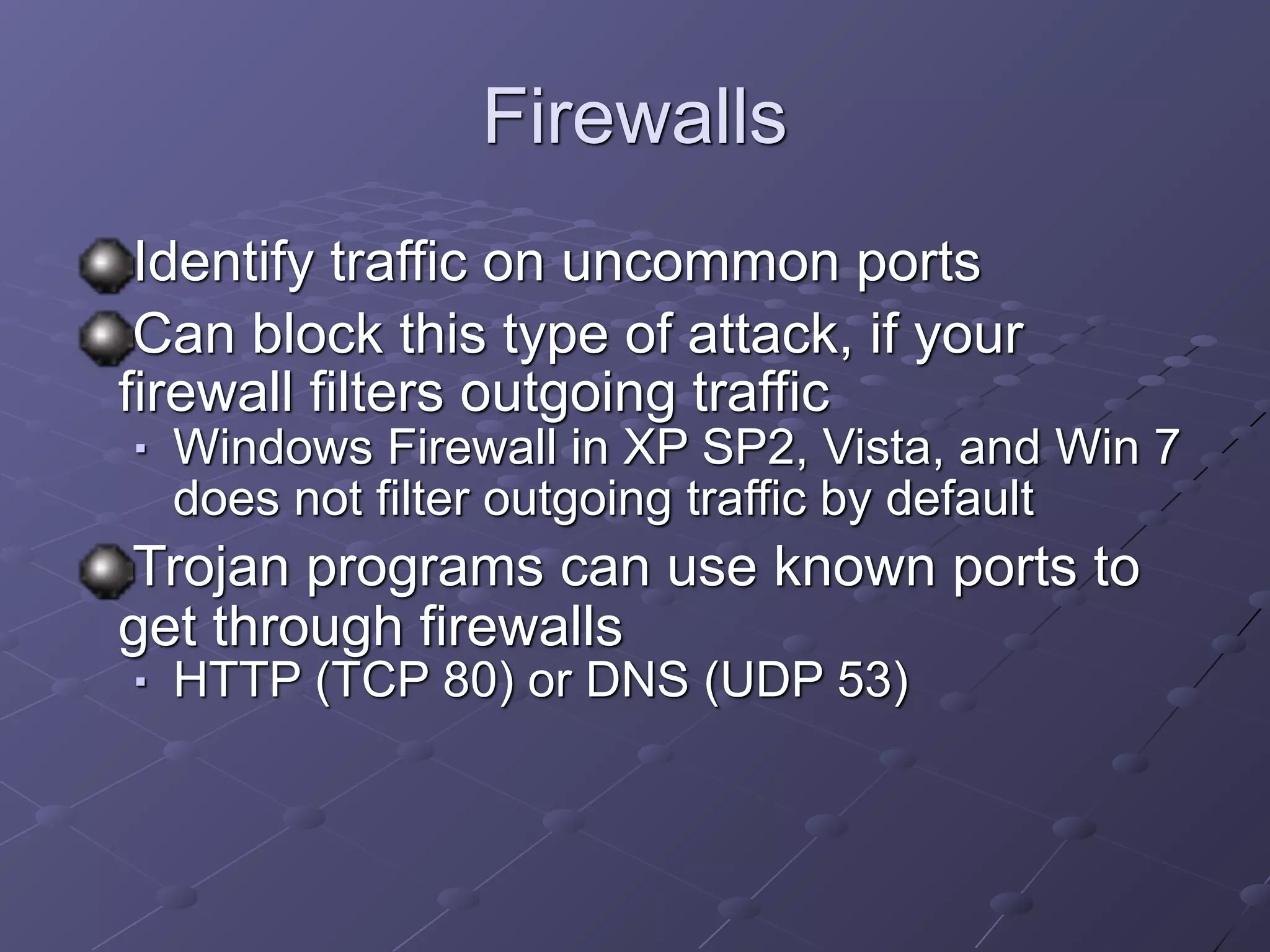
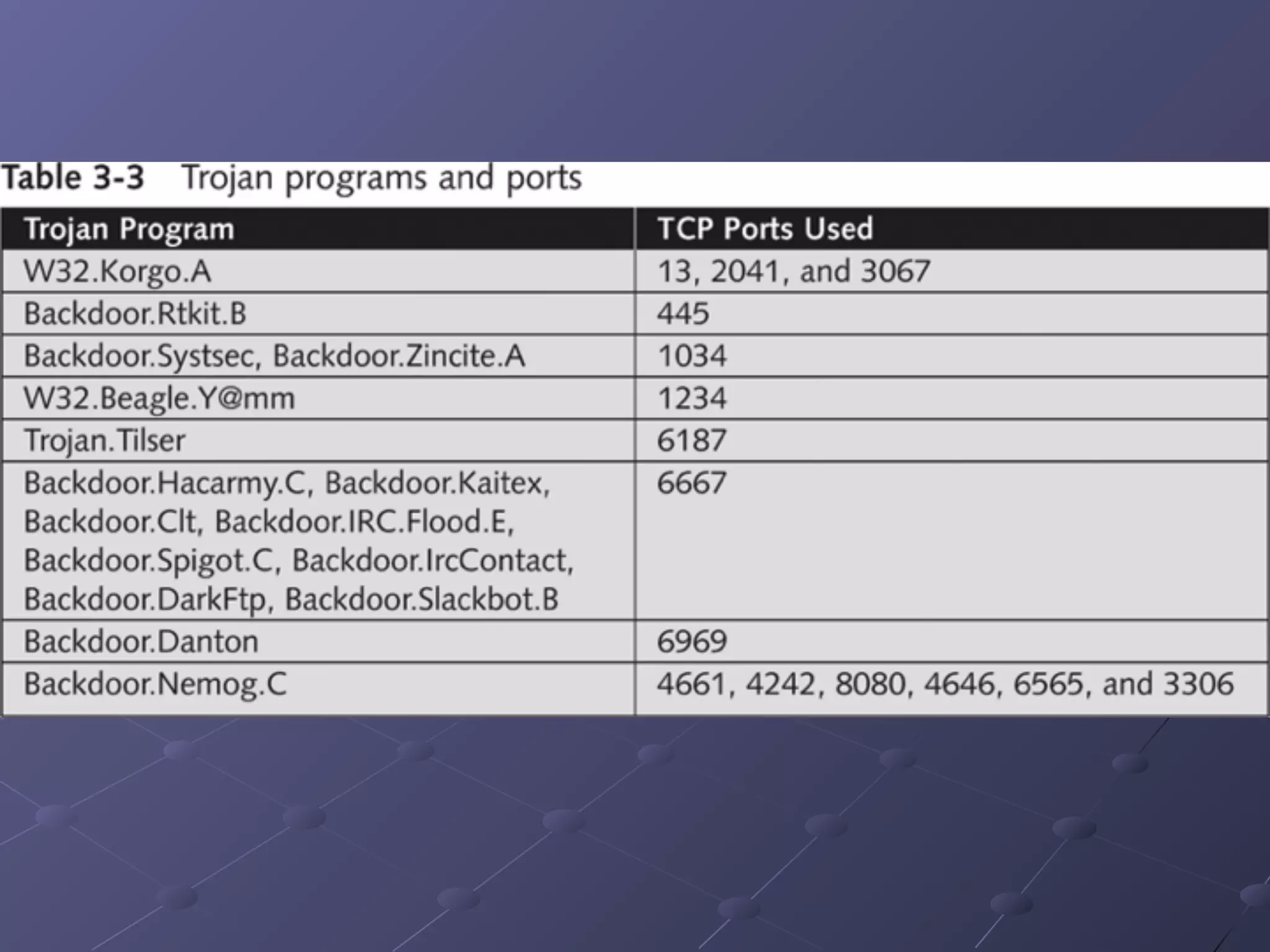
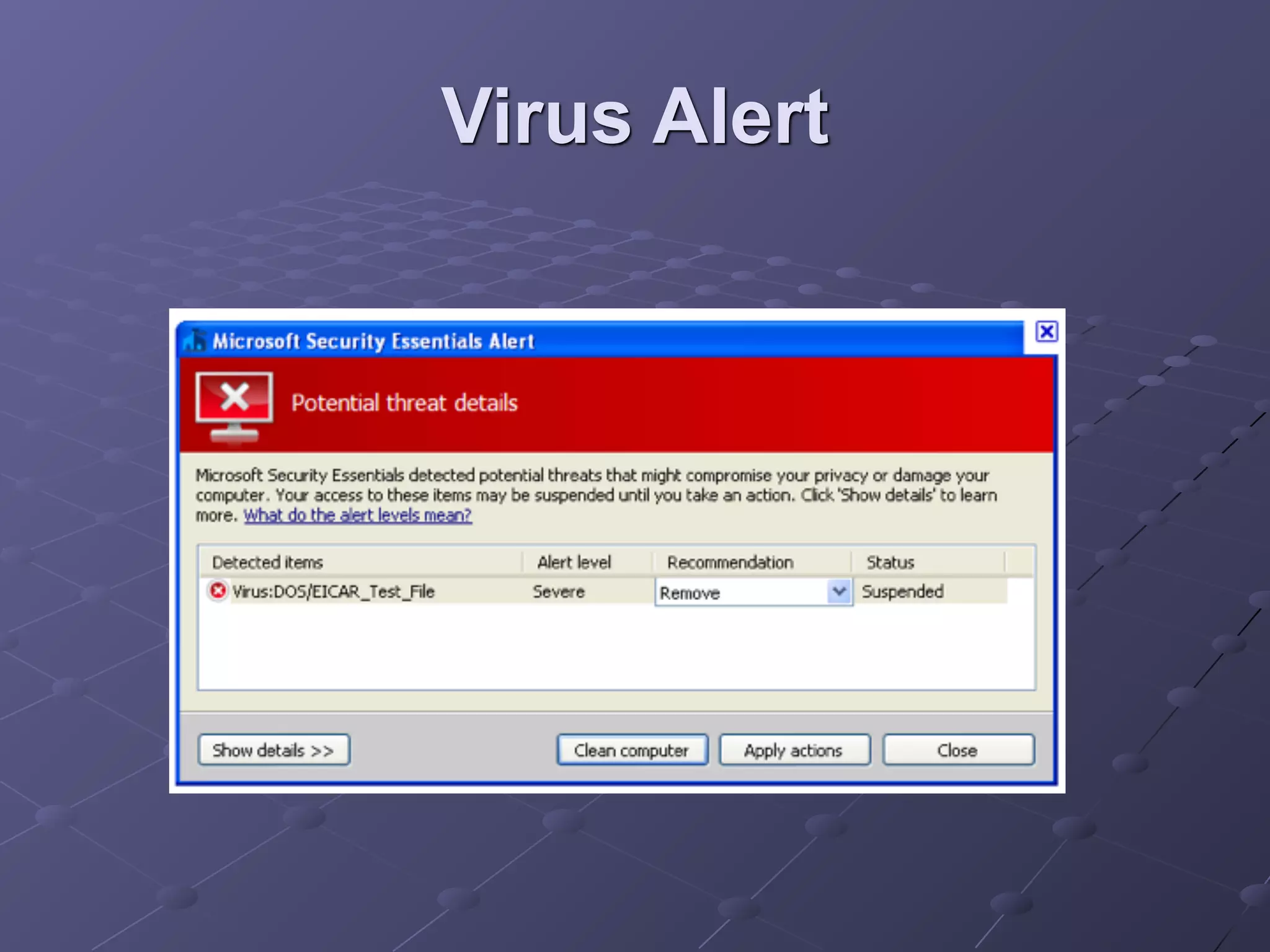
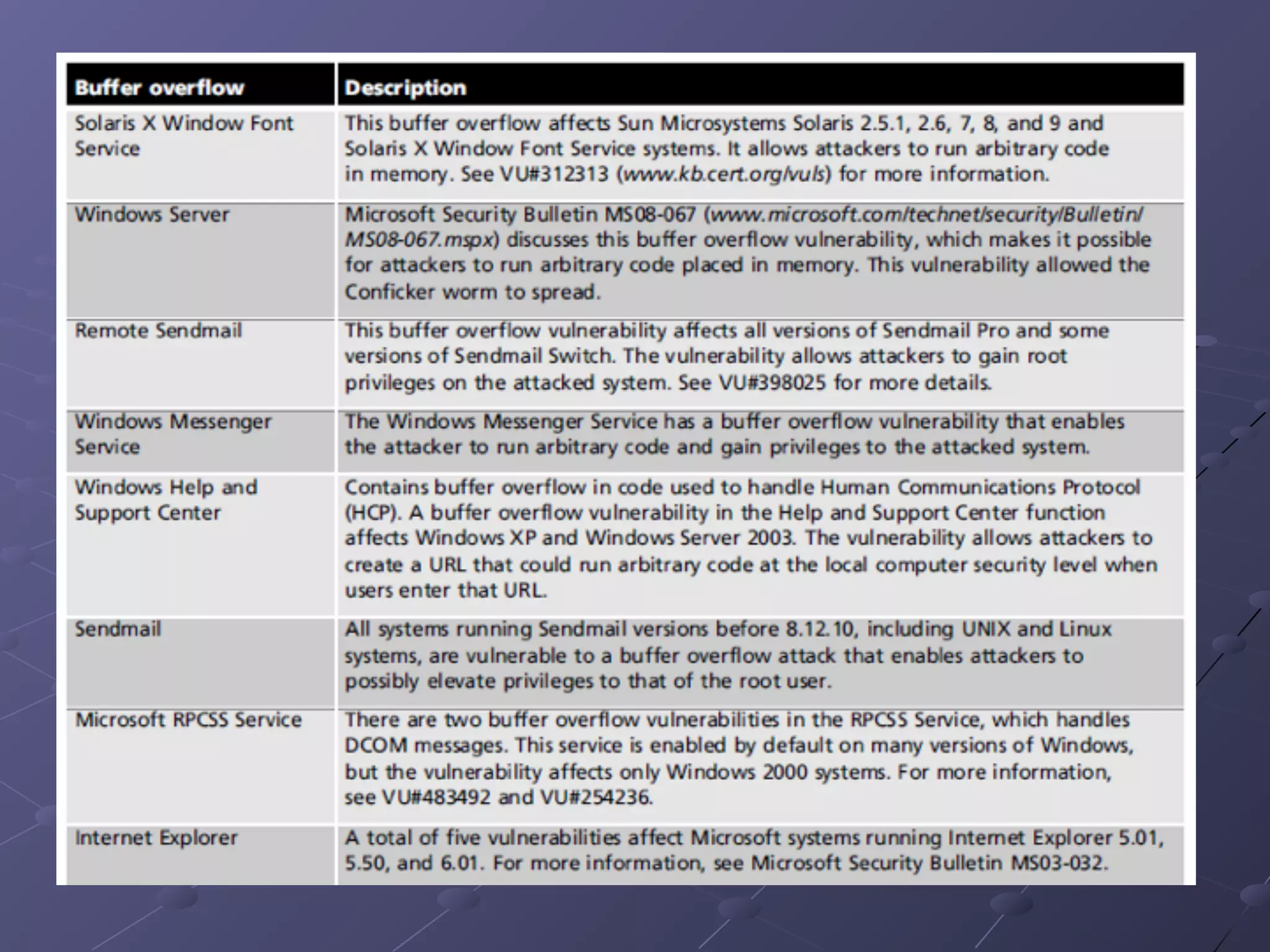
The document discusses various types of malware including viruses, worms, and trojan horses, outlining their behaviors, methods of propagation, and potential impacts on networks. It emphasizes the importance of antivirus software and user education in protecting against such threats, as well as discusses denial-of-service attacks and physical security measures necessary to safeguard network resources. Overall, it highlights the continuous evolution of cybersecurity threats and the need for vigilant protection strategies.