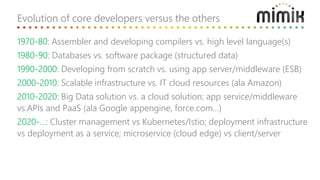
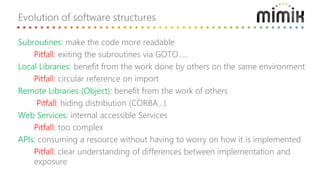
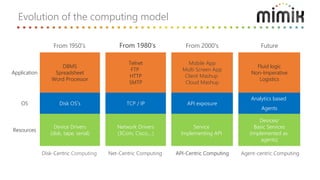
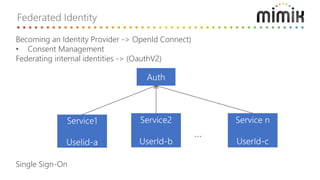
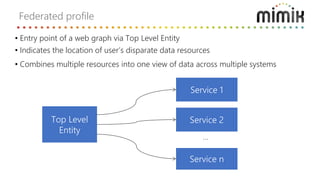
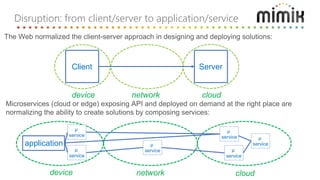
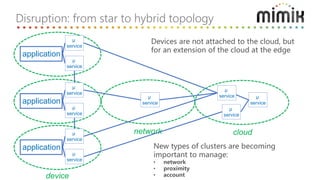
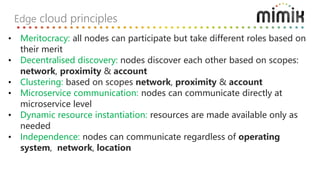
Michel Burger discusses extending cloud computing to the edge by deploying microservices and other cloud-native technologies closer to endpoints and data sources. He outlines how software and computing models have evolved over time from mainframes to client-server architectures to modern cloud-native approaches. Burger also discusses principles for building cloud applications including designing for failure, scaling, and managing state.