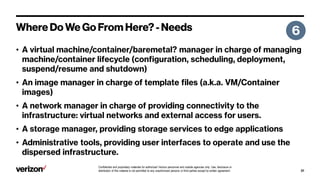
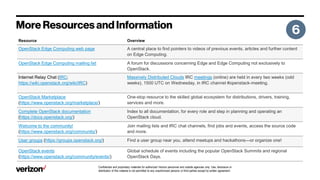
The document discusses confidential and proprietary materials for authorized Verizon personnel and outside agencies. It states that use, disclosure, or distribution of these materials is not permitted without a written agreement and is only for authorized individuals. It contains information about managed services, platforms, and resources related to edge computing using OpenStack.