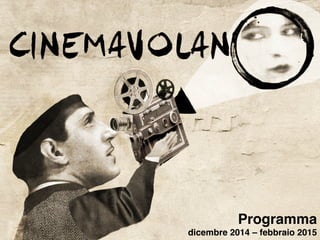
Cinema Volano - Programma Dicembre-Febbraio
•
0 likes•438 views
Programma completo fino a Febbraio 2015, con possibili modifiche future.
Report
Share
Report
Share
Download to read offline
Recommended
"Vita a giudizio" di Maria Rosa Menzio - Teatro e Scienza 

“VITA A GIUDIZIO”
MARIA ROSA MENZIO
di Maria Rosa Menzio
con MARIA ROSA MENZIO (Vita) MARICA VINASSA e ANTONIO CORNELJ (danza)
REGIA e VIDEO di MARIA ROSA MENZIO
Al termine dello spettacolo conferenza
“Il Genio Scientifico”
a cura di Francesco Profumo, Presidente Gruppo IREN, Mini- stro dell’Istruzione, Università e Ricerca (dal 2011 al 2013), ex Rettore del Politecnico di Torino ed ex Presidente del CNR
Digital Citizenship and Surveillance Society: Media

Presentation given by Karin Wahl-Jorgensen and Lucy Bennett at the "Surveillance and Citizenship" conference, Cardiff University, June 18, 2015
Corporate espionage versus competitive intelligence

The document discusses the difference between competitive intelligence and corporate espionage. Competitive intelligence involves gathering information from public records and thinking creatively about available public sources, while corporate espionage involves illegally obtaining private information. As business becomes more global, the distinction between legal and illegal information gathering will need to be clearer, and competitive intelligence practices rather than espionage should be used to get necessary information ethically. Learning competitive intelligence strategies can help businesses succeed without resorting to illegal tactics.
FLAME Conference Program

This document announces a conference titled "FLAME: Framing the Late Antique and Early Medieval Economy" to be held on April 29-30, 2016 at Princeton University. It will consist of presentations on topics related to coins, minting, and the economy in Late Antiquity and the Early Middle Ages. An additional workshop on circulation will take place on May 1. The conference is cosponsored by several departments and centers at Princeton University and will include discussions of coinage and monetary economies in the Byzantine Empire, Balkans, Mediterranean, and Western Europe during this transitional period.
10 Spying Strategies To Generate More Profit

This document outlines 10 strategies for generating more profit by spying on competitors. It discusses spying on competitors' placement strategies, top ads and creatives, split testing results, profitable traffic sources, mobile publishers, and keywords. Speakers from iSpionage and WhatRunsWhere provide insights and examples from ChristianMingle.com, BeyondDiet.com, Audible.com, and Zoosk to illustrate how to apply these strategies to an organization's own marketing. The strategies are meant to help cut costs and optimize performance by learning from competitors' testing and successes.
Recommended
"Vita a giudizio" di Maria Rosa Menzio - Teatro e Scienza 

“VITA A GIUDIZIO”
MARIA ROSA MENZIO
di Maria Rosa Menzio
con MARIA ROSA MENZIO (Vita) MARICA VINASSA e ANTONIO CORNELJ (danza)
REGIA e VIDEO di MARIA ROSA MENZIO
Al termine dello spettacolo conferenza
“Il Genio Scientifico”
a cura di Francesco Profumo, Presidente Gruppo IREN, Mini- stro dell’Istruzione, Università e Ricerca (dal 2011 al 2013), ex Rettore del Politecnico di Torino ed ex Presidente del CNR
Digital Citizenship and Surveillance Society: Media

Presentation given by Karin Wahl-Jorgensen and Lucy Bennett at the "Surveillance and Citizenship" conference, Cardiff University, June 18, 2015
Corporate espionage versus competitive intelligence

The document discusses the difference between competitive intelligence and corporate espionage. Competitive intelligence involves gathering information from public records and thinking creatively about available public sources, while corporate espionage involves illegally obtaining private information. As business becomes more global, the distinction between legal and illegal information gathering will need to be clearer, and competitive intelligence practices rather than espionage should be used to get necessary information ethically. Learning competitive intelligence strategies can help businesses succeed without resorting to illegal tactics.
FLAME Conference Program

This document announces a conference titled "FLAME: Framing the Late Antique and Early Medieval Economy" to be held on April 29-30, 2016 at Princeton University. It will consist of presentations on topics related to coins, minting, and the economy in Late Antiquity and the Early Middle Ages. An additional workshop on circulation will take place on May 1. The conference is cosponsored by several departments and centers at Princeton University and will include discussions of coinage and monetary economies in the Byzantine Empire, Balkans, Mediterranean, and Western Europe during this transitional period.
10 Spying Strategies To Generate More Profit

This document outlines 10 strategies for generating more profit by spying on competitors. It discusses spying on competitors' placement strategies, top ads and creatives, split testing results, profitable traffic sources, mobile publishers, and keywords. Speakers from iSpionage and WhatRunsWhere provide insights and examples from ChristianMingle.com, BeyondDiet.com, Audible.com, and Zoosk to illustrate how to apply these strategies to an organization's own marketing. The strategies are meant to help cut costs and optimize performance by learning from competitors' testing and successes.
Virus&malware

Viruses & malware come in many forms including computer viruses, worms, Trojan horses, spyware, and adware. Computer viruses can infect systems and replicate without user knowledge. Types of viruses include resident, direct action, overwrite, boot, macro, directory, and polymorphic viruses. Worms replicate to spread to other systems without user intervention. Trojans appear benign but perform malicious actions like unauthorized access. Spyware and adware secretly monitor users or display advertisements.
Cyber attack

In this presentation i have given the overview of different kind of cyber attacks or crimes, Email frauds ,fake mails ,how to create it and how to prevent it and different types of software's used for spying.......
Vishwadeep Presentation On NSA PRISM Spying

In this presentation we shows how NSA based PRISM works.
What methodology NSA used. What data Types NSA Collects. And How we can bypass NSA
Stuxnet flame

Stuxnet, Duqu, and Flame are sophisticated cyber weapons discovered between 2010-2012 that targeted industrial systems and stole information. Kaspersky Lab analysis found that a module from the early 2009 version of Stuxnet, known as "Resource 207", was actually a Flame plugin, indicating Flame existed prior to Stuxnet. This module was used by both Stuxnet and Flame to spread via USB drives using identical code. Stuxnet and Flame are believed to have been used by the U.S. to wage cyber warfare against Iran.
Cyber espionage - Tinker, taylor, soldier, spy

A look at the methodology and techniques or hackers, cyber criminals and state sponsored attackers. Explores the kill chain, Geo political instability and the dark web.
Lecture - Espionage by the Numbers: Introduction to Number Stations - Delft U...

This document discusses numbers stations and espionage. It describes how numbers stations transmit encrypted messages to spies using techniques like one-time pads and code tables. The document outlines the anatomy of a message, including call signs, headers with agent IDs and message sizes, figure groups, and redundancy checks. It also discusses who has historically operated numbers stations like the UK, Cuba, Russia and examines cases where spies have been arrested for receiving messages from numbers stations.
Espionage (m)

This document defines espionage and counterespionage. Espionage involves the collection of intelligence against unfriendly countries through both legal and illegal means. Legal espionage can occur through embassies, refugees, infiltrators, or technology. Illegal espionage includes activities like photography of restricted areas, bugging parties, using agents, phone tapping, and electronic surveillance. Counterespionage aims to foil enemy espionage and subversion attempts through preventive measures like controlling identities, communications, activities, movements, and publications to detect subversive activities. Detective counterespionage measures include surveillance, observation, secret searches, and secret inquiries.
Win32/Flamer: Reverse Engineering and Framework Reconstruction

In this talk one wouldn’t see any speculations on state-sponsored cyber-espionage and сonspirology theories on cyber weapon development. In the presentation authors will concentrate on different approaches to analysis of the malware based on object oriented architecture with respect to one of the most complex threat ever known while AV industry exists: Win32/Flamer. The authors will present methods of analysis of the malware developed in the course of research of such threats as Stuxnet, Duqu and Festi. The talk will shed light on the problems the researchers face during investigation of complex threats and the ways to deal with them using tools by Hex-Rays. The authors will also present the result of research on reconstructing framework which was used to construct Win32/Flamer and will show its similarity with Stuxnet/Duqu/Gauss with respect to code and architecture.
Cyber espionage nation state-apt_attacks_on_the_rise

In the digital age, one of the most effective ways to gather data and information about a potential enemy state is by infiltrating their ranks with malware. This webinar takes a deep drive into advanced persistent threat attacks performed by nation states. We will discuss various actors, government sponsored hackers, such as Duke, Bear, and Panda. Then we will look at malware created, like Regin, Elise, Flame, Equation Group, Babar, OnionDuke, and Dark Hotel.
Chetan

Flame photometry is a technique that uses the intensity of light emitted from excited metal atoms to determine the concentration of metals in a solution. It works by nebulizing a liquid sample into a flame, which excites the metal atoms causing them to emit light at characteristic wavelengths. A monochromator isolates the wavelengths, and a detector measures the light intensities to quantify the metals. Common applications include analysis of sodium, potassium, lithium, calcium, and barium in biological fluids and industrial samples. Potential interferences include overlap of emission spectra between elements, ionization of atoms, and chemical reactions affecting atomization. New technologies allow simultaneous detection of multiple elements to improve accuracy and efficiency.
Espionage

Espionage involves governments or individuals obtaining secret information without authorization. Spies collect valuable intelligence for agencies while blending in anonymously. A handler manages human agents and networks, training them in secret communication techniques. Agents operate under direction to acquire information, while moles pretend loyalty while spying. Spy rings coordinate cells of agents, with members ignorant of others to limit damage if caught. Dead drops, concealment devices, and secret codes help spies exchange information covertly while maintaining operational security.
Flame test part 2

This document describes the procedure and observations of a flame test experiment. The experiment involves placing various metal salt solutions on a nichrome wire and exposing the wire to a flame to observe the color of the flame. Each metal ion produces a unique color that can be used to identify the metal. Some difficulties noted are that some colors are similar, and samples with multiple metals produce mixed colors that are difficult to interpret. Real-world applications of flame tests discussed are in fireworks to produce various colored explosions, and in forensic science to identify metals in blood samples.
More Related Content
Viewers also liked
Virus&malware

Viruses & malware come in many forms including computer viruses, worms, Trojan horses, spyware, and adware. Computer viruses can infect systems and replicate without user knowledge. Types of viruses include resident, direct action, overwrite, boot, macro, directory, and polymorphic viruses. Worms replicate to spread to other systems without user intervention. Trojans appear benign but perform malicious actions like unauthorized access. Spyware and adware secretly monitor users or display advertisements.
Cyber attack

In this presentation i have given the overview of different kind of cyber attacks or crimes, Email frauds ,fake mails ,how to create it and how to prevent it and different types of software's used for spying.......
Vishwadeep Presentation On NSA PRISM Spying

In this presentation we shows how NSA based PRISM works.
What methodology NSA used. What data Types NSA Collects. And How we can bypass NSA
Stuxnet flame

Stuxnet, Duqu, and Flame are sophisticated cyber weapons discovered between 2010-2012 that targeted industrial systems and stole information. Kaspersky Lab analysis found that a module from the early 2009 version of Stuxnet, known as "Resource 207", was actually a Flame plugin, indicating Flame existed prior to Stuxnet. This module was used by both Stuxnet and Flame to spread via USB drives using identical code. Stuxnet and Flame are believed to have been used by the U.S. to wage cyber warfare against Iran.
Cyber espionage - Tinker, taylor, soldier, spy

A look at the methodology and techniques or hackers, cyber criminals and state sponsored attackers. Explores the kill chain, Geo political instability and the dark web.
Lecture - Espionage by the Numbers: Introduction to Number Stations - Delft U...

This document discusses numbers stations and espionage. It describes how numbers stations transmit encrypted messages to spies using techniques like one-time pads and code tables. The document outlines the anatomy of a message, including call signs, headers with agent IDs and message sizes, figure groups, and redundancy checks. It also discusses who has historically operated numbers stations like the UK, Cuba, Russia and examines cases where spies have been arrested for receiving messages from numbers stations.
Espionage (m)

This document defines espionage and counterespionage. Espionage involves the collection of intelligence against unfriendly countries through both legal and illegal means. Legal espionage can occur through embassies, refugees, infiltrators, or technology. Illegal espionage includes activities like photography of restricted areas, bugging parties, using agents, phone tapping, and electronic surveillance. Counterespionage aims to foil enemy espionage and subversion attempts through preventive measures like controlling identities, communications, activities, movements, and publications to detect subversive activities. Detective counterespionage measures include surveillance, observation, secret searches, and secret inquiries.
Win32/Flamer: Reverse Engineering and Framework Reconstruction

In this talk one wouldn’t see any speculations on state-sponsored cyber-espionage and сonspirology theories on cyber weapon development. In the presentation authors will concentrate on different approaches to analysis of the malware based on object oriented architecture with respect to one of the most complex threat ever known while AV industry exists: Win32/Flamer. The authors will present methods of analysis of the malware developed in the course of research of such threats as Stuxnet, Duqu and Festi. The talk will shed light on the problems the researchers face during investigation of complex threats and the ways to deal with them using tools by Hex-Rays. The authors will also present the result of research on reconstructing framework which was used to construct Win32/Flamer and will show its similarity with Stuxnet/Duqu/Gauss with respect to code and architecture.
Cyber espionage nation state-apt_attacks_on_the_rise

In the digital age, one of the most effective ways to gather data and information about a potential enemy state is by infiltrating their ranks with malware. This webinar takes a deep drive into advanced persistent threat attacks performed by nation states. We will discuss various actors, government sponsored hackers, such as Duke, Bear, and Panda. Then we will look at malware created, like Regin, Elise, Flame, Equation Group, Babar, OnionDuke, and Dark Hotel.
Chetan

Flame photometry is a technique that uses the intensity of light emitted from excited metal atoms to determine the concentration of metals in a solution. It works by nebulizing a liquid sample into a flame, which excites the metal atoms causing them to emit light at characteristic wavelengths. A monochromator isolates the wavelengths, and a detector measures the light intensities to quantify the metals. Common applications include analysis of sodium, potassium, lithium, calcium, and barium in biological fluids and industrial samples. Potential interferences include overlap of emission spectra between elements, ionization of atoms, and chemical reactions affecting atomization. New technologies allow simultaneous detection of multiple elements to improve accuracy and efficiency.
Espionage

Espionage involves governments or individuals obtaining secret information without authorization. Spies collect valuable intelligence for agencies while blending in anonymously. A handler manages human agents and networks, training them in secret communication techniques. Agents operate under direction to acquire information, while moles pretend loyalty while spying. Spy rings coordinate cells of agents, with members ignorant of others to limit damage if caught. Dead drops, concealment devices, and secret codes help spies exchange information covertly while maintaining operational security.
Flame test part 2

This document describes the procedure and observations of a flame test experiment. The experiment involves placing various metal salt solutions on a nichrome wire and exposing the wire to a flame to observe the color of the flame. Each metal ion produces a unique color that can be used to identify the metal. Some difficulties noted are that some colors are similar, and samples with multiple metals produce mixed colors that are difficult to interpret. Real-world applications of flame tests discussed are in fireworks to produce various colored explosions, and in forensic science to identify metals in blood samples.
Viewers also liked (12)
Lecture - Espionage by the Numbers: Introduction to Number Stations - Delft U...

Lecture - Espionage by the Numbers: Introduction to Number Stations - Delft U...
Win32/Flamer: Reverse Engineering and Framework Reconstruction

Win32/Flamer: Reverse Engineering and Framework Reconstruction
Cyber espionage nation state-apt_attacks_on_the_rise

Cyber espionage nation state-apt_attacks_on_the_rise
Cinema Volano - Programma Dicembre-Febbraio
- 1. Programma dicembre 2014 – febbraio 2015! !
- 2. Programma dicembre 2014 – febbraio 2015! ! ! TORNERANNO I PRATI! Venerdì 5, sabato 6 e domenica 7 dicembre ad ore 20.30! Regia: Ermanno Olmi - Genere: drammatico/guerra - Durata 80’! ! ! UN INSOLITO NAUFRAGO NELL’INQUIETO MARE D’ORIENTE! Venerdì 12, sabato 13 e domenica 14 dicembre ad ore 20.30! Regia: Sylvain Estibal - Genere: commedia - Durata 99’! ! !
- 3. Programma dicembre 2014 – febbraio 2015! ! ! BOXTROLLS – LE SCATOLE MAGICHE prezzo unico € 3,50! Sabato 13 e domenica 14 dicembre ad ore 16.00! Regia: Graham Annable, Anthony Stacchi - Genere: animazione - Durata 97’! ! IL GATTOPARDO! Venerdì 26 ad ore 16.00 e 20.30, sabato 27 dicembre ad 20.00! Regia: Luchino Visconti - Genere: drammatico, storico - Durata 185’! ! !
- 4. Programma dicembre 2014 – febbraio 2015! ! ! IL MIO AMICO NANUK prezzo unico € 3,50! Sabato 27 e domenica 28 dicembre ad 15.30! Regia: Roger Spottiswoode, Brando Quilici - Genere: avventura - Durata 90’! ! ! DUE GIORNI E UNA NOTTE! Venerdì 2, sabato 3 e domenica 4 gennaio ad ore 20.30! Regia: Jean-Pierre Dardenne, Luc Dardenne - Genere: drammatico - Durata 95’!
- 5. Programma dicembre 2014 – febbraio 2015! ! ! MAGIC IN THE MOONLIGHT! Venerdì 9, sabato 10 e domenica 11 gennaio ad ore 20.30! Regia: Woody Allen - Genere: commedia - Durata 98’! ! ! I PINGUINI DI MADAGASCAR prezzo unico € 3,50! Sabato 10 e domenica 11 gennaio ad ore 16.00! Regia: Eric Darnell, Simon J. Smith - Genere: animazione - Durata 92’!
- 6. Programma dicembre 2014 – febbraio 2015! ! ! IL SALE DELLA TERRA! Venerdì 16, sabato 17 e domenica 18 gennaio ad ore 20.30! Regia: Wim Wenders, Juliano Ribeiro Salgado – Genere Documentario – Durata 100’! ! ! PRIDE! Venerdì 23, sabato 24 e domenica 25 gennaio ad ore 20.30! Regia: Matthew Warchus - Genere: commedia - Durata 120’ !
- 7. Programma dicembre 2014 – febbraio 2015! ! ! BIG HERO 6 prezzo unico € 3,50! Sabato 24 e domenica 25 gennaio ad ore 16.00! Regia: Don Hall, Chris Williams - Genere: animazione - Durata 105’! ! ! ! THE IMITATION GAME! Venerdì 30, sabato 31 e domenica 1 febbraio ad ore 20.30! Regia: Morten Tyldum - Genere: drammatico/thriller - Durata 113’!
- 8. Programma dicembre 2014 – febbraio 2015! ! AMERICAN SNIPER! Venerdì 6, sabato 7 e domenica 8 febbraio ad ore 20.30! Regia: Clint Eastwood - Genere: azione/guerra - Durata 120’! ! ! PADDINGTON prezzo unico € 3,50! Sabato 7 e domenica 8 febbraio ad ore 16.00! Regia: Paul King - Genere: animazione - Durata 95’! !