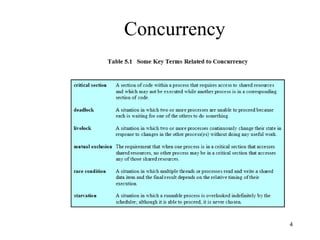
This document discusses problems that can occur with concurrency, including sharing global resources, locating programming errors, and efficiently locking resources. It also covers solutions to concurrency issues like mutual exclusion using semaphores, monitors, and message passing between processes.