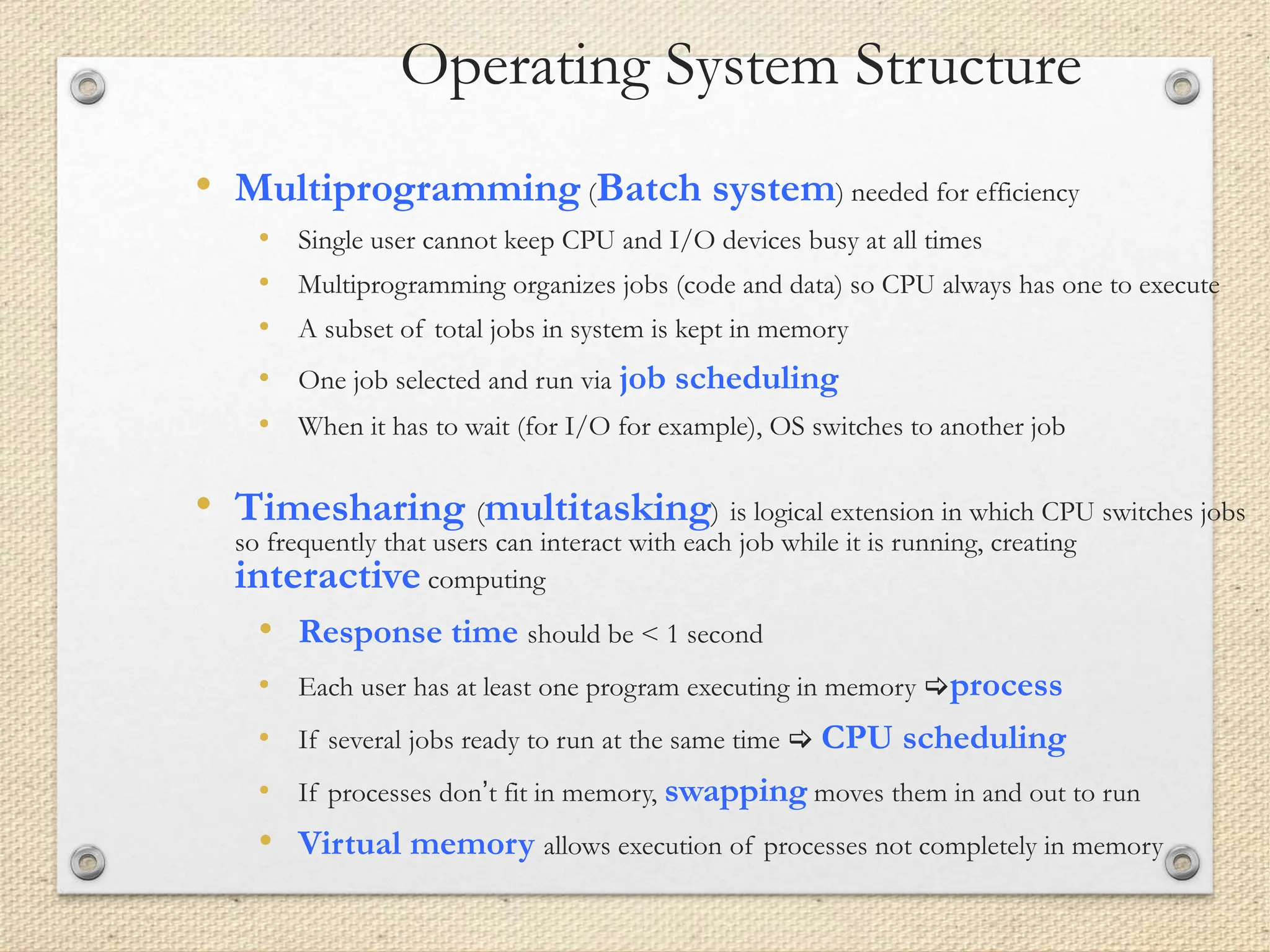
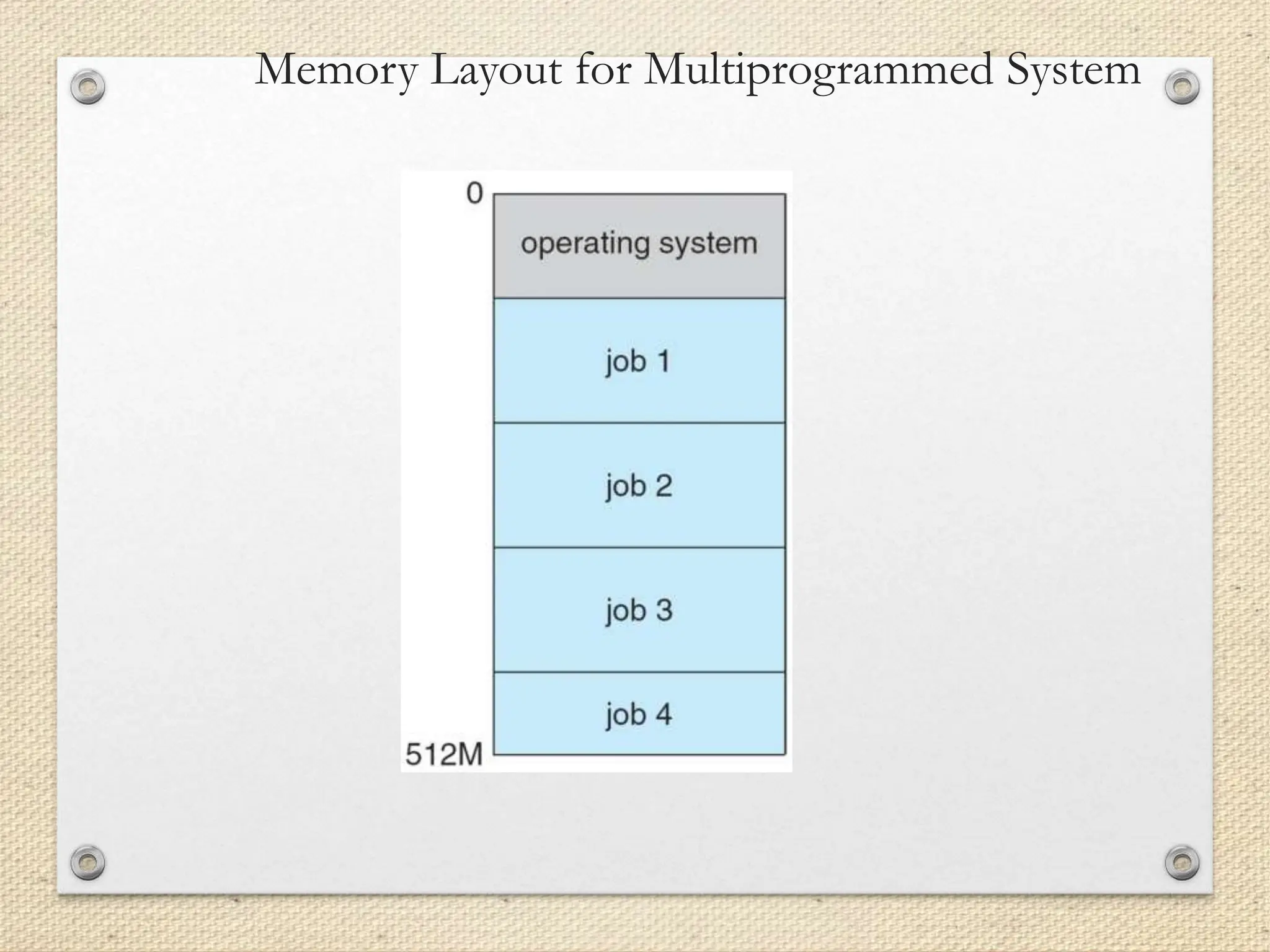
This document provides an overview of operating system concepts. It begins with an introduction to operating systems and their basic functions such as executing programs, allocating resources, and acting as an interface between hardware and software. It then describes computer system organization including CPUs, memory, I/O devices, and buses. Next, it discusses operating system structure, operations, and common components like process management, memory management, and storage management. Finally, it provides examples of different computing environments and open-source operating systems.