Report
Share
Download to read offline
Recommended
Object Oriented Programming with JAVA

Lecture Notes
Module-1, Chapter-1
An Overview of Java
Programme: B E (CSE)
Semester: 3
Course Code: BCS306A
Course Instructor: Demian Antony Dmello
2022 Scheme of VTU
An Overview of Java: Object-Oriented Programming (Two Paradigms, Abstraction, The Three OOP Principles), Using Blocks of Code, Lexical Issues (Whitespace, Identifiers, Literals, Comments, Separators, The Java Keywords).
Data Types, Variables, and Arrays: The Primitive Types (Integers, Floating-Point Types, Characters, Booleans), Variables, Type Conversion and Casting, Automatic Type Promotion in Expressions, Arrays, Introducing Type Inference with Local Variables.
Operators: Arithmetic Operators, Relational Operators, Boolean Logical Operators, The Assignment Operator, The ? Operator, Operator Precedence, Using Parentheses.
Control Statements: Java’s Selection Statements (if, The Traditional switch), Iteration Statements (while, do-while, for, The For-Each Version of the for Loop, Local Variable Type Inference in a for Loop, Nested Loops), Jump Statements (Using break, Using continue, return).
An Overview of Java; Data Types, Variables and Arrays; Operators; Control Statements.
Introducing Classes; Methods and Classes.
Inheritance; Interfaces.
Packages; Exceptions.
Multithreaded Programming; Enumerations, Type Wrappers and Autoboxing.
Textbook
Java: The Complete Reference, Twelfth Edition, by Herbert Schildt, November 2021, McGraw-Hill, ISBN: 9781260463422
References:
Programming with Java, 6th Edition, by E Balagurusamy, Mar-2019, McGraw Hill Education, ISBN: 9789353162337
Thinking in Java, Fourth Edition, by Bruce Eckel, Prentice Hall, 2006 (https://sd.blackball.lv/library/thinking_in_java_4th_edition.pdf)
OSV - Unit - 7 - I/O Management & Disk scheduling

I/O Devices, Organization of I/O functions, Operating System Design issues, I/O
Buffering, Disk Scheduling (FCFS, SCAN, C-SCAN, SSTF), RAID, Disk
Cache
Quran with Tajwid Surah 21 ﴾القرآن سورۃ الأنبياء﴿ Al-Anbiya' 🙪 PDF

Quran with Tajwid Surah 21 ﴾القرآن سورۃ الأنبياء﴿ Al-Anbiya' 🙪 PDFCaller To Islam / الداعية الإسلامي
LIST OF SURAHS ► https://plus.google.com/+CallertoislamTk-site/posts/eF8NukHeGDBData Types, Variables, and Arrays in JAVA

Lecture Notes
Module-1, Chapter-2
Data Types, Variables, and Arrays
Programme: B E (CSE)
Semester: 3
Course Code: BCS306A
Course Instructor: Demian Antony Dmello
2022 Scheme of VTU
An Overview of Java: Object-Oriented Programming (Two Paradigms, Abstraction, The Three OOP Principles), Using Blocks of Code, Lexical Issues (Whitespace, Identifiers, Literals, Comments, Separators, The Java Keywords).
Data Types, Variables, and Arrays: The Primitive Types (Integers, Floating-Point Types, Characters, Booleans), Variables, Type Conversion and Casting, Automatic Type Promotion in Expressions, Arrays, Introducing Type Inference with Local Variables.
Operators: Arithmetic Operators, Relational Operators, Boolean Logical Operators, The Assignment Operator, The ? Operator, Operator Precedence, Using Parentheses.
Control Statements: Java’s Selection Statements (if, The Traditional switch), Iteration Statements (while, do-while, for, The For-Each Version of the for Loop, Local Variable Type Inference in a for Loop, Nested Loops), Jump Statements (Using break, Using continue, return).
An Overview of Java; Data Types, Variables and Arrays; Operators; Control Statements.
Introducing Classes; Methods and Classes.
Inheritance; Interfaces.
Packages; Exceptions.
Multithreaded Programming; Enumerations, Type Wrappers and Autoboxing.
Cuatro Jinetes - Serie Alberto de Chick Publications. 5ta. Parte.

De la serie: Alberto".
Quinta Parte.
Ministro Eliezer Lara Montoya.
www.eslahoradelaverdad.com.mx
www.facebook.com/zerlaramontoya
Recommended
Object Oriented Programming with JAVA

Lecture Notes
Module-1, Chapter-1
An Overview of Java
Programme: B E (CSE)
Semester: 3
Course Code: BCS306A
Course Instructor: Demian Antony Dmello
2022 Scheme of VTU
An Overview of Java: Object-Oriented Programming (Two Paradigms, Abstraction, The Three OOP Principles), Using Blocks of Code, Lexical Issues (Whitespace, Identifiers, Literals, Comments, Separators, The Java Keywords).
Data Types, Variables, and Arrays: The Primitive Types (Integers, Floating-Point Types, Characters, Booleans), Variables, Type Conversion and Casting, Automatic Type Promotion in Expressions, Arrays, Introducing Type Inference with Local Variables.
Operators: Arithmetic Operators, Relational Operators, Boolean Logical Operators, The Assignment Operator, The ? Operator, Operator Precedence, Using Parentheses.
Control Statements: Java’s Selection Statements (if, The Traditional switch), Iteration Statements (while, do-while, for, The For-Each Version of the for Loop, Local Variable Type Inference in a for Loop, Nested Loops), Jump Statements (Using break, Using continue, return).
An Overview of Java; Data Types, Variables and Arrays; Operators; Control Statements.
Introducing Classes; Methods and Classes.
Inheritance; Interfaces.
Packages; Exceptions.
Multithreaded Programming; Enumerations, Type Wrappers and Autoboxing.
Textbook
Java: The Complete Reference, Twelfth Edition, by Herbert Schildt, November 2021, McGraw-Hill, ISBN: 9781260463422
References:
Programming with Java, 6th Edition, by E Balagurusamy, Mar-2019, McGraw Hill Education, ISBN: 9789353162337
Thinking in Java, Fourth Edition, by Bruce Eckel, Prentice Hall, 2006 (https://sd.blackball.lv/library/thinking_in_java_4th_edition.pdf)
OSV - Unit - 7 - I/O Management & Disk scheduling

I/O Devices, Organization of I/O functions, Operating System Design issues, I/O
Buffering, Disk Scheduling (FCFS, SCAN, C-SCAN, SSTF), RAID, Disk
Cache
Quran with Tajwid Surah 21 ﴾القرآن سورۃ الأنبياء﴿ Al-Anbiya' 🙪 PDF

Quran with Tajwid Surah 21 ﴾القرآن سورۃ الأنبياء﴿ Al-Anbiya' 🙪 PDFCaller To Islam / الداعية الإسلامي
LIST OF SURAHS ► https://plus.google.com/+CallertoislamTk-site/posts/eF8NukHeGDBData Types, Variables, and Arrays in JAVA

Lecture Notes
Module-1, Chapter-2
Data Types, Variables, and Arrays
Programme: B E (CSE)
Semester: 3
Course Code: BCS306A
Course Instructor: Demian Antony Dmello
2022 Scheme of VTU
An Overview of Java: Object-Oriented Programming (Two Paradigms, Abstraction, The Three OOP Principles), Using Blocks of Code, Lexical Issues (Whitespace, Identifiers, Literals, Comments, Separators, The Java Keywords).
Data Types, Variables, and Arrays: The Primitive Types (Integers, Floating-Point Types, Characters, Booleans), Variables, Type Conversion and Casting, Automatic Type Promotion in Expressions, Arrays, Introducing Type Inference with Local Variables.
Operators: Arithmetic Operators, Relational Operators, Boolean Logical Operators, The Assignment Operator, The ? Operator, Operator Precedence, Using Parentheses.
Control Statements: Java’s Selection Statements (if, The Traditional switch), Iteration Statements (while, do-while, for, The For-Each Version of the for Loop, Local Variable Type Inference in a for Loop, Nested Loops), Jump Statements (Using break, Using continue, return).
An Overview of Java; Data Types, Variables and Arrays; Operators; Control Statements.
Introducing Classes; Methods and Classes.
Inheritance; Interfaces.
Packages; Exceptions.
Multithreaded Programming; Enumerations, Type Wrappers and Autoboxing.
Cuatro Jinetes - Serie Alberto de Chick Publications. 5ta. Parte.

De la serie: Alberto".
Quinta Parte.
Ministro Eliezer Lara Montoya.
www.eslahoradelaverdad.com.mx
www.facebook.com/zerlaramontoya
Chapter 03 Basic Computer Components ~ Urdu Guide

This is an short essential guide about basic components of a Computer system in Urdu.
For more guides in Urdu:
More free computer guides at:
http://titanscomputer.blogspot.com
LSE Finance Certificate

LSE Summer School Program, Finance class of 2018. Achieved ‘A’ grade in Finance, equivalent to top 10% in a class of 264 students.
DBMS Unit - 5 - Query processing and optimization

Evaluation of relational algebra expressions, Query equivalence, Join strategies, Query optimization algorithms.
Chapter 01 Introduction to Computer - Urdu Guide by: TitansComputer

This is a beginner guide to computer in Urdu. It will help people who are looking for a newbie guide to computer in Urdu. First steps to know for a newbie to computer.
For more free guides visit: http://titanscomputer.blogspot.com
Chapter 10 Using Windows Control Panel ~ Urdu Guide

Control Panel is the place where you configure how your computer hardware behave, which programs to remain or delete from windows and configure for PC security from outsiders/hackers. Some of the main thing you do in Control panel is adding new devices, install their drivers or even update them, configuring your PC peripheral devices such mouse, keyboard, monitor/LCD (resolutions, refresh frequency, colors), and printers, etc.
In general, you can configure you computer hardware, security, install/uninstall programs and much more.
For more free guides visit: http://titanscomputer.blogspot.com
More Related Content
What's hot
Chapter 03 Basic Computer Components ~ Urdu Guide

This is an short essential guide about basic components of a Computer system in Urdu.
For more guides in Urdu:
More free computer guides at:
http://titanscomputer.blogspot.com
LSE Finance Certificate

LSE Summer School Program, Finance class of 2018. Achieved ‘A’ grade in Finance, equivalent to top 10% in a class of 264 students.
DBMS Unit - 5 - Query processing and optimization

Evaluation of relational algebra expressions, Query equivalence, Join strategies, Query optimization algorithms.
Chapter 01 Introduction to Computer - Urdu Guide by: TitansComputer

This is a beginner guide to computer in Urdu. It will help people who are looking for a newbie guide to computer in Urdu. First steps to know for a newbie to computer.
For more free guides visit: http://titanscomputer.blogspot.com
Chapter 10 Using Windows Control Panel ~ Urdu Guide

Control Panel is the place where you configure how your computer hardware behave, which programs to remain or delete from windows and configure for PC security from outsiders/hackers. Some of the main thing you do in Control panel is adding new devices, install their drivers or even update them, configuring your PC peripheral devices such mouse, keyboard, monitor/LCD (resolutions, refresh frequency, colors), and printers, etc.
In general, you can configure you computer hardware, security, install/uninstall programs and much more.
For more free guides visit: http://titanscomputer.blogspot.com
What's hot (20)
Python Programming ADP VTU CSE 18CS55 Module 1 Chapter 3

Python Programming ADP VTU CSE 18CS55 Module 1 Chapter 3
Python Programming ADP VTU CSE 18CS55 Module 2 Chapter 4

Python Programming ADP VTU CSE 18CS55 Module 2 Chapter 4
Chapter 01 Introduction to Computer - Urdu Guide by: TitansComputer

Chapter 01 Introduction to Computer - Urdu Guide by: TitansComputer
Chapter 10 Using Windows Control Panel ~ Urdu Guide

Chapter 10 Using Windows Control Panel ~ Urdu Guide
Viewers also liked
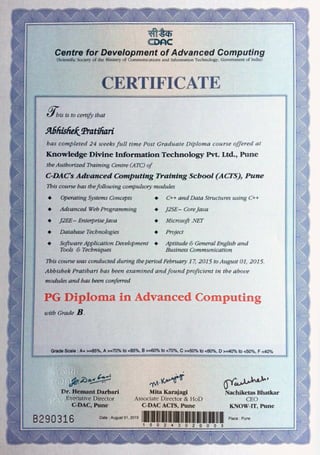
Oops Paper

this is good question set for CCAT exam and alos for CCEE
for more details please visit
http://acts.cdac.in
http://cdacguru.wordpress.com
http://fb.com/cdacguru
Capitulo 1 leer y escribir en la escuela- Delia Lerner

Reseña capitulo 1 leer y escribir en la escuela - Delia Lerner
Viewers also liked (9)
PSY 302 WEEK 2 ASSIGNMENT MOTIVATIONAL THEORIES AND FACTORS

PSY 302 WEEK 2 ASSIGNMENT MOTIVATIONAL THEORIES AND FACTORS
Capitulo 1 leer y escribir en la escuela- Delia Lerner

Capitulo 1 leer y escribir en la escuela- Delia Lerner
Recently uploaded
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Join Maher Hanafi, VP of Engineering at Betterworks, in this new session where he'll share a practical framework to transform Gen AI prototypes into impactful products! He'll delve into the complexities of data collection and management, model selection and optimization, and ensuring security, scalability, and responsible use.
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
Recently uploaded (20)
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Generative AI Deep Dive: Advancing from Proof of Concept to Production
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
UiPath Test Automation using UiPath Test Suite series, part 5

UiPath Test Automation using UiPath Test Suite series, part 5
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...