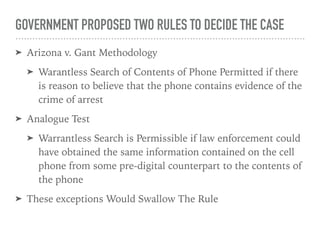
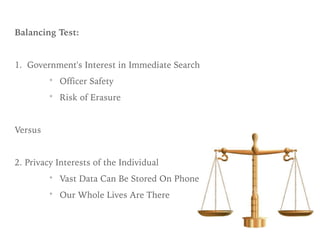
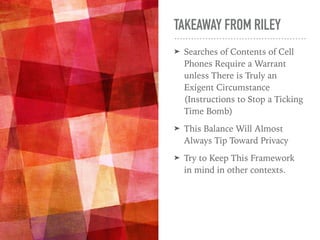
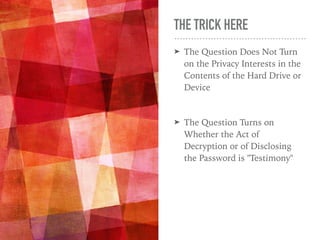
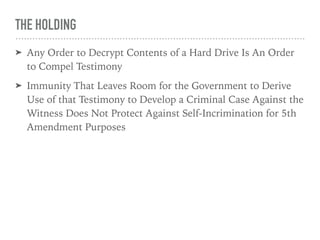
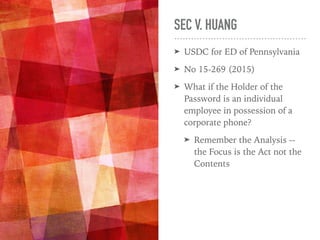
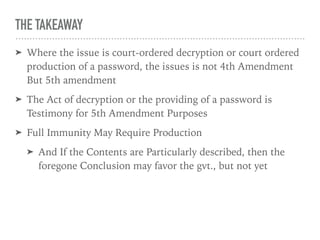
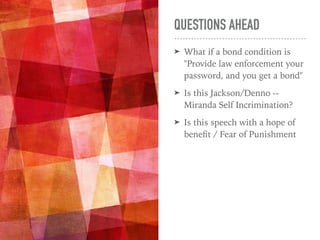
The document discusses the interaction between technology and criminal law, focusing on issues related to search and seizure of cell phones under the 4th and 5th Amendments. Key cases such as Riley v. California and U.S. v. Doe highlight that warrantless searches of cell phone contents are generally prohibited, and compelled decryption of devices is considered testimony protected by the 5th Amendment. It emphasizes the importance for legal practitioners to stay informed about technology to effectively handle cases involving digital evidence.