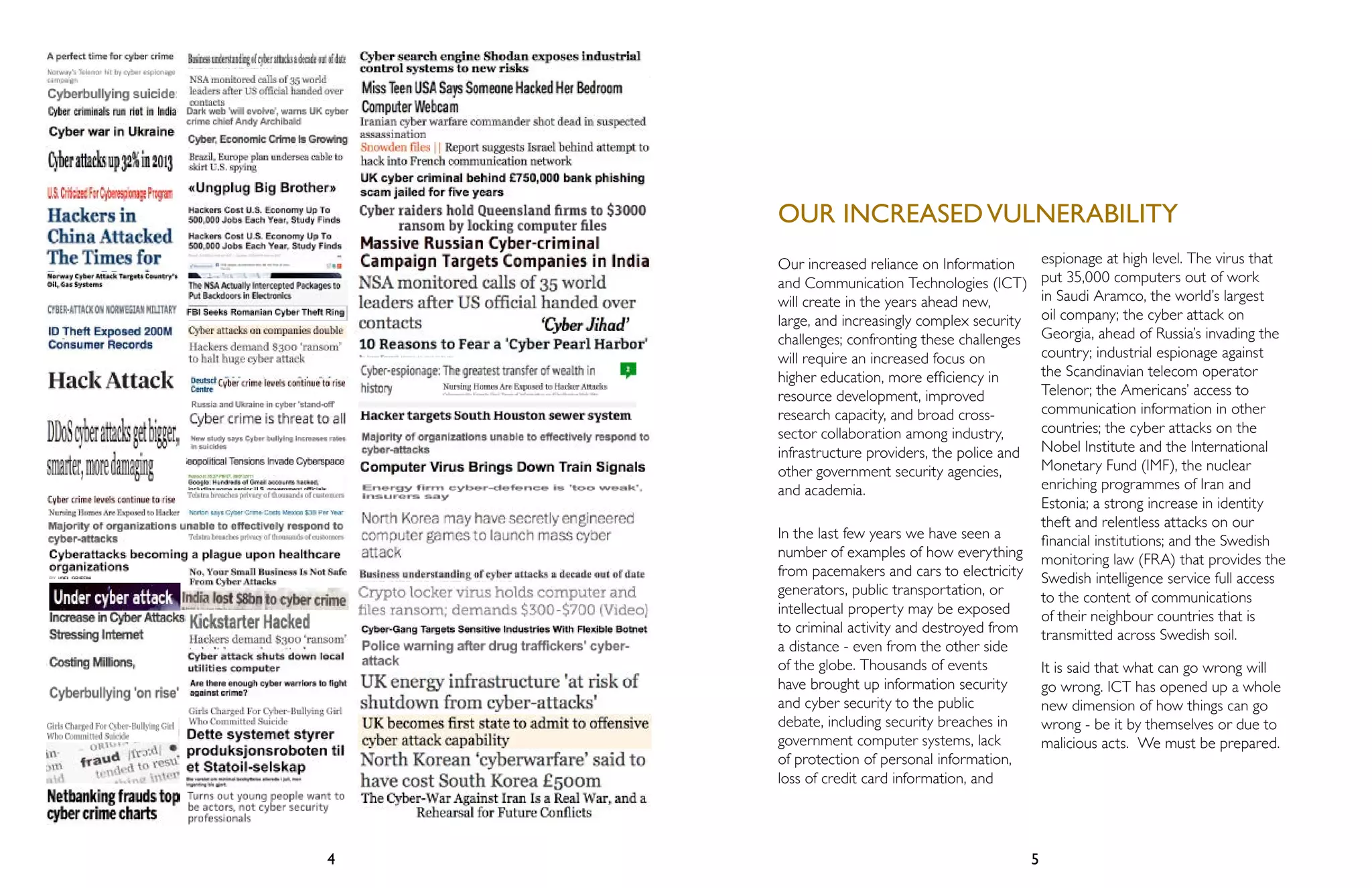
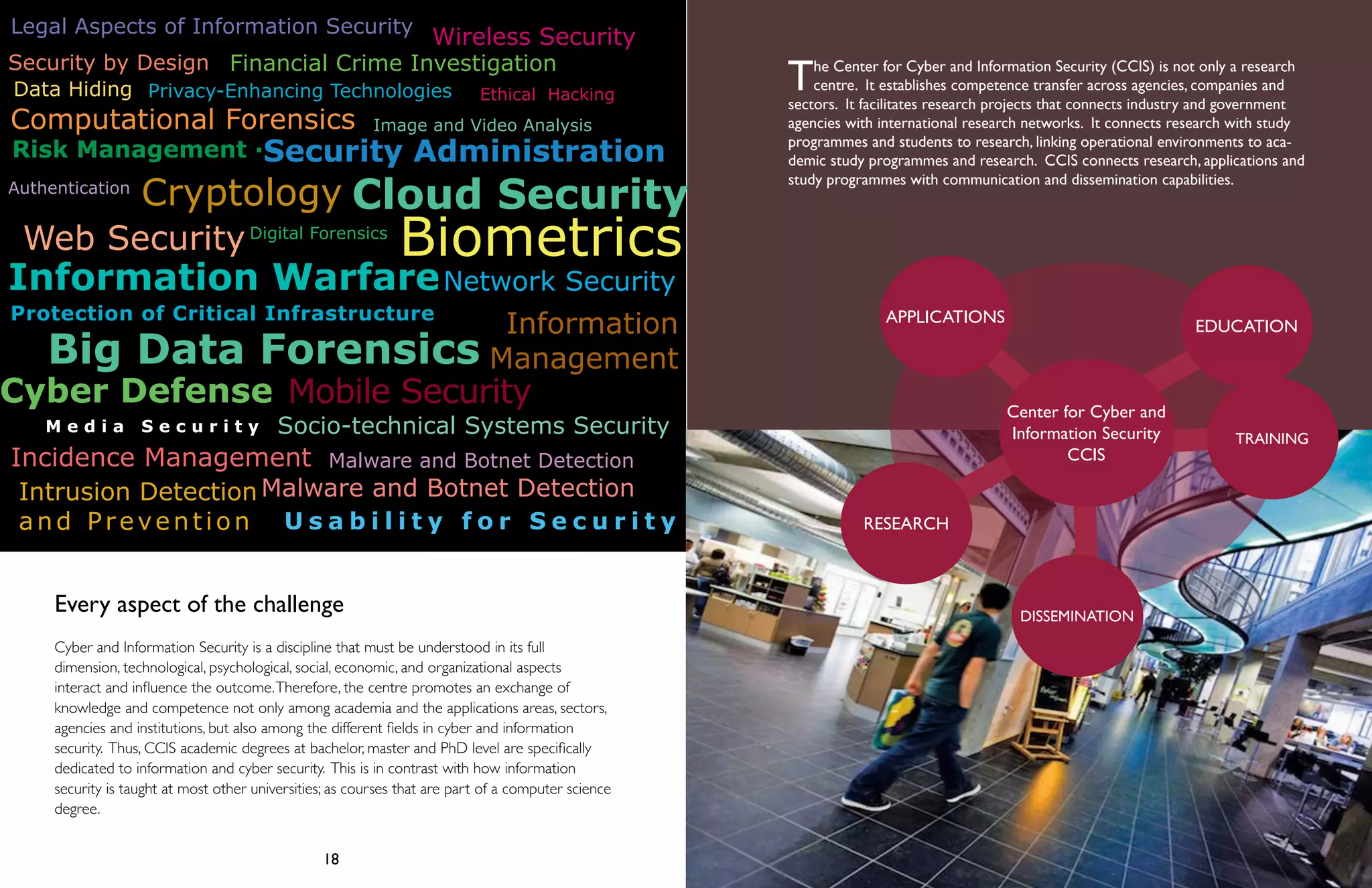
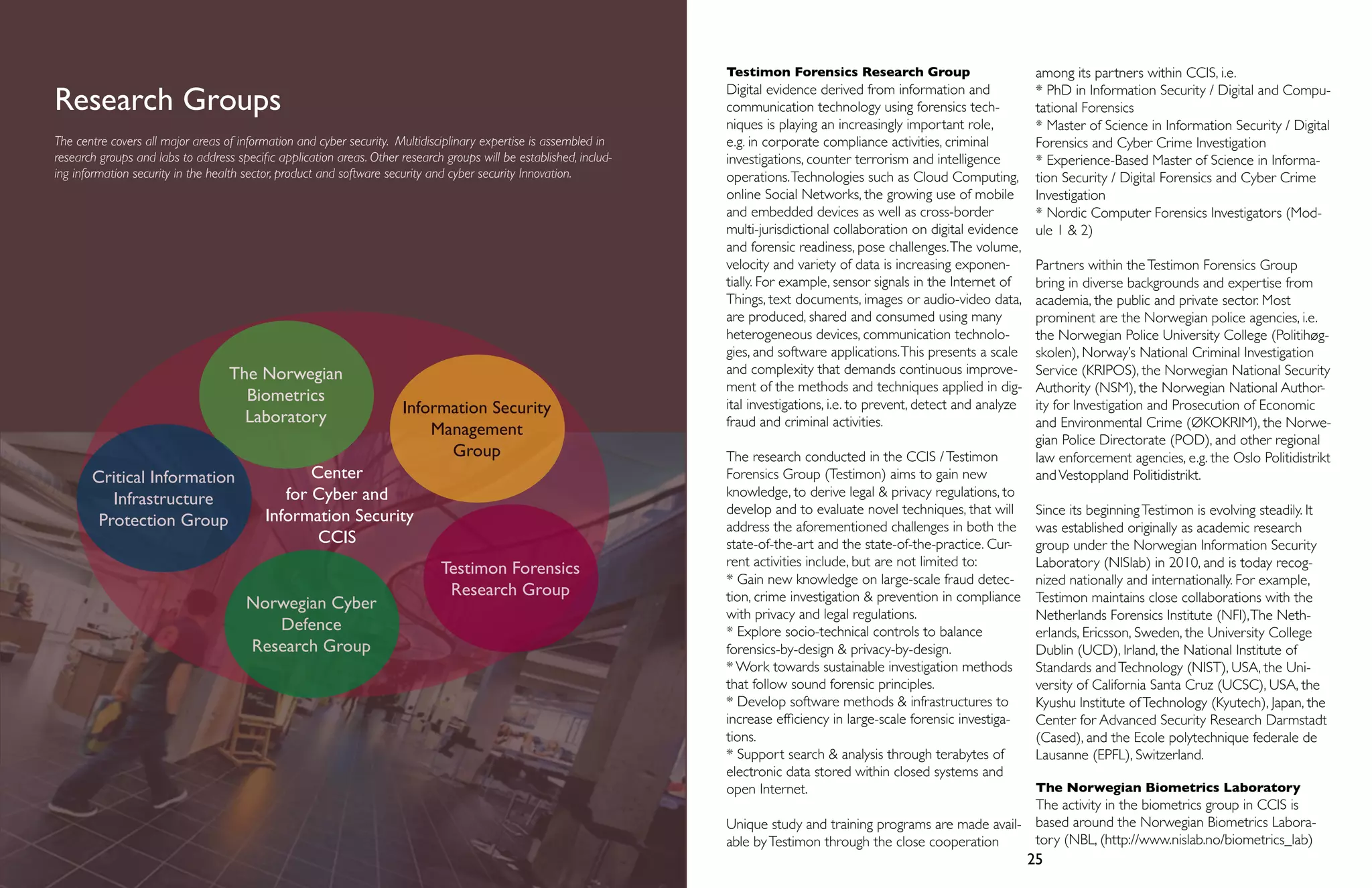
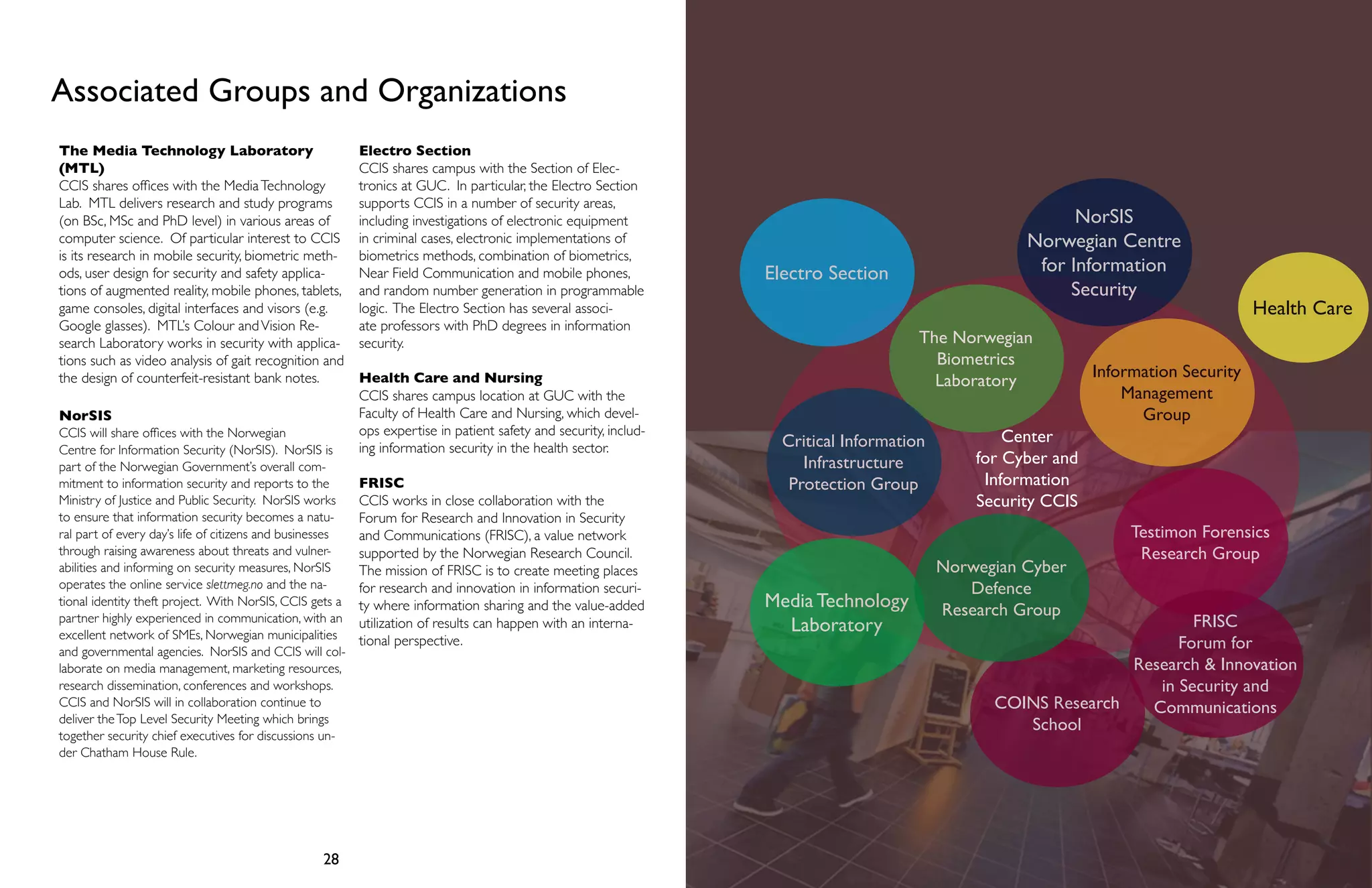
The document discusses the establishment of the Center for Cyber and Information Security (CCIS) in Norway. It notes that modern societies have become dependent on information and communication technologies, making them vulnerable to cyber threats. In response, key national cybersecurity stakeholders in Norway have partnered to create CCIS, a national center for research, training, and education in cyber and information security. CCIS aims to strengthen Norway's cybersecurity expertise and skills through research, training programs, collaboration, and developing the workforce. It will involve partnerships between universities, government agencies, and private companies.