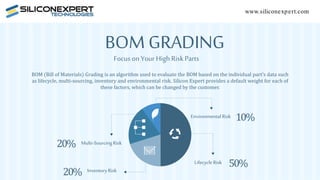
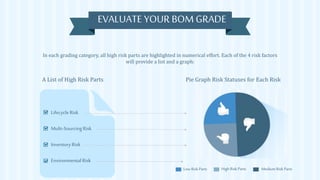
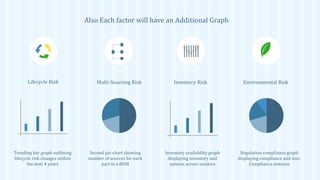
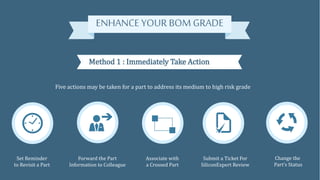
Silicon Expert offers a BOM grading algorithm to evaluate high-risk parts based on factors like lifecycle, multi-sourcing, inventory, and environmental risks, with customizable weightings. The service highlights high-risk components and provides visual data representations, such as lists and graphs, to assess risks. Additionally, it recommends actions for improving the BOM grade and offers solutions for addressing high-risk parts.