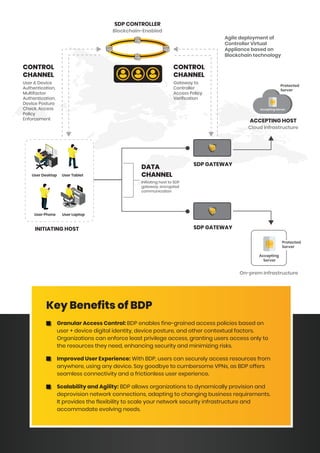
The document discusses Software Defined Perimeter (SDP) as an innovative security framework that enhances network security by overcoming traditional perimeter-based models. It highlights Block Armour's Blockchain Defined Perimeter (BDP), which integrates SDP with blockchain technology, providing granular access control and secure remote access to resources. Key benefits include improved user experience, scalability, and reduced insider threats through decentralized identity management and immutable audit trails.