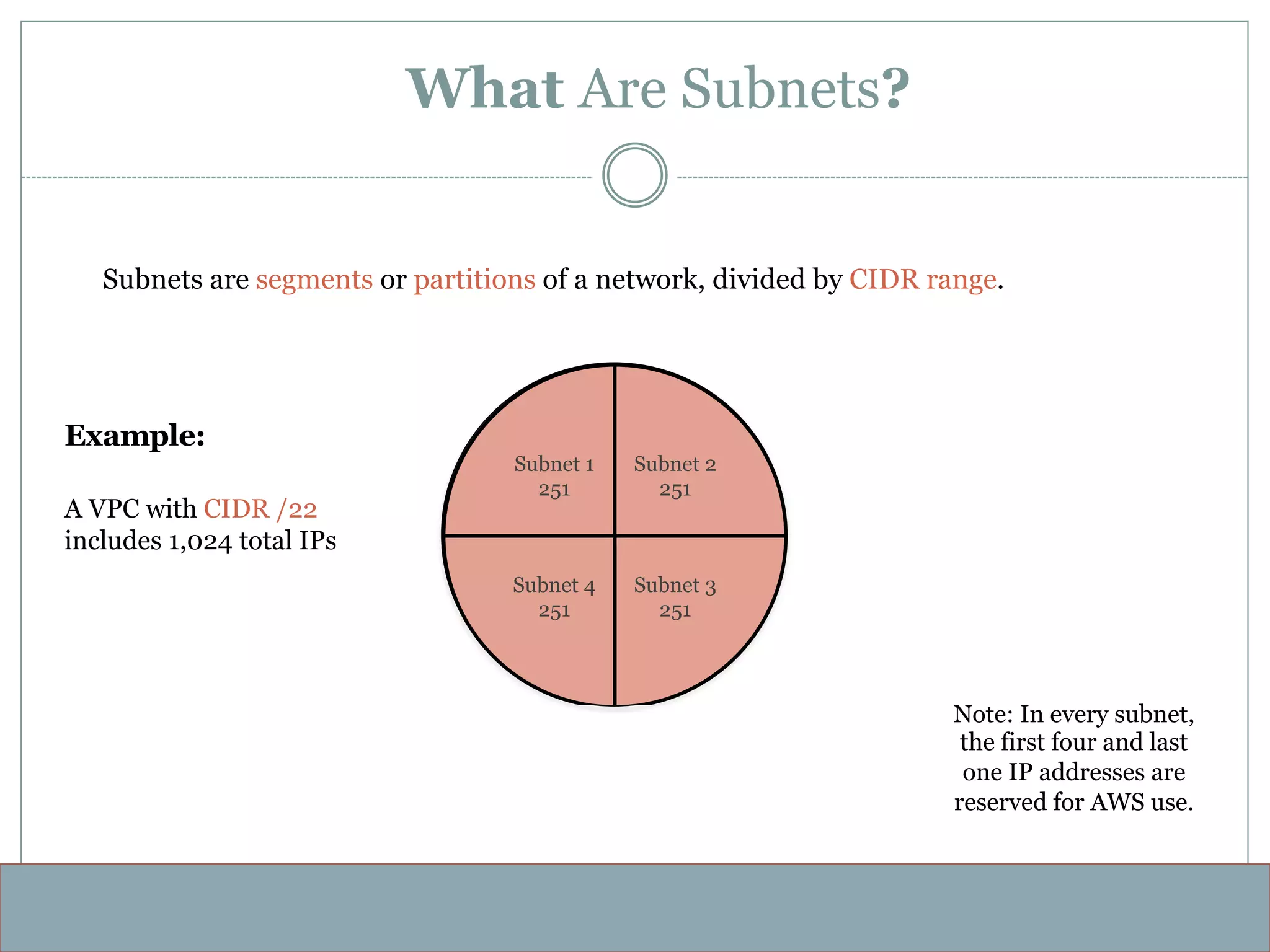
The document discusses Amazon Virtual Private Clouds (VPCs). It describes VPCs as isolated virtual networks within the AWS cloud that allow users to define their own virtual networking environments, including IP ranges, subnets, route tables and network gateways. It provides examples of how to configure public and private subnets, security groups, route tables and internet gateways to control traffic within a VPC network.