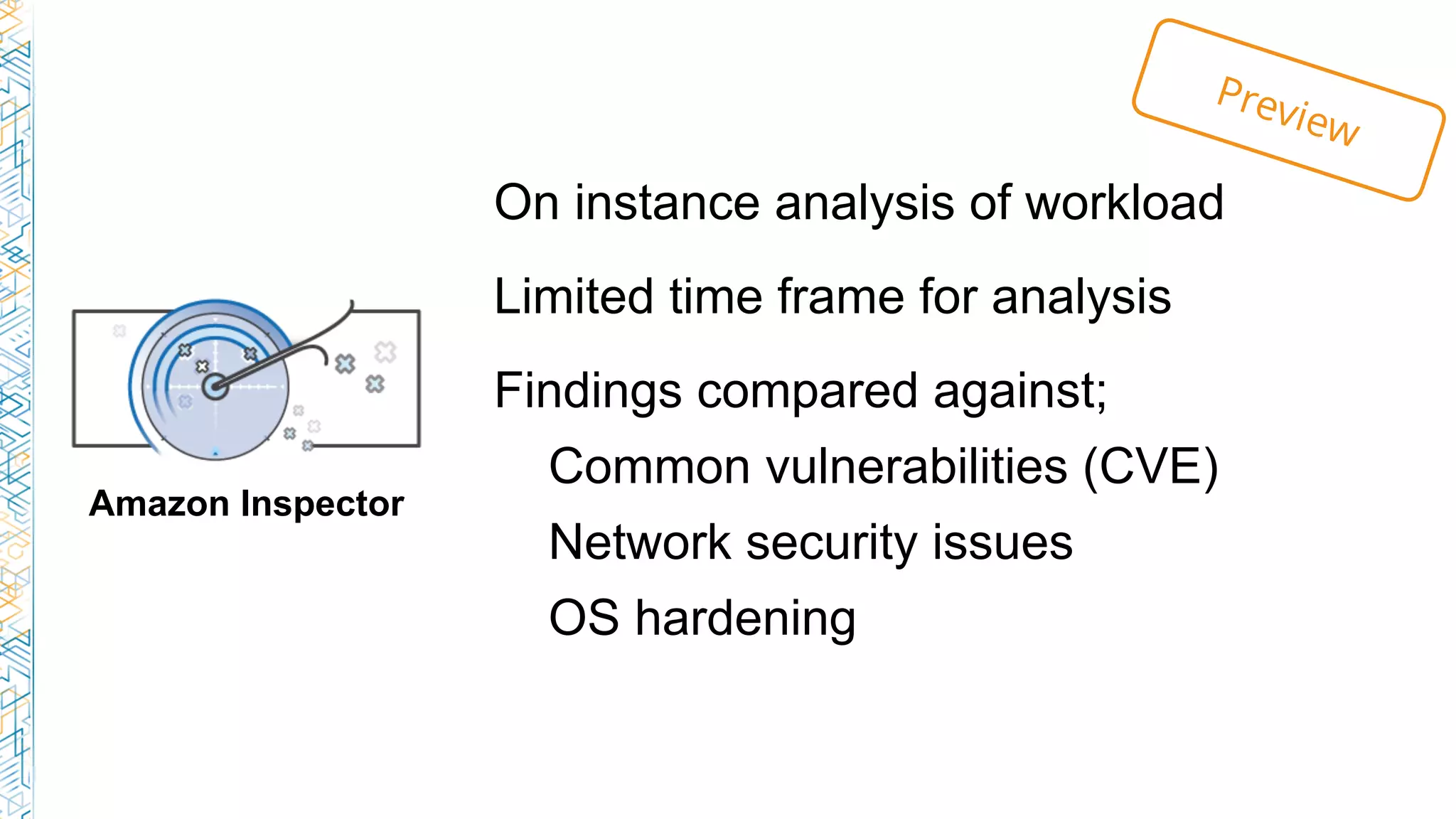
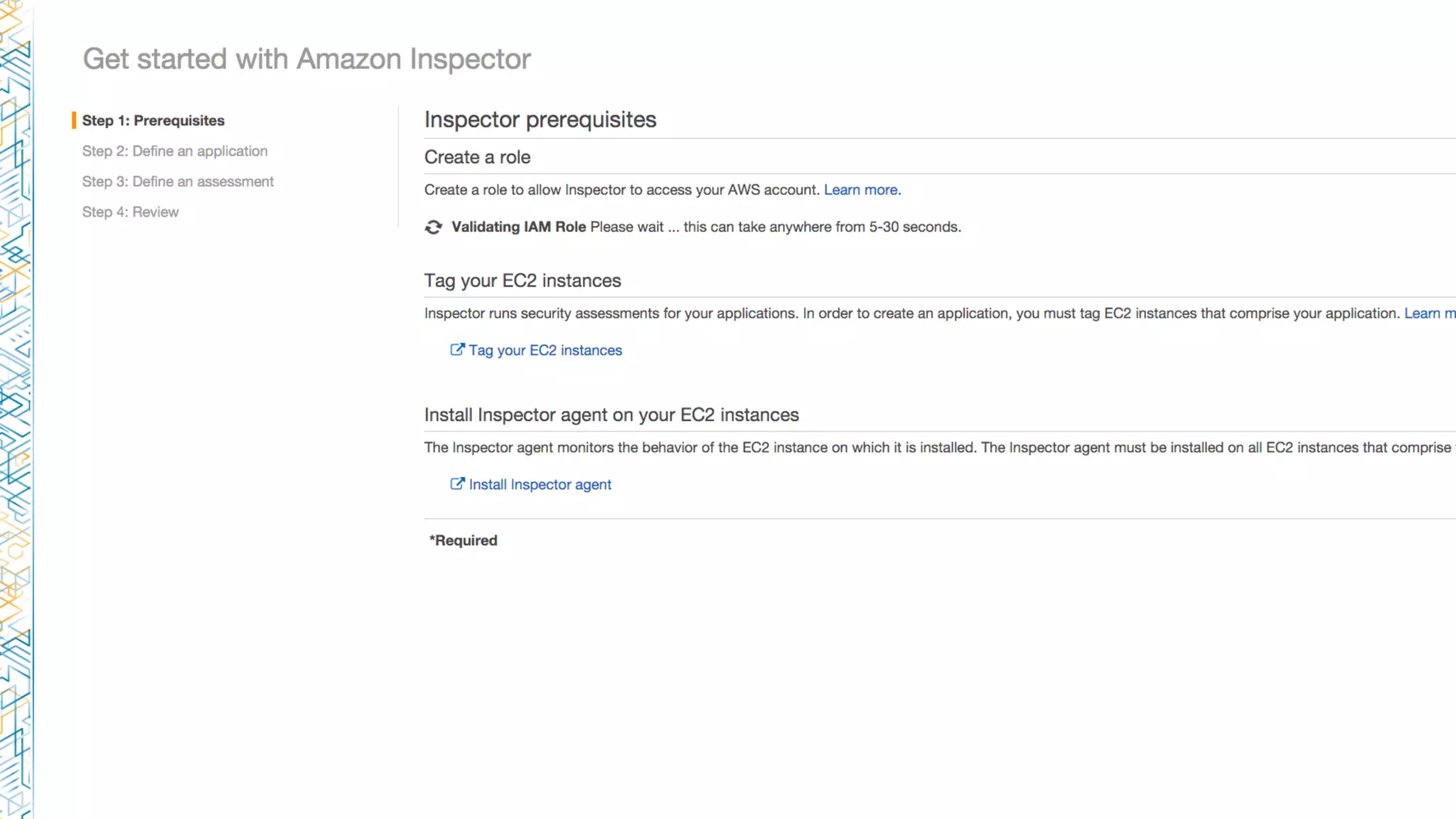
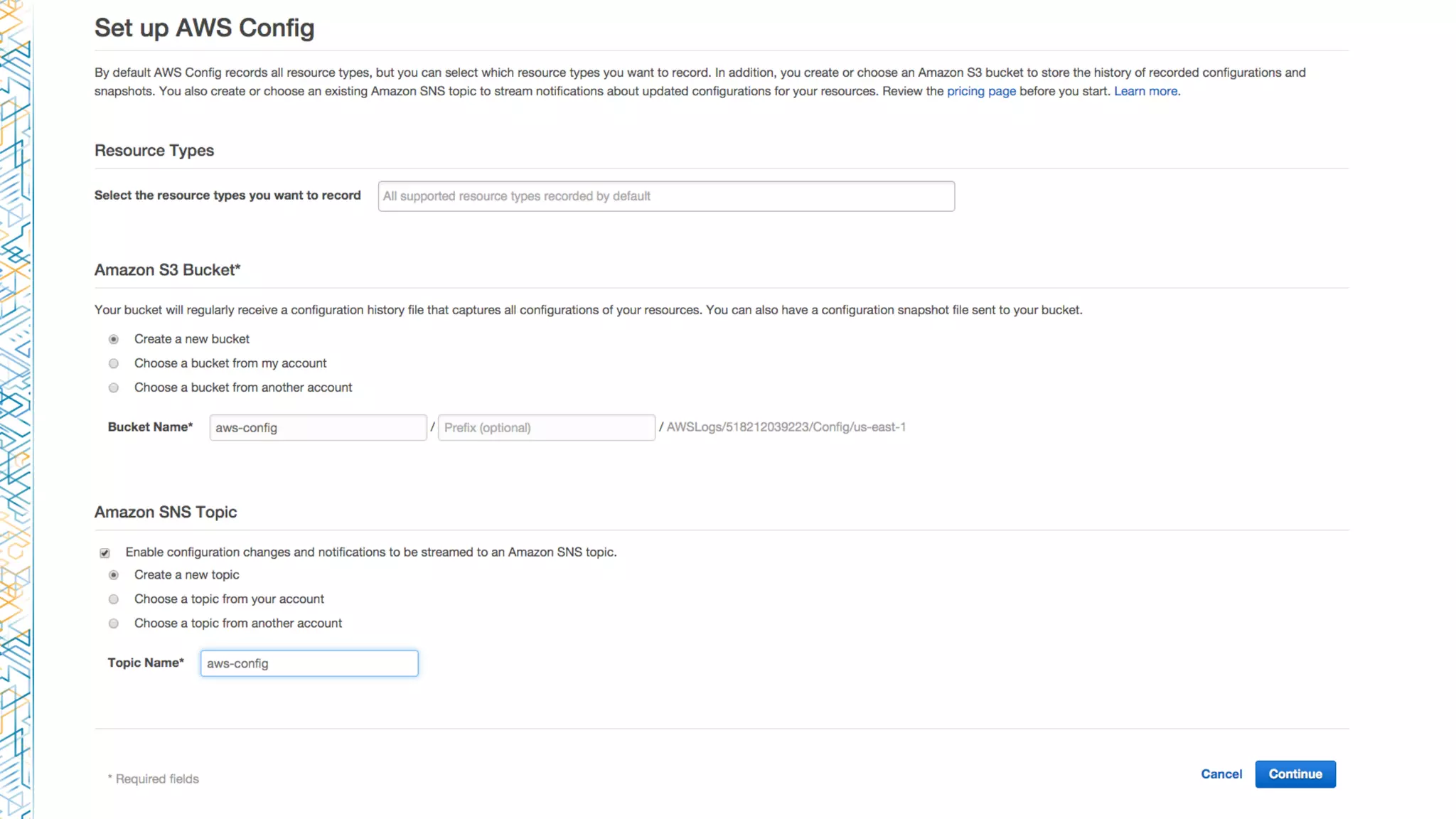
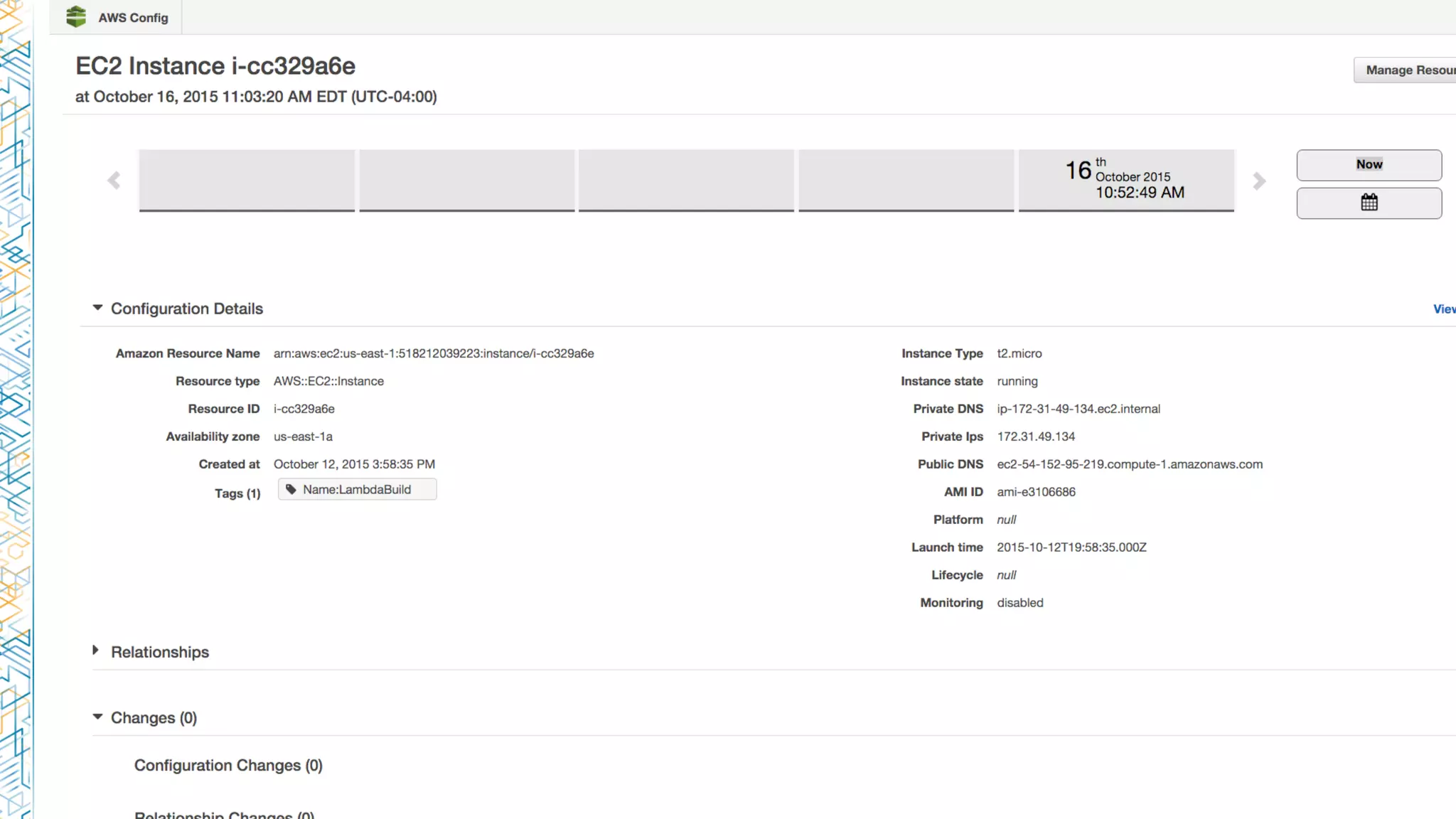
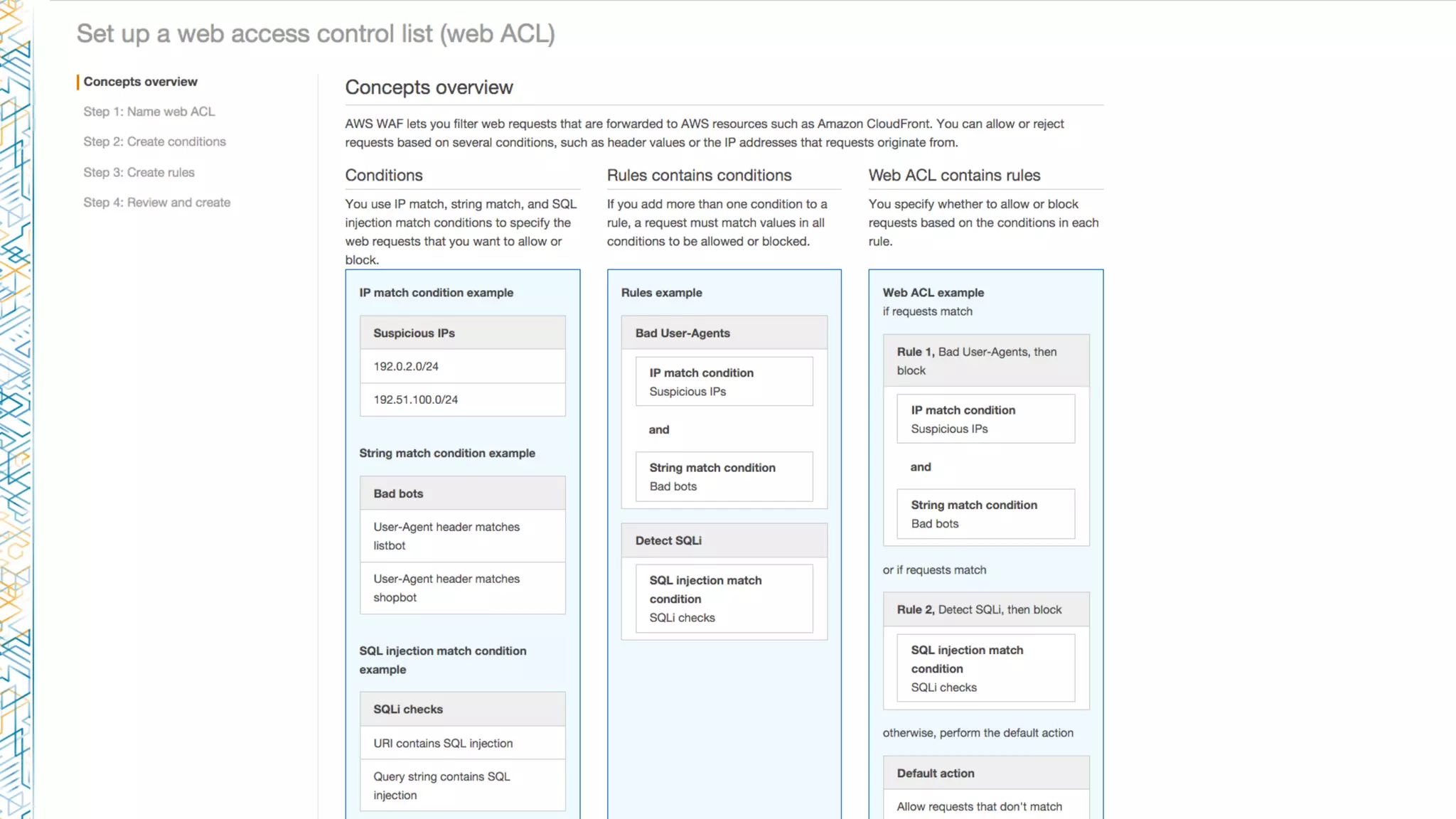
The document discusses various AWS services including security features like Amazon Inspector and AWS WAF, data services such as Amazon Elasticsearch and QuickSight, and event-driven computing with AWS Lambda and CloudWatch. It highlights the advantages of these tools for compliance reporting, data migration, and visualization. Additionally, it offers links to related resources and information on best practices.