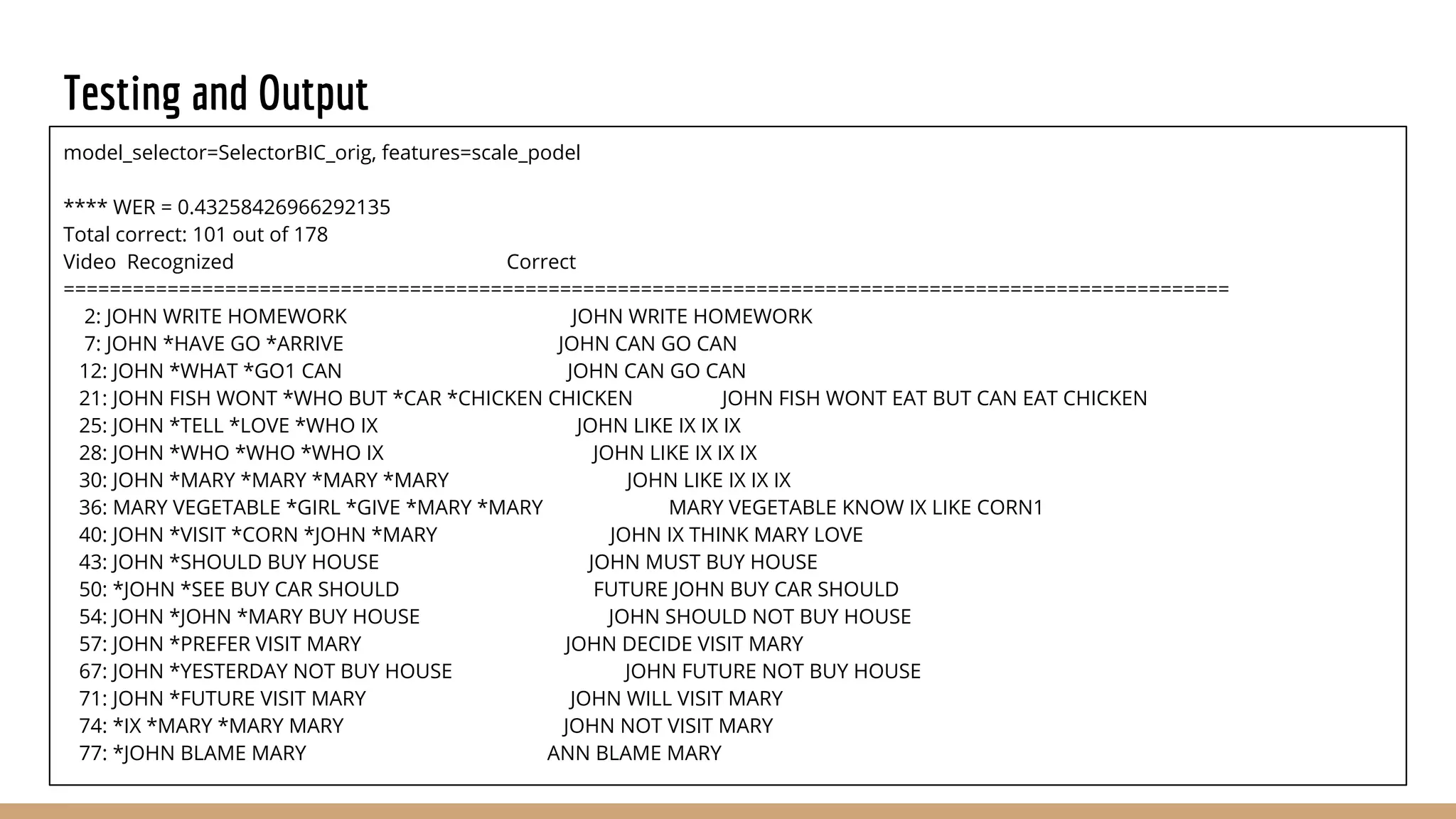
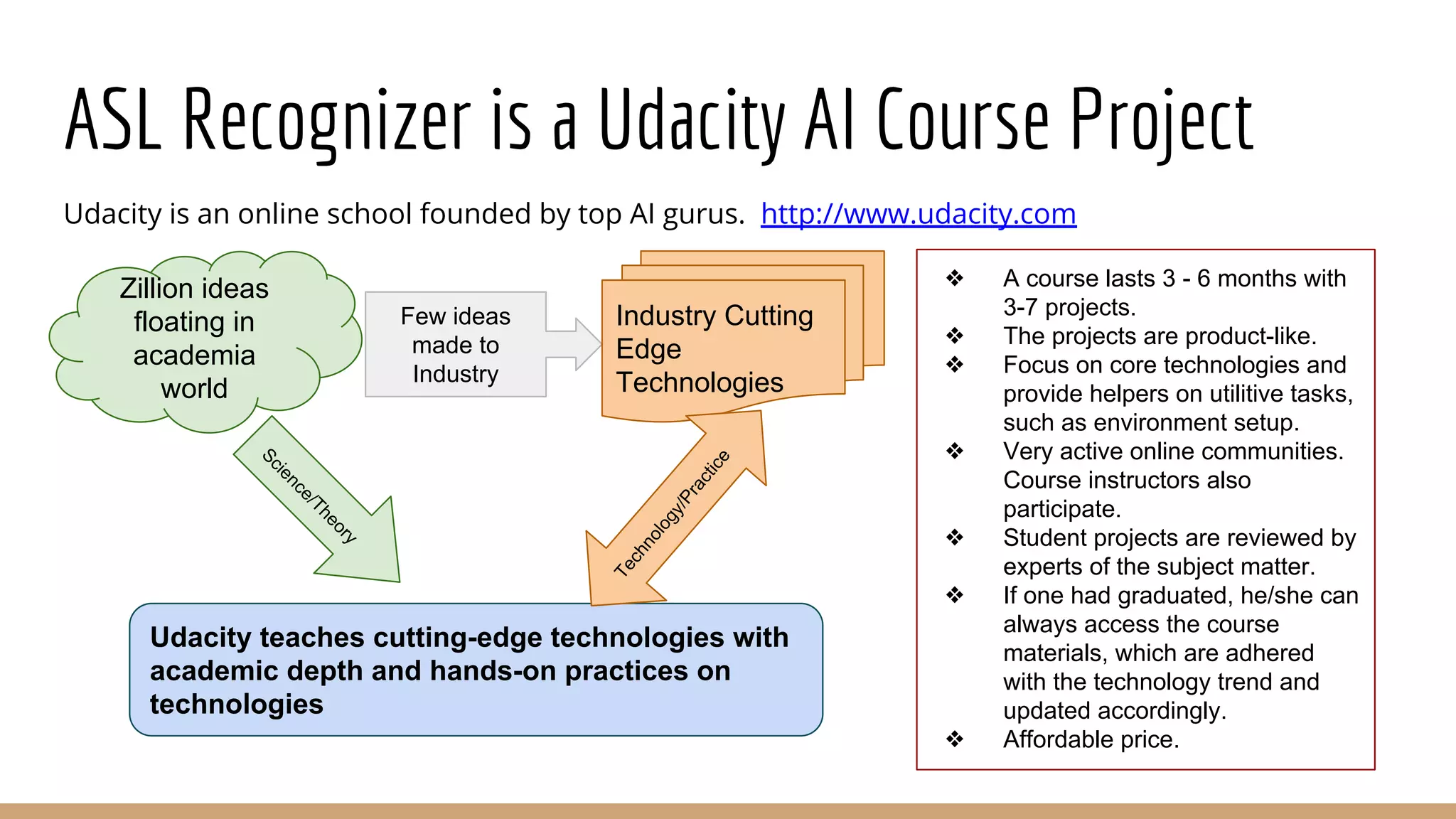
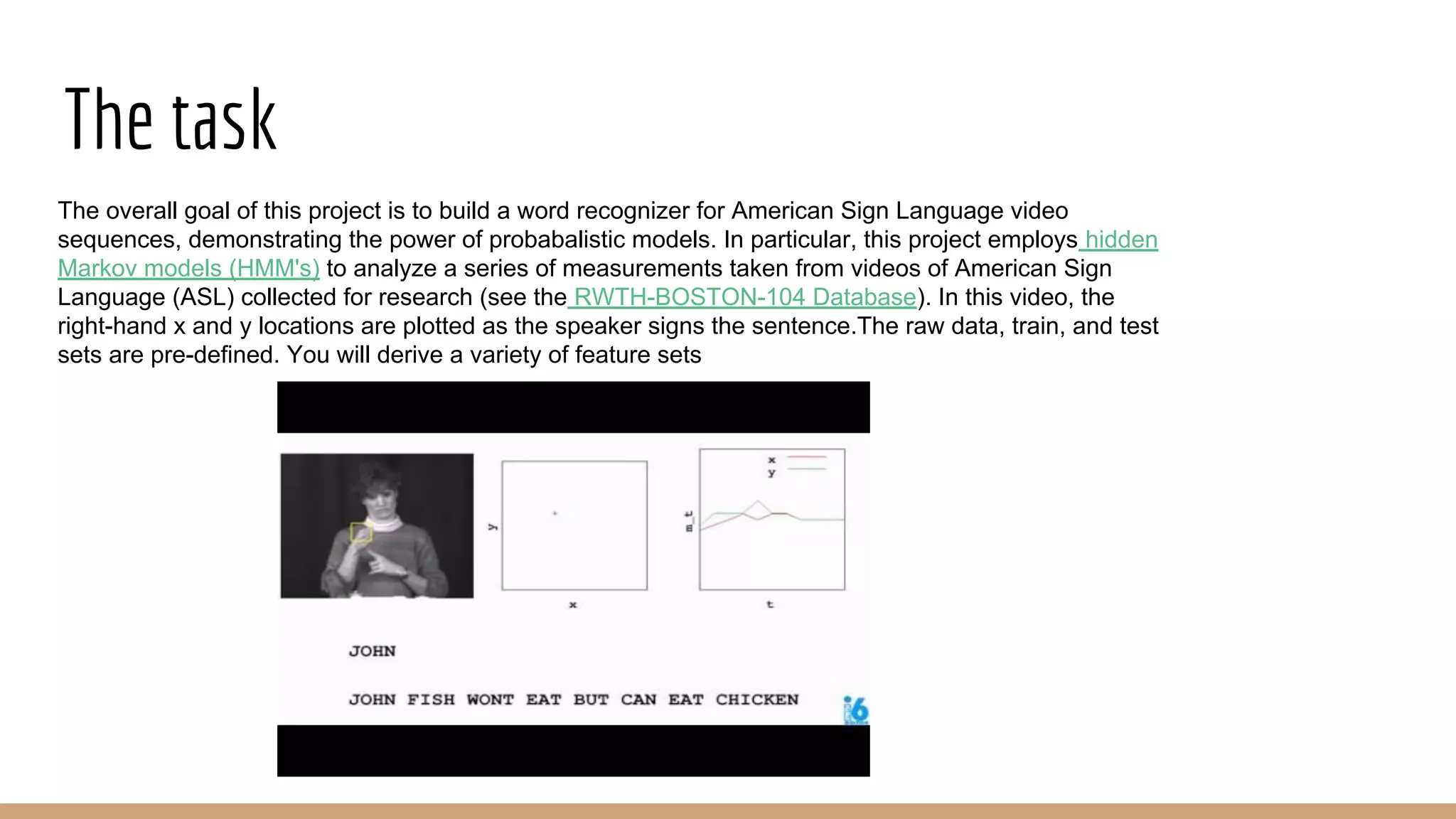
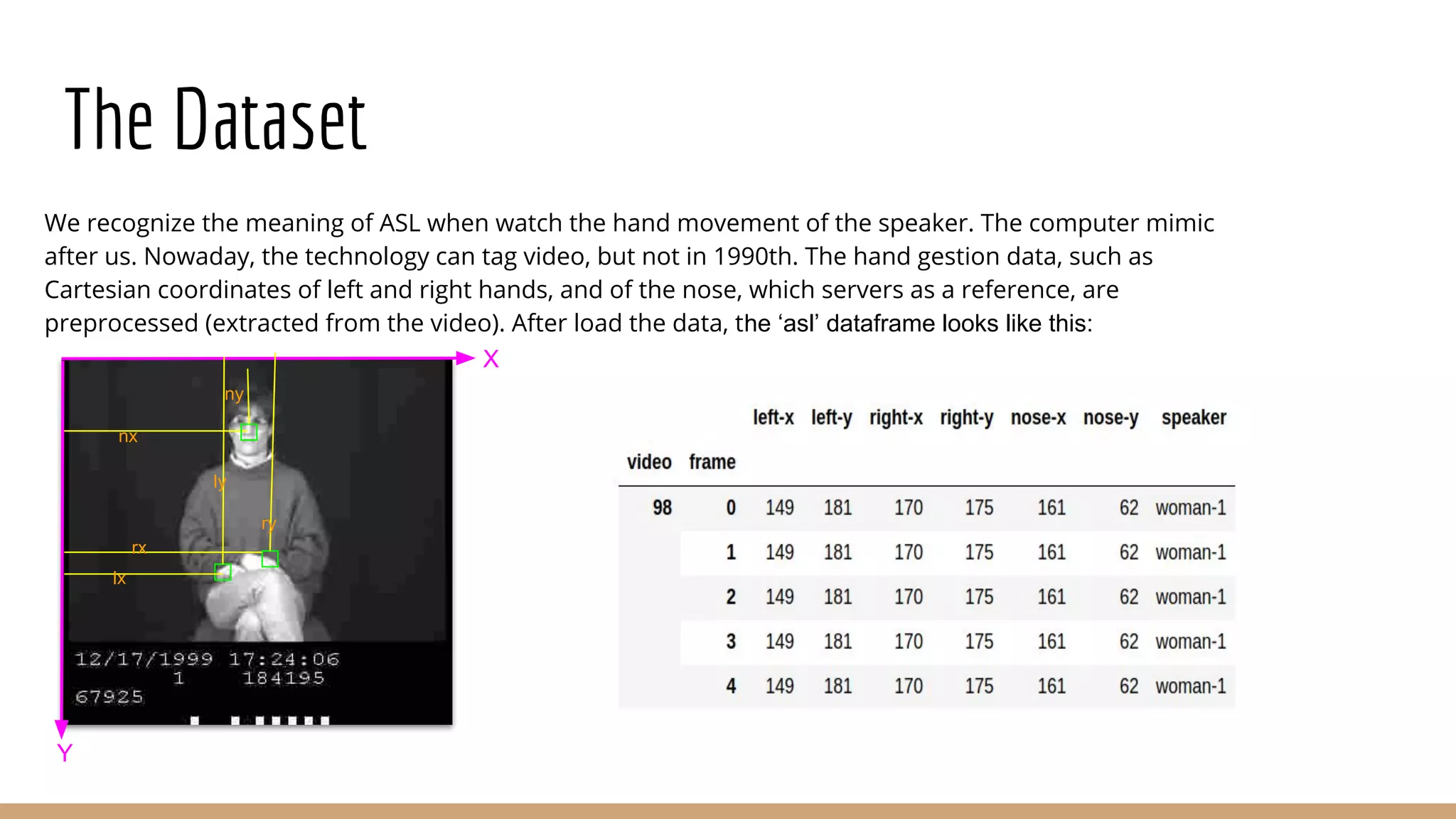
The document outlines a project for creating an American Sign Language (ASL) recognizer using hidden Markov models (HMM) to analyze video sequences. It details the structure of the data sets used for training and testing, as well as the feature extraction techniques employed to improve model accuracy. Ultimately, the model achieved a recognition rate of 43.2%, successfully recognizing 101 out of 178 words.
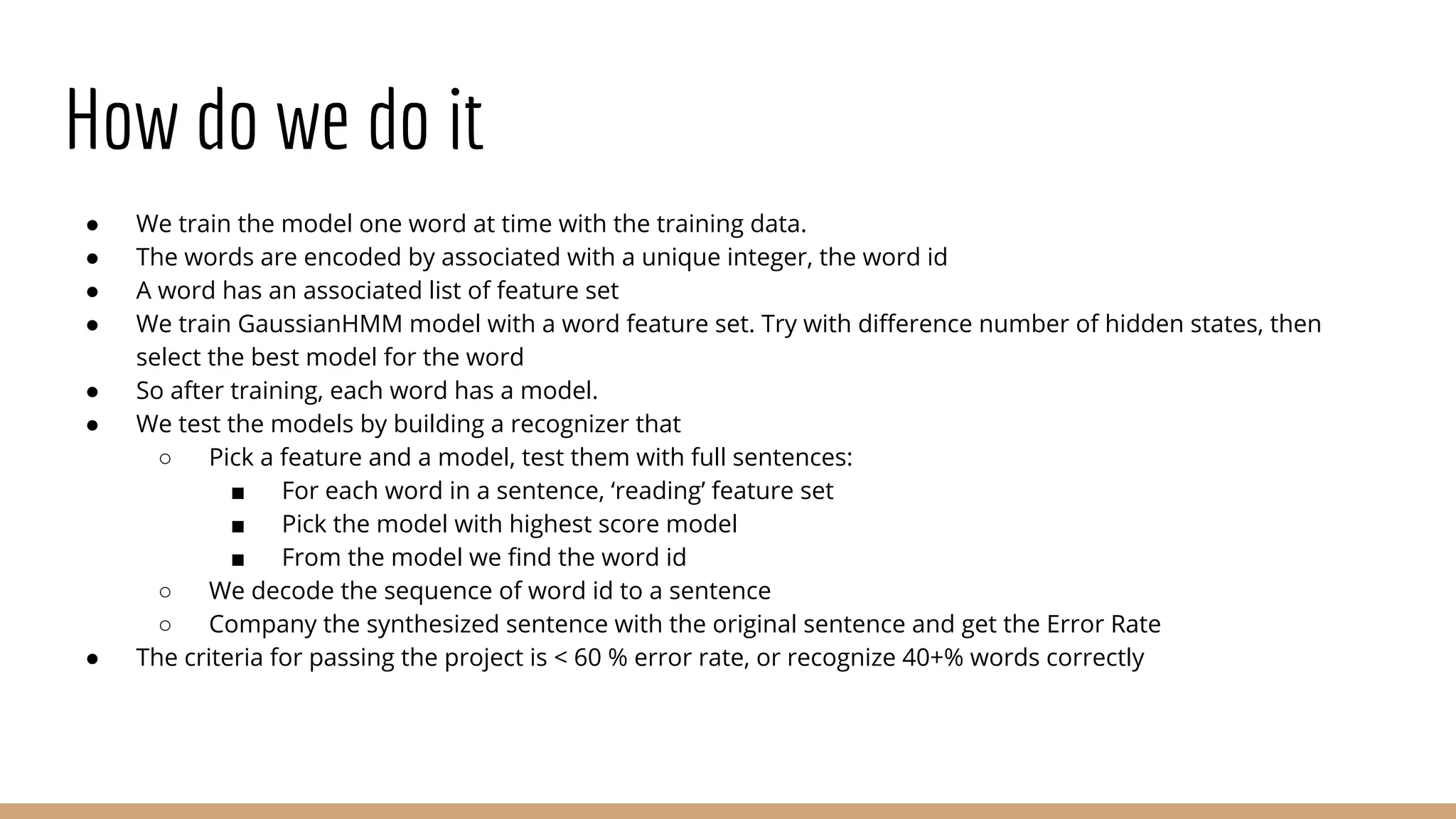
![Feature Extraction
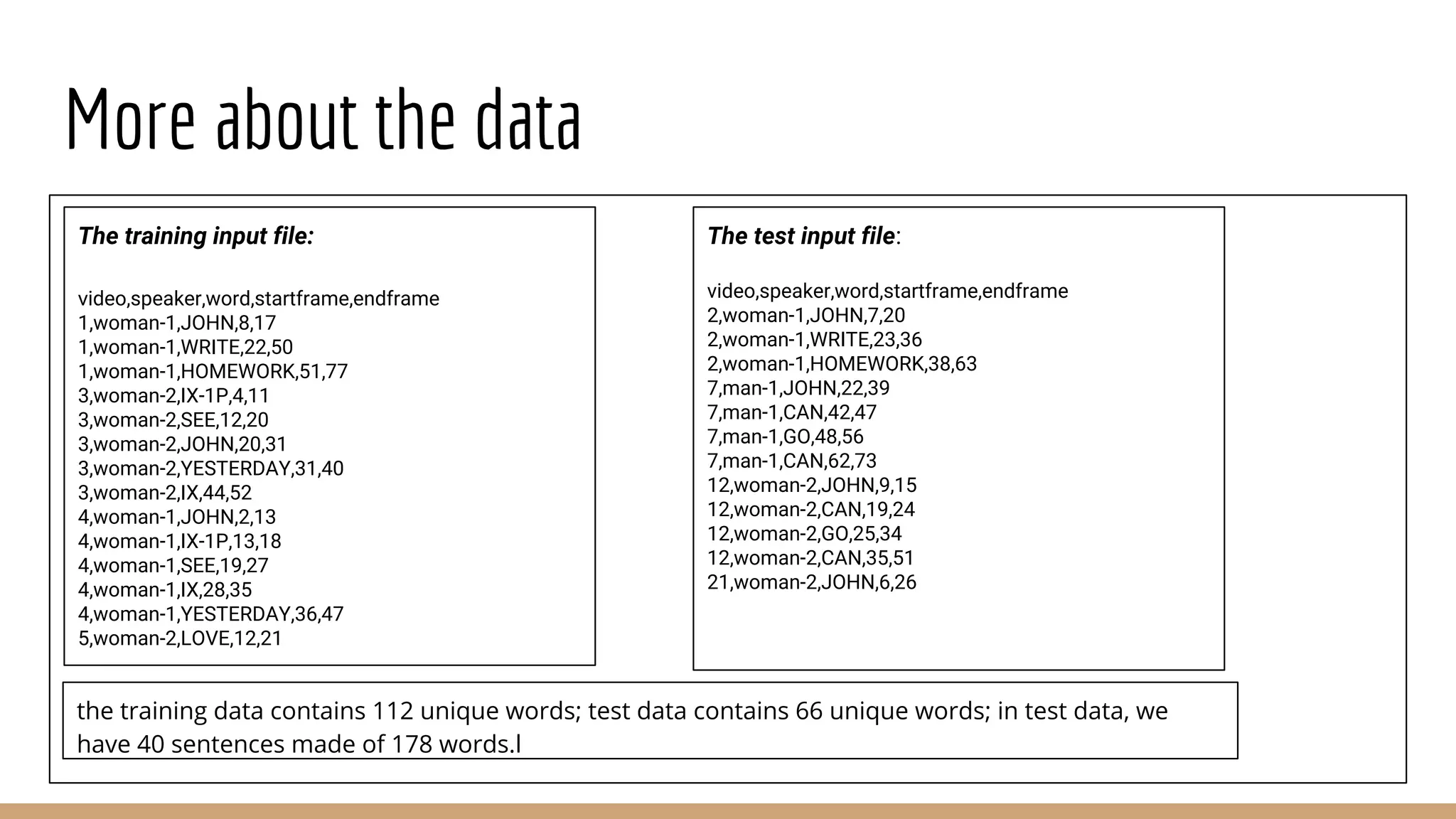
Features are data we feed into networks. Feature selection is crucial in success of a network. Use common sense to
select features. Examples:
X
Y
g-ly
g-ry
g-rx
g-lx
Feature_ground
features_ground = ['grnd-rx', 'grnd-ry', 'grnd-lx', 'grnd-ly']
asl.df['grnd-ly'] = asl.df['left-y'] - asl.df['nose-y']
asl.df['grnd-lx'] = asl.df['left-x'] - asl.df['nose-x']
...
X
rr
ltheta
lr
rtheta
feature_polar
features_polar = ['polar-rr', 'polar-rtheta', 'polar-lr', 'polar-ltheta']
asl.df['polar-rr'] = np.sqrt((asl.df['right-x']- asl.df['nose-x'])**2 + (asl.df['right-y']-asl.df['nose-y'])**2)
asl.df['polar-rtheta'] = np.arctan2(asl.df['right-x']- asl.df['nose-x'],asl.df['right-y'] - asl.df['nose-y'])
...](https://image.slidesharecdn.com/americansignlanguagerecognizer-180526222820/75/American-sign-language-recognizer-6-2048.jpg)