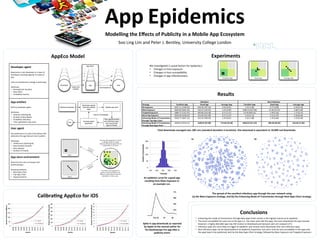
The document discusses a model called Appeco that investigates the factors contributing to app epidemics within a mobile app ecosystem. It highlights three main causal factors: changes in host exposure, susceptibility, and app infectiousness, and examines different strategies for app publicity. Key findings reveal that enhancing transmission through the new apps chart yields the highest epidemic likelihood, while user susceptibility significantly influences app download rates.