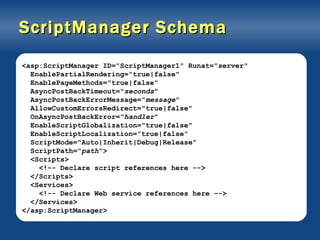
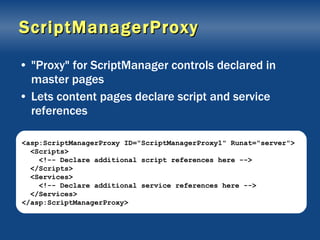
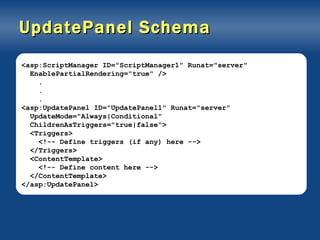
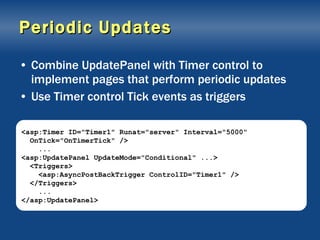
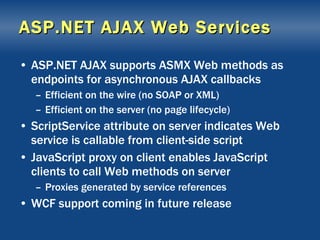
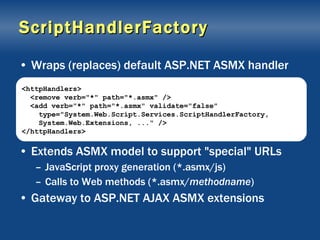
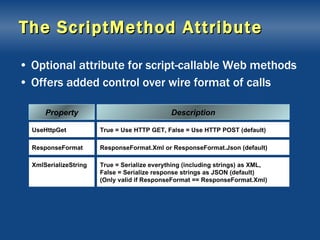
The document provides a comprehensive overview of ASP.NET AJAX extensions, detailing how the ScriptManager, UpdatePanel, and associated controls work to enable asynchronous web interactions and partial-page rendering. It discusses elements like script references, triggers, Page Methods, and AJAX web services, explaining how these components work together to enhance web application performance and user experience. Additionally, it covers the implementation of periodic updates, handling errors, and utilizing JSON for data interchange within AJAX applications.












![Script-Callable Web Service [System.Web.Script.Services.ScriptService] public class ZipCodeService : System.Web.Services.WebService { [System.Web.Services.WebMethod] public string[] GetCityAndState (string zip) { ... } }](https://image.slidesharecdn.com/xmk-100726182516-phpapp01/85/AJAX-ASP-Net-21-320.jpg)



![ASMX Wire Format POST /AtlasRC/ZipCodeService.asmx/GetCityAndState HTTP/1.1 Accept: */* Accept-Language: en-us Referer: http://localhost:1997/AtlasRC/ZipCodePage.aspx UA-CPU: x86 Accept-Encoding: gzip, deflate User-Agent: Mozilla/4.0 (compatible; MSIE 7.0; ...) Host: localhost:1997 Content-Length: 15 Connection: Keep-Alive Cache-Control: no-cache {"zip":"98052"} Request HTTP/1.1 200 OK Server: ASP.NET Development Server/8.0.0.0 Date: Fri, 29 Dec 2006 21:06:17 GMT X-AspNet-Version: 2.0.50727 Cache-Control: private, max-age=0 Content-Type: application/json; charset=utf-8 Content-Length: 16 Connection: Close ["REDMOND","WA"] Response JSON-encoded input JSON-encoded output](https://image.slidesharecdn.com/xmk-100726182516-phpapp01/85/AJAX-ASP-Net-26-320.jpg)



![Using ScriptMethod [System.Web.Script.Services.ScriptService] public class ZipCodeService : System.Web.Services.WebService { [System.Web.Services.WebMethod] [System.Web.Script.Services.ScriptMethod (ResponseFormat=ResponseFormat.Xml)] public XmlDocument GetCityAndState (string zip) { ... } } Method returns XML document, so serialize as XML rather than JSON](https://image.slidesharecdn.com/xmk-100726182516-phpapp01/85/AJAX-ASP-Net-32-320.jpg)


![Defining a Page Method public partial class MyPage : System.Web.UI.Page { [System.Web.Services.WebMethod] public static string[] GetCityAndState (string zip) { ... } ... }](https://image.slidesharecdn.com/xmk-100726182516-phpapp01/85/AJAX-ASP-Net-35-320.jpg)




![Loading Profile Properties Sys.Services.ProfileService.load(['ScreenName'], onLoadCompleted, onLoadFailed); ... function onLoadCompleted(result, context, methodName) { window.alert(Sys.Services.ProfileService.properties.ScreenName); } function onLoadFailed(err, context, methodName) { window.alert(err.get_message()); } Pass null to load all profile properties](https://image.slidesharecdn.com/xmk-100726182516-phpapp01/85/AJAX-ASP-Net-40-320.jpg)
![Saving Profile Properties Sys.Services.ProfileService.properties.ScreenName = 'Bob'; Sys.Services.ProfileService.save(['ScreenName'], onSaveCompleted, onSaveFailed); ... function onSaveCompleted(result, context, methodName) { window.alert('Save succeeded'); } function onSaveFailed(err, context, methodName) { window.alert(err.get_message()); } Pass null to save all profile properties](https://image.slidesharecdn.com/xmk-100726182516-phpapp01/85/AJAX-ASP-Net-41-320.jpg)
