2-preface and pages
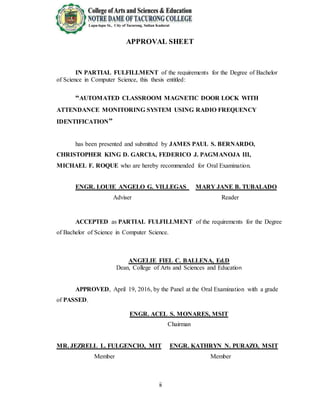
- 1. ii APPROVAL SHEET IN PARTIAL FULFILLMENT of the requirements for the Degree of Bachelor of Science in Computer Science, this thesis entitled: “AUTOMATED CLASSROOM MAGNETIC DOOR LOCK WITH ATTENDANCE MONITORING SYSTEM USING RADIO FREQUENCY IDENTIFICATION” has been presented and submitted by JAMES PAUL S. BERNARDO, CHRISTOPHER KING D. GARCIA, FEDERICO J. PAGMANOJA III, MICHAEL F. ROQUE who are hereby recommended for Oral Examination. ENGR. LOUIE ANGELO G. VILLEGAS MARY JANE B. TUBALADO Adviser Reader ACCEPTED as PARTIAL FULFILLMENT of the requirements for the Degree of Bachelor of Science in Computer Science. ANGELIE FIEL C. BALLENA, Ed.D Dean, College of Arts and Sciences and Education APPROVED, April 19, 2016, by the Panel at the Oral Examination with a grade of PASSED. ENGR. ACEL S. MONARES, MSIT Chairman MR. JEZRELL L. FULGENCIO, MIT ENGR. KATHRYN N. PURAZO, MSIT Member Member
- 2. iii ABSTRACT The study was entitled Automated Classroom Magnetic Door Lock with Attendance Monitoring System Using Radio Frequency Identification was developed to automate mainly the attendance montoring system of teachers and students of the Notre Dame of Tacurong College and to provide classroom security and maintenance access. The main onjective of the study was to developed an Arduino and Visual Studio 2015-based attendance monitoring system which accepts Radio Frequency Identification Tag data and set of numeric codes for room security password. The Radio Frequency Identification or RFID enabled the system to capture and record the Lates and Absences of both teachers and students while the set of numeric codes gave the school personel access to classrooms to perform security and maintennace without using the RFID tag and RFID reader. The proposed system provided the following benefits such as fast and accurate systematic data recording, eliminated attendance roll calls, data security and maintenace, saved money, time and effort and paper works, eliminated large amount of papers used, convenience, organised data for reports and printing, as well as it minimized electric consumption on every classrooms during class breaks. The technologies used in the proposed system were Microsoft Visual Studio 2015, MsSql 2015 Local Database, Arduino Uno R3 and Gizduino v.5.0 microporcessors, 16x2 Liquid Crystal Display or LCD, 600 and 300 - LED Fail Safe Electro-Magnetic Locks, RFID Tag or Card, RFID Readers and a Desktop Computer. The methodology of the proposed study included the operational diagram of the proposed system, context and physical data flow diagram, entity relationship diagram, developmental approach, schedule and timeline, and the budgetary outlay.
- 3. iv After the research project was developed, the result showed that the Automated Classroom Magnetic Door Lock with Attendance Monitoring System Using Radio Frequency Identification satisfied the objectives of the study. When it was tested, it showed that through the attendance monitoring, the accuracy, reliability, convenience and security satisfied the needs of the teachers and studnents. It was highly recommended that the system should have a centralized monitoring system control capable to network all Automated Classroom Magnetic Door Lock with Attendance Monitoring System. should not be limited to Microsoft Operating System (O.S.) and Visual Studio.net platforms but should also in other platforms (i.e. Linux, Mac O.S., iOS, Java programming software). should also provide access to students in viewing their attendance records in aweb browser or in a mobile application using the Internet. should use two database platforms to back up all files. should have a power backup generator or device such as Uninterruptible Power Supply or (UPS) in case of power failure.
- 4. v ACKNOWLEDGEMENT First and foremost, the researchers would like to thank the Almighty Father for giving then knowledge and wisdom in fulfilling this study. The presence of God really helped them and never them down despite all the trials, sacrifices and hardships that encountered. They would also like to extend their gratitude to their Alma Mater, Notre Dame of Tacurong College for giving us quality education and training. The researchers would like to thank the following people who helped them and shared their knowledge for the success of this study. To their Thesis Adviser, Engr. Loiue Angelo Villegas, MSIT, They would like to express their sincere gratitude for hes support patience they, motivation, enthusiasm, and immense knowledge shared to them. They would also like to acknowledge their Thesis Writing Instructress, Mrs. Analiza S. Henodia, MIT, for imparting her support, guidance, patience and trust during the whole semester’s. To their grammarian, Mrs. Mary Jane B. Tubalado, for accepting the responsibility of being the thesis reader and for the worthy suggestion and constructive criticism that greatly improve this research. To their panelists, we would like to thank our dear panelists, Engr. Acel S. Monares, MSIT, Engr. Kathryn N. Purazo , MSIT and Mr. JEZRELL L. FULGENCIO, MIT, for their time and effort, insightful comments and in checking our work for improvements despite of their busy schedules. Lastly, They would like to thank dearly their parents, brothers, sisters, relatives and friends, especially to Mr. Jessie L. Fulgar, Mr. Francis Jason V. Tugade and Mr. Danilo R. Aquino III, for helping them and sharing them his expertise and great ideas to finish the Thesis. The Researchers
- 5. vi DEDICATION This research study is heartily and lovingly dedicated to our beloved parents, Mr. and Mrs. Pilgriminda S. Bernardo and family, Mrs. Winefreda D. Garcia, Mrs. Jocelyn J. Pagmanoja and family, Col. Peter F. Roque and Marlyn G. Ferolino who have been the source of our financial assistance and inspiration. They gave us a lot of patience and helped us motivate ourselves to research more and dedicate more time in pursuing our study. Above all, to our loving and forgiving God who has been the source of all our strength, knowledge and wisdom in doing this research. Without Him, this study will not be possible.
- 6. vii TABLE OF CONTENTS Page APPROVAL SHEET………………………………………………………… ii ABSTRACT……….………………………………………………….……… iii ACKNOWLEDGEMENT…………………………………….……………… v DEDICATION………………………………………………………..……… vi TABLE OF CONTENTS………………………………………………..…… vii LIST OF TABLES……………………………………………………………. ix LIST OF FIGURES…………………………………………………...……… x APPENDICES………………………………………………………..………. xii CHAPTER I. INTRODUCTION……………………………………………. 1 Background of the Study………………………………..……. 1 Objectives of the Study………………………………………. 5 Significance of the Study………………………………….…. 6 Scope and Limitation……………..……………………….…. 8 Definition of Terms………………………………………..…. 10 II. REVIEW OF RELATED LITERATURE…………………… 12 III. TECHNICAL BACKGROUND……………………………... 15 IV. METHODOLOGY….….….….….….….….….….….….…… 30 Operational Diagram…………………………………………. 30 System Analysis……………………………………………… 36 Developmental Approach……………………………….……. 39
- 7. viii Schedule and Timeline……………………………….………. 44 Budgetary Outlay…………………………………………….. 45 V. RESULTS AND DISCUSSION…………………………...… 47 VI. CONCLUSION AND RECOMMENDATIONS………….…. 55 Conclusion…………………………………………………… 61 Recommendation…………………………………………..…. 55 REFERENCES…………………………………………………………….… 57 APPENDICES……………………………………………………………..… 58
- 8. ix LIST OF TABLES Table Page 1 Hardware and Software Requirements…………………..…… 40 2 Schedule and Timeline……………………………………….. 44 3 Budgetary Outlay…………………………………………….. 45 4 List of Hardware and Software Tools and Equipment……..… 45
- 9. x LIST OF FIGURES Figure Page 1. Network and System Architecture................................................................ 15 2. Passive RFID Tag (125 KHzMango)............................................................ 17 3. GizDuino 5.0 RFID Reader.......................................................................... 18 4. GizDuino Version 5 w/ATmega328P........................................................... 19 5. 4x4 Universal Keypad.................................................................................. 20 6. Arduino Uno Microcontroller R3................................................................. 20 7. 16x2 Liquid Crystal Display 1602A............................................................. 21 8. Centralized Computer Server (PC).............................................................. 22 9. Visual Studio.net 2015.................................................................................. 22 10. MsSql Local Database 2015....................................................................... 23 11. Ebelco 300/600 – LED Electro Magnetic Lock (Fail-Safe)....................... 24 12. Customized Printed Circuit Board (PCB)................................................... 25 13. Self-Lock Channel 12 volts Relay.............................................................. 26 14. Potentiometer 10kOhm............................................................................... 27 15. Gizduino v.5 and Arduino Uno microcontroller programming languages.. 28 16. Printer.......................................................................................................... 29 17. Operational Diagram of Automated Classroom Magnetic Door Lock with Attendance Monitoring Systemusing Radio Frequency Identification............. 30 18. Accessing Classroom and Attendance Monitoring using Radio Frequency Identification..................................................................................................... 32 19. Using Push Button inside the Classroom.................................................... 33
- 10. xi 20. Overriding the System 4x4 Using Universal Keypad................................. 34 21. Context Data Flow Diagram (Level 0)....................................................... 36 22. Data Flow Diagram (Level 1)..................................................................... 37 23. Entity Relationship Diagram (ERD)........................................................... 38 24. Automated Classroom Magnetic Door Lock with Attendance Monitoring System using Radio Frequency Identification frequency….….….….….….….….….. 47 25. Algorithm flowchart for teacher attendance monitoring and classroom security access and entry........................................................................................................... 48 26. Algorithm flowchart for student attendance monitoring............................ 50 27. Algorithm flowchart for security and maintenance personnel classroom access............................................................................................... 51 28. Database Structure of Automated Classroom Magnetic Door Lock with Attendance Monitoring System using Radio Frequency Identification............................... 52 29. Miniature prototype simulation model....................................................... 53
- 11. xii APPENDICES Appendix Page A User’s Manual………………………………………………... 58 B Application Letter for Thesis Adviser……………………….. 75 C Application Letter for Grammarian/Reader………………….. 76 D Application Letter for Preliminary Defense………………….. 77 E Application Letter for Chapters Defense…………………….. 78 F Application Letter for Final Defense………………………… 79 G Proponents’ Profile…………………………………………... 80 H Source Code………………………………………………….. 84
