The document summarizes the effects of a computer worm that disrupted AT&T's phone network on January 15. A flaw in AT&T's System Seven software caused a broadcast message from a 4ESS machine in New York to trigger similar messages from 114 other 4ESS machines nationwide. This overwhelmed the signaling network with messages and prevented most calls from connecting. The incident highlighted AT&T's lack of redundancy and vulnerability from centralized operations. While the specific cause was still unknown, it showed the risks of putting blind faith in technology without understanding how systems work.



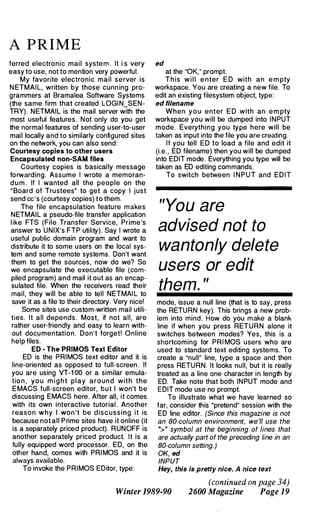
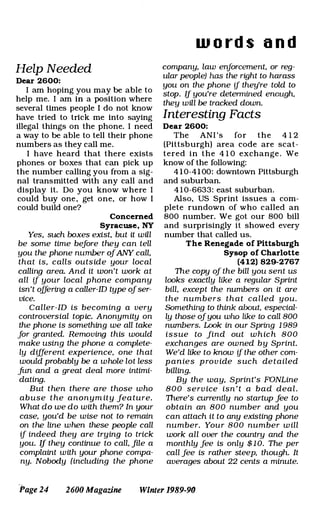
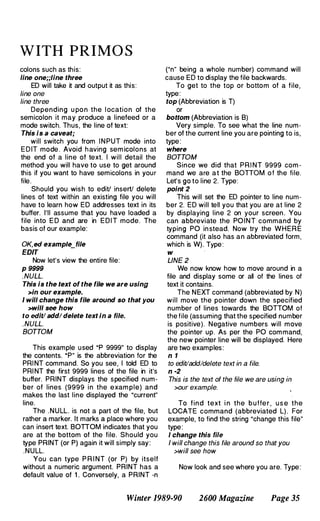
![•
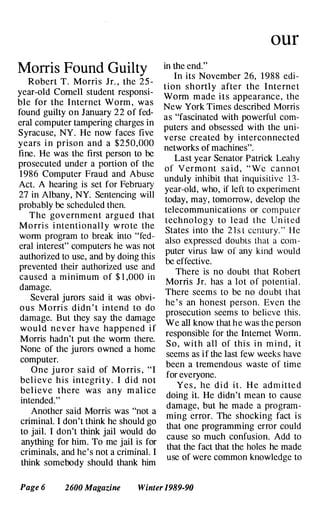
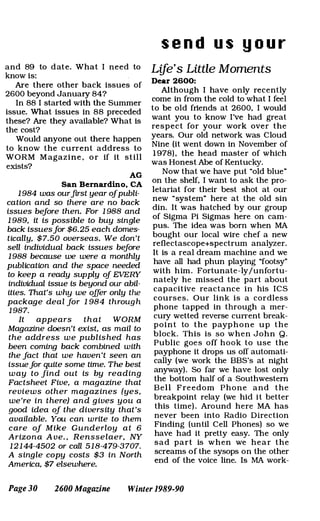
In nem
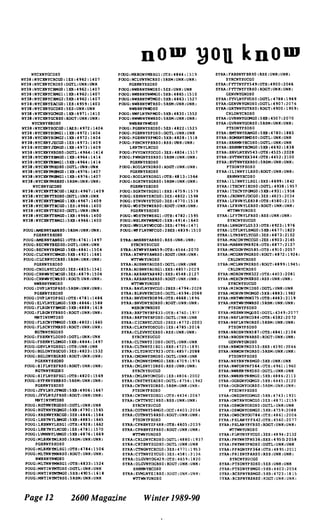
NGFLNy76CGO
BUFF:SDTNNYFIDSO DGTL:UNK:UNK
BurF:SLCKN'fSICGO 3£5:5163:2325
BUFF:SLMNNyww945 5XB:5192:2216
BUFf:SPVLNYWHCGO 3E5:5125:2253
surF:SRPLNYSB2520TB:5275:2356
BUFF:SRPLNYSBDSO DGTL:UNK:UNK
BUFF:TNWNNYTWCGO IllS:5050:234"
BUFF:VRBGNYVBDSO DGTL:lJNK:UNK
BUFF:WLSNNYMERSI RSS:4994:2373:
LCPTN'fLKCGO
BUFF:WLVLNYNM593 SXB:5129:2108
BUFF:WNKHNYWKCGO 28£5:5103:2313
BUFF:WSNCNYUNDSO DGTL:UNK:UNK
BurF:WSNCNYUNMGO 5XB:5074:2304
BUFF:WSVLNYNCCGO lAES:5049:2319
BUFF:WTPTNYWRCGO 3£5:4935:2292
BUFF:YNTWNTITCGO 3£5:5025:2395
CISP:BBYLNYBNDSO DGTL:4939:1314
CIS? :BRWDNYBWDSO SES:4912:1311
CISP:BYSHNYBYDSO DGTL:UNK:UNK
CISP:CALVNYSPRSO 5RSM:UNK:UlH(:
RVRDNYRVDSO
CISP:C!ofo1KN'fCMDSO 5[5:4911:1327
CISP:C�KNyC�GO 5XB:UNK:UNK
CISP:CTCHNYCUOSO DGTL:UHK:UHK
CISP:CTCHNYCUMGO 5XB:4191:1246
CISP:DRPKNYDPCGO 1AEs:4928:1321
CISP:DRPKNYDPMGO 5XB:4928:1321
CISP:EBTNNYEHMGO 5XB:4185:1200
CISP:ENPTNYENCGO lES:4906:1331
CISP:ENPTNYENDSO DG'I'L:UlU(:UHK
CISP:ENPTNYENMGO 5XB:4906:1331
CISP:GPTSNYGPMGO 5XB:4112:1243
CISP:GPTSNYGPRSO ROGT:UHK: UNK:
CTCBNYCUDSO
CISP:BMB'fNYBBOSO DG'l'L:UNK:UNK
CISP:HMB'fNYBBMGO 5XB:4836:1232
CISP:HNSTNYHUCGO lAES:4920:1344
CISP:HNSTNYHUDSO 5ES:UNK:UNK
CISP:HNSTNYBUMGO 5XB:4920:1344
CISP:BNSTNYBUMGI 5XB:4920:1344
CISP:LHSTNYLBCGO 1£5:4946:1315
CISP:LHSTNYLBDSO 5ES:UNK:UNK
CISP:MNTKNYMTD50 5ES:UNK:UNK:
RVBDNYRVOS0
CISP:MNTKNYMTMGO 5XB:4139:1118
CISP:MSTCNYMCOSO 5r.s:UNK:UNK
CISP:OCBHNYOBCGO 2£S:4929:1284
CISP:OCBHNYOBRSO 5RSM:UNK:UNK:
BYSBNYBYDSO
CISP:PCBGNYPBCGO lAES:4894:1280
CISP:PCBGNY'PBMGO 5XB:4894:1280
CISP:PJSTNYPJDSO DG'l'L:4870:1309
CISP:RNKNNYRNCGO lES:4894:1302
CISP:RNKNNYRNDSO 5ES:UNK:UNK
CISP:RNKNNYRNMGO 5XB:4894:1302
CISP:RVHDNYRVDSO 5ES:4843:1256
CISP:SATNNYSNMGO 5XB:4821:1216
CISP:SGHRNYSGDSO DG'l'L:UNK:UNK
CISP:SGHRNYSGMGO 5XB:4796:1211
CISP:SHHMNYSBDSO DG'l'L:UNK:UNK
CISP:SEiHMNYSHMGO 5XB:4862:1292
CISP:SLDNNYSEDSO DGTL:UNK:UNK
CISP:SLDNNYSEMGO 5XB:4819:1296
CISP:SMTWNYSMCGO I£S:4898:1311
CISP:SM'l'KNYSMDSO DGTL:UNK:UHK
CISP:SMTNNYS!+1GO 5XB:4898:1317
CISP:STKTNYSKDSO DGTL:UNK:UNK
CISP:STKTNYSKMGO 5XB:4876:1311
CISP:SYVLNYSADSO DGTL:4906:1286
CISP:WHBHNYWBDSO DGTL:UNK:UNK
CISP:NHBHNYWBMGO 5XB:4859:1240
GDCY FLPKNYFPCGO lAES:4970:1367
GDCY FLPKNYFPDSO DGTL:UNK:UNK
GDCY FLPKNYFPMG1 5XB:4910:1361
GDCY FRDLNYFMCGO lAES:4943:1333
GDCY FRDLNYFMUSO 5ES:UNK:UNK
GDCY fRPTNYfPDSO DG'!'L:4912:1341
GDCY FRPTNYFPMG1 5XB:4912:1341
GDCY FRPTNYFPMG2 5XB:4972:1341
GDCY GLCVNYGCDSO 5£S:4940:1315
"9opk St a t e
GOCY:GRCYNYGCCGO:lAES:4958:1355
GOCY:GRCYNYGCOS0:[x;TL:UNK:UNK
GOCY:GRNKNYGHDS0:5ES:4962:1377
GDCY:HCVLNYHVCGO:IMS:4946:1348
GDCY:HCVLNYHVDSO:[x;TL:UNK:UNK
GDCY:BCVLNYHVMG1:5XB:4946:1348
GDC'l:BCVLNYRVMG2:5XB:4946:1348
GOCY:HMPSNYHSDS0:[x;TL:4966:1354
GDCY:HMPSNYHSMG1:5XB:4966:1354
GOCY:LNBBNYLBDSO:DGTL:UN!::UN!:
GDCY:LNBBNYLB/-CO:5XB:4991:1343
GOCY:LNBHNYLBMG1:5XB:4991:1343
GOCY:LVTIfNYLTDSO:DGTL:UNI<:UNK
GOCY:LVTNNYLTMGO:5XB:4952:1341
GOCY:LVTNNYLTMG1:5XB:4952:1341
GDCY:LYBRNYLBCGO:1AtS:4978:1352
GDCY:LYBRNYLBDSO:DGTL:UNI<:UNK
GOCY:MINLNYMIDS0:[x;TL:4961:1359
GDCY:MINLNYMIMG2:5XB:4961:1359
GDCY:MNHSNYMHDSO: SES:UNI<:UNI<
GOCY:MNRSNYMHKiO:lXB:4958:1375
GDCY:MSPQNYHPOSQ:OGTL:4954:132<1
GDCY:HSPQNYMPMG1:5XB:4954:1324
GOCY: OYBANYOYMGO:5XB:4930:1364
GDCY:OYBAN'fOYRSO:5RSH :UNK:UNI<:
GLCVNYGCDSO
GDCY:PLVWNYFVCGO:1ES:4940:1344
GDCY:PLVWNYPVOSO:5ES:UN!::UNK
GDCY:PTWANYPWDSO:5ES:UNK:UNI<
GDCY:PTWANYP�O:5XB: 4952:1380
GOCY:RSLNN'lRODS0:DGTL:4953:1367
GOCY:SYOSNYSYOS1:[X;TL:UNI<:UNI<
GOCY: WBYNNYNEDSO:DGTL:4954:1355
GDCY: WDMRNYFRDSO:DGTL:UNK:UNK
GOCY:WDMRNYFRMGO:5XB:4987:1354
GOC'l:NOMRNYFRMGl:5XB:4981:1354
GDCY:NNTGNYWTCGO:lAES:4961:1334
GDCY:NNTGNYWTDS0:[X;TL:UNK:UNK
GDCY:WNTGNYWTMGl:5XB:4961:133-4
GOC'f:yPHNNYYAMGO:5XB:4882:1282
N'f21:N'lCMNYl3CGO:1MS:4998:1404
NY21:NYCMNY13DS0:5ES:4998:1404
NY21:NYCMNYI3DS1:DGTL:UNK:UNK
NY21: NYCMNY13MGl:lXB:4998:1404
NY21:NYCMNY13MG2:lXB:4998:1404
NY21:NYCMNY18CGO:lAES:4998:1407
NY21:NYCMNY18DSO:5ES:4998:1407
NY21:NYCMNYl8DS1:DGTL:UN!::UNK
NY21: NYCMNYl8MGO:lXB:4998:1407
NY21:N'lCHNYl8MG1:lXB:4998:1407
NY21:NYCMNYI8MG2:1XB:4998:1407
NY21:NYCMNY30CGO:lAES:4995:1405
NY21:NYCMNY30CG1:lAtS:4995:1405
NY21:NYCMNY30DS0:[x;TL:UN!(:UN!(
NY21:NYCMNY30MGl:lXB:4995:1405
NY21:NYCHNY30MG2:lXB:4995:1405
NY21:NYCMNY30MG3:lXB:4995:1405
NY21:NYCMNY36CGO:IES:4995:1408
NY21:NYCMNY36CG1:IMS:4995:1408
NY21:NYCMNY36CG2:lES:4995:1408
NY21:NYCMN'l36DSO:DGTL:4995:1408
NY21:NYCMNY36DS1:5ES:UNK:UN!(
NY21:NYCMNY42CGO:IMS:4994:1407
NY21:NYCMNY42CGl:IAES:4994:1401
NY21:NYCMNY42CG2:1MS:4994:1407
NY21:NYCMNY42CG3:IAES:4994:1407
NY21:NYCMNY42DS0:DGTL:UN!::UN!:
NY21:NYCMNY50CGO:1AES:4993:1409
NY21:NYCMNY50CG1:lAtS:4993:1409
NY21:NYCMNY50DSO:DGTL:4993:1409
NY21:NYCMNY50DS1:5ES:UN!::UNK
NY21:NY01NY50DS2:DGTL:UN!(:UN!(
NY21:NY01NY50MG2:lXB:4993:1409
NY21:NYCMNY50MC3:5XB:4993:1409
NY21:NYCMNY50MG4:5XB:4993:1409
NY21:NYCMNY50MG5:5XB:4993:1409
NY21:NYCMNYAAMGO:lXB:5002:1405
NY21:NYCMNYAPRSO:RDGT:4993:1409:
NYCMNY50DSO
NY21:NYCMNYBSCGO:lAES:5005 1404
NY21:NY01NYBSCGI:IAES:5005 1404
NY21:NYCMNYBSCG2:IAES:5005 1404
NY21:NYCMNYBSCG3:1AES:5005 1404
N'l21:NYCMNYBSCG4 lAtS 5005:1404
NY21:NYCMNYBSDSO DGTL UNI<:UNK
NY21:NYCMNYBSDSI DGTL UNI<:UNK
NY21 :NYCMNYBSDS2 DGTL UNK:UNI<
NY21:NYCMNYSRRSO ROGT 4993:1409:
NYCMNY50DSO
NY21:NYCMNYSRRS1:ROOT:UNK:UNK:
NYCMN'l50DS1
NY21:NYCMNYSRRS2:ROGT:UNK:UN!(:
NYCMNY50DS2
NY21:NYCMNYSTCGO lAtS:S004:1405
NY21:NYCMNYSTCGl lAtS:5004:1405
NY21:NYCMNYSTDSO DGTL:UN!(:UN!:
NY21:NYCHNYVSCGO lAtS:5002:1405
NY21:NYCMNYVSDSO 5ES:UN!::UN!:
NY21:NYCMNYWSCGO lES:5004:1406
NY21:NYCMNYWSCGl lAtS:5004:1406
NY21:NYCMNYWSCG2 1AES:5004:1406
NY21:NYCMNYWSCG3 1AES:5004:1406
NY21:NYCMNYWSCG4 lAES:5004:1406
NY21:NYCMNYWSDSO DGTL:5004:1406
NY21:N'lCMNYWSDSl DGTL:UNI<:UNI<
NY21:NYCMNYWSDS2 DG'l'L:UNI<:UNI<
NY21:NYCMNYWSDS3 DG'TL:UNK:UNI<
NY21:NYCMNYWSMG2 1XB:5004:1406
NY21:NYCMNYWSMG4 5XB:5004:1406
NY21:NYCMNYWSMG5 5XB:5004:1406
NY21:NYCMNYWSMG8 5)(8:5004:1406
NY21:NYCMNYWSRSO RDGT:5004:1406:
NYCMN'fwSDSO
NY21:NYCRNYNOCGO lAES:5039:1401
NY21:NYCRNYNDMGO 5XB:5039:1401
NY21:NYCRN'fNSDSO DGTL:5027:1406
NY21:NYCRNYNSDS1 DGTL:UN!::UNX
NY21:NYCRN'fNSMGO 1XB:5027:1406
NY21:NYCRN'fNSMGl 5XB:5027:1406
NY21:NYCRNYSSCGO lAES:5052:1404
NY21:NYCRNYSSMGO 5XB:5052:1404
NY21:NYCRNYWSCGO lAES:5037:1411
NY21:NYCRNYWSMGO 5XB:5037:1411
NY38:NYCMNY37CGO lAES:4994:1405
NY38:NYCHNY37CG1 1AES:4994:1405
NY38:NYCMNY37DSO DGTL:UNX:UNK
NY38:NYCMNy)7DSl 5E5:UNK:UNK
NY38:NYCMNY37MGl 1XB:4994:1405
NY38:NYCMNY37MG2 1XB:4994:1405
NY38:NYCMNY37MG3 lXB:4994:1405
NY3:::NYCMNY31MG4 5XB:4994:140S
NY38:NYCMNY37MG5 SXB:4994:140S
NY38:NYCMNY31MG6 5XB:4994:1405
NY38:NYCMNY56CGO lAES:4991:1405
NY38:NYCMNY56CGl lAtS:4991:1405
NY38:NYCMNY56CG2 lAES:4991:1405
NY38:NYCMNY56CG3 1AES:4991:140S
NY38:NYCMNY56CG4 lAt5:4991:1405
NY38:NYCMNY56DSO DG'l'L:UNK:UNK
NY38:NYCMNY56MG6 5xB:4991:1405
NY38:NYCMNY7]CGO lAES:4989:1410
NY38:NYCMNY7)DsO DGTL:UNK:UNK
NY38:NYCMNY73MGO lXB:4989:1410
NY38:NYCMNY"13MG1 5XB:4989:1410
NY38:NYCMNY79CGO 1ES:4988:1406
NY38:NYCMNY79CG1 lAtS:4988:1406
NY3e :NYCMNY790S0 DGTL:UNK:UNI<
NY38:NYCMNY79MGO lXD:4988:1406
NY38:NYCMNY79MG1 5xB:4988:1406
NY38:NYCMNy79MG2 5XB:4988:1406
NY38:NYCMNY97CGO 1AES:4985:1407
NY38:NYCMNY970S0 5ES:UNI<:UNK
NY38:NYCMNY97MGO lXB:4985:1407
NY38:NYCMNY97MG1 lXB:4985:1407
NY38:NYCMNYCACGO lES:4911:1411
NY38:NYCMNYCADSO DGTL:UNI<:lJNK
NY38:NYCMNYCAMGO 1XB:4977:1411
NY38:NYCMNYMNCGO lAES:4983:1410
NY38:NYCMNYMNDSO DGTL:UNK:UNK
NY38:NYCMNYMNMG1 1XB:4983:1410
NY38:NYCMNYTHCGO 1E5:4969:1414
NY38:NYCMNYTBMGO lXB:4969:1414
NY38:NYCMNYWACGO lES:4973:1413
NY38:NYCMNYWADSO DGTL:UNK:UNK
NY38:NYCMNYWAMGO lXB:4973:1413
NY38:NYCXNYCIRS1 5RSM:UN!::UNK:
Winter 1989-90 2600 Magazine Page 11](https://image.slidesharecdn.com/2600v06n4winter1989-200423193121/85/2600-v06-n4-winter-1989-11-320.jpg)
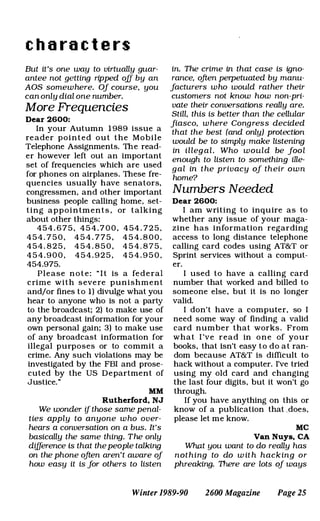
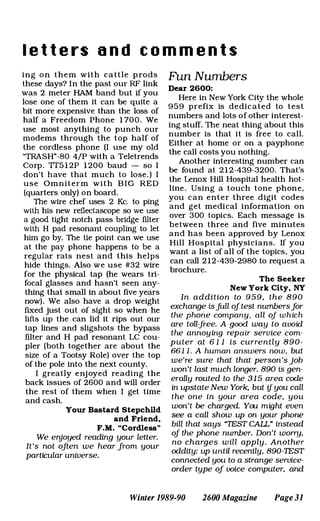
![are summarized below.
S I M (System Information/Meteri ng)
Commands System status and resource
monitoring of local and remote systems
from any point within the network.
RESUS (REmote System USer) Facility
Control of remote Prime systems from any
terminal. Allows use of console-only com
mands from a remote terminal.
Collection and collation of event mes
sages, including PRIMOS and network
eve n t s , through D S M ' s U n s o l ici ted
Message Handling (UMH) and logging ser
vices, with redirection of event messages to
log files or users throughout the network.
Generalized logging of DSM messages
in private or system logs, with commands
for administering, displaying and printing
logs.
Facilities for defining users' access to
DSM commands throughout the network,
in a single configuration file.
As you can see, the DSM utilities can
be a very u seful asset to have .
Unfortunately, SYS1 privileges (administra
tor) are required to use the most exciting
aspects of the DSM utilities. All normal
users can utilize the SIM commands, and I
have even mentioned some of them i n
other parts o f this series. What is really
useful to us, however, are the RESUS and
log utilities. In a nutshell here are the basic
DSM commands. After this list will be full
discourses on the RESUS utility and the
SIM commands.
Remote System Control:
R ESUS - I nvokes P r i m e ' s R E mote
System USer facility.
Event M essage Handling and
Redirection:
CON FIG_UM confi g u re s DSM
Unsolicited Message Handling.
Administering Logs:
ADMIN LOG - creates and administers
DSM 109 files.
Displaying and Printing Logs:
DISPLAY_LOG - displays and prints the
contents of log files, including system and
network event logs.
DSM Configurator Commands:
CONFIG DSM - creates a new DSM con
figuration
-
file.
MORE
DlSTRIBUTE_DSM - distributes a new
DSM configuration file.
STATUS_DSM - displays the currently
active configuration.
DSM Startup and Shutdown Commands :
START_DSM - starts DSM system con
sole commands.
STOP_DSM - stops DSM system console
commands.
For more information on any of the DSM
commands, type:
HELP command-name
or
command-name -HELP
The RESUS Utility
RESUS is the REmote System U Ser
facility, and allows remote operation of the
physical supervisor console from any termi
nal. What this basically means is that, with
RESUS enabled, all users with administra
tor access will be able to execute com
mands that are normally only executable
from the system console. It will let you force
other users off the system (not a good idea
to use this capability unless you MUST),
take the sy stem down (you m u s t be
STU PID to do such a thing), etc. RESUS
s u p p o rts the fol low i n g co m m an d l i n e
options:
-ENABLE
-DISABLE [-FORCE]
-START [-ON node name]
-STOP
-STATUS [-ON node group]
-HELP [-NO_WAIT]
-USAGE
-ENABLE
This option enables RESUS to be used
o n a s y s te m . I t i s o n l y valid from the
supervisor terminal.
-DISABLE
This option is used to prevent RESUS
from being used on a system on which it
has previously been -E NABLEd. The -
FORC E option must be supplied if the
RESUS is actually in use. It is only valid
from the supervisor terminal.
-START [-ON node name]
This is the means by which an autho
rized user of RESUS may invoke REmote
System USer facilities on a system. If -ON
Page 16 2600 Magazine Winter 1989-90](https://image.slidesharecdn.com/2600v06n4winter1989-200423193121/85/2600-v06-n4-winter-1989-16-320.jpg)
![PRIME HACKING
node name i s omitted, the default is the
local node. For this command to be suc
cessful, RESUS must previously have been
-ENABLEd at the supervisor terminal.
-STOP
This option terminates remote control of
the su pervi s o r term i n al , leaving the
REmote System USer facilities available for
use by other authorized u sers . It is only
valid from the remote terminal in control of
the supervisor terminal through RESUS.
-STATUS [-ON nodegroup]
This displays the current stat u s o f
RESUS o n all nodes in a specified node
group. If a node group is not specified, the
status of the local node is displayed.
-HELP, -H [-NO_WAIT, -NW]
Displays command-specific Help text.
-USAGE
Displays command line syntax.
The DSM SIM Commands
The D S M S I M (Sy stem
Information/Metering) commands gather
and display information about system/net
work status and resource usage from any
point on the network.
SI M commands are invoked from the
P R I MOS com m a n d l i n e . They can be
invoked from any terminal to display infor
mation about any system on the network.
They can be invoked once, or periodically
at specified time intervals. Output displays
are paginated for screen display and can
be recorded in private or system log files.
User access to SIM commands on local
and remote nodes is controlled by DSM
security.
A list of S I M commands and descrip
tions of the general SIM options follows.
LIST ASSIGNED DEVICES - lists
assigned devices
-
L1ST_ASYNC - lists asynchronous termi
nals
LIST COMM CONTROLLERS - lists
comms contrOllers configuration
LIST_CONFIG - lists PRIMOS coldstart
configuration
LIST_DISKS - lists disk partition names
L1ST_LAN_NODES - lists nodes on
LAN300 local networks
LIST_MEMORY - lists physical memory
usage
L1ST_PRIMENET_NODES - lists
PRI MENET configured nodes
LIST PRIMENET LINKS - lists active
PRI MENET links -
L1ST_PRIM ENET_PORTS - lists assigned
PRIMENET ports
LIST_PROCESS - lists active system pro
cesses
LIST_SEMAPHORES - lists active
semaphores
LIST_SYNC - lists synchronous line config
uration
LIST_UNITS - lists users open file units
L1ST_VCS - lists active virtual circuits
General SIM options are:
-HELP, -H [-NO_WAIT, -NW]
-USAGE
-ON {node, nodegroup}
-PRIVATE_LOG, -PLOG pathname [-
NTTY, -N]
-SYSTEM_LOG, -SLOG path name [
NTTY, -N)
-NO WAIT, -NW
-FR EQ integer
-TIMES integer
-START, -S date+time
-STOP date+time .
-ON {node, nodegroup}
This option allows you to specify the tar
get node, or nodegroup to which the com
mand is to be directed. The default is to
direct the command to the node on which
the command is invoked.
-PRIVATE_LOG, -PLOG pathname [
NTIY, -N )
-SYSTEM_LOG, -SLOG pathname [
-NTTY, -N ]
The -PRIVATE_LOG option allows you
to specify a standard PRI MOS pathname
as a DSM log file to which all messages
from the target nodes are to be logged. If
the log does not already exist, it is created
automatically for you. User DSMASR (the
DSM application server) must have ALL
access to the directory that contains the
log.
The -SYSTEM_LOG option allows you
a ·similar facility using logs that are main
tained on the system logging directory
DSM*>LOGS. System logs only exist on
Winter 1989-90 2600 Magazine Page 1 7](https://image.slidesharecdn.com/2600v06n4winter1989-200423193121/85/2600-v06-n4-winter-1989-17-320.jpg)
![this directory or its subdirectories, and must
be created with the ADMIN_LOG command
prior to use.
Logged d ata can s u b sequentl y be
retrieved, printed and displayed using the
DISPLAY LOG command.
-NTTY, -N; can be used with the -PRI
VATE_LOG and -SYSTE M_LOG options,
and indicates that no data i s to be dis
played to the user. When this option is
used, the command spawns a phantom
which executes the com mand on your
behalf, and frees your terminal.
-HELP, -H [NO_WAIT, -NW]
This option overrides all other options to
display help information about the associat
ed command.
-USAGE
This option overrides all other options to
display usage information, for the associat
ed command.
-NO WAIT, -NW
This option indicates that you are not to
be prompted or queried during the com
mand output display.
I f th i s option is n o t u s e d , y o u are
prompted betwee n each target node ' s
response, and after every 2 3 lines (1 page)
of output displays "-More-" and waits for
your response. To see more output press
the carriage return. To suppress further
output and return to command level, type
Q, Quit, N , or No. Any other response will
display more output.
-FREQ
-TIMES
-START, -S
-STOP
These options can be u sed to imple
ment periodic execution of a command.
-FREQ option provides periodic execu
tion of a c o m m an d , with the i n terval
between executions determined i n sec
onds. The interval you specify is the inter
val between two successive executions of a
com mand, and not the interval between
completion of the command's display and
the next execution. The interval is corrected
to the n earest m ultiple of fou r seconds
below that specified. If FREQ 0 is specified,
the command is re-executed immediately
on completion of the previous execution. If
INFILTRATING
the interval elapses before completion of
the previous display, the next execution is
delayed until the display is complete.
-TIMES is used in association with the -
FREQ option, to set a limit on the number
of times that a command is to be executed.
-START, -S sets the date and time that
execution starts. The format can be in
either ISO standard:
(YY_MM_DD.HH:MM:SS)
or in USA standard:
(MM/DDIYY.HH:MM :SS)
Defaults are: year to current year; date
to current date; and time to zero.
-STOP sets the date and time execution
stops ; format and defaults are the same as
for -START.
I n the absence of any of these four
options, the command is executed once,
and immediately.
I n the presence of any of these four
options, the defaults applied to the ur.speci
fied options are:
-FREQ - Immediate reexecution
-TIMES - infinite
-START - now
-STOP - never
For more information on any of the SIM
commands, type:
HELP command-name
or
command-name -HELP
PRIMOS Electronic Mail Capabilities
PRIMOS, like any other operating sys
tem worth its beans, supports full electronic
mail capabilities. However, the mail system
used will vary from system to system. A
lack of standards? Perhaps. But I find it
enjoyable learning the differences between
the many mail systems available.
I won't discuss how to use the mail sys
tems due to lack of space, but that should
pose no problem, as all of them have online
help available.
Prime Computer, I nc.'s old mail system
(invoked by typing MAI L) is your typical
run-of-the-mill mail system. It's not too diffi
cult to figure out how to use.
Prime Computer, Inc. has also created
a P R I MOS im plementation of the U N I X
XMAIL system. This seems to b e their pre-
Page 18 2600 Magazine Winter 1989-90](https://image.slidesharecdn.com/2600v06n4winter1989-200423193121/85/2600-v06-n4-winter-1989-18-320.jpg)
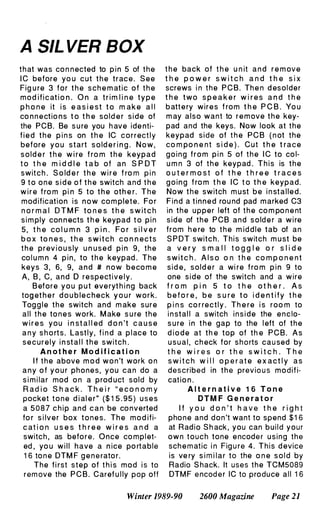
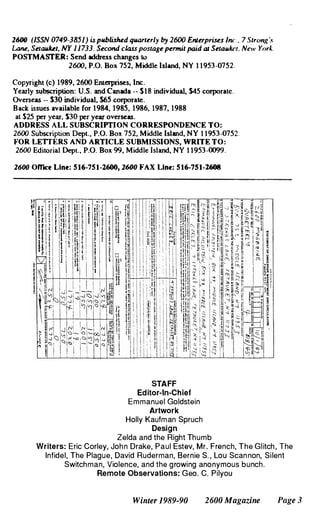
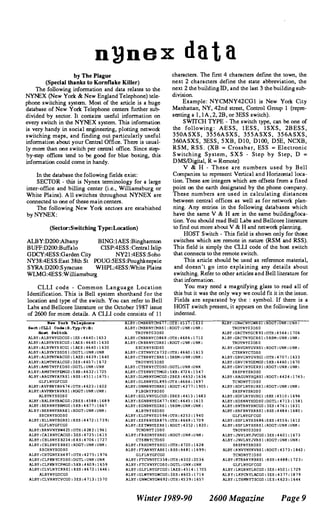
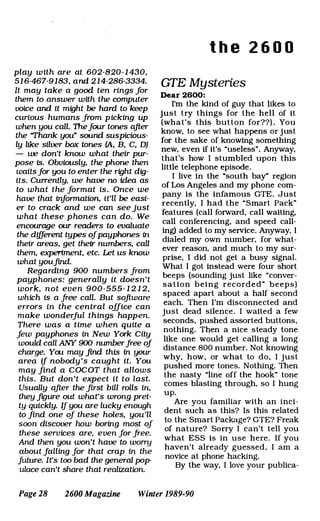
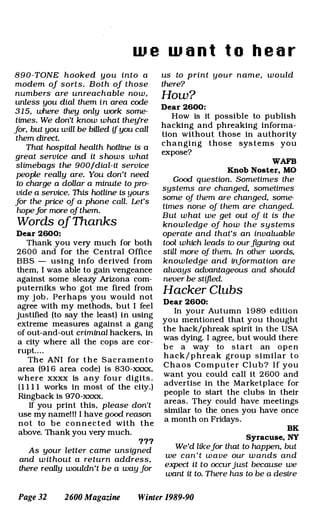
![FOUR EXTRA TONES
!
I ", i "J Q
i
.,. =
i
"' I " I
I ": z � , '"
1:
i " I
I col ,,1: e N i N '"
1 '-'
i
::! I
1
-[ I I
I
I
- ..
i
... .
I
I I -
N ,.., ..
= = =
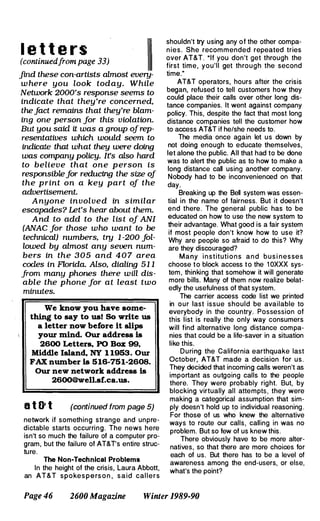
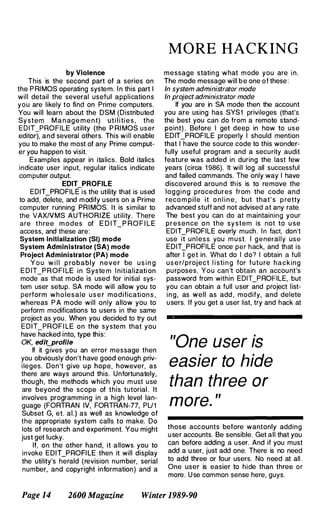
rlgurp 4. 1111,. s t h e rn n t l c h sl",lIIftr t o thp RediD Shar.k dellite
1
I
1 2 J,1 r
e . Up
[Ol I
cnl 2 . e .
C O L 3
COL 4
·1.SU ROW 1
M
ROW 2
ROW ]
n olO 4
2 - 0 F - 8
G N O
KEyrRD
6 �� "
[ 2 �l ).1 f I 3 2 0 speaker 7'
Winter 1989-90
ose 1
'N
H.
C=:J
lONE . 6
OUT
2600 Magazine
..,
c
"
Page 23](https://image.slidesharecdn.com/2600v06n4winter1989-200423193121/85/2600-v06-n4-winter-1989-23-320.jpg)


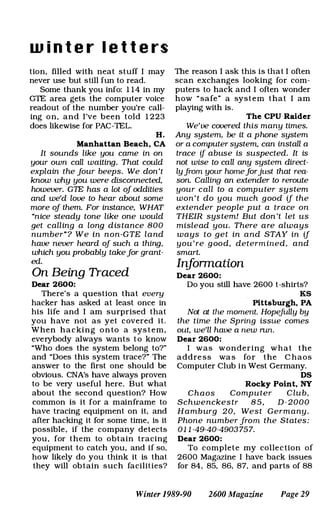

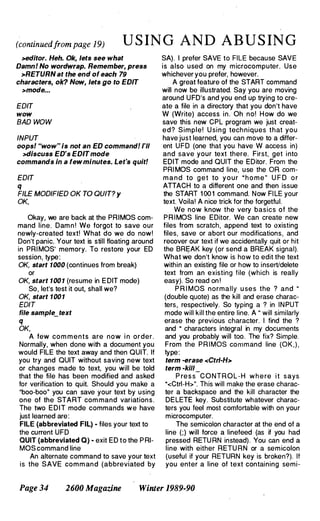
![O N A PR I M E
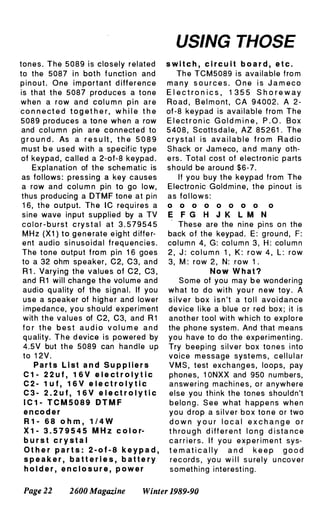
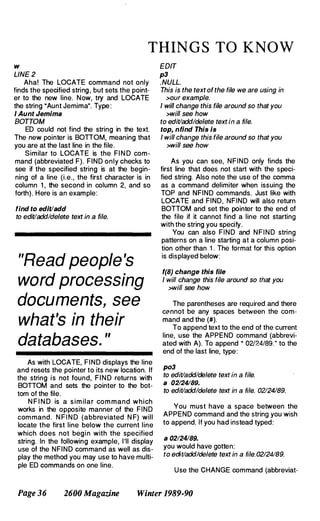
ed C) to change a string in the current line.
The first character after the CHANGE com
mand is used as the delimiter. This is a
more complicated command than most
other ED commands. Format:
CHANGE/strlng-1/strlng-21[G] [n]
·stri n g - 1 " i s the o ri g i n a l string and
·string-2" is the replacement string. G spec
ifies a global change. If G is omitted then
only the first occurance of string-1 will be
changed. ·n" is a pointer value. If it is 0 or 1
(default values) then the change will be
made to the current line (assuming the G
. option is not in use). If "n" is a value other
than 0 or 1 then ED will inspect and make
changes on ·n" lines starting at the current
line. As usual, ED will reset the pointer to
the last line inspected. Should the file con
tain fewer than "n" lines, ED will make the
specified changes in all the lines of the file
and end by saying BOnOM.
Should you wish to change a string con
taining slashes (I), CHANGE's delimiter
character, then substitute a new delimiter
character. Examples:
f 02
to edit/add/delete text in a file. 02124189.
change:021:011:
to edit/add/delete text in a file. 0 1124189.
c#lll-#
to edit/add/delete text in a file. 0 1-24-89.
c/01-24124-Febl
to edit/add/delete text in a file. 24-Feb-89.
You should always issue the TOP com
mand prior to making global file changes.
To insert characters at the beginning of
a line, use CHANGE like this:
po3
to edit/add/delete textin a file. 24-Feb-89.
c//Last Line -> 1
Last Line -> to edit/add/delete text in a
>file. 24-Feb-89.
Remember our dilemma with the semi
colon character (;)? Say you want to have
semicolons in your file. First, let's mark
where we want ED to put the semicolon.
Do this:
po3
Last Line -> to edit/add/delete text in a
>file. 24-Feb-89.
c/. 241@ 241
Last Line -> to edit/add/delete text in a
>file@ 24-Feb-89.
top, cl@l;/g9999
Last Line -> to edit/add/delete text in a
>file; 24-Feb-89.
If you know where you want your semi
colons from the start then just use a char
acter that y o u don 't p lan o n u s i n g
elsewhere in the file (like the @ character)
and place them where you desire. Then
perform the above procedure. Voila! Instant
semicolons when you thought it couldn't be
done.
To delete commands from a file, use the
DELETE command (abbreviated with D). I
believe I don't like the second line of our
example file. Let's delete it. To do this,
type:
po2
d
top
p9999
. NULL.
This is the text of the file we are using in
>our example.
Last Line -> to edit/add/delete text in a
>file; 24-Feb-89.
. NULL.
No more line 2. As with other ED com
mands, DELETE deletes from the current
line. DELETE 1 will not delete the first line
of the fil e , but rathe r the cu rrent l i n e .
DELETE 5 will delete the fifth line from the
current line (with starting line being the cur
rent line).
The last ED command I will go over is
the RETYPE command (abbreviated with
R). RETYPE will delete the current line and
replace it with the specified string. Notice
that the text of our example is now nonsen
sical. The second line is a sentence frag
ment. Let's fix this grammatical error.
po2
Last Line -> to edit/add/delete text in a
Winter 1989-90 2600 Magazine Page 37](https://image.slidesharecdn.com/2600v06n4winter1989-200423193121/85/2600-v06-n4-winter-1989-37-320.jpg)