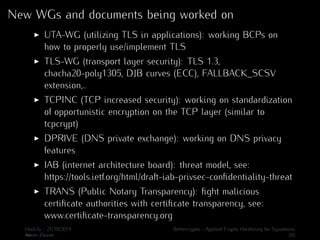
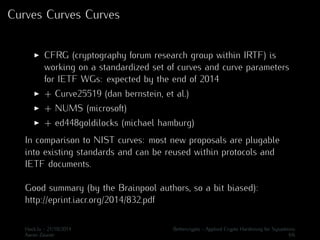
The document discusses the reaction from the Internet Engineering Community to the Snowden leaks. It describes how the IETF began working on drafts and new working groups to prevent pervasive monitoring after 2013. This includes the TLS, UTA, TCPINC, and DPRIVE working groups which are standardizing improvements to TLS, application usage of TLS, TCP encryption, and DNS privacy. The CFRG is also working to standardize a set of cryptographic curves for use in IETF protocols by the end of 2014, including Curve25519, NUMS, and ed448goldilocks.