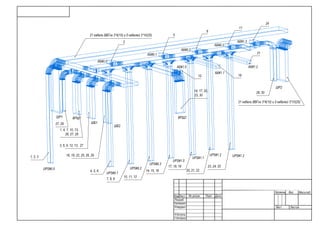
Кабельная трасса, схема обвязки оборудования 0,4кВ
•
0 likes•153 views
Кабельная трасса, схема обвязки оборудования 0,4кВ
Report
Share
Report
Share
Recommended
Uninterruptible power adoption trends to 2025

This document discusses trends in uninterruptible power supply (UPS) adoption for data centers through 2025. Key findings include:
- Centralized UPS systems will likely continue to dominate in large data centers (over 1 MW capacity), especially those owned by enterprises and colocation providers.
- Distributed UPS systems with batteries at the rack level will see limited growth due to technical challenges and customer preferences for centralized systems.
- Medium voltage UPS adoption will remain low due to concerns over costs, reliability, safety, and operational complexity compared to traditional low voltage UPS systems.
- While centralized UPS is widely used, pain points around battery maintenance and reliability will likely persist through 2025 without new technologies or approaches.
Свод знаний управление проектами

Руководство к Своду знаний по управлению проектами
Четвертое издание (Руководство PMBOK®)
IoT— концепция, изменяющая мир

Технологии Интернета вещей — это уже не просто абстракция, доступная жителям ведущих мировых стран:
проекты IoT, несмотря на всю неопределенность в области стандартов и подходов, постепенно внедряются
в Украине. Хотим мы этого или нет — мир вокруг стремительно меняется.
UI report

Uptime Institute report: Post-pandemic data centers.
Post-pandemic data centers UI Intelligence report.
Author: Andy Lawrence, Executive Director of Research, Uptime Institute
2020 battery market Ukraine

Журнал СЕТИ И БИЗНЕС Обзор рынка промышленных герметичных батарей, Украина, 2020
Salt batteries. Sodium Nickel Chloride batteries.

TL Range Batteries for Energy Backup applications available with a capacity of 200, 160, 120 and 80 Ah .
Wiring unlimited.

Ohm’s Law
Kirchhoff's current law (1st Law)
The current flowing into a junction must be equal to
current flowing out of it.
Kirchhoff's voltage law (2nd Law)
The sum of all voltages around any closed loop in a
circuit must equal zero.
Recommended
Uninterruptible power adoption trends to 2025

This document discusses trends in uninterruptible power supply (UPS) adoption for data centers through 2025. Key findings include:
- Centralized UPS systems will likely continue to dominate in large data centers (over 1 MW capacity), especially those owned by enterprises and colocation providers.
- Distributed UPS systems with batteries at the rack level will see limited growth due to technical challenges and customer preferences for centralized systems.
- Medium voltage UPS adoption will remain low due to concerns over costs, reliability, safety, and operational complexity compared to traditional low voltage UPS systems.
- While centralized UPS is widely used, pain points around battery maintenance and reliability will likely persist through 2025 without new technologies or approaches.
Свод знаний управление проектами

Руководство к Своду знаний по управлению проектами
Четвертое издание (Руководство PMBOK®)
IoT— концепция, изменяющая мир

Технологии Интернета вещей — это уже не просто абстракция, доступная жителям ведущих мировых стран:
проекты IoT, несмотря на всю неопределенность в области стандартов и подходов, постепенно внедряются
в Украине. Хотим мы этого или нет — мир вокруг стремительно меняется.
UI report

Uptime Institute report: Post-pandemic data centers.
Post-pandemic data centers UI Intelligence report.
Author: Andy Lawrence, Executive Director of Research, Uptime Institute
2020 battery market Ukraine

Журнал СЕТИ И БИЗНЕС Обзор рынка промышленных герметичных батарей, Украина, 2020
Salt batteries. Sodium Nickel Chloride batteries.

TL Range Batteries for Energy Backup applications available with a capacity of 200, 160, 120 and 80 Ah .
Wiring unlimited.

Ohm’s Law
Kirchhoff's current law (1st Law)
The current flowing into a junction must be equal to
current flowing out of it.
Kirchhoff's voltage law (2nd Law)
The sum of all voltages around any closed loop in a
circuit must equal zero.
Toshiba Rechargeable Battery SCiB™

This document summarizes the characteristics and performance of Toshiba's SCiBTM industrial lithium-ion battery. The battery can be used across various applications due to its excellent safety, long cycle life of over 20,000 charges, rapid charging capability, and ability to operate in temperatures from -30°C to 45°C. It is suited for applications involving electric vehicles, stationary power, and more.
Eaton 9 sx UPS user manual ru

Руководство пользователя Eaton UPS 9SX:
Eaton 9SX 700i
Eaton 9SX 1000i
Eaton 9SX 1500i
Eaton 9SX 2000i
Eaton 9SX 3000i
Eaton 9SX 1000i Rack2U
Eaton 9SX 1500i Rack2U
Eaton 9SX 2000i Rack2U
Eaton 9SX 3000i Rack2U
Eaton 9SX EBM 36V Tower
Eaton 9SX EBM 48V Tower
Eaton 9SX EBM 96V Tower
Eaton 9SX EBM 36V Rack2U
Eaton 9SX EBM 48V Rack2U
Eaton 9SX EBM 72V Rack2U
Eaton 2m cable 36V EBM Tower
Eaton 2m cable 48V EBM Tower
Eaton 2m cable 96V EBM Tower
Eaton cable adaptor 9SX 9130 36V Tower
Eaton cable adaptor 9SX 9130 48V Tower
Eaton cable adaptor 9SX 9130 96V Tower
Eaton 9SX 5000i
Eaton 9SX 6000i
Eaton 9SX EBM 240V Tower
Eaton 2m cable 240V EBM Tower
Eaton cable adaptor 9SX 9130 240V Tower
Gigabit Network Card
«Вперше в Україні – унікальна система автоматизованого контролю прав на об’єк...

«Вперше в Україні – унікальна система автоматизованого контролю прав на об’єкти інтелектуальної власності», опубликованной в журнале «Інтелектуальна власність» в номере №9, 2015г.
Техническая спецификация, гибридный инвертор резервного электропитания

Техническая спецификация, гибридный инвертор резервного электропитания. 1-20кВА.
21.04.2017 резервное электропитание

Гибридный инвертор с возможностью использования Фото Электрических Панелей - ФЭП.
ДСТУ IEC 62040-3:1999 IDT

ДСТУ IEC 62040-3:1999 IDT
Стандарт IEC 62040-3:1997 принят как ДСТУ прямым переводом - IDT
Электронные Стабилизаторы часть вторая

Стабилизаторы с высокочастотным регулированием напряжения, часть вторая
Октаэдры с эмос

Наш слух — явление достаточно сложное. Все дело в том, что разные звуковые частоты воспринимаются нами с разной эффективностью.
Tier Standard Topology

Аннотация
Разработанный Uptime Institute стандарт Tier Standard: Topology служит объективной основой для сравнения функциональности, мощности и прогнозируемой готовности (или надежности) то пологической схемы инфраструктуры определенного ЦОДа с другими ЦОДами, или же для сравнения неско льких ЦОДов. Данный стандарт описывает критерии разделения инфраструктуры ЦОДа на четыре класса, разли чающихся уровнем резервирования активных компонентов и каналов распределения. Основным содержанием стандарта является определение четырех уровней Tier и тесты, призванные подтвердить соответствие этим определениям. Специальный раздел «Комментарий» содержит практические примеры конфигураций и проектных решений, отвечающих требованиям стандарта Tier. Эти примеры поясняют принятые в данном стандарте критерии классификации.
Инфраструктура ЦОД Tier Standard: Operational Sustainability

Аннотация
Разработанный Uptime Institute стандарт Tier Standard: Operational Sustainability является объективной методикой,
которая позволит владельцам ЦОДов настроить программу управлени я объектами в соответствии со стандартом
Tier установленного оборудования площадки для достижения коммерческих целей или основных задач организац ии.
Стандарт Tier Standard: Operational Sustainability определяет алгоритмы и риски за пределами системы классификаци и
Tier (I, II, III и IV), которые влияют на показатели работы ЦОДа в долгосрочной перспективе. Стандарт Tier Standard:
Operational Sustainability приводит к общему знаменателю управление площадкой и функциональность ее инженерных
систем.
On-Line Against Delta Technology 

On-Line Against Delta Technology.
This document is due to a contribution of the following:
Companies Authors
AEG SVS Horst Scholz / Wilhelm Sölter
MGE UPS Systems Mr. Böschen / Mr. Odenthal
Piller Mr. Darrelmann / Mr. Sachs
Sicon-Socomec Mr. Neutzner
Siemens Mr. Fischer
Victron Mr. Raap
IMV Invertomatic Mr. Schwerzmann
Victron Netpro 600 1500 

This document provides detailed specifications for the Victron NetPro 600-1500 VA UPS series. It describes the functional principles of the UPS, including normal operation using the input converter to charge batteries and power the load via the output converter, and backup operation during power outages using battery power converted by the output converter. It also lists the external features, dimensions, weights, and electrical specifications of the UPS, including input and output voltage ranges and tolerances, frequencies, waveforms, transfer times, and safety/EMC standards.
Отчет Audit report RAPID7

The audit report summarizes a security audit performed on May 28, 2014. The audit found 2 vulnerabilities on 1 system, with no critical vulnerabilities. The most common vulnerabilities were related to TCP sequence number approximation and generic ICMP timestamp responses. To address these issues, patches need to be applied to disable ICMP timestamp responses and enable TCP MD5 signatures.
Отчет Executive penetration RAPID 7

This security audit report summarizes the results of a scan of one system on the TEST_CSA network from May 28, 2014 01:49 to May 28, 2014 01:50. The scan found 11 vulnerabilities total, including 1 critical vulnerability and 7 severe vulnerabilities. The most common vulnerabilities were certificate-common-name-mismatch, cifs-smb-signing-disabled, cifs-smb-signing-not-required and ssl-self-signed-certificate. The cifs-smb-signing-disabled vulnerability posed the highest risk to the organization. The scan identified 1 operating system and 8 services running, with the HTTPS service found to have the most vulnerabilities at 7.
Отчет Executive overview RAPID7

The audit found 11 vulnerabilities on the scanned system, including 1 critical vulnerability that requires immediate attention. There were also 7 severe vulnerabilities that should be addressed promptly. The cifs-smb-signing-disabled vulnerability poses the highest risk to the organization. The audit identified 1 operating system and 8 services running on the scanned system, with the HTTPS service found to have the most vulnerabilities at 7.
Отчет Csa report RAPID7

The audit report summarizes the results of a security audit performed on the network. It found 11 vulnerabilities total, including 1 critical vulnerability that requires immediate attention. The most common vulnerabilities were certificate-common-name-mismatch and cifs-smb-signing-disabled. The vulnerability that poses the highest risk is cifs-smb-signing-disabled with a risk score of 768. The audit scanned 1 system running Microsoft Windows Server 2008 R2 and found 8 services, with HTTPS having the most associated vulnerabilities at 7.
Report PAPID 7

The audit report summarizes the results of a security audit performed on May 28, 2014. The scan found 2 vulnerabilities, with one being severe. The tcp-seq-num-approximation vulnerability was the most common and highest risk. The report provides details on the discovered systems, vulnerabilities found, and recommendations to address the tcp-seq-num-approximation and generic-icmp-timestamp vulnerabilities.
Инструкция пользователя, инверторы Apsx 6048 и APSX 3024

Инструкция пользователя, инверторы Apsx 6048 и APSX 3024
More Related Content
More from Sergey Yrievich
Toshiba Rechargeable Battery SCiB™

This document summarizes the characteristics and performance of Toshiba's SCiBTM industrial lithium-ion battery. The battery can be used across various applications due to its excellent safety, long cycle life of over 20,000 charges, rapid charging capability, and ability to operate in temperatures from -30°C to 45°C. It is suited for applications involving electric vehicles, stationary power, and more.
Eaton 9 sx UPS user manual ru

Руководство пользователя Eaton UPS 9SX:
Eaton 9SX 700i
Eaton 9SX 1000i
Eaton 9SX 1500i
Eaton 9SX 2000i
Eaton 9SX 3000i
Eaton 9SX 1000i Rack2U
Eaton 9SX 1500i Rack2U
Eaton 9SX 2000i Rack2U
Eaton 9SX 3000i Rack2U
Eaton 9SX EBM 36V Tower
Eaton 9SX EBM 48V Tower
Eaton 9SX EBM 96V Tower
Eaton 9SX EBM 36V Rack2U
Eaton 9SX EBM 48V Rack2U
Eaton 9SX EBM 72V Rack2U
Eaton 2m cable 36V EBM Tower
Eaton 2m cable 48V EBM Tower
Eaton 2m cable 96V EBM Tower
Eaton cable adaptor 9SX 9130 36V Tower
Eaton cable adaptor 9SX 9130 48V Tower
Eaton cable adaptor 9SX 9130 96V Tower
Eaton 9SX 5000i
Eaton 9SX 6000i
Eaton 9SX EBM 240V Tower
Eaton 2m cable 240V EBM Tower
Eaton cable adaptor 9SX 9130 240V Tower
Gigabit Network Card
«Вперше в Україні – унікальна система автоматизованого контролю прав на об’єк...

«Вперше в Україні – унікальна система автоматизованого контролю прав на об’єкти інтелектуальної власності», опубликованной в журнале «Інтелектуальна власність» в номере №9, 2015г.
Техническая спецификация, гибридный инвертор резервного электропитания

Техническая спецификация, гибридный инвертор резервного электропитания. 1-20кВА.
21.04.2017 резервное электропитание

Гибридный инвертор с возможностью использования Фото Электрических Панелей - ФЭП.
ДСТУ IEC 62040-3:1999 IDT

ДСТУ IEC 62040-3:1999 IDT
Стандарт IEC 62040-3:1997 принят как ДСТУ прямым переводом - IDT
Электронные Стабилизаторы часть вторая

Стабилизаторы с высокочастотным регулированием напряжения, часть вторая
Октаэдры с эмос

Наш слух — явление достаточно сложное. Все дело в том, что разные звуковые частоты воспринимаются нами с разной эффективностью.
Tier Standard Topology

Аннотация
Разработанный Uptime Institute стандарт Tier Standard: Topology служит объективной основой для сравнения функциональности, мощности и прогнозируемой готовности (или надежности) то пологической схемы инфраструктуры определенного ЦОДа с другими ЦОДами, или же для сравнения неско льких ЦОДов. Данный стандарт описывает критерии разделения инфраструктуры ЦОДа на четыре класса, разли чающихся уровнем резервирования активных компонентов и каналов распределения. Основным содержанием стандарта является определение четырех уровней Tier и тесты, призванные подтвердить соответствие этим определениям. Специальный раздел «Комментарий» содержит практические примеры конфигураций и проектных решений, отвечающих требованиям стандарта Tier. Эти примеры поясняют принятые в данном стандарте критерии классификации.
Инфраструктура ЦОД Tier Standard: Operational Sustainability

Аннотация
Разработанный Uptime Institute стандарт Tier Standard: Operational Sustainability является объективной методикой,
которая позволит владельцам ЦОДов настроить программу управлени я объектами в соответствии со стандартом
Tier установленного оборудования площадки для достижения коммерческих целей или основных задач организац ии.
Стандарт Tier Standard: Operational Sustainability определяет алгоритмы и риски за пределами системы классификаци и
Tier (I, II, III и IV), которые влияют на показатели работы ЦОДа в долгосрочной перспективе. Стандарт Tier Standard:
Operational Sustainability приводит к общему знаменателю управление площадкой и функциональность ее инженерных
систем.
On-Line Against Delta Technology 

On-Line Against Delta Technology.
This document is due to a contribution of the following:
Companies Authors
AEG SVS Horst Scholz / Wilhelm Sölter
MGE UPS Systems Mr. Böschen / Mr. Odenthal
Piller Mr. Darrelmann / Mr. Sachs
Sicon-Socomec Mr. Neutzner
Siemens Mr. Fischer
Victron Mr. Raap
IMV Invertomatic Mr. Schwerzmann
Victron Netpro 600 1500 

This document provides detailed specifications for the Victron NetPro 600-1500 VA UPS series. It describes the functional principles of the UPS, including normal operation using the input converter to charge batteries and power the load via the output converter, and backup operation during power outages using battery power converted by the output converter. It also lists the external features, dimensions, weights, and electrical specifications of the UPS, including input and output voltage ranges and tolerances, frequencies, waveforms, transfer times, and safety/EMC standards.
Отчет Audit report RAPID7

The audit report summarizes a security audit performed on May 28, 2014. The audit found 2 vulnerabilities on 1 system, with no critical vulnerabilities. The most common vulnerabilities were related to TCP sequence number approximation and generic ICMP timestamp responses. To address these issues, patches need to be applied to disable ICMP timestamp responses and enable TCP MD5 signatures.
Отчет Executive penetration RAPID 7

This security audit report summarizes the results of a scan of one system on the TEST_CSA network from May 28, 2014 01:49 to May 28, 2014 01:50. The scan found 11 vulnerabilities total, including 1 critical vulnerability and 7 severe vulnerabilities. The most common vulnerabilities were certificate-common-name-mismatch, cifs-smb-signing-disabled, cifs-smb-signing-not-required and ssl-self-signed-certificate. The cifs-smb-signing-disabled vulnerability posed the highest risk to the organization. The scan identified 1 operating system and 8 services running, with the HTTPS service found to have the most vulnerabilities at 7.
Отчет Executive overview RAPID7

The audit found 11 vulnerabilities on the scanned system, including 1 critical vulnerability that requires immediate attention. There were also 7 severe vulnerabilities that should be addressed promptly. The cifs-smb-signing-disabled vulnerability poses the highest risk to the organization. The audit identified 1 operating system and 8 services running on the scanned system, with the HTTPS service found to have the most vulnerabilities at 7.
Отчет Csa report RAPID7

The audit report summarizes the results of a security audit performed on the network. It found 11 vulnerabilities total, including 1 critical vulnerability that requires immediate attention. The most common vulnerabilities were certificate-common-name-mismatch and cifs-smb-signing-disabled. The vulnerability that poses the highest risk is cifs-smb-signing-disabled with a risk score of 768. The audit scanned 1 system running Microsoft Windows Server 2008 R2 and found 8 services, with HTTPS having the most associated vulnerabilities at 7.
Report PAPID 7

The audit report summarizes the results of a security audit performed on May 28, 2014. The scan found 2 vulnerabilities, with one being severe. The tcp-seq-num-approximation vulnerability was the most common and highest risk. The report provides details on the discovered systems, vulnerabilities found, and recommendations to address the tcp-seq-num-approximation and generic-icmp-timestamp vulnerabilities.
Инструкция пользователя, инверторы Apsx 6048 и APSX 3024

Инструкция пользователя, инверторы Apsx 6048 и APSX 3024
More from Sergey Yrievich (20)
«Вперше в Україні – унікальна система автоматизованого контролю прав на об’єк...

«Вперше в Україні – унікальна система автоматизованого контролю прав на об’єк...
Техническая спецификация, гибридный инвертор резервного электропитания

Техническая спецификация, гибридный инвертор резервного электропитания
Инфраструктура ЦОД Tier Standard: Operational Sustainability

Инфраструктура ЦОД Tier Standard: Operational Sustainability
Инструкция пользователя, инверторы Apsx 6048 и APSX 3024

Инструкция пользователя, инверторы Apsx 6048 и APSX 3024
